Firmitas' Device-Side Security is Changing the Face of OT Systems
- What's Unique Firmitas' Product?
- What's the difference between device-side and network-based protection?
- How has connectivity changed our industries?
- How protected are smart cities today?
- If you were the minister of cyber security, what would you do to improve your country's protection against cyber threats?
Firmitas cyber solutions is a technology company founded in 2014 by a team of industry veterans with extensive experience both in the technology and business worlds. They specialize in providing adaptable operational cyber-defense solutions that protect connected systems, and specifically mission-critical systems. In this interview, Gil Keini talks about the difference between device-based and network-based security, and explains why your devices are more important than your data. Share
What's Unique Firmitas' Product?
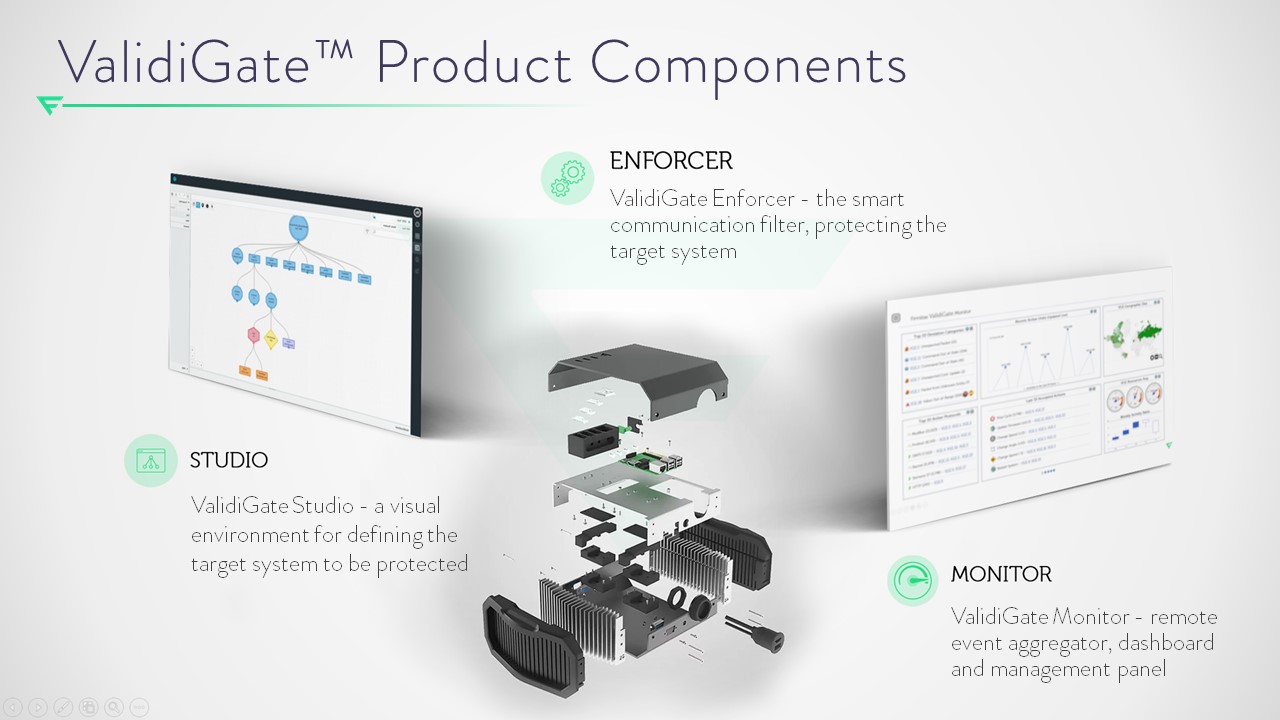
Firmitas developed a product to protect mission critical systems and operational systems from attacks coming over the communication interfaces. Our approach is unique because we rely on whitelist-based technology to enforce the correct behavior of each system component.
Instead of looking for anomalies, attacks, or attack patterns, our solution is an edge device- side solution, designed to be deployed in-line to enforce the correct and expected communications, in and out of the system. By doing so, we help enforce the safe and secure operational envelope of OT (Operational Technology) systems.
What's the difference between device-side and network-based protection?
Network-based security solutions assume a specific network structure and topology, and are usually deployed on the network boundary. The problem with networks today, is that they are completely perforated, even OT networks. There's more than one entry and exit point. With devices having Wi-Fi, Bluetooth and other communication capabilities, anyone can communicate to your devices and reconfigure or reprogram them, sometimes with the knowledge of the operator, and sometimes without.
Specifically in OT networks, the structure of the network allows communication between devices without going through the headquarters. Any network-based security solution may miss communication between devices. So once compromised, devices can attack other devices within the network without being detected. Therefore we believe that protection should be per device or per system. Additionally, each system behaves in a different way and has its own unique characteristics. This requires tailored protection, based on specific device configuration and deployment considerations.
How has connectivity changed our industries?
Two decades ago, networks were characterized by their relative simplicity, featuring a clearly defined boundary with a singular point of entry and exit. Furthermore, the production of devices was limited to a smaller number of manufacturers, and obtaining information about these devices was more challenging.
The rise of connectivity allowed more devices to connect to other devices and other networks. Simultaneously, information about these devices became accessible to almost anyone. Unintentionally, this trend lowered the threshold for attacks. Since today every device is smart and connected, compromising one device can act as an entry point and a pivot to attack other devices within the network.
Furthermore, devices today are significantly more complex. The manufacturing and supply chain is a very complex network of vendors incorporating many hardware and software components. Assuming that a device is secured when it's out of the box, is not a valid assumption these days.
With the connectivity of all these devices we get the benefit of improved visibility, data collection, and efficiency. The downside is that we expose all of these devices to malicious attacks.OT systems are devices that were designed to perform a specific task affecting the physical world.
Medical devices, industrial IOT, connected cars, smart roads, smart cities, building management systems, they all have one thing in common, that once attacked, it's not just information which is at risk, it's people's lives. An attack can cause physical damage to people and even death. Protecting OT systems is more critical to civilization than just data. Data protection technologies are more advanced, but sadly there are very few companies that attempt to protect OT networks and devices. Currently, most solutions are focused on detection and device management. We're the only ones who are actually targeting protection by prevention - protecting the end device from malicious usage & hacking.
How protected are smart cities today?
To the best of my knowledge, protection of smart cities is based mostly on technologies and methodologies derived and suitable for protecting enterprise and data networks. Are these methodologies providing benefit? Maybe, but they do not provide enough protection against process-based attacks and specific attacks targeting operational-systems. These systems are way too exposed.
If you were the minister of cyber security, what would you do to improve your country's protection against cyber threats?
At nation level, I would probably provide incentives to companies, factories and cities to deploy technological solutions for cyber protection, preferably local companies and startups but not only. Understanding that by providing incentives, like tax benefits for large organizations to protect their own systems, we are actually reducing the money paid to the government, but the benefits on the national level, are significantly higher. A robust national infrastructure will provide significant business value, raise the revenue of these companies and thus increase the amount of taxes they pay. Any attack on these organizations is an attack on the employees, their families, their communities, and everyone else related. It's easier to see when you talk about a smart city, as these are citizens of the nation we are talking about. But essentially, any money that is directed towards protecting our critical infrastructure is going to return the investment very quickly. The government should encourage companies to test new technologies, even if some solutions are overlapping in capabilities. Investing in security is significantly cheaper than handling the damage of an attack, and this is without even mentioning the damage to the environment and to people's health. From a business perspective it's a much better solution.



Please, comment on how to improve this article. Your feedback matters!