DOM-XSS Bug Affecting Tinder, Shopify, Yelp, and More
Our team of security researchers was researching dating apps client-side security, and one of the main focus targets was Tinder.
After initial reconnaissance steps were done, a Tinder domain with multiple client-side security issues was found - meaning hackers could have access to users' profiles and details.
Immediately after finding these vulnerabilities, we contacted Tinder via their responsible disclosure program and started working with them.
We learned that the vulnerable endpoint isn’t owned by Tinder, but by branch.io, an attribution platform used by many big corporations around the globe. The Tinder security team helped us get in touch with them, and accordingly, they’ve put out a timely patch.
Upon further investigation, it was discovered that numerous prominent websites, such as Shopify, Yelp, Western Union, and Imgur, were inadvertently exposing the vulnerable endpoint in their code and domains. Consequently, there is a potential risk for up to 685 million users.
While the flaw has already been fixed, if you have recently used Tinder or any of the other affected sites, we recommend checking to make sure your account hasn't been compromised. It's a good idea to change your password ASAP.
Details:
DOM-based XSS vulnerability, also known as “type-0 XSS” is a class of cross-site scripting vulnerability that appears within the DOM. It is a type of attack wherein the attack payload is executed as a result of modifying the DOM environment in the victim’s browser, more so in a dynamic environment. In DOM-based XSS, the HTML source code and response of the attack will be exactly the same. This means the malicious payload cannot be found in the response, making it extremely difficult for browser-built in XSS mitigation features like Chrome’s XSS Auditor to perform.
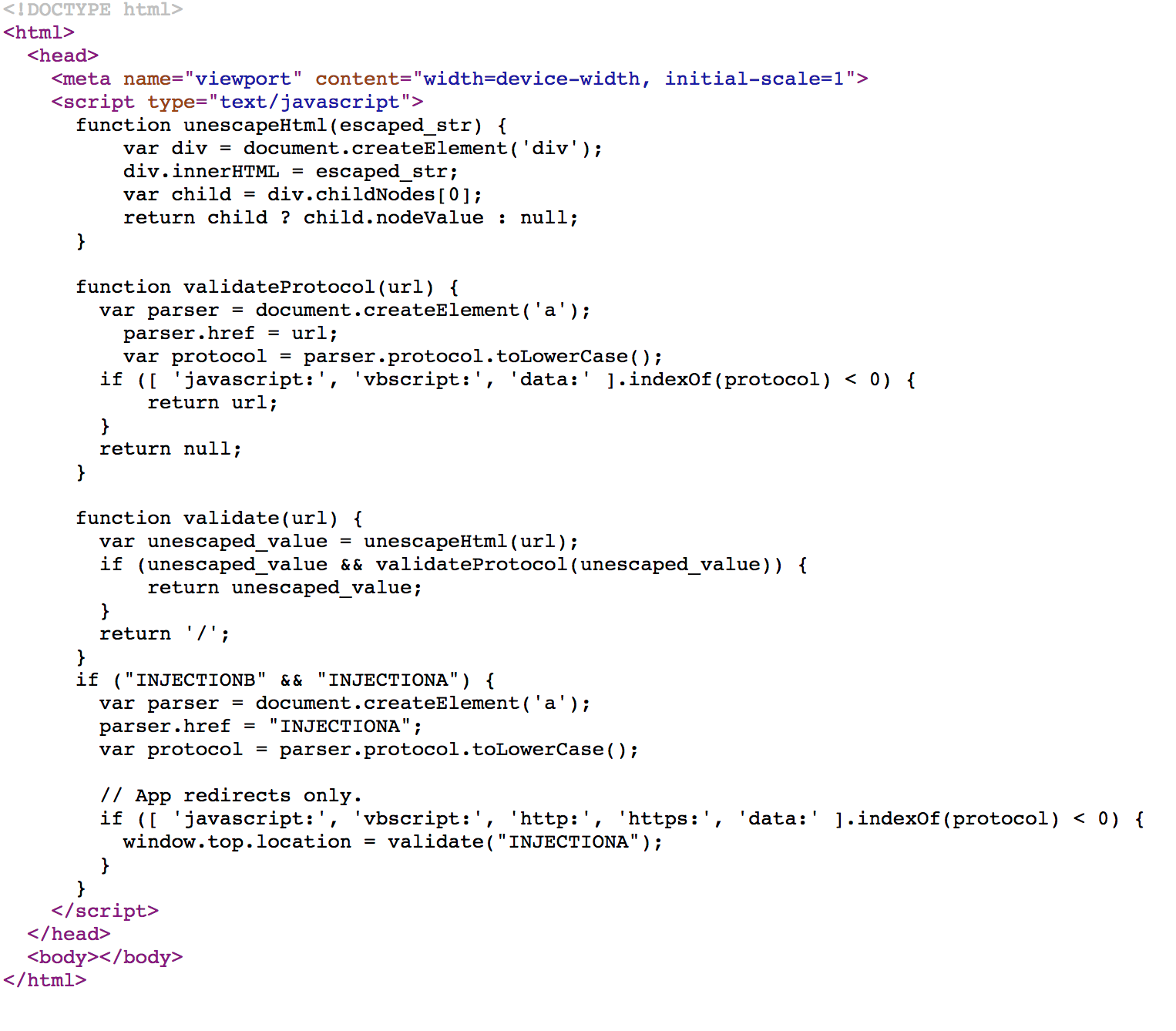
Can you spot the vulnerabilities?
The fact that the vulnerability is DPM based and branch.io still isn't using CSP made these vulnerabilities easy to exploit in any browser we like.
This meant that by modifying redirect strategy to a specially crafted payload to manipulate the DOM.
1. DOM XSS
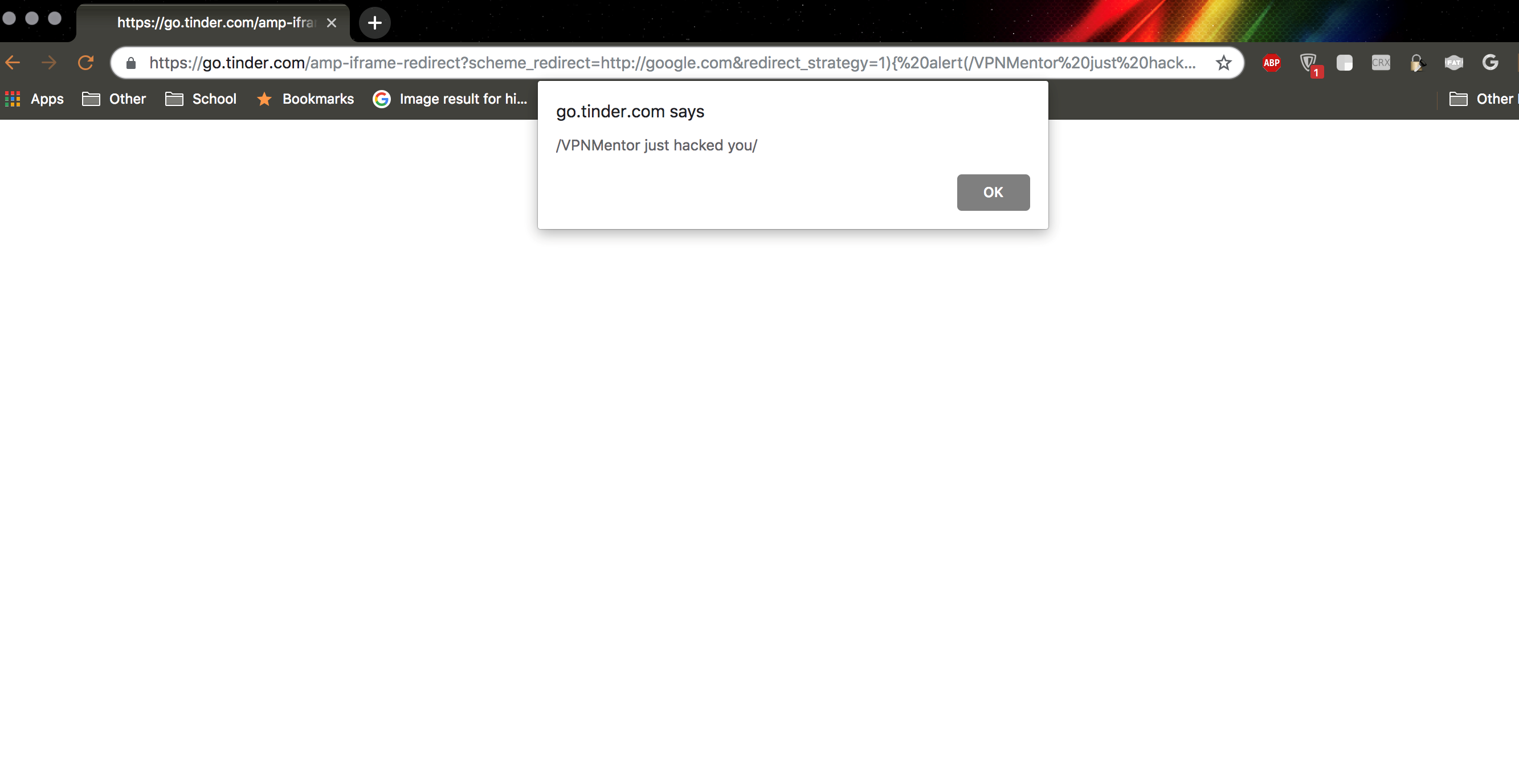
For example, our initial finding was the endpoint https://go.tinder.com/amp-iframe-redirect was prone to multiple vulnerabilities (scheme_redirect & redirect_strategy GET parameters control the div content).
redirect_strategy is “INJECTIONA” and scheme_redirect is “INJECTIONB” from the code above.
This meant that by modifying redirect_strategy to a dom-xss payload, it was possible to execute client-side code in the context of a Tinder domain in any browser:
https://go.tinder.com/amp-iframe-redirect?scheme_redirect=http://google.com&redirect_strategy=1)%7B%0Aalert(1)%3B//
will render in the DOM as:
if (1){ alert(1);// && "INJECTIONA") {
var parser = document.createElement('a');
