Raptor School Safety Software Breach Exposed 4 Million Records Including Highly Sensitive Data

Cybersecurity Researcher, Jeremiah Fowler, discovered and reported to vpnMentor about a non-password protected database that contained an estimated 4 million records, which included sensitive school safety records and PII of students, parents, and school staff.
The non-password protected documents were in three separate cloud storage buckets and totaled 4,024,001 records. Upon further research, the documents indicated the database belonged to a Texas-based school security company called Raptor Technologies. I reviewed a limited sample of documents and log records that contained what appeared to be sensitive information related to students, teachers, parents, and school safety plans or procedures. I immediately sent a responsible disclosure notice and received confirmation that indeed the data belonged to Raptor Technologies. The company took action to secure the exposed database, and public access was restricted the following day. It is unknown how long the database was exposed or if anyone else may have accessed the database, as only an internal forensic audit could identify potentially malicious access.
Among the documents I saw were:
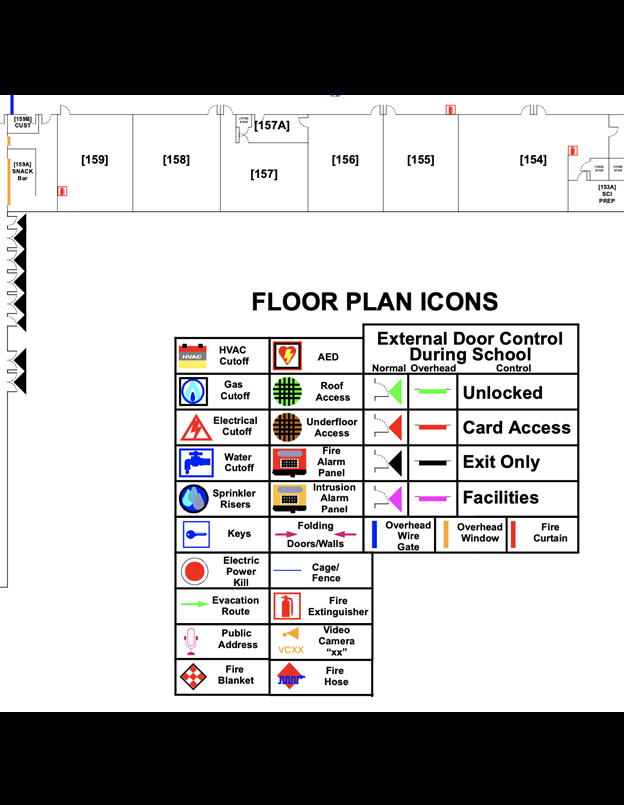
- School incident response plans, layouts of schools or classrooms, and notes regarding infrastructure challenges, such as malfunctioning cameras or security gaps;
- Details on background check systems (including names) were listed among the files;
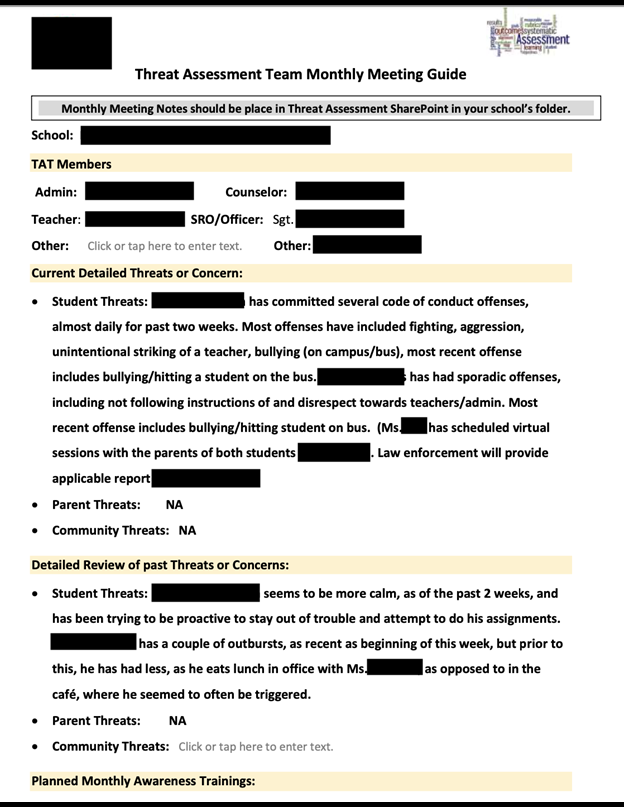
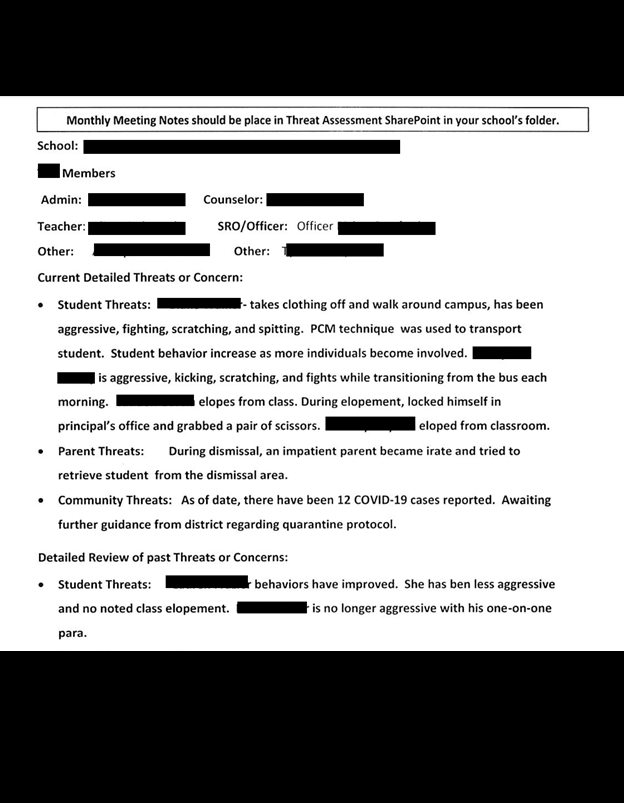
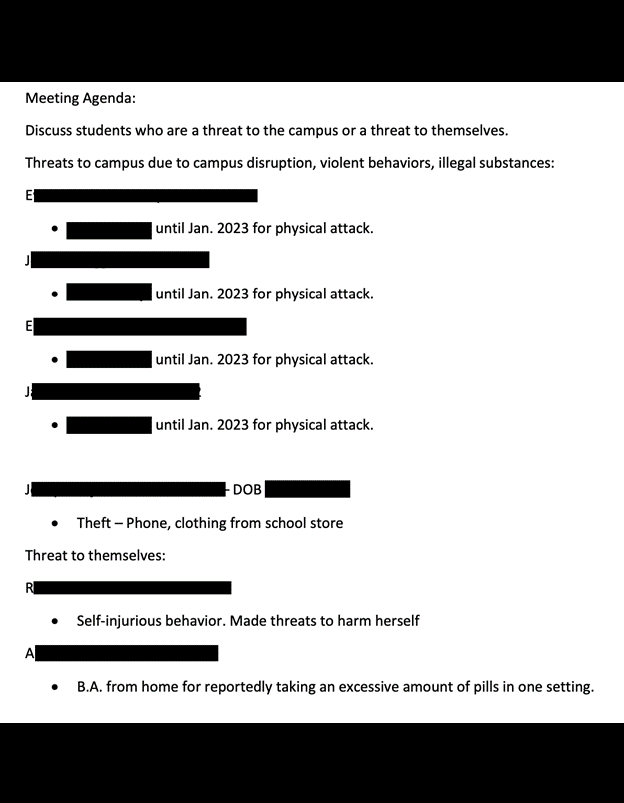
- Documents regarding at-risk students, which detailed their personal and medical conditions, any