What Is VPN Tunneling — The Ultimate Guide For 2026
VPN tunneling securely extends a private network across the internet. It encrypts data at the source, sends it through a virtual tunnel, and decrypts it at the destination, protecting your information from unauthorized access and cyber threats.
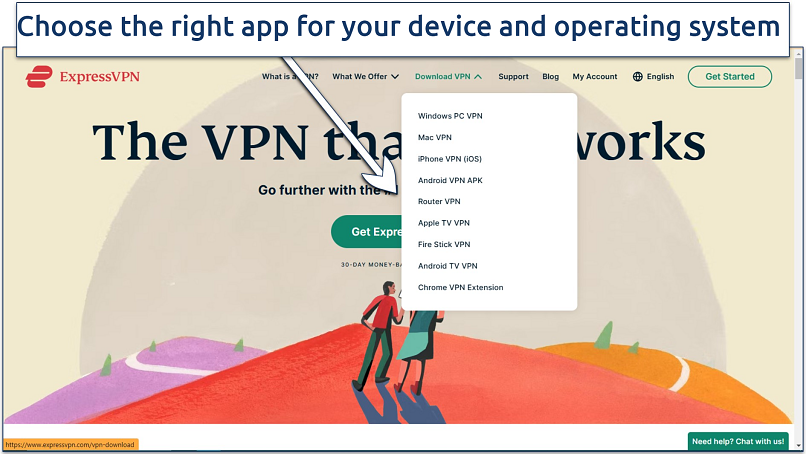
Downloading a VPN app is the simplest method to establish a VPN tunnel. However, if you want more control or customization, you can also set up VPN tunnels using open-source software like OpenVPN and WireGuard. Read on to find easy guides for setting up a VPN tunnel on any platform, from personal devices to enterprise solutions like Cisco and Palo Alto.
Quick Guide: How To Create a VPN Tunnel in 3 Easy Steps
- Get a VPN. The easiest way to create a VPN tunnel is to download a VPN app.
- Connect to a server. Pick a server from the location list, or let the VPN automatically choose the best one.
- Start browsing. Now your data is encrypted and routed through a safe VPN tunnel, so no one can track your online activities.
Pro Tip: Use a Reputable VPN For Safe & Easy VPN Tunneling
Creating a VPN tunnel manually can be complex and time-consuming. In addition to installing tools like OpenVPN or WireGuard, you need to rent a server and configure network settings. This process requires a deep understanding of network configurations and security protocols, which can be overwhelming for the average user.
A simpler and more reliable alternative is to use a commercial VPN. These services provide easy-to-use applications that allow for quick connections to global servers, robust security features like AES 256-bit encryption and IP/DNS leak protection, and customer support for troubleshooting. Additionally, using a VPN service is often more cost-effective than managing a personal server.
What Is VPN Tunneling & How Does It Work?
VPN tunneling refers to the method of transmitting data privately and securely over a public network, like the internet, by encapsulating the data packets in an encrypted tunnel. This tunnel effectively creates a secure "private" path through which data travels between a device and a VPN server, protecting it from interception or tampering by external parties. Here’s a detailed explanation of the process:
- Establishing the connection. When you initiate a VPN connection from your device (client) to the VPN server, the client first authenticates itself using credentials like a username/password, certificates, or other methods. The VPN server and client then agree on the encryption standards to be used, such as Advanced Encryption Standard (AES), and start encrypting the data.
- Encapsulation and encryption. Data packets are encapsulated, meaning they are wrapped inside another packet with an additional VPN-specific header. This encapsulated packet is then encrypted, ensuring that only the VPN server can decrypt it. The encapsulation also masks the true destination of the packets, preventing potential attackers from knowing which websites or services you're accessing.
- Transmission via protocols. The encapsulated data is transmitted through the tunnel using protocols like OpenVPN, IKEv2/IPSec, PPTP, or WireGuard. Each protocol has its way of managing encryption, authentication, and transmission, impacting speed and security. The VPN server then receives the encrypted packet and decrypts it, forwarding the original data packet to its intended destination.
- Return traffic. When the VPN server receives data back from the destination, it encapsulates and encrypts the response and sends it back through the tunnel to your client. Your device decrypts the packet, accessing the response data securely.
