Report: Two Corporate Finance Companies Leak Half a Million Legal and Financial Documents Online
vpnMentor’s research team, led by Noam Rotem, recently uncovered a breached database leaking a massive amount of sensitive financial documents online.
Whatever the intended purpose of this database was, over 500,000 highly sensitive and private legal and financial documents were exposed, compromising numerous parties to the risk of fraud and theft.
Had criminal hackers discovered this database, there would have been dire consequences for all involved.
Company Profile
The database appears to be linked to MCA Wizard, an iOS and Android app developed by two companies: Advantage Capital Funding and Argus Capital Funding. Launched in January 2018, the app is no longer available for download.
Based on our research, Advantage and Argus seem to be the same company under two different names, both based in New York, USA. For instance:
- They have similar company names
- Any description of MCA Wizard online includes the following: “Advantage and Argus Capital Funding work as a single united team with market-leading firms around the world and give our clients the highest quality advice possible.”
- Their websites share identical text in certain sections
- They share a CFO and other executive staff and physical address
As such, we will refer to them as a pair throughout this report.
What is an MCA?
“MCA” stands for Merchant Cash Advance, a type of financial instrument used to provide loans and credit advances to small business owners. These loans are usually short term - less than two years - and high interest. Some providers charge 10-15% interest.
MCAs are a controversial practice, as providers use loopholes in business, finance, and banking laws to bypass regulations and act without oversight from independent bodies.
Aside from seemingly developing the MCA Wizard app, Advantage and Argus provide funding and startup capital to business owners without access to traditional lending and financial services.
Timeline of Discovery and Owner Reaction
Sometimes, the extent of a data breach and the owner of the data are obvious, and the issue quickly resolved. But rare are these times. Most often, we need days of investigation before we understand what’s at stake or who’s leaking the data.
Understanding a breach and its potential impact takes careful attention and time. We work hard to publish accurate and trustworthy reports, ensuring everybody who reads them understands their seriousness.
Some affected parties deny the facts, disregarding our research, or playing down its impact. So, we need to be thorough and make sure everything we find is correct and accurate.
In this case, we discovered the breached database on Amazon Web Services (AWS) in December 2019. Advantage and Argus were using an S3 bucket, a popular method of storage on AWS, but one that requires the users to set up their own security protocols.
However, the purpose and ownership of the database were not initially apparent. In fact, from the beginning of our research, a lot was unclear about this discovery.
While the database’s URL contained ‘MCA Wizard,’ most files had no relation to the app.
Instead, they originated from both Advantage and Argus. Furthermore, throughout our research, files were still being uploaded to the database, even though MCA Wizard seems to have been closed down.
Information on all three entities is scarce, but they appear to be owned and operated by the same people. However, there is no clear connection between MCA Wizard and the two companies that own it anywhere online.
Finally, when we tried to contact both companies, we were unable to do so. Argus does not provide a contact email, while our emails to Advantage’s contact address failed to deliver.
Eventually, we contacted AWS directly, and the breach was closed shortly after.
- Date discovered: 24th December 2019
- Date vendors contacted: 30th December 2019
- Date of contact with AWS: 7th January 2020
- Date of Action: 9th January 2020
Example of Entries in the Database
The database contained over 500,000 documents, totaling 425GB of data. Within was a wide range of documents covering many aspects of Advantage and Argus’s businesses, finances, and dealings with other companies.
The files our team viewed included but were not limited to:
- Credit reports
- Bank statements
- Contracts
- Legal paperwork
- Driver's licenses
- Purchase orders and receipts
- Tax returns
- Transaction reports for credit cards and merchant bank accounts
- Scanned copies of bank checks
- Access information for bank accounts
- Corporate shares outline
- Social Security information
These files didn’t just compromise the privacy and security of Advantage and Argus, but also the customers, clients, contractors, employees, and partners.
The following examples demonstrate the wide range of this leak.
