Popular Firefox Security Extensions Are Open to Reuse Attacks
- What is a Reuse Attack?
- How Would a Reuse Attack Occur?
- Are Reuse Attacks Common?
- Are Jetpack Add-ons Susceptible?
- What Security Extensions Are Vulnerable to Reuse Attacks?
- Did Any Security Extensions Pass the Vulnerability Test?
- What Are the Best Ways to Prevent Reuse Attacks?
- Is a Universal Fix Being Developed?
- Conclusion
New research has found some of the most popular Firefox add-ons, including powerful security extensions, are vulnerable to reuse attacks. This article details the situation. Share
At the Blackhat Asia Conference in early April 2016, researchers from Northeastern University and Boston University revealed nine of the top ten Firefox extensions are vulnerable to reuse attacks. Unfortunately, this includes a few of the most popular security extensions available in the Add-on catalog. In this article, we discuss how these attacks could happen, describe the compromised security extensions, and recommend some precautionary measures to lessen your exposure risk.
What is a Reuse Attack?
In this context, a reuse attack occurs when a malicious extension exploits the functions of a legitimate – yet vulnerable – extension to perform an attack on a user’s browser. The research group developed a static analyzer – named CrossFire – to identify reuse vulnerabilities in Firefox add-ons for both the Windows and Mac platforms, including:
- Network access
- File input/output
- Code execution
- Clipboard access
- Cookie store access
- Bookmarks access
- Password store access
- Preference access
- Event listener registration
Through these add-on faults, it is possible for an attacker to control your browser and perform malicious actions, such as:
- opening and displaying the contents of a URL in a new browser tab.
- sending an HTTP request to an attacker-specified URL.
- downloading a list of files without activating the Firefox download prompt.
- executing binary files to modify website content.
How Would a Reuse Attack Occur?
In order for such an attack to occur, a user must download the extension with the reuse vulnerability AND a malicious extension. The hidden code within the attacking add-on would then execute without the user’s knowledge.
“Attackers could write an extension that looks innocuous to anyone reviewing the plug-in,” researcher William Robertson said while presenting at the conference. “But once added to the Firefox browser, the benign looking extension could easily exploit a second Firefox extension to plant malware on the user’s computer.”
The attacks are made possible because legacy Firefox frameworks do not isolate add-on functions. Therefore, malicious add-on code can use API calls from legitimate add-ons to execute attacks while appearing to be harmless. They can also gather sensitive data contained in other add-ons because add-ons share Firefox’s Cross-Platform Communication Object Model (XPCOM).
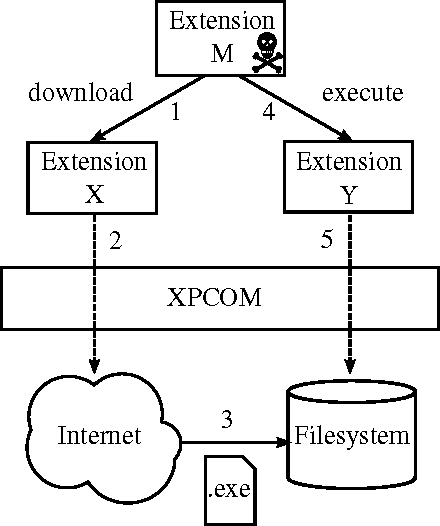 Credit: Buyukkayhan et al.
Credit: Buyukkayhan et al.
Are Reuse Attacks Common?
No. The researchers told vpnMentor that many other news outlets have blown the issue out of proportion.
“Most online articles we read about CrossFire blew the problem out of proportion, and made it out to look like all Firefox extensions are evil and should immediately be removed from the computer. Of course, that would not be a sensible reaction to the issue at hand.”
But with so many of the popular extensions possessing vulnerabilities, it does open the door for such attacks to happen.
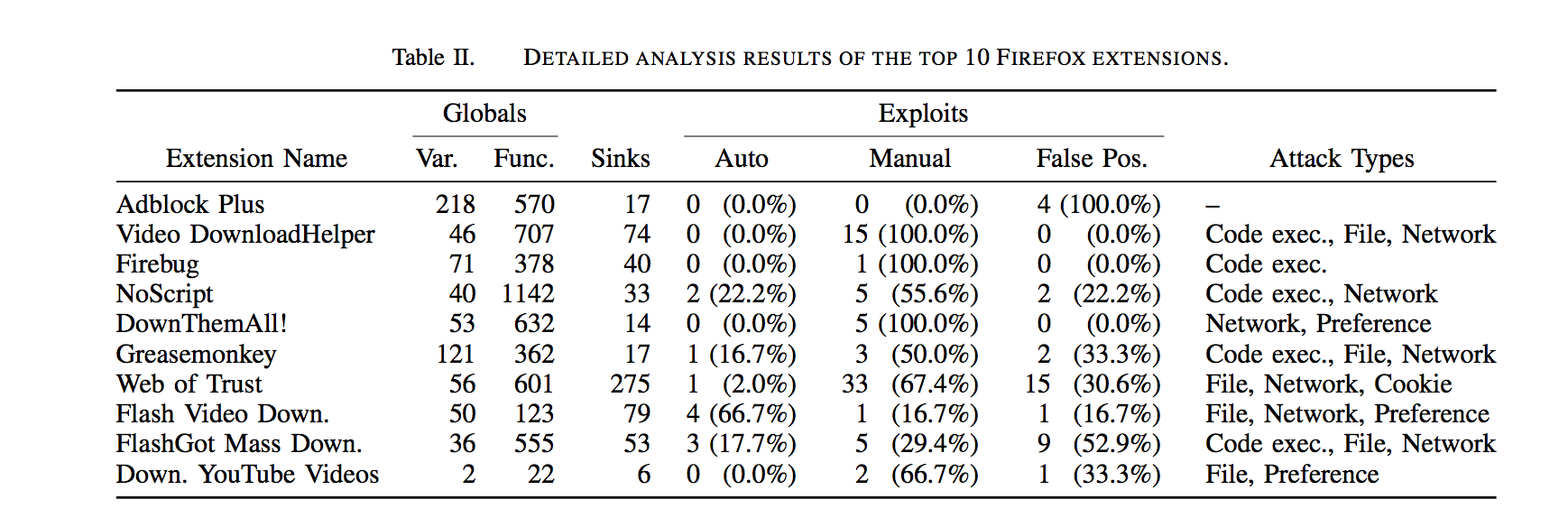 Credit: Buyukkayhan et al.
