CompTIA Security+ Guide to Network Security Fundamentals- Free Chapter Included!
Dr. Mark Ciampa is an Associate Professor of Information Systems in the Gordon Ford College of Business at Western Kentucky University. Prior to this he was an Associate Professor and served as the Director of Academic Computing at Volunteer State Community College in Gallatin, Tennessee for 20 years. Mark has worked in the IT industry as a computer consultant for the U.S. Postal Service, the Tennessee Municipal Technical Advisory Service, and the University of Tennessee. He has published 17 articles in peer-reviewed journals and is also the author of over 23 technology textbooks, including Security+ Guide to Network Security Fundamentals 5ed, CWNA Guide to Wireless LANs 2ed, Guide to Wireless Communications, Security Awareness: Applying Practical Security In Your World 5ed, and Networking BASICS. Dr. Ciampa holds a PhD in technology management with a specialization in digital communication systems from Indiana State University and also has certifications in Security+ and HIT. We've had the pleasure of chatting with Mr. Ciampa about his work, followed by a sneak preview to his latest book CompTIA Security+ Guide to Network Security Fundamentals. Share
What's inspired you to write CompTIA Security+ Guide to Network Security Fundamentals?
My general interest in security came through my work in teaching network security for many years. At one time security was called "network security" because it was envisioned that we should use the computer network to create an impenetrable perimeter as a barrier to attacks. In other words, the network was seen as the moat around protecting the castle. Of course, it soon became evident that such an approach would not work, since there are so many different avenues (such as USB flash drives and email attachments, to name just a few) through which attacks may enter. I had written several college-level books for my long-time publisher, Cengage Learning, since 1995. Cengage Learning followed up on that interest I had and asked me if I would be interested in writing a book on security in 2003. I did, and since then I have written nine books on security and am currently working on another book to be published Fall 2017. My motivation for writing the book was to help students learn about security in order to both protect themselves as well as serve as secure IT professionals.
What new knowledge did you gain whilst writing this book?
The knowledge that I gained has been very significant. Writing a book requires you to dig deeply into the subject so that you can effectively communicate the material to the readers. At one level security may be likened to the field of health care: there are a wide number of diseases that can attack the human body. When communicating that information, are we speaking to seasoned medical professionals who have studied and worked to seek cures, often devoting themselves to a single disease? Or are we speaking to a broader audience that may not have that background but still need to know how to live a healthy lifestyle so as to minimize the impact of specific diseases? I have a strong interest in helping the latter audience, which I think is often overlooked in instruction about security. Although I have written books that deal with very specific areas of security for a more professional audience, this book is more general to help readers understand the basis of security in terms of the various attacks and required defenses. This book maps to the current CompTIA Security+ SY0-401 exam objectives and can be used to help prepare for taking the Security+ certification exam.
The book can be purchased on the publisher's web site, or through Amazon
Below is the first chapter of CompTIA Security+ Guide To Network Security Fundamentals
Chpater 1: Introduction to Security- Today’s Attacks and Defenses
What is the deadliest security attack that you can imagine? A virus that erases all the contents of a hard disk drive? A malicious program that locks up files until the user pays a “ransom” to have them released? The theft of millions of user passwords?
Although each of these attacks can be extremely harmful, the deadliest attacks could result in the actual death of the victim. These deadly attacks are directed against medical devices that sick patients rely upon to live.
An insulin pump is a small medical device worn by diabetics that administers insulin as an alternative to multiple daily injections with an insulin syringe or pen. One security researcher, himself a diabetic, demonstrated at a security conference a wireless attack on an insulin ump that could secretly change the delivery dosage of insulin to the patient.1 By scanning for wireless devices in a public space up to 300 feet (91 meters), this researcher could locate vulnerable insulin pumps made by a specific medical device manufacturer, and then force these devices to dispense fatal insulin doses—just as an attacker could.2 Another security researcher “hacked” into a defibrillator used to stabilize heartbeats and reprogrammed it, and also disabled its power save mode so the battery ran down in hours instead of years. It is estimated that there are more than 3 million pacemakers and 1.7 million Implantable Cardioverter Defibrillators (ICDs) in use today that are vulnerable to these types of wireless attacks.3 This threat was so real that a former vice president of the U.S. had his defibrillator removed and replaced with one that lacked capabilities that an attacker might exploit.
Other serious concerns regarding medical devices have also surfaced. A vendor that manufactures medical ventilators maintains a website from which software updates to the ventilators can be downloaded and installed. A security researcher discovered that the website was infected with 48 viruses that could be installed on a user’s computer, and 20 of the 347 pages of this website contained infections.4 And spreading medical device malware is not limited to infecting websites. Today devices that perform medical imaging like computerized tomography (CT) scans automatically send scan results as PDF file attachments to email accounts. This email capability can be highly vulnerable and make an ideal entry point for an attacker to install medical device malware.
