What is VPN Obfuscation? Best Way to Hide VPN Traffic in 2026
Advanced detection methods can identify your VPN connection. This lets websites (like Netflix) block your access, helps ad networks collect your data, and may lead to ISP throttling. However, the best obfuscated VPNs can avoid detection and enhance your privacy.
This article explains what VPN obfuscation is and shows how obfuscation camouflages your VPN traffic as regular internet activity. It can come in many forms, including specialized obfuscated VPN servers, stealth protocols, and proxies. I also clarify what sets this mode apart from encryption, double VPN, and Onion over VPN.
My team and I tested 50+ obfuscated VPNs to find the best services. They can get past the most sophisticated geoblocks and firewalls (for example, in restriction-heavy countries like the UAE). Their reliable security features protect your personal information and prevent ISPs from intentionally slowing down your speeds. Plus, you can torrent safely, thanks to P2P traffic support.
ExpressVPN is my favorite obfuscated VPN. It safeguards your data on all popular operating systems with a built-in obfuscation mode and military-grade encryption. Besides, it has a vast server network and impressive speeds to access international content from anywhere without interruptions. Best of all — you can try ExpressVPN with confidence (it’s backed by a trustworthy 30-day money-back guarantee*).
What Does “Obfuscated VPN” Mean?
An “obfuscated VPN” refers to a VPN that can disguise your encrypted traffic as a regular internet activity. Providers often use proprietary names for obfuscation, such as OpenVPN scramble, stealth technology/VPN/mode, obfsproxy servers, traffic obfuscation, or VPN cloaking technology.
Connecting to a VPN routes your data via an encrypted channel to protect your web activities and IP address. However, information from your device travels in data packets. Certain online services can recognize encryption patterns in these packets to block you (typically with a “proxy error” or “access denied” message). This may create extra security gaps for hackers and also let your ISP see what you do online.
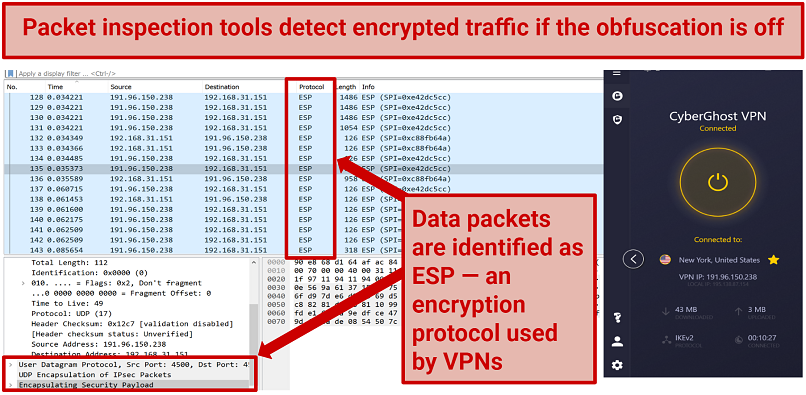 Without obfuscation, WireShark identifies encrypted ESP traffic used by CyberGhost
Without obfuscation, WireShark identifies encrypted ESP traffic used by CyberGhost
Also, OpenVPN (the default protocol for most VPNs) adds a distinctive signature that advanced deep packet inspection can detect. Obfuscation protocols replace metadata in encrypted data patterns to hide the traces of encryption. So, your VPN connection appears as typical online traffic (HTTPS, TCP, or UDP). VPN obfuscation typically assigns port number 443 to the data packet to further mask it as HTTPS traffic
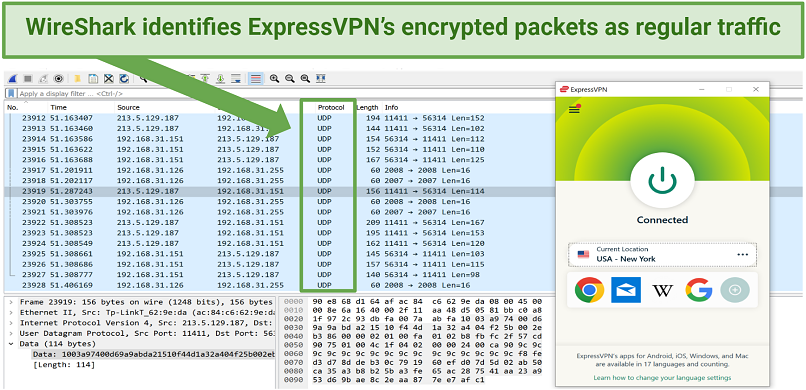 ExpressVPN's obfuscation mode makes VPN connection appear as standard internet traffic (UDP)
ExpressVPN's obfuscation mode makes VPN connection appear as standard internet traffic (UDP)
Even though it looks complicated, it’s very easy to use. VPN providers usually mark obfuscated servers so you can access them quickly. You might find obfuscation tech especially useful in countries where internet restrictions are often implemented during important political events or to censor sensitive content. ISPs and governments spy on users’ traffic and block certain websites.