mental health or legal problems they might be having, and the threats they pose to the school;
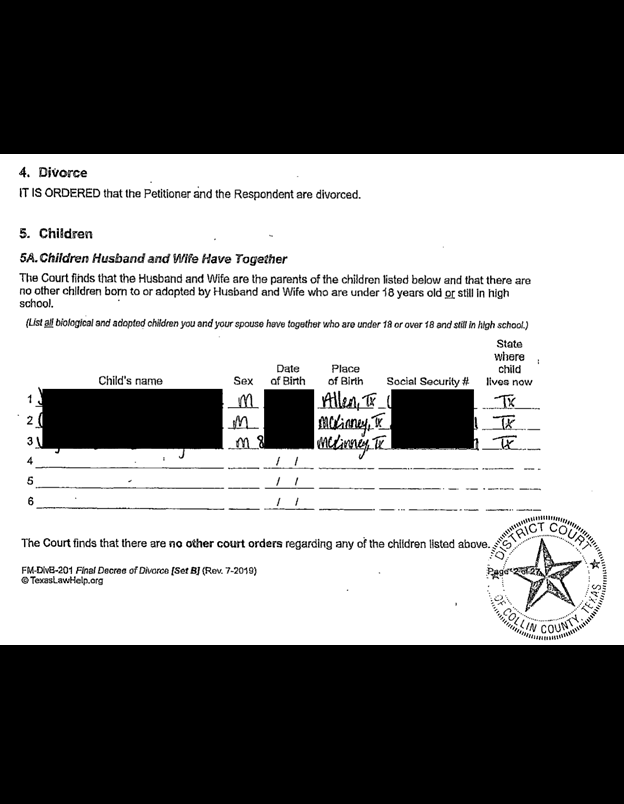
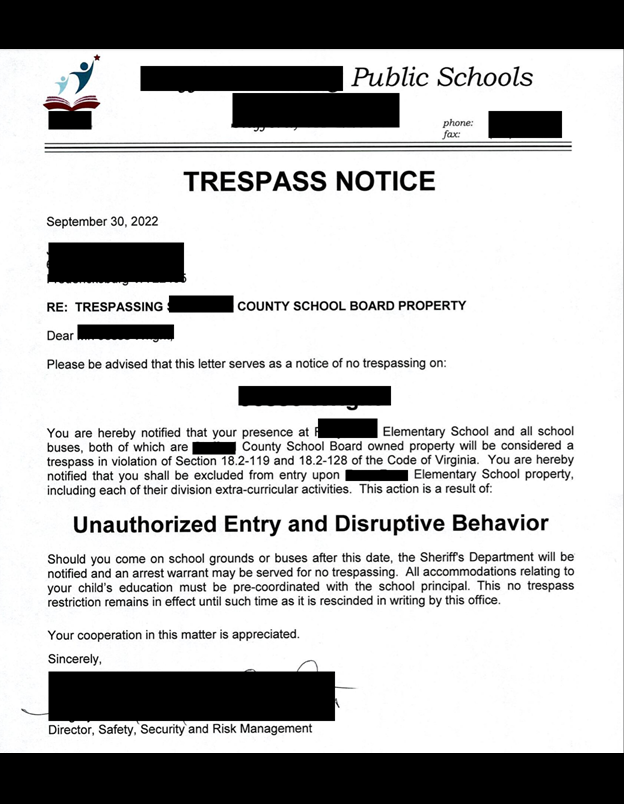
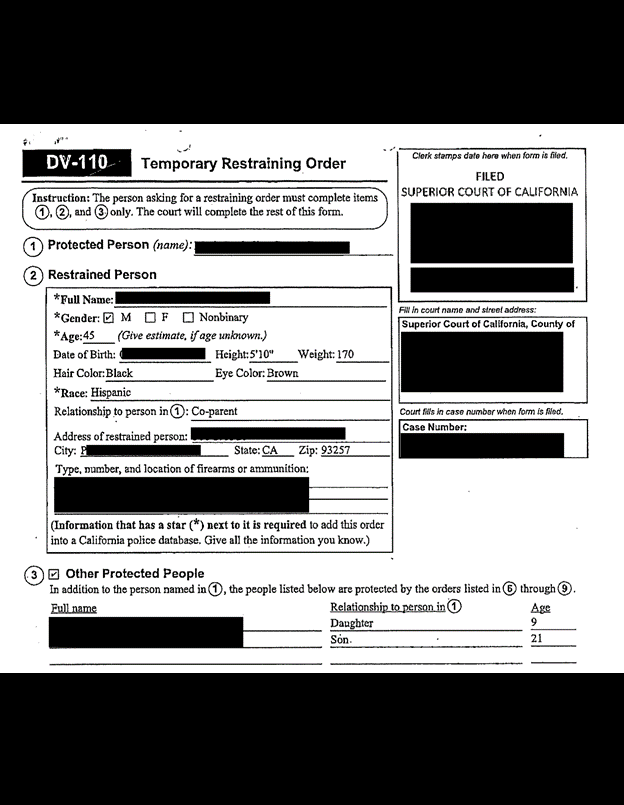
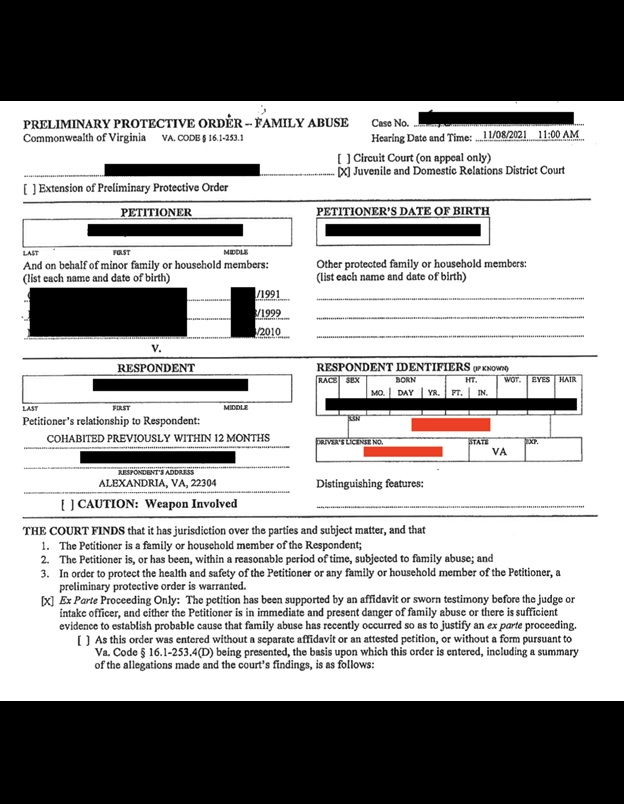
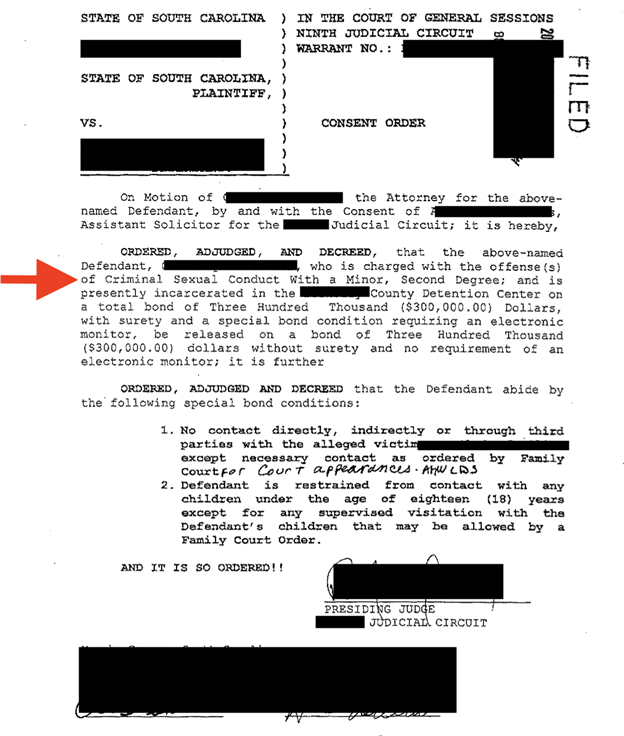
- Scanned.PDF files or images of court-ordered protection orders, divorce decrees, and other official legal documents;
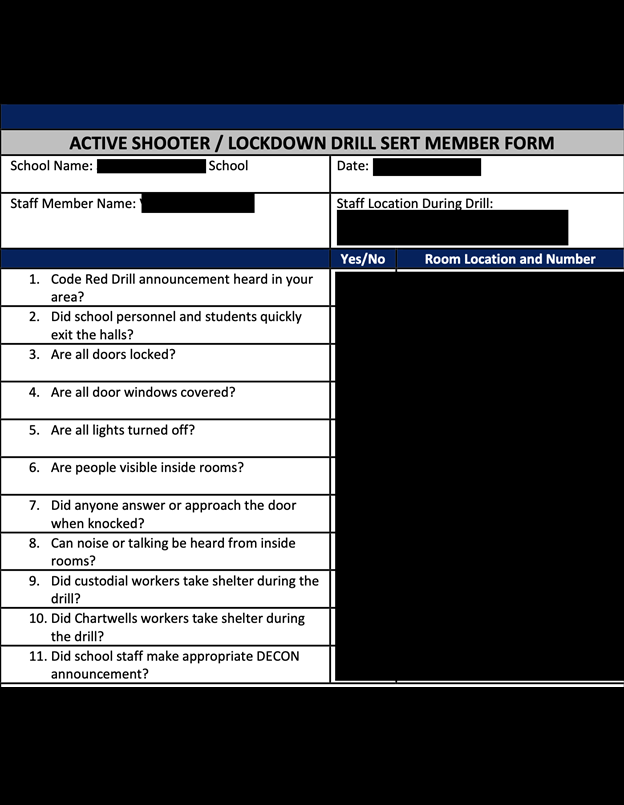
- Documents indicating monthly drills and detailing incidents or non-compliance of safety protocols as indicated by school staff.