The U.S. Department of Homeland Security (DHS) has issued a report entitled “Attack Surface: Healthcare and Public Health Sector.” This report says these attacks are “now becoming a major concern…. In a world in which communication networks and medical devices can dictate life or death, these systems, if compromised, pose a significant threat to the public and private sector.”5 The national Information Security and Privacy Advisory Board (ISPAB) said that the United States Computer Emergency Readiness Team (US-CERT) should create “defined reporting categories for medical device cybersecurity incidents.”6
Until recently the Food and Drug Administration (FDA), which regulates the design and manufacture of medical devices, did not have any regulations regarding how these devices should be configured and connected to a network. Now the FDA is taking notice. It has issued an “FDA Safety Communication” document recommending that medical device manufacturers and health care facilities should “take steps to assure that appropriate safeguards are in place to reduce the risk of failure due to cyberattack, which could be initiated by the introduction of malware into the medical equipment or unauthorized access to configuration settings in medical devices and hospital networks.” And to make sure that these recommendations are followed, the FDA has stated that for any medical devices that do not “appropriately address” security risks, the FDA “might consider” withholding its approval of the device.7
This position requires an understanding of configuration and operation but not necessarily technical mastery. Security administrator. The security administrator has both technical knowledge and managerial skills. A security administrator manages daily operations of security
technology, and may analyze and design security solutions within a specific entity as well as identifying users’ needs.
Security technician. This position is generally an entry-level position for a person who has the necessary technical skills. Technicians provide technical support to configure security hardware, implement security software, and diagnose and troubleshoot problems.
Individuals in these positions are not the only ones responsible for security. It is the job of every employee—both IT and non-IT—to know and practice basic security defenses.
Employment trends indicate that employees with certifications in security are in high demand. As attacks continue to escalate, the need for trained and certified security personnel also increases. Unlike some IT positions, security is rarely offshored or outsourced: because security is such a critical element in an organization, security positions generally remain within the organization. In addition, security jobs typically do not involve “on-the-job training” where employees can learn as they go; the risk is simply too great. IT employers want and
pay a premium for certified security personnel.
The job outlook for security professionals is exceptionally strong. According to the U.S. Bureau of Labor Statistics (BLS) “Occupational
Outlook Handbook,” the job outlook for information security analysts through the end of the decade is expected to grow by 22 percent,
faster than the average growth rate. The increase in employment will add 65,700 positions to the more than 300,000 already in this field.8
To verify security competency, a vast majority of organizations use the Computing Technology Industry Association (CompTIA) Security+ certification. Of the more than 250 security certifications currently available, Security+ is one of the most widely recognized security certifications and has become the security foundation for today’s IT professionals.
It is internationally recognized as validating a foundation level of security skills and knowledge. The CompTIA Security+ certification is a vendor-neutral credential that requires passing the current certification exam SY0-401. A successful candidate has the knowledge and skills
required to identify risks and participate in risk mitigation activities; provide infrastructure, application, operational and information security; apply security controls to maintain confidentiality, integrity, and availability; identify appropriate technologies and products; troubleshoot security events and incidents; and operate with an awareness of applicable policies, laws, and regulations.
The CompTIA Security+ certification is aimed at an IT security professional who has a recommended background of a minimum of two years’ experience in IT administration with a focus on security, has technical information security experience on a daily basis, and possesses a broad knowledge of security concerns and implementation.
This chapter introduces the network security fundamentals that form the basis of the Security+ certification. It begins by examining the current challenges in computer security and why it is so difficult to achieve. It then defines information security in detail and explores why it is important. Finally, the chapter looks at who is responsible for these attacks and what are the fundamental attacks and defenses.
Challenges of Securing Information
A silver bullet refers to a precise and infallible remedy that rapidly and effortlessly resolves a major issue. For a layperson, it might appear that there should be a silver bullet for computer security, like integrating superior hardware or employing a more secure software program. However, in truth, there's no singular or simplistic solution for safeguarding devices to protect the data they house. The complexities of this reality can be demonstrated by examining the variety of cyber attacks users confront currently and the challenges in mounting defenses against these attacks.