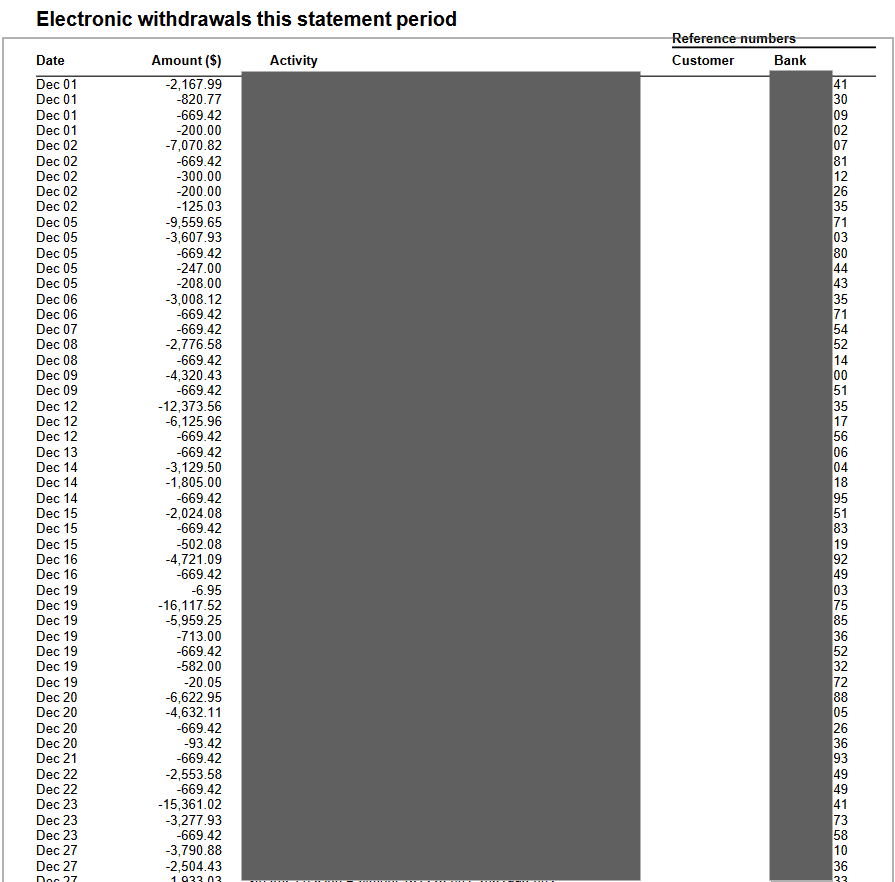
Example 1: Bank statement detailing account withdrawals
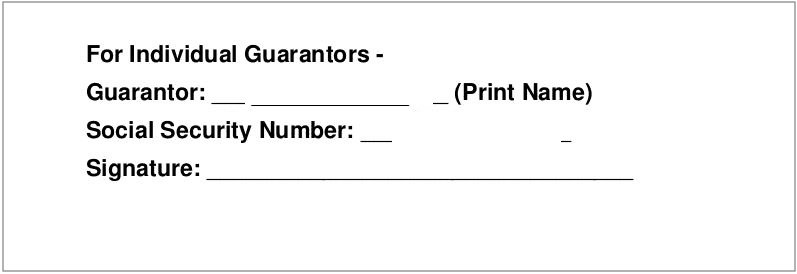
Example 2: Social Security number of Advantage and Argus employee exposed
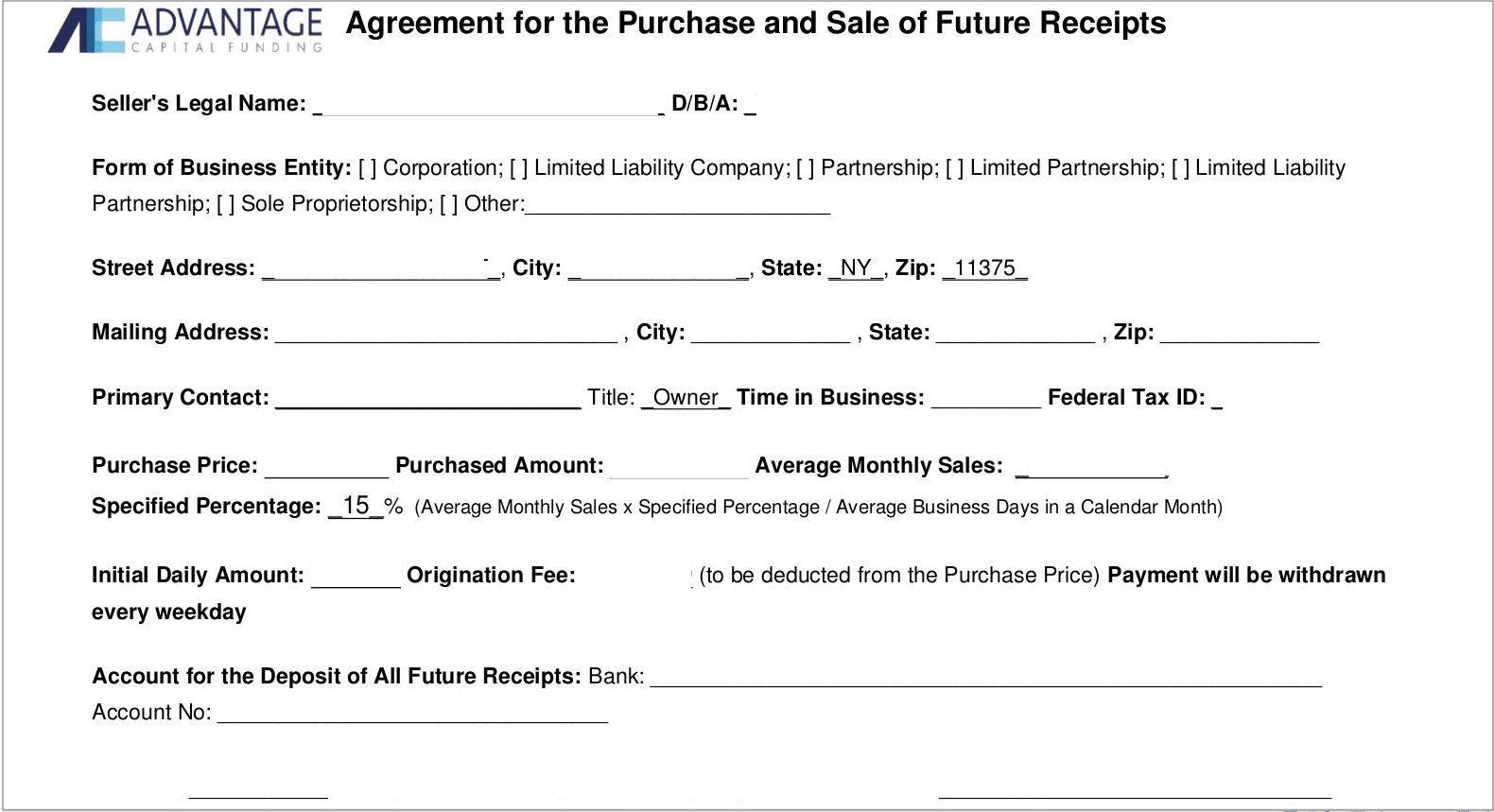
Example 3: Details of a financial agreement with a 3rd party
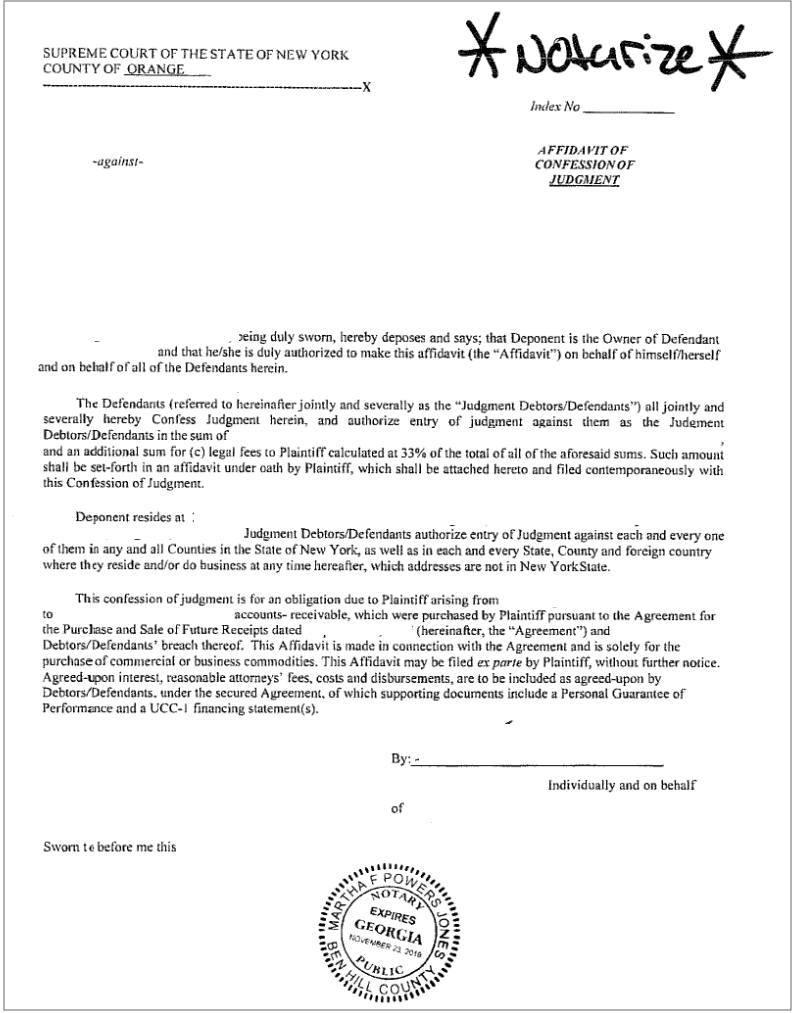
Example 4: Sensitive legal documents also exposed
Impact For Advantage and Argus
This leak raises serious credibility and trust issues for Advantage and Argus. By not sufficiently securing this database and revealing so much information, they have compromised the safety, privacy, and security of their clients, partners, and customers.