All information was accessed in accordance with ethical security research practices. No sensitive information has been disclosed beyond the necessary scope of this report.
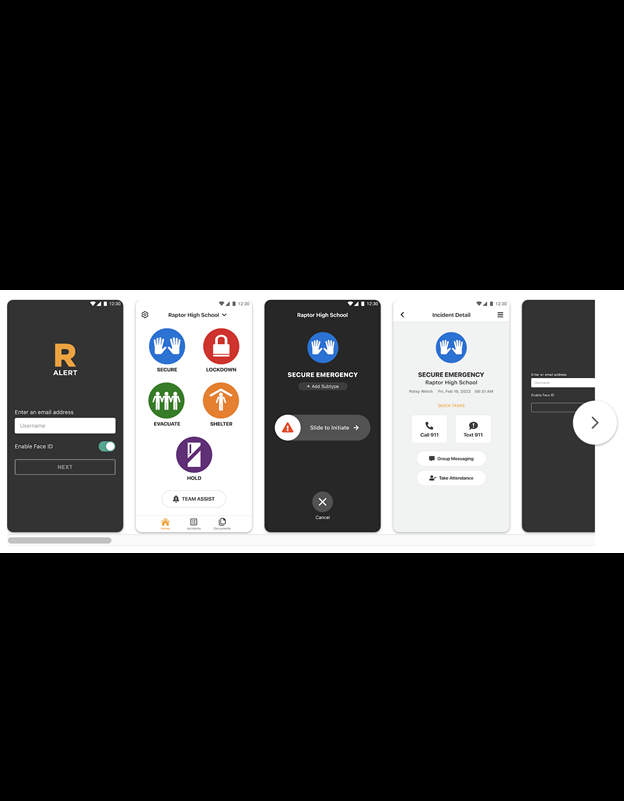
Raptor Technologies offers various solutions, such as a visitor management system that allows schools to track and screen visitors, volunteers, and contractors. The system ensures they are not listed on any sex offender registries or watchlists, and that they generally have no known risk factors associated with them. The company also offers emergency management tools that enable schools to identify and respond to emergencies, including attendance tracking, drills, and other systems for crisis management. Reporting features are also part of Raptor Technologies’ offerings, assisting schools with safety regulations and generating reports for audits or compliance purposes. This includes documentation for incidents that occur on school grounds.
According to their website: The Raptor integrated suite of school safety software and services along with the SchoolPass automated attendance and dismissal products covers the full spectrum of school safety. Raptor school safety software is reportedly used by more than 60,000+ schools worldwide, including those across 5,300+ U.S. districts. In 2023, there were an estimated 13,000+ school districts in the U.S., which means the exposure could potentially impact nearly 40% of American schools. When searching for information about schools that use the Raptor services, I found several publicly available documents that showed privacy agreements, pricing information, and government contractor information. One 2018 invoice publicly posted online indicated that Raptor’s service fees for a single school district amounted to approximately $17k per month.