Today’s Security Attacks
Despite the fact that information security continues to rank as the number one concern of IT managers and tens of billions of dollars are spent annually on computer security, the number of successful attacks continues to increase. Recent attacks include the following:
- Attackers penetrated the network of a credit card processing company that handles prepaid debit cards. They then manipulated the balances and limits on just five prepaid cards. These cards were then distributed to “cell managers” in different countries who were responsible for using the cards to withdraw cash from automated teller machines (ATMs). In one month almost $5 million was fraudulently withdrawn from ATM machines around the world in 5700 transactions. A cell in New York City was responsible for withdrawing $400,000 in 750 fraudulent transactions at 140 ATM locations in the city in only 2.5 hours. A similar attack manipulated account balances and withdrawal limits on 12 more cards that were distributed to cell members to withdraw an additional $40 million from ATM machines around the world. The New York City cell withdrew $2.4 million in 3000 ATM transactions in just 10 hours.
- Marc G. was in the kitchen when he began to hear strange sounds coming from the nursery of his two-year-old daughter Allyson. Marc and his wife entered the nursery and heard a stranger’s voice calling out Allyson’s name, cursing at her and calling her vile names. The parents discovered that the voice was coming from the electronic baby monitor in Allyson’s room that contained a camera, microphone, and speaker connected to their home Wi-Fi network. Because they did not have any security set on their wireless network, the attacker had been able to take control of the baby monitor from an unknown remote location. When Marc and his wife stepped in front of the camera, the attacker turned his verbal attack toward them. They quickly unplugged the device. The parents surmised that the attacker knew their daughter’s name because he saw “Allyson” spelled out on the wall in her room. This situation is not unique: it is estimated that there are more than 100,000 wireless cameras that can easily be exploited because they have virtually no security.
- The Twitter account of the Associated Press (AP) was broken into and a fictitious tweet was posted claiming there were “two explosions in the White House and [the U.S. President] is injured.” Even though the tweet was only visible for a matter of minutes before it was removed, because of this fictitious tweet the Dow Jones industrial average dropped immediately (it recovered later in the day). AP now joins the ranks of many large corporate brands—including CBS television websites 60 Minutes and 48 Hours, the New York Times, the Wall Street Journal, the Washington Post, Burger King, and Jeep—who have been victims of recent Twitter break-ins. And these attacks will likely only escalate as social media sites become more frequently used for distributing information. The U.S. Securities and Exchange Commission (SEC) recently said that it would allow public companies to disclose corporate information on social media sites like Twitter.
- Malware called Ploutus that infects a bank’s ATM demonstrates how vulnerable these cash-dispensing machines can be. The infection begins with the attacker inserting a CD-ROM disc that contains malware into the ATM computer’s disc drive (on some ATMs the disc drive is actually accessible from the outside). The malware then installs a “backdoor” so that the attackers can manipulate the machine via the ATM’s keypad. After entering the code 123456789ABCDEFG to access the malware, instructions can be given through entering a series of numbers on the keypad. The latest version of Ploutus malware can be instructed to print the entire ATM configuration (if a USB printer is connected to an exposed USB port), display information about the money currently available in the ATM, and instruct the machine to dispense money.9
- A serial server is a device that connects to a remote system through the Internet (technically it provides remote access to serial ports over TCP/IP) so that administrators can access the remote system as if it were connected to the local network. The remote systems that use serial servers include not only traffic stoplight systems but also a wide variety of industrial control applications, point of sale (POS) terminals in retail stores, energy management devices, fueling stations, hospital medical device monitors, and oil and gas monitoring stations. Serial servers are highly vulnerable and can thus expose the remote systems that are connected to them. It is