What Is VPN Split Tunneling?
Split tunneling is like having two separate roads for your internet traffic: one for secure data and another for regular browsing. With split tunneling, you can choose which apps or websites go through the encrypted tunnel of your VPN and which ones take the direct route.
These are the most common types of split tunneling:
- App-based split tunneling routes specific apps, like a corporate client, through the VPN while others bypass it.
- URL/domain-based tunneling sends traffic from selected websites through the VPN.
- Network-based split tunneling directs certain networks, like a corporate LAN, through the VPN while other networks use a regular internet connection.
By excluding non-sensitive traffic from the VPN, your encrypted connection isn't overloaded, improving speeds for essential VPN traffic. Additionally, routing only critical traffic through the VPN minimizes data usage and helps avoid overage charges on metered connections. You can also access local network devices (e.g., printers or NAS) while still being connected to the VPN for sensitive browsing.
Types of VPN Tunneling Protocols
VPN protocols are the underlying technologies that enable secure data transmission across different types of VPN tunnels. Each type of tunnel relies on specific protocols, which are crucial for maintaining data security, speed, and reliability in VPN communication.
Two main types of VPN tunnels are remote access and site-to-site. Remote access tunnels allow individual devices to connect to a remote server, granting secure access to private resources and the ability to browse the internet safely. In contrast, site-to-site tunnels are designed to connect entire networks, often used to securely link office locations for seamless resource sharing.
To choose the right protocol for your needs, consider factors like security, speed, device compatibility, and ease of use. If privacy is your main priority, use a protocol with strong encryption, like OpenVPN. For speed, especially with high-latency networks, I recommend WireGuard.
OpenVPN
OpenVPN is an open-source protocol known for its strong security and flexibility. It generally uses SSL/TLS for encryption, but it can also support AES, RSA, and other advanced ciphers. It’s widely compatible across various platforms, so you can use it to create a VPN tunnel on almost any device.
I recommend OpenVPN for both personal and corporate use. However, OpenVPN requires significant technical expertise to configure properly, especially for advanced features like routing policies, firewall traversal, and certificate management. Additionally, OpenVPN traffic can be blocked by some firewalls. In that case, I recommend using TCP port 443 to blend in with HTTPS traffic.
WireGuard
WireGuard is a relatively new VPN protocol designed to provide fast connections with minimal overhead. It was consistently faster than OpenVPN in my tests. The entire codebase is around 4,000 lines, much smaller than other protocols like OpenVPN (around 100,000 lines). This helps it run faster and reduces the potential for bugs and vulnerabilities.
If privacy is a priority, I recommend using WireGuard only in combination with a no-logs VPN. Due to its static IP configuration, WireGuard can make it easier to correlate your identity with your IP address. To minimize traceability while using WireGuard, VPN providers need to enforce strict no-logs policies and implement measures like dynamic IP addresses, frequent key rotation, and ephemeral key pairs.
IKEv2/IPSec
IKEv2/IPSec is known for its stability on mobile devices. It combines the Internet Key Exchange version 2 (IKEv2) and Internet Protocol Security (IPsec) to establish secure, encrypted connections. In my tests, it consistently maintained stable connections while switching between WiFi and mobile data.
Despite its strengths, IKEv2/IPsec can be susceptible to blocks by strict firewalls since it relies on specific UDP ports (500 and 4500), potentially restricting its use in certain network environments. Additionally, setting up IKEv2/IPsec can be complex, requiring significant technical knowledge, particularly in managing certificates and cryptographic keys.
L2TP/IPSec
L2TP/IPsec is a combination of two protocols often used together to provide secure VPN connections. Layer 2 Tunneling Protocol (L2TP) provides the tunneling mechanism, while Internet Protocol Security (IPSec) handles encryption. This protocol is commonly used for remote access VPNs. It’s built into many operating systems, including Windows, macOS, and Linux, making it easy to deploy without third-party software.
Due to its double encapsulation process and encryption overhead, it’s less efficient compared to newer protocols like OpenVPN and WireGuard. Configuring IPsec securely requires technical knowledge, plus it may be blocked by strict firewalls due to the reliance on specific ports.