How the records were broken down in the exposed storage repositories:
I identified what appeared to be internal information in all 3 exposed environments.
Production documents: 81,511 files
Production logs: 2,598,461 blobs / 779 GB
Staging documents: 7,900 files
Staging logs: 1,002,394 / 25 GB
Testing documents: 1,326 files
Testing logs: 332,409 / 23 GB
School Security, Privacy, and Serious Threats
School safety is a major concern in the United States, given the significant number of tragedies that have happened through the years. According to a report by the National Center for Education Statistics, from 2000 to 2021, there were 276 casualties (108 killed and 168 wounded) in active shooter incidents at elementary and secondary schools and 157 casualties (75 killed and 82 wounded) in active shooter incidents at postsecondary institutions. Having said that, I am not implying the schools affected by this exposure are at any imminent risk. This context serves to highlight the hypothetical dangers of exposed security details in school settings.
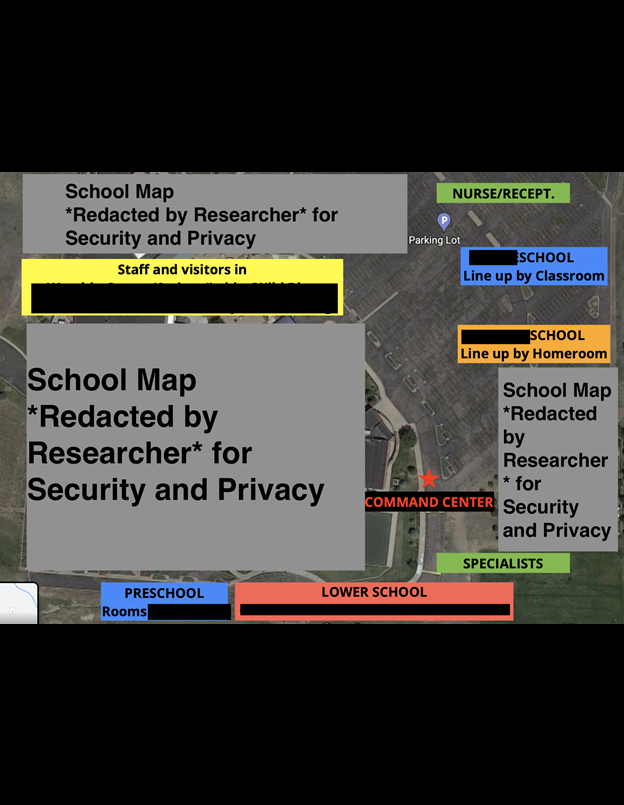
As a result of this data breach, I observed a large number of documents such as school maps, camera locations, security vulnerabilities, meeting points, and step-by-step actions of emergency response plans. The documents leaked online could potentially have real-world consequences if accessed by the wrong individuals. Although it is not an imminent risk, here are a few examples of how a criminal could hypothetically misuse the exposed information (if anyone else accessed it while it was open):
- Court Records: I saw numerous court documents, which included restraining or protection orders that provided details of abuse. I also saw documents indicating criminal sexual offenses with an underage person and details of the specific cases. Divorce and custody documents indicated the terms of the agreements and contained PII of parents and children including SSN numbers. The exposure of SSN numbers increases the risk of identity theft or financial crimes.