estimated that there are 114,000 serial servers accessible from the Internet that expose more than 13,000 serial ports and their connected remote systems.10 - Indonesia has now overtaken China as the number one source of attack traffic. About 38 percent of all attacks now come from Indonesia. China has fallen to second place with about 33 percent of all attacks coming from there, while the U.S. is at a distant third place (6.9 percent but down from 8.3 percent). These three countries, combined with seven others, now account for 89 percent of all attack traffic. The rapid ascent of Indonesia to the top of the list is even more significant given that previously this country accounted for only 1 percent of all attack traffic. The surge is evidently related to the increase in the average Internet connection speed in Indonesia: broadband access has increased 125 percent in one year.11
- A security researcher demonstrated how easy it would be to manipulate any aircraft in the sky. This is because the computers that control today’s airplanes are not protected from attacks. The researcher, who both works in IT and is a trained commercial pilot,
demonstrated how an attacker can easily upload bogus flight plans and give detailed commands to these systems. In one demonstration he showed how to manipulate the steering of a Boeing jet while the aircraft was in autopilot mode. He could also take
control of most of the airplane’s systems so that, for example, he could send panic throughout the aircraft cabin by making the oxygen masks drop down. And he could even make the plane crash by setting it on a collision course with another airplane in the vicinity.12 - Researchers have found similar weaknesses in the systems used by ocean vessels. Ships share information about their current position and course with other ships in the area as well as with offshore installations like harbors, and this information can be tracked via the Internet. Because this software is not protected, an attacker could easily modify every detail of the vessel, such as its position, course, speed, name, and status number. Attackers could also send fake alerts that a person has fallen overboard, that a storm is approaching, or that a collision is imminent with another ship. They could also create a fictitious “ghost” ship that does not even exist or change information about the type of ship or cargo it is carrying (in their test the researchers took a ship that was physically located on the Mississippi River in Missouri but made it appear as if the ship were on a lake in Dallas). An attacker could also alter a system that
identifies buoys and lighthouses, causing ships to wreck.13 - Web browsers typically send User Agent Strings to a web server that identify such items as the browser type and the underlying operating system so that the web server can respond appropriately (for example, the web server can send different formats of the requested webpage based on what the browser can display). Attackers can use a web browser to send the User Agent String “xmlset_roodkcableoj28840ybtide” to specific wireless routers in order to access the router’s settings through a “backdoor” and bypass all security. As an interesting note, it appears that this backdoor was actually implanted by the manufacturer: if the second half of the User Agent String is reversed and the number in the middle is removed, it reads edit by joel backdoor.14
- Online sites like Craigslist and eBay are very popular for buyers and sellers of items from electronics to automobiles. However, the Federal Bureau of Investigation (FBI) is warning buyers to beware. Attackers masquerading as legitimate sellers frequently advertise items at “too-good-to-be-true” prices to entice a large number of victims; however, the attackers do not post photos of the item for sale but instead offer to send a photo as an email attachment or as a link upon request. Increasingly these attachments contain malware: when the recipients open the attachment their computers become infected. Potential buyers are encouraged to not ask to be sent a photo but instead request that the original posting be modified so that it includes a photo.
- A computer cluster for cracking passwords was configured that comprised five servers and 25 graphics cards that can generate 350 billion password guesses (candidates) per second. This cluster could break any eight-character password in a maximum of 5.5 hours.
- Apple has admitted that Mac computers on its own campus became infected. Apple employees visited an infected website for software developers and their computers then became infected. The infection was successful because Apple’s own computers were not updated with the latest security patches. Once the attack was identified by Apple it released a tool that patched 30 vulnerabilities and defects and disinfected malware on Apple Mac computers.
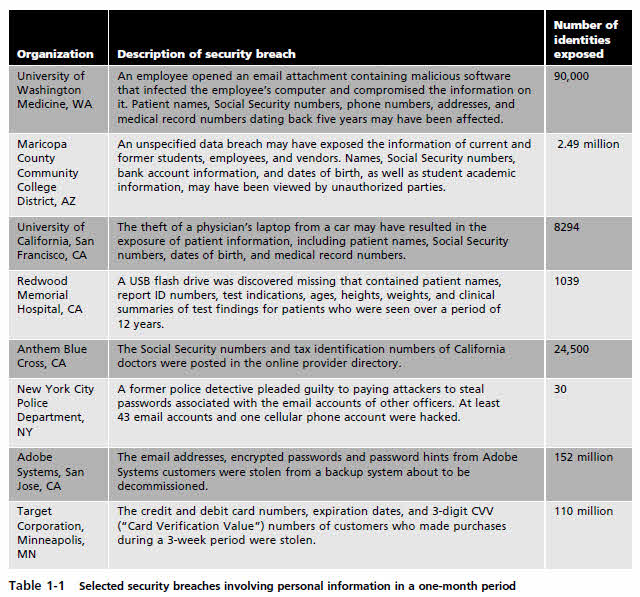
The number of security breaches that have exposed users’ digital data to attackers continues to rise. From 2005 through early 2014 over 666 million electronic data records in the U.S. had been breached, exposing to attackers a range of personal electronic data, such as address, Social Security numbers, health records, and credit card numbers.15 Table 1-1 lists some of the major security breaches that occurred during a one-month period, according to the Privacy Rights Clearinghouse.