parser.href = "INJECTIONA";
var protocol = parser.protocol.toLowerCase();
2. validateProtocol() and validate() Bypass
Also notice how validateProtocol() uses indexOf to check the schemes - the indexOf() method returns the position of the first occurrence of a specified value in a string. This method returns -1 if the value to search for never occurs. However, it can be tricked by using javascript://%0aalert(0)//good.com/https:// -- both the validate functions can be bypassed because indexOf will find “https://“
var parser = document.createElement('a');
parser.href = url;
var protocol = parser.protocol.toLowerCase();
if ((‘javascript:', 'vbscript:', ‘data:').indexOf(protocol) < 0) {return url;
}
....
return null;
if (['http:', 'https:'].indexOf(protocol) < 0) {
window.top.location = validate("http://google.com");
}
So, how did this bug affect more than Tinder?
go.tinder.com is an alias for custom.bnc.lt, a Branch.io resource. And many other companies have their alias pointing to it.
To name a few websites affected by this vulnerability: RobinHood, Shopify, Canva, Yelp, Western Union, Letgo, Cuvva, imgur, Lookout, fair.com and more.
Thanks to the fast response we got from Branch’s security team, this vulnerability has now been fixed for everyone’s domains.
Other recent studies of ours:
Critical RCE Vulnerability Found in Over a Million GPON Home Routers



Please, comment on how to improve this article. Your feedback matters!