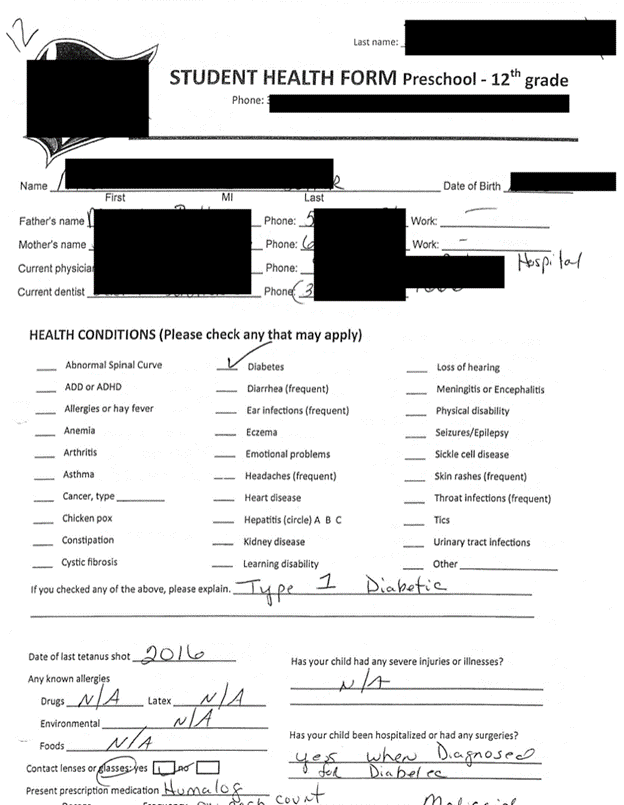
- Health Records: I also saw multiple student health forms that report known health conditions to school officials. Exposed health data could potentially compromise students’ privacy and confidentiality. Personal information contained in health reports, such as names, addresses, birth dates, or insurance details, could hypothetically be exploited by cybercriminals to commit various types of fraud. If sensitive health information becomes public, students could face stigmatization or discrimination from peers, educators, or potential employers based on their health conditions. Exposing student health reports online could be a potential violation of HIPAA privacy laws and other state regulations of ethical standards regarding patient confidentiality.
- Incident Reports and Safety Drill Summary Reports: The incident reports contained names of students and detailed their at-risk behavior or conflicts. Some of these descriptions could be highly embarrassing or stigmatize the student later in life if they were publicly disclosed. The safety drills indicated specific details such as safety vulnerabilities, security weaknesses, the time it took to complete the drill, and lessons learned. The drills are meant to streamline the process of being prepared for an emergency, and the summary reports should be accessed by authorized personnel only.
- School Maps: The database contained a massive amount of detailed school maps that identified classroom locations, room number, evacuation routes, meeting points, camera locations, security positions (if any), and many other potentially sensitive aspects of each school. Exposed maps can potentially provide critical information about the school layout, security protocols, and responses during emergency situations. This information could aid individuals with malicious intent by exploiting weaknesses or vulnerabilities identified in the exposed records.
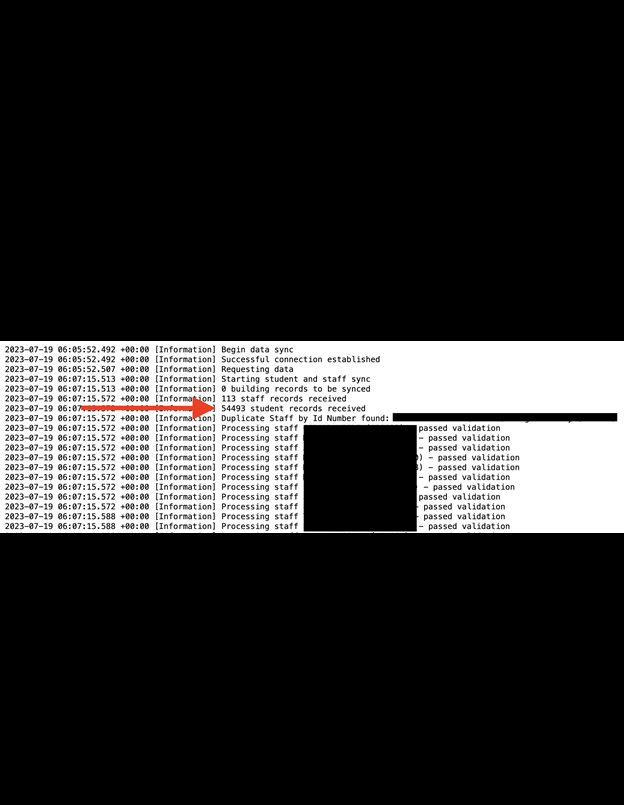
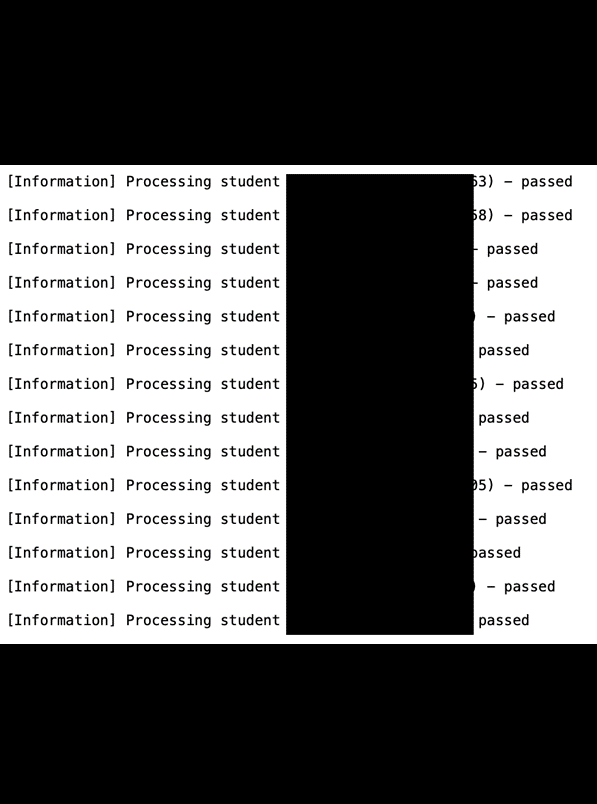