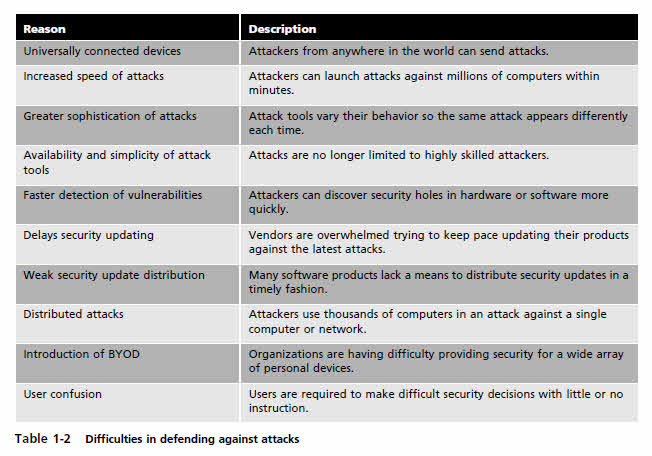
Difficulties in Defending Against Attacks
The challenge of keeping computers secure has never been greater, not only because of the number of attacks but also because of the difficulties faced in defending against these attacks. These difficulties include the following:
- Universally connected devices. It is unthinkable today for any technology device— desktop computer, tablet, laptop, or smartphone—not to be connected to the Internet. Although this provides enormous benefits, it also makes it easy for an attacker halfway around world to silently launch an attack against a connected device.
- Increased speed of attacks. With modern tools at their disposal, attackers can quickly scan millions of devices to find weaknesses and launch attacks with unprecedented speed. Most attack tools initiate new attacks without any human participation, thus increasing the speed at which systems are attacked.
- Greater sophistication of attacks. Attacks are becoming more complex, making it more difficult to detect and defend against them. Attackers today use common Internet protocols and applications to perform attacks, making it more difficult to distinguish an attack from legitimate traffic. Other attack tools vary their behavior so the same attack appears differently each time, further complicating detection.
- Availability and simplicity of attack tools. Whereas in the past an attacker needed to have an extensive technical knowledge of networks and computers as well as the ability to write a program to generate the attack, that is no longer the case. Today’s software attack tools do not require any sophisticated knowledge on the part of the attacker. In fact, many of the tools, such as the Kali Linux interface shown in Figure 1-1, have a graphical user interface (GUI) that allows the user to easily select options from a menu. These tools are freely available or can be purchased from other attackers at a surprisingly low cost.
- Faster detection of vulnerabilities. Weakness in hardware and software can be more quickly uncovered and exploited with new software tools and techniques.
- Delays in security updating. Hardware and software vendors are overwhelmed trying to keep pace with updating their products against attacks. One antivirus software security institute receives more than 200,000 submissions of potential malware each day.16 At this rate the antivirus vendors would have to create and distribute updates every few seconds to keep users fully protected. This delay in distributing security updates adds to the difficulties in defending against attacks.
- Weak security update distribution. While vendors of mainstream products, such as Microsoft, Apple, and Adobe, have a system for notifying users of security updates for many of their products and distributing them on a regular basis, few other software vendors have invested in these costly distribution systems. Users are generally unaware that a security update even exists for a product because there is no reliable means for the vendor to alert the user. Also, these vendors often do not create small security updates that “patch” the existing software, but instead they fix the problem in an entirely new version of the software—and then require the user to pay for the updated version that contains the patch. Attackers today are focusing more on uncovering and exploiting vulnerabilities in these products.
- Vendors of smartphone operating systems are particularly wellknown for not providing security updates on a timely basis, if at all.
Most vendors and wireless carriers do not attempt to provide users with significant updates (such as from version 5.6 to 5.7), instead
hoping that users will purchase an entirely new smartphone—and service contract—to have the latest and most secure device. - Distributed attacks. Attackers can use hundreds of thousands of computers under their control in an attack against a single server or network. This “many against one” approach makes it virtually impossible to stop an attack by identifying and blocking a single source.
- Introduction of BYOD. Until recently IT departments were “autocratic”: they established technology standards for users by specifying which devices could be purchased by a department for its employees and would refuse to allow unauthorized personal devices to be connected to the corporate networks. However, coinciding with the introduction of modern tablet computers in 2010 and the widespread usage of smartphones, users began to pressure IT departments to allow them to use and connect their personal devices to the company’s network (called BYOD or bring your own device). This trend of allowing employees to use their own personal devices to connect to the corporate network has made it difficult for IT departments to provide adequate security for an almost endless array of devices that they do not own.
- User confusion. Increasingly, users are called upon to make difficult security decisions regarding their computer systems, sometimes with little or no information to guide them. It is not uncommon for a user to be asked security questions such as Do you want to
view only the content that was delivered securely? or Is it safe to quarantine this attachment? or Do you want to install this add-on? With little or no direction, users are inclined to provide answers to questions without understanding the security risks.
Table 1-2 summarizes the reasons why it is difficult to defend against today’s attacks.



Please, comment on how to improve this article. Your feedback matters!