Report: British Printing Press Leaks Confidential Material & More
The vpnMentor cybersecurity research team, led by Noam Rotem and Ran Locar, have uncovered a leaking S3 Bucket with over 270k records and greater than 343GB in size on an Amazon server, belonging to Doxzoo. There are potentially over 100,000 users affected by this data leak, with implications not only for copyright violations, but also American and British military data exposure.
Doxzoo Company Profile
Doxzoo is a document printing and binding production company, based in the U.K., but servicing customers globally since 2014. The data leak includes print jobs for many high-profile clientele, including elite universities, US and UK military branches, Fortune 500 companies, and many, many more.
On their website, Doxzoo boasts ISO accreditation for, among other things, security, and prides themselves on keeping their customers’ documents in “safe hands.”
Timeline of Discovery and Owner Reaction
Sometimes the extent of a data breach and the owner of the data are obvious, and the issue quickly resolved. But rare are these times. Most often, we need days of investigation before we understand what’s at stake or who’s leaking the data.
Understanding a breach and its potential impact takes careful attention and time. We work hard to publish accurate and trustworthy reports, ensuring everybody who reads them understands their seriousness.
Some affected parties deny the facts, disregarding our research or playing down its impact. So, we need to be thorough and make sure everything we find is correct and true.
In this case, we easily identified Doxzoo as the owner of the database and contacted the company with our findings. However, Doxzoo never responded to our communication attempts. They only closed the data leak after we reached out to Amazon.
- Date discovered: January 22, 2020
- Date company notified: January 26, 2020
- Date Amazon notified: February 5, 2020
- Date bucket closed: February 11, 2020
Examples of Entries in the Database
Doxzoo has a handful of high-profile customers for whom they are executing a variety of print jobs, including complete scripts and screenplays, full-length books, sought-after paid wellness plans, and internal military handbooks, to name a few projects. They also get requests from private individuals who order family scrapbooks (complete with pictures of the kids), bachelorette souvenirs with potentially compromising photos of the bride-to-be, and more. Additionally, Doxzoo seems to regularly request full scans of photo IDs (such as passports) to fulfill orders.
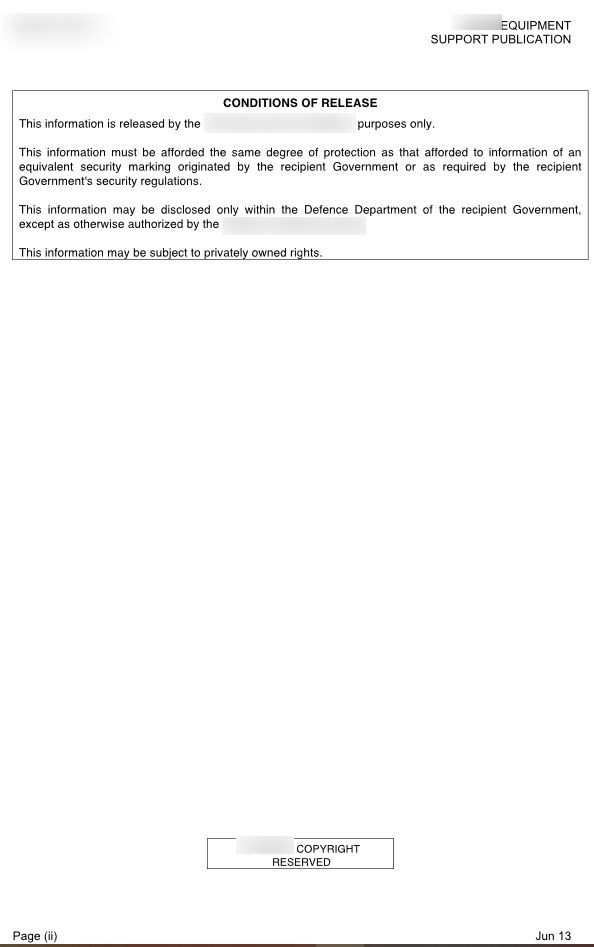
Confidential military material
Here’s the list of data that our research team found and was able to identify:
Data Impacted
- PII
- Full names
- Addresses
- Email addresses
- Passport scans
- PCI
- Payment method
- Last four digits of payment method
- Order details (items ordered, date, amount/receipt)
- Tracking labels
- Copyrighted Publications
- Full-length books
- Screenplays
- Scripts for one of the top TV series around the world
- Paid Programs
- University course material (including elite institutions)
- Diet and exercise plans
- Exam preparation classes
- Teacher’s guides with answers for tests
- Certifications, diplomas, and degrees
- Medical documents, log books, etc.