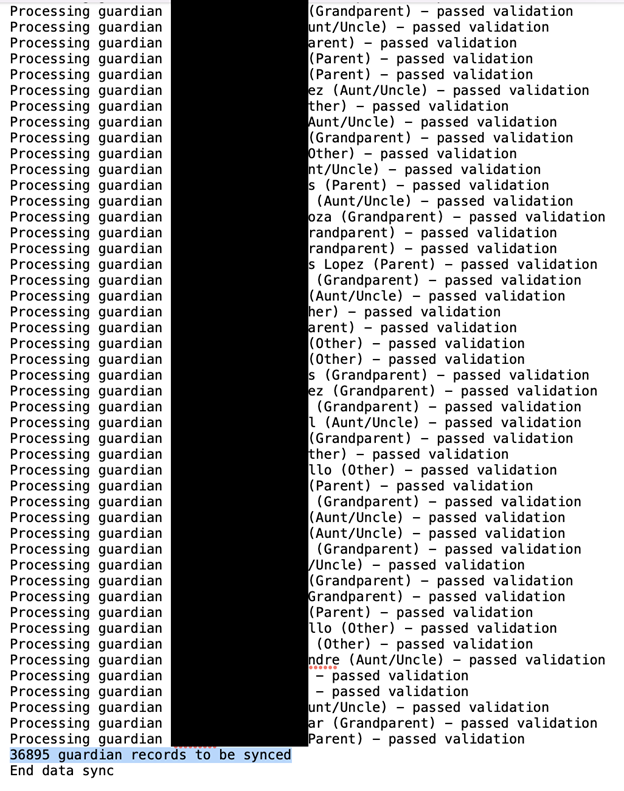
- Server or Application Logs: Applications communicate functions, actions, and errors with a server and generate logs that can contain detailed information. Logging records when publicly exposed can inadvertently disclose data, application functionality, or other internal communications that could potentially lead to additional security vulnerabilities. I saw a very large number of logs containing identifiable information such as student, teacher, or parent names. The logs also included student and staff ID numbers and other information that could pose additional privacy risks.
To clarify, this assessment is provided in the context of highlighting potential risks and does not imply any actual exploitation of the data. The intention is to encourage stronger security measures and awareness of the vulnerabilities that such data exposures can present. Given the numerous risks for educational institutions, it is crucial for schools to prioritize the security of potentially sensitive records related to emergency protocols, drills, or sensitive maps. I highly recommend that schools and companies who manage school data take proactive cybersecurity measures. This would include restricting access to such records, conducting regular security assessments, and encrypting sensitive information that is collected and stored.
As an ethical security researcher, I never download or extract the data I find. I only review a limited sample for verification and to indicate the potential risks. My intention is to enhance cybersecurity awareness. I imply no wrongdoing or neglect by Raptor Technologies. I also do not imply that there are any threats or risks to the schools, students, or staff. Our goal is to inform and raise awareness about potential vulnerabilities for the benefit of better data protection measures and security practices. As mentioned, it is unknown how long the database was exposed or if it was accessed by anyone else.



Please, comment on how to improve this article. Your feedback matters!