Those affected may take action against Advantage and Argus for doing so, either from ceasing to do business with either company or possibly pursuing legal actions. Both would result in considerable loss of clients, contracts, business relationships, and ultimately, revenue.
Furthermore, a leak like this may attract the attention of US financial and data security regulators. The state of California recently passed the California Consumer Privacy Act (CCPA) precisely to deal with data leaks of this nature. Advantage and Argus will have to consider how they will comply with the law to mitigate any further investigations.
Advantage and Argus themselves could also have been exposed to many forms of fraud, and illegal threats had malicious hackers discovered this database. Using details of both companies' structures, relationships, and finances, criminals could have pursued any of the following illegal schemes:
- Phishing campaigns
- Check and financial fraud
- Extortion and blackmail
- Selling their confidential files on the Dark Web
- Targeting the companies with ransomware, spyware, malware, and similar forms of online attack
- Much more
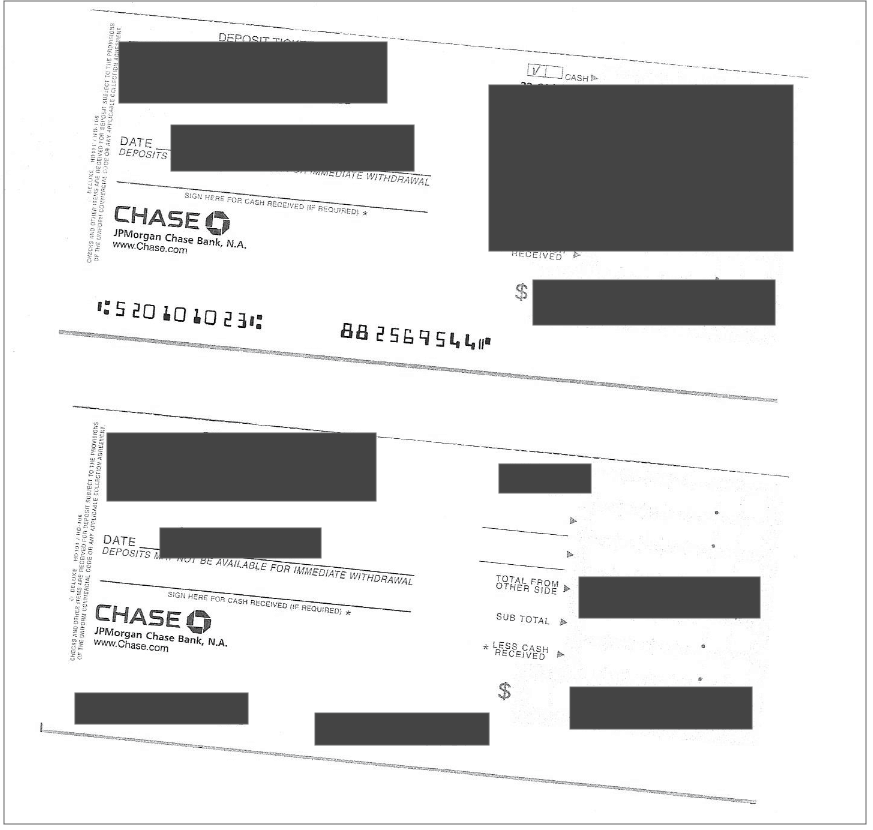
Example 5: Checks related to Advantage and Argus business activities
Impact For Advantage and Argus Customers, Clients, Partners
Many of the risks detailed above also apply to the businesses and individuals whose private financial, legal, and personal information Advantage and Argus exposed.