Popular VPN Obfuscation Techniques
VPNs use obfuscated servers, protocols, and proprietary technologies to scramble your encoded traffic. Obfuscation techniques are mostly supported by 2 protocols — OpenVPN and WireGuard. Some of these methods are more effective than others at shielding your activities. So, let's focus on the most reliable VPN obfuscation techniques.
1. OpenVPN Scramble (XOR Scramble)
This technology changes the VPN signature in your data packets into a random code, masking the encrypted traffic. The tunneling protocols appear as HTTPS and UDP data, hiding the fact you're using a VPN. OpenVPN (XOR) Scramble is the default technology for most VPNs with OpenVPN tunneling protocol.
Unfortunately, some malware developers use XOR Scramble to hide malicious code in applications and executable files. Besides, its cipher is relatively simple and can be cracked, making XOR obfuscation not the most reliable tool for bypassing geoblocks. However, XOR and OpenVPN together give decent encryption that makes up for XOR’s weak security.
2. Shadowsocks (SOCKS5 Proxy)
The Shadowsocks proxy forwards your VPN traffic via a secure server to disguise it as a regular internet activity. This protocol is an open-source SOCKS5-based proxy project and works similarly to the SSH tunnel because it makes VPN-encrypted traffic look like HTTPS.
It masks your web traffic with AEAD cipher (SOCKS5 doesn’t encrypt data, that’s why these 2 proxies are used together). Shadowsocks encryption isn’t the strongest, but it works well when paired with OpenVPN.
This proxy also integrates with a WireGuard security protocol, an industry standard for premium VPNs. Shadowsocks was mainly created to circumvent China’s Great Firewall and other heavily regulated internet environments.
3. Obfsproxy
Obfuscate proxy (also known as obfsproxy or obscure proxy) protocol wraps your traffic in an extra encryption layer. This technique is an umbrella term for Pluggable Transports — traffic alteration mechanisms — such as obfs2, obfs3, obfs4, meek, and Scramblesuit. The last 3 are best for bypassing censorship, as obfs2 and obfs3 are outdated and easily detected by DPI.
Obfsproxy is primarily used for TOR browsers, but some VPNs utilize it to hide OpenVPN tunneling too. It was created in response to blocking Tor traffic in countries like China, Iran, Syria, and Russia. To make the obfuscation proxy work, it has to be configured on both the VPN app and the server.
Its encryption uses a handshake that has no recognizable byte patterns. However, the more advanced DPI technology can detect it and not let the encrypted traffic through. Obfsproxy is lightweight and uses less bandwidth, which can be useful but also makes it less secure.