Credit: Buyukkayhan et al.
In fact, a main point of the research was to prove the inadequacies of current add-on vetting practices. To prove the point, the team uploaded a “malicious” extension and got it through Firefox’s highest level of review. This add-on, which they called ValidateThisWebsite, advertised an ability to analyze websites to determine if they met current code standards. Behind the façade, however, the extension actually paired with a legitimate extension to open a website of their choosing in a new tab. It was harmless, but it showed how an attack could occur.
Are Jetpack Add-ons Susceptible?
Yes. While the work primarily focused on the vulnerabilities in legacy Firefox extensions due to their popularity and prevalence, the team said extensions built through the current Jetpack/Add-on SDK platform are not immune to extension-reuse attacks.
What Security Extensions Are Vulnerable to Reuse Attacks?
The paper mentions two prominent security add-ons:
- NoScript:

This extension lets users choose the sites that can run JavaScript, Java, and other plugins. It currently has more than 2 million users. Update: NoScript’s author has recently responded to the CrossFire article, calling it “cheap research.”  Web of Trust:
Web of Trust:
A known worldwide website reputation and rating service that helps users make informed decisions about whether to trust a website or not when searching, shopping, or surfing online. It has more than 900,000 users.
In addition to these two security extensions, the researchers said KeeFox showed  vulnerabilities during the tests. This extension connects Firefox to KeePass Password Safe, the most popular open source (and free) password manager. Available to PC users only, it has been downloaded more than 59,000 times.
vulnerabilities during the tests. This extension connects Firefox to KeePass Password Safe, the most popular open source (and free) password manager. Available to PC users only, it has been downloaded more than 59,000 times.
Note: the researchers tested 323 random extensions along with the ones on the top-10 list. This random sample may include more security extensions than the ones listed here.
Did Any Security Extensions Pass the Vulnerability Test?
Yes. Adblock Plus came through without any reuse vulnerabilities. This is a positive development for the 20+ million users who have downloaded this extension.
What Are the Best Ways to Prevent Reuse Attacks?
The researchers emphasized that reuse attacks are only possible when a malicious add-on is downloaded and combined with at least one vulnerable add-on. Moreover, extensions that boast robust programming and receive regular updates are less susceptible to such vulnerabilities. As a result, vpnMentor provides the following recommendation:
- Using extensions with an active update record
- Only downloading extensions from known sources
- Keeping your browser up-to-date
- Managing your extension library and removing those you no longer use
According to the researchers, the key for short-term protection is vigilance. By informing users, developers, and Mozilla vetters about this issue, everyone can be on the lookout to blacklist malicious extensions.
“Naturally, we do not intend our work to be interpreted as an attack on the efforts of Firefox’s cadre of extension vetters, who have an important and difficult job…” they wrote in the paper. “Nevertheless, our experiments demonstrate that current [add-on vetting tools are] insufficient to handle this class of attack, and the techniques we propose can serve as a first step towards bolstering the vetting process to detect extension-reuse vulnerabilities.”
The team is also moving the CrossFire project to GitHub. When it is available, anyone can submit an extension as an input and see the code-reuse vulnerabilities inside it. Developers would then be able to issue updates to fix the faults.
Is a Universal Fix Being Developed?
Yes. The research sparked a quick response from Mozilla: “Because risks such as this one exist, we are evolving both our core product and our extensions platform to build in greater security.”
such as this one exist, we are evolving both our core product and our extensions platform to build in greater security.”
The company notes that add-ons written through the new WebExtensions platform (available in beta with Firefox 46) prevent the problem. Also, when Mozilla’s Electrolysis Project launches later this year, extensions will be isolated via sandboxing. This shift will prevent any malicious extension from communicating with a vulnerable one.
Conclusion
Since vulnerabilities extend to almost all of the most popular add-ons, the threat of reuse attacks cannot be taken lightly. It is important to stress, however, that vigilant add-on installation coupled with closer scrutiny by vetters and developers should prevent malicious add-ons from entering the Firefox library. So, be sure to download trusted security extensions that are kept up-to-date from now on, or at least until the Electrolysis project is implemented.



Please, comment on how to improve this article. Your feedback matters!