SSTP
Secure Socket Tunneling Protocol (SSTP) was developed by Microsoft and is primarily used on Windows devices. SSTP utilizes SSL/TLS encryption to establish a secure connection between the user's device and the VPN server. It uses the same encryption mechanisms as HTTPS, enabling it to pass through most firewalls and proxy servers without special configuration.
The main SSTP's limitation is its restricted cross-platform compatibility. Additionally, it’s slower than OpenVPN and WireGuard. Although it can go undetected by most firewalls by using TCP port 443, strict network policies filtering encrypted traffic can still pose challenges.
PPTP
Point-to-Point Tunneling Protocol (PPTP) is one of the oldest VPN protocols and is known for its simplicity and ease of setup. However, PPTP is considered the least secure option due to its outdated encryption methods and vulnerability to cyber threats.
While it may offer faster connection speeds compared to other protocols, its weak encryption makes it susceptible to interception and data manipulation. PPTP is commonly used for basic internet browsing and legacy system compatibility but is not recommended for transmitting sensitive information or accessing secure networks.
Proprietary VPN Protocols
Besides the open-source and widely adopted VPN protocols, there are several VPN protocols developed by specific companies. These protocols often aim to enhance certain aspects of VPN performance, such as speed, security, or ease of use. Here’s an overview of some notable proprietary VPN protocols:
- ExpressVPN’s Lightway offers quick connection times and efficient switching between network types. It uses wolfSSL, known for its strong security credentials, and parts of its code are open-source for transparency.
- NordVPN’s NordLynx is based on WireGuard, but it incorporates a double NAT system to address privacy concerns associated with static IP addresses. It maintains WireGuard’s advantages in speed and simplicity while enhancing user privacy.
- Hotspot Shield’s Hydra VPN optimizes speed and reliability over long distances. It’s also known for its ability to work on networks with heavy restrictions and in heavily censored regions.
- VyprVPN’s Chameleon obfuscates VPN traffic to look like regular TLS-encrypted web traffic. This can be useful on networks where VPN use is restricted.
- Astrill VPN’s StealthVPN disguises VPN traffic to bypass deep packet inspections (DPI) and VPN blocks. It adds an extra layer of obfuscation and encryption, making it a reliable choice for users in highly restrictive environments.
How To Set Up a Secure VPN Tunnel
Creating a VPN tunnel can seem daunting if you're new to it. Here's a step-by-step guide to help you get started:
- Select a reliable VPN with fast worldwide servers, military-grade encryption, and strict privacy policies. Once you've chosen a provider, download and install the VPN software onto your device.
 I found ExpressVPN very easy to install on all my devices
I found ExpressVPN very easy to install on all my devices - Launch the application and log in using your credentials. From there, you'll typically have the option to choose a server location to connect to.
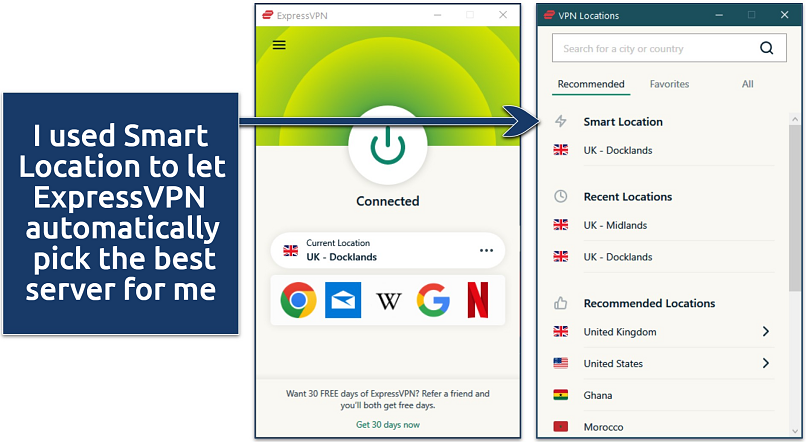 You can connect to servers in over 105 countries
You can connect to servers in over 105 countries - Connect to your chosen server to establish the VPN tunnel. This process encrypts your internet traffic and hides it from prying eyes. You can now browse the internet, access online services, and communicate with others knowing that your data is protected within the VPN tunnel.