4. OpenVPN Over SSL/TLS (Stunnel)
Stunnel is open-source software that disguises your VPN activity as HTTPS traffic. It adds a Secure Sockets Layer (SSL) or Transport Layer Security (TLS) encryption to your OpenVPN connection. They’re both commonly used by VPNs; however, SSL is quite outdated, whereas TLS 1.3 was updated in 2018.
Some providers can safeguard your data packets with an additional Secure Socket Shell (SSH) encryption — but it’s not as popular as SSL and is mainly used in business.
One thing to note is that Stunnel isn’t a good choice for streaming or torrenting, as it severely reduces your speeds. Plus, setting up Stunnel isn’t easy and must be done on the user's and the server’s end, so most VPN companies don’t provide it by default.
Why Do You Need an Obfuscated VPN?
Many VPNs don’t offer obfuscation technology. Besides, it may even be inconvenient for every online activity, as it might affect your speed. Still, there are some cases where you’d want to obfuscate your traffic with a reliable provider like ExpressVPN. It might reduce the speeds due to encryption, but it’s not enough to affect the quality of its performance.
1. Avoiding Deep Packet Inspections
VPNs divide your traffic into encrypted data packets (blocks). These blocks contain metadata — descriptive information that can reveal that you’re routing your traffic via an encrypted server. ISPs and network administrators for websites, schools, and offices often use deep packet inspection (DPI) to identify and block VPNs. Thankfully, services with reliable obfuscation avoid DPI methods, effectively hiding that you’re using a VPN.
2. Improving Online Privacy
A VPN obfuscation obscures your encryption traffic from ISPs, ad networks, and hackers. You basically hide that you’re safeguarding your web activities and IP address with a VPN. This adds another security layer against websites that want to sell your data and cyber criminals who are after your sensitive information. Many torrenters, journalists, activists, and politicians find this feature helpful.
3. Bypassing Firewalls in Restricted Environments
Obfuscated servers are especially useful for people who live in highly restrictive countries. ISPs in China, UAE, and Russia stop you from accessing websites and apps via a VPN. Some other restrictive countries include Iran, Egypt, Turkey, and Pakistan. They also attempt to block ports used by popular tunneling protocols like OpenVPN (port 1194).
But the best VPNs with obfuscation work against the toughest firewalls, including the Great Firewall of China and North Korea’s blocks. This lets you freely access international apps like WhatsApp, Facebook, Twitter, and YouTube, no matter where you are.
4. Accessing Streaming Platforms With Anti-VPN Blocks
Obfuscation techniques also help avoid VPN blocks used by popular streaming platforms, including Netflix US, Disney+, and Amazon Prime Video. For example, trying to watch Hulu with a VPN results in an error message. However, obfuscating your traffic allows you to watch films and shows from your accounts as normal.
Platforms like Hulu and BBC iPlayer are known for detecting and blocking IP addresses that belong to VPN providers. They use methods such as DPI, IP blacklisting, and port blocking.
5. Preventing ISP Throttling to Improve Speeds
ISPs may intentionally reduce your internet speeds if you frequently engage in high-bandwidth activities, like UHD streaming and online gaming. They also throttle P2P connections and tethering (mobile hotspot) traffic. Some providers automatically slow speeds for VPN traffic, knowing you may use it for data-heavy activity. However, an obfuscated VPN masks your traffic to let you avoid throttling.
Bear in mind that you can’t prevent throttling if you’ve exceeded your ISP’s monthly data limits or soft caps. However, a VPN prevents discrimination against particular types of internet traffic, like downloading large files and UHD live streaming.
Best VPNs With Obfuscation — Quick Picks (2026)
These VPNs performed well at hiding encrypted traffic from VPN blocks, firewalls, and deep packet inspection. I focused on services with reliable obfuscation methods, strong privacy features, and speeds that hold up well in everyday use.
1. ExpressVPN — Automatic Obfuscation Across Its Entire Network
ExpressVPN stands out because its obfuscation works automatically across the entire network whenever it detects deep packet inspection, so there’s no need to adjust settings or look for special servers. In my tests, it worked reliably on restrictive networks, and I was able to access blocked sites without issues.