However, the potential problems go much further for the people doing business with both companies.
Many of the files we viewed revealed Social Security numbers and other forms of Personally Identifiable Information (PII) belonging to a diverse range of private individuals and business owners. These could be used to commit additional forms of fraud against those affected, including wholesale identity theft.
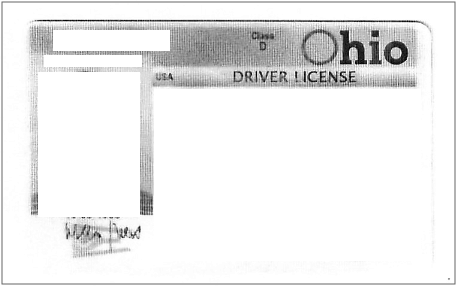
Example 6: A driver license scan reveals PII of an individual without any clear relation to Advantage and Argus
The financial and legal consequences of such crimes could destroy a not just a person’s businesses, but their entire life.
Advice from the Experts
Advantage and Argus could have easily avoided this leak if they had taken some basic security measures to protect the database. These include, but are not limited to:
- Securing their servers.
- Implementing proper access rules.
- Never leaving a system that doesn’t require authentication open to the internet.
Any company can replicate the same steps, no matter its size.
For a more in-depth guide on how to protect your business, check out our guide to securing your website and online database from hackers.
Securing an Open S3 Bucket
It’s important to note that open, publicly viewable S3 buckets are not a flaw of AWS. They’re usually the result of an error by the owner of the bucket. Amazon provides detailed instructions to AWS users to help them secure S3 buckets and keep them private.
These include:
- Making a bucket private and adding authentication protocols.
- Following AWS access and authentication best practices.
- Adding more layers of protection to an S3 bucket to further restrict who can access it from every point of entry.
For Advantage and Argus Customers, Clients, and Partners
If you’re a customer of Advantage and Argus and concerned about how this breach might impact you, contact the companies directly to find out what steps they’re taking.
To learn about data vulnerabilities in general, read our complete guide to online privacy.
It shows you the many ways cybercriminals target internet users, and how you can stay safe.
How and Why We Discovered the Breach
The research team at vpnMentor identified a breach in the database of Advantage and Argus during a comprehensive web mapping project. Our investigators employ port scanning to scrutinize specific IP blocks, probing systems for exposed vulnerabilities that could serve as potential weak spots. Each of these weak spots is then thoroughly analyzed for possible data leakage.
When they find a data breach, they use expert techniques to verify the database’s identity. We then alert the company of the breach. If possible, we will also inform any other party affected by the breach.
Our team was able to access this database because it was completely unsecured and unencrypted.
The purpose of this web mapping project is to help make the internet safer for all users.
As ethical hackers, we’re obliged to inform a company when we discover flaws in their online security. We reached out to Advantage and Argus, not only to let them know about the vulnerability but also to suggest ways in which they could make their system secure.
These ethics also mean we carry a responsibility to the public. Advantage and Argus customers and clients must be aware of a data breach that impacts them too.
We also never sell, store, or expose any information we encounter during our security research.
About Us and Previous Reports

This has included an enormous data leak exposing the travel arrangements and details of members of the US military. We also revealed that a company owned by European hotel giant AccorHotels compromised the privacy and security of hotel guests around the world. You may also want to read our VPN Leak Report and Data Privacy Stats Report.
[Publication date: 19.02.2020]



Please, comment on how to improve this article. Your feedback matters!