You can also set up a VPN tunnel without using a commercial VPN app, but it involves additional steps. Here’s a simplified step-by-step guide:
- Decide on the VPN software or service. There are many options available, ranging from commercial products to open-source solutions. I recommend OpenVPN and WireGuard clients since they’re compatible with almost any device.
- Set up the VPN server. Your VPN tunnel will need an endpoint server. Depending on your needs and resources, this could be a dedicated server, a cloud server, or even a home server.
-
- Install the VPN software. For example, you would install OpenVPN server software if you're using OpenVPN.
- Configure the server settings. This includes setting up encryption, defining network settings, and configuring authentication methods.
- Configure authentication. Determine how users will authenticate with the VPN. Options include certificates, username/password, and multi-factor authentication.
- Set up encryption. Choose the encryption protocol and cipher. This is critical for protecting the data that passes through the VPN tunnel. I recommend AES-256, which is highly secure.
- Client setup. Install and configure VPN client software on the devices connecting to the VPN server. Input the server address, configure encryption settings, and load any necessary authentication credentials.
- Test the connection. Once everything is set up, test the VPN tunnel to see if it works correctly and securely. Ensure that client devices can connect to the VPN server and access resources as expected. Use tools like Wireshark to analyze traffic and check that data is properly encrypted.
- Maintenance and monitoring. Regularly update the VPN software and monitor VPN logs to address security issues or unauthorized access attempts.
How To Create a VPN Tunnel On Any Device
VPN Tunnelling for Personal Devices
The easiest way to create a VPN tunnel on your PC or phone is to download a VPN app for your operating system and connect to a server. However, if you want to avoid commercial providers, here’s how to set up a VPN tunnel manually:
1. Windows:
- Open VPN settings through the Control Panel or Settings, add a new VPN connection, and enter your server details, login credentials, and connection type.
- Connect to the VPN and verify the connection is secure.
2. macOS:
- Go to System Preferences > Network, add a new VPN connection, and configure it with the required server and authentication details.
- Test the connection for its security.
3. Android
- Go to Settings > Network & internet > Advanced > VPN.
- Tap on Add VPN at the top-right corner.
- Choose your preferred protocol (such as PPTP, L2TP/IPsec, or SSTP) and enter the necessary server, username, and password.
- Select the created VPN profile and tap Connect.
4. iOS:
- Go to Settings > General > VPN.
- Tap on Add VPN Configuration.
- Select the type (IKEv2, IPsec, or L2TP), then input your server's information and login credentials.
- After saving the configuration, turn the VPN on by toggling the switch next to its profile.
VPN Tunnelling for Enterprise Platforms
This is a general guide for setting up a VPN tunnel on several major enterprise platforms. The process can be adapted based on specific needs, which may require additional steps like integrating enterprise authentication systems or setting up more complex routing rules.
1. Amazon Web Services (AWS):
- Use AWS VPN services to create a secure and private connection between your network and your AWS environments.
- Set up an AWS Site-to-Site VPN by creating a Virtual Private Gateway attached to your VPC.
- Configure the VPN connection and customer gateway on your side of the connection.
2. Microsoft Azure:
- Use Azure VPN Gateway to establish secure, cross-premises connectivity.
- Create a Virtual Network Gateway in your Azure portal, set up a VPN gateway, and configure your local network gateway.
- Implement site-to-site or point-to-site VPN connections as per your organizational requirements.
3. Cisco ASA:
- Use Cisco’s Adaptive Security Device Manager (ASDM) to set up a VPN.
- Configure the ASA for SSL or IPsec VPN tunnels.
- Apply strong encryption standards and authentication methods for a secure connection.
4. FortiGate:
- Implement a VPN using FortiGate’s intuitive interface for setting up IPsec or SSL VPNs.
- Define the phase 1 and phase 2 parameters, and configure firewall policies.
- Monitor the VPN status through FortiGate’s dashboard to maintain security.
5. Check Point:
- Set up a VPN with Check Point’s Security Gateway software.