It also combines this built-in obfuscation with Lightway and OpenVPN. Our speeds dropped by only 16% on a distant server, which kept browsing, streaming, gaming, and other high-bandwidth activity running smoothly.
2. Private Internet Access (PIA) — Shadowsocks Obfuscation With More Customization
Private Internet Access is a strong fit if you want more control over your obfuscation setup. Its Shadowsocks protocol helps disguise VPN traffic against deep packet inspection and can work well on restrictive networks, while the customizable encryption settings let you prioritize either stronger protection or better speeds.
It includes a Multi-Hop and Obfuscation feature that routes traffic through a proxy for another layer of masking, and I had no IP/DNS leaks while testing it. From our experience, PIA averaged 69 Mbps, which was fast enough for streaming, gaming, and other data-heavy activities.
3. NordVPN — Obfuscated Servers to Help Avoid ISP Throttling
NordVPN is a good match if your main goal is hiding VPN traffic from your ISP to reduce the chance of throttling. Its obfuscated servers mask your connection while routing traffic through strong encryption and protocols like OpenVPN and NordLynx, which makes it harder for providers to analyze your activity and slow certain types of traffic. This was especially useful during testing on mobile hotspots, where throttling is more common. Our speeds dropped by 32% on US servers with obfuscation enabled, but the slowdown wasn’t noticeable in everyday use.
Quick Comparison Table: Obfuscated VPN Features
Quick Guide: How to Obfuscate Traffic With a VPN in 3 Easy Steps
- Get a reliable VPN. I suggest ExpressVPN for its built-in obfuscation that protects your data, and vast network of servers to avoid geoblocks. You can try ExpressVPN risk-free (it’s backed by a 30-day money-back guarantee).
- Connect to a server. The obfuscation is usually enabled by default, so connect to a server in a location that matches the content you want. For example, choose a US server to get a US IP address.
- Start browsing. You’re all set to browse, stream, and play games while obfuscating your VPN activities.
FAQs
What is an obfuscated server, and how does it work?
Obfuscated VPN servers mask your encrypted connection as ordinary internet traffic (HTTPS, TCP, or UDP). It’s not just servers — some of the best VPNs use different obfuscation techniques to safeguard your data. Popular solutions include OpenVPN Scramble, Shadowsocks, Obfsproxy, and Stunnel. Additionally, there are several other less common obfuscation technologies:
- V2Ray/VMess — This protocol routes your VPN traffic via a third-party server to avoid restricted environments.
- SoftEther — OpenVPN-supported technology that bypasses firewalls with an Ethernet over an HTTPS tunnel.
- Secure Socket Tunnel Protocol — This protocol is used for secure data transmission in some Windows-native applications.
- SSTP — It was created to replace the outdated and vulnerable PPTP protocol, and it’s supported on Windows, Linux, Android, and a variety of routers. SSTP is closed-source and has dubious links with the NSA, established by Edward Snowden in 2013.
By replacing identifiable VPN metadata in data packets with random data, these technologies make it challenging to detect a VPN connection. As a result, users can effectively circumvent ISP throttling and stringent VPN blocks, providing a more reliable method for accessing online content without restrictions.
Can VPN obfuscation technologies help me access Netflix US?
VPN obfuscation can help bypass strict firewalls used by sites like Netflix US, but encryption and global network are more important. Actually, the best VPNs with military-grade encryption and worldwide servers can reliably avoid geoblocks even without obfuscation. The obfuscation does help, though. It wraps your VPN traffic in an extra security layer, increasing your chances of getting around advanced firewalls.
What is the difference between obfuscation, encryption, and double VPN?