- Musical compositions
- Religious texts
- Floor plans detailing various security elements
- Internal military documents (including classified information)
Specialized university course material
Personal photos for printed albums
Internal corporate documents
Countries Affected
These are the countries where we found Doxzoo customers included in the leak, but we did not open each file and it is possible that there are more clients in additional countries that were impacted.
- United States of America
- United Kingdom
- Sri Lanka
- Nigeria
- India
Clients' passports
Professional credentials of individuals
Data Breach Impact
Confidential Information
The items contained this leak often hold private and/or confidential information within. The promise of secure facilities and systems are key selling points for clients such as the military, and the breach of that guarantee is not only a failure in service, but also potentially holds a security risk along with it.
Identity Theft
Knowing the full name, birthdate, and, yes, even the incarceration record of an individual can provide criminals with enough information to steal that person’s identity.
Identity theft does not always mean that the thief will claim that they are a particular individual in real life; it also allows them to engage in credit fraud, drain your bank account, and engage in scams to family, friends, and other associates of the identity theft victim.
Copyright Violations
Anyone with access to the countless copyrighted documents contained within this database could easily download them without having to pay for their contents and also illegally upload them to a torrent network, available for free to all.
Advice from the Experts
Doxzoo could have easily avoided this leak if they had taken some basic security measures to protect the S3 Bucket. These include, but are not limited to:
- Secure your servers.
- Implement proper access rules.
- Never leave a system that doesn’t require authentication open to the internet.
Any company can replicate the same steps, no matter its size. For a more in-depth guide on how to protect your business, check out our guide to securing your website and online database from hackers.
For those affected by the leak
You can contact Doxzoo directly and find out how they are resolving this issue and plan on protecting your data better in the future. If you may have your personal information on the Doxzoo platform - and are concerned about how this breach might impact you or other data vulnerabilities in general, read our complete guide to online privacy to help better protect yourself online in the future.
It shows you the many ways cyber criminals target internet users, and the steps you can take to stay safe. You can also use a VPN to hide some of the data collected by Doxzoo. A VPN will mask your IP address and country of residence, giving you an added layer of protection even if your data is leaked.
How and Why We Discovered the Breach
During an extensive web mapping project, the research team at vpnMentor uncovered a breach in Doxzoo's database. Our investigators employ port scanning to investigate specific IP blocks and evaluate systems for vulnerabilities through any open gaps. Each of these gaps is then thoroughly inspected for possible instances of data leakage.
When they find a data breach, they use expert techniques to verify the database’s identity. We then alert the company to the breach. If possible, we will also alert those affected by the breach.
We were able to access Doxzoo’s S3 bucket because it was completely unsecured and unencrypted. Using a web browser, the team could access all files hosted on the database.
The purpose of this web mapping project is to help make the internet safer for all users. As ethical hackers, we’re obliged to inform a company when we discover flaws in their online security.
However, these ethics also mean we also carry a responsibility to the public. This is especially true when the companies data breach contains such a huge amount of private and sensitive information.
About Us and Previous Reports

In the past, we’ve discovered a breach in LightInTheBox that compromised the data of its customers. We also recently revealed that a company owned by major hotel chain AccorHotels exposed over 1TB of guests’ data. You may also want to read our VPN Leak Report and Data Privacy Stats Report.



Please, comment on how to improve this article. Your feedback matters!