- Configure a VPN community involving your gateways and manage the shared secret and encryption settings.
- Use Check Point’s SmartDashboard to manage and monitor the VPN connection.
6. Palo Alto:
- Use Palo Alto Networks’ GlobalProtect software to create a VPN that extends the corporate security policy to all users, regardless of their location.
- Configure GlobalProtect gateways, portals, and agents to ensure secure connectivity and consistent policy enforcement.
- Regularly update and monitor the network to protect against threats.
Best VPNs for Safe & Easy VPN Tunneling in 2026
- ExpressVPN — Offers the fast and secure Lightway protocol to tunnel your connection to over 3,000 private servers.
- CyberGhost — Easy to set up and create a private VPN tunnel on your PC, phone, router, and more.
- Private Internet Access — Lets you set up a VPN tunnel on as many devices as you want, simultaneously.
FAQs
What is the difference between a VPN and a VPN tunnel?
A VPN tunnel is just a part of the overall VPN architecture. A VPN (Virtual Private Network) is a broad technology that enhances online privacy and security by encrypting your internet connection. A VPN tunnel refers to the encrypted link through which all your data passes. While all VPNs use tunnels to secure your data, the specific protocols used to create these tunnels can vary significantly, impacting security, speed, and compatibility.
Which VPN tunneling protocol is the best?
No single protocol is best for all scenarios. OpenVPN is widely recommended for its strong security and versatility across different types of networks. On the other hand, WireGuard is gaining popularity for its faster speeds and modern cryptographic techniques. You need to choose the best protocol for your specific needs regarding speed, security, and compatibility.
What is a site-to-site VPN tunnel?
A site-to-site VPN tunnel allows two or more secure networks to communicate as if they were on the same local network. This usually requires dedicated equipment like firewalls, routers, or dedicated VPN appliances from Cisco, Fortinet, or Palo Alto. Here’s how to create a VPN tunnel on any device. Typically used by businesses, this type of VPN tunnel helps securely connect international offices and enables resources to be shared safely across locations.
Can I create a VPN tunnel to my home network?
Yes, you can create a VPN tunnel to your home network. This is often done using consumer-friendly VPN software that you install on your home router or a network device configured as a VPN server. Installing a VPN to set up a VPN tunnel is easy on most devices. You can also do this by using open-source software like OpenVPN or WireGuard, but this requires technical expertise.
What is VPN tunneling in AWS?
VPN tunneling in AWS creates a secure and private communication link between your on-premises network and your AWS Virtual Private Cloud (VPC). This is useful for businesses that require secure access to cloud resources from various locations without exposure to internet threats. VPN tunneling works by encapsulating and encrypting traffic between these networks.
Can I set up a VPN tunnel for free?
Yes, by using open-source software like OpenVPN or WireGuard on your own server. However, while the software might be free, it may still incur costs related to running a server or using cloud services. Plus, setting up the VPN tunnel requires additional technical steps. Free commercial VPN services are also available but often have limitations such as bandwidth caps, fewer server locations, and weaker security practices compared to paid alternatives.
Conclusion
Creating a VPN tunnel can be as straightforward as downloading a VPN app or as detailed as manually setting one up using open-source software. The process requires choosing the right setup method depending on your technical expertise and specific security needs.
Selecting the correct protocol is crucial when establishing a VPN tunnel because it directly impacts your connections' security, speed, and reliability. Different protocols offer varying balances of these elements, so it’s essential to understand the strengths and limitations of each option to ensure your VPN tunnel meets your specific requirements for security and performance.
Your online activity may be visible to the sites you visit
Your IP Address:
216.73.217.61
Your Location:
US, Ohio, Columbus
Your Internet Provider:
Some sites might use these details for advertising, analytics, or tracking your online preferences.
To protect your data from the websites you visit, one of the most effective steps is to hide your IP address, which can reveal your location, identity, and browsing habits. Using a virtual private network (VPN) masks your real IP by routing your internet traffic through a secure server, making it appear as though you're browsing from a different location. A VPN also encrypts your connection, keeping your data safe from surveillance and unauthorized access.
I like it but network problem
I need good network 56.8



Please, comment on how to improve this article. Your feedback matters!