Obfuscation isn’t the same as encryption or double VPN, but it complements these technologies. Using an obfuscation mode hides encryption patterns, so no one can detect your VPN traffic. As for the encryption, it transports your data packets via secure VPN servers to safeguard your actual location and browsing information. Double VPN (Multi-Hop) routes your data via two servers for additional protection.
What to do if the VPN obfuscation doesn't work?
Select another server or change your connection settings to solve your issues. You may need to switch your provider — a VPN with advanced obfuscation can bypass geoblocks in a few clicks. If this doesn’t help, here are the solutions that might:
- Change to another tunneling protocol or obfuscation mode (if possible) in the VPN settings.
- Try activating and deactivating the kill switch and other security features to see if you can establish a connection.
- Update or reinstall your VPN app, as your version may be outdated or incorrectly installed (especially if you installed it using Android APK).
- Disable your antivirus software (firewall); if this works, add the VPN to the list of trusted apps.
- Configure your router and network settings (you may need to contact your ISP for extra information).
- Check your connection for IP/DNS leaks — the obfuscation might not work if your VPN exposes your data.
- Connect to a server nearest to your physical location. For example, try the servers in Hong Kong or Taiwan if you're in China.
- Contact the VPN customer support service for quick troubleshooting.
Do obfuscated servers slow down my internet connection speed?
Yes — obfuscation technology uses algorithms to disguise metadata in encrypted data blocks to hide traces of VPN activity. This can increase the data travel time between servers. However, the best VPNs have top-grade protocols that conceal your encrypted traffic with minimal speed losses. Obfuscation can even improve your internet connection by preventing your ISPs from throttling your connection for certain activities.
Is it safe to use obfuscated VPN servers?
Yes, but obfuscation doesn’t guarantee 100% online privacy — you still need a VPN with advanced security features. Simply connect to an obfuscated VPN with AES 256-bit encryption to safeguard your data. You can further enhance your security with a reliable kill switch and a strict no-logs policy. Plus, using a VPN with obfuscation is legal almost everywhere, as long as you do it for lawful purposes.
Can I make my traffic obfuscated with free VPNs?
Unlikely — most free VPNs lack high-grade obfuscation techniques and security features. It’s much more reliable to get a premium VPN with a trustworthy money-back guarantee. Free services tend to have small networks that can’t bypass popular streaming platforms and subpar speeds for streaming. Besides, these VPNs can sell your data to advertisers, as they usually don’t have strict no-logs policies.
Free proxies and Tor browsers are bad alternatives, too. A proxy service doesn’t encrypt your traffic, leaving you vulnerable. Tor protects your traffic at the cost of speeds, so you can’t reliably stream or torrent. Some providers substitute obfuscation for Onion over VPN — it encrypts your data and routes it through the Tor network. However, this mode makes your speed painfully slow and can still expose your VPN signature.
Summary
The best obfuscated VPNs can deal with refined geo-restrictions and ISP throttling. They also wrap your encrypted traffic in another level of security, letting you browse, stream, and torrent in privacy, even from restrictive locations.
ExpressVPN is my top obfuscation VPN. The obfuscated mode is available on its entire network to effortlessly access your favorite apps and streaming platforms anywhere. Plus, its military-grade encryption, tunneling protocols (Lightway and OpenVPN), and strict no-logs policy provide robust online protection. You can try ExpressVPN without risk since it’s backed by a 30-day refund policy.
Your online activity may be visible to the sites you visit
Your IP Address:
216.73.217.24
Your Location:
US, Ohio, Columbus
Your Internet Provider:
Some sites might use these details for advertising, analytics, or tracking your online preferences.
To protect your data from the websites you visit, one of the most effective steps is to hide your IP address, which can reveal your location, identity, and browsing habits. Using a virtual private network (VPN) masks your real IP by routing your internet traffic through a secure server, making it appear as though you're browsing from a different location. A VPN also encrypts your connection, keeping your data safe from surveillance and unauthorized access.



Please, comment on how to improve this article. Your feedback matters!