Report - Gearbest Hack: Hundreds of Thousands Affected Daily by Huge Data Breach
Led by Noam Rotem, a well-known white hat hacker and activist, VPNMentor’s research team discovered a major security breach in Gearbest.
With hundreds of thousands of sales every day, Gearbest is a highly successful Chinese e-commerce company.
The site sells a range of electronics and appliances, as well as clothing, accessories, and homeware. While it sells some internationally-known brands like OnePlus, most are smaller Chinese brands.
It ships to more than 250 countries and territories across the globe, and ranks in the top 100 websites in almost 30% of these regions. Gearbest has subdomains in 18 languages, generating global appeal.
Gearbest is owned by Chinese conglomerate, Globalegrow. The parent company operates several internationally successful sites, including Zaful, Rosegal, and DressLily. In 2015, their sales hit $550 million; 2017 saw the company celebrate a $1.48 billion turnover.
The company’s runaway success is a triumph for Gearbest and its sister companies. However, it’s not such great news for the sites’ customers.
vpnMentor can exclusively reveal that Gearbest’s database is completely unsecured – as are those belonging to its sister companies.
Gearbest Data Breach
Our hackers could access different parts of Gearbest’s database, including:
- Orders database
Data includes products purchased; shipping address and postcode; customer name; email address; phone number - Payments and invoices database
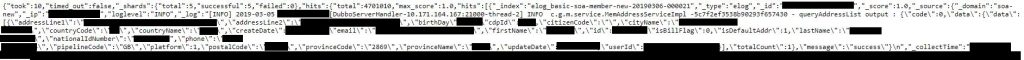
Data includes order number; payment type; payment information; email address; name; IP address - Members database
Data includes name; address; date of birth; phone number; email address; IP address; national ID and passport information; account passwords
We accessed these databases in March 2019, and discovered 1.5+ million records.
Gearbest’s database isn’t just unsecured. It’s also providing potentially malicious agents with a constantly-updated supply of fresh data.
Security Issues
Aside from our ability to access complete sets of personally identifiable information for millions of users, Gearbest’s data breach raises several other very serious issues.
User Privacy
Gearbest’s Privacy Policy states that while they do collect user information, it is with the focused purpose of serving their customers.
The privacy policy also specifies that while users are responsible for their own passwords, they encrypt sensitive information and employ external verification software to protect customers.
The data viewed as a result of this hack reveals this to be untrue. We saw lots of sensitive information - including email addresses and passwords - that was completely unencrypted.
Additionally, the database contains large amounts of personally identifiable information that is not required when completing the duties of an e-commerce store. For example, a shipping address is crucial to fulfilling orders. An IP address is not.
This is particularly worrying given the current trend towards a more open and honest internet. Services providers across multiple industries, strive to increase transparency for their customers. Gearbest's shady practices do the opposite.
Gearbest seems to infringe on their own privacy policy. However, this isn’t the most significant risk to user privacy here.
User Safety
An open database filled with personal information can compromise users’ safety online. The records we saw show full sets of unencrypted data, including email addresses and passwords.
(It’s worth noting that some email addresses contained some hashing. We don’t know if this was intentional and should have appeared everywhere, or if some of their data corrupted. Our hackers believe that it was a partially-implemented security measure that is simply not doing its job.)
The screenshot below shows snippets from two set of user data we harvested from the database.
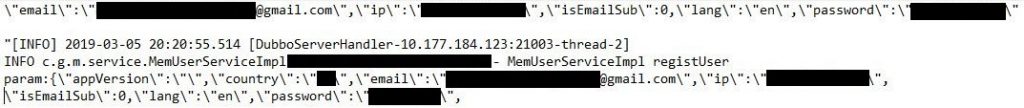 We were able to log in to these two Gearbest accounts and operate them as if we were the users. We could view current and past orders, accumulated Gearbest points, and change the account password and details.
We were able to log in to these two Gearbest accounts and operate them as if we were the users. We could view current and past orders, accumulated Gearbest points, and change the account password and details.
Hackers could use this information to create “local” damage: by accessing user accounts using their email and password, they can change user orders, manipulate account details, and spend monies from saved payment methods.
However, this information could also be used in a far more sinister way. By cross-referencing different databases, hackers could easily steal Gearbest’s customers’ identities.
As seen below, the Members database includes this user’s IP address, full postal address, email address, birth date, and, most worryingly, their national identity number.
Depending on the country and requirements, this could be enough information to give hackers access to online government portals, banking apps, health insurance records, and more.
Payment Details
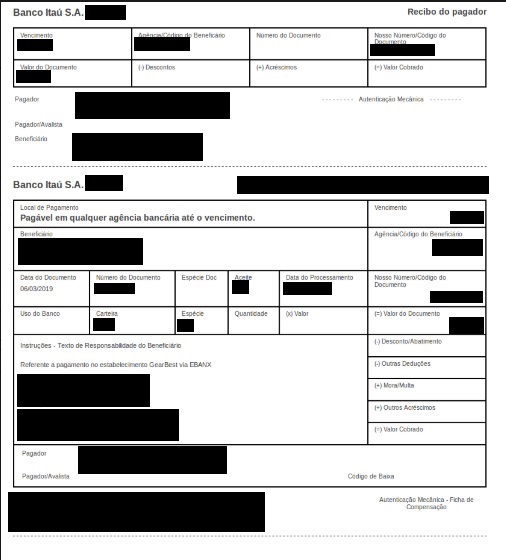
When examining the Payments and Invoices database, we noticed the term “Boleto” appeared multiple times, exclusively in reference to Brazilian orders (Brazil accounts for 9.2% of Gearbest’s global traffic).
It refers to Boleto Bancario (literally, “Bank Ticket”), a payment method which is regulated by the Brazilian Federation of Banks.
It’s similar to the Oxxo payment system used in Mexico. Oxxo allows users to create a voucher which functions like a debit card: users load the amount of their choosing, and can spend what’s available. Each voucher features a unique bar code; this gives users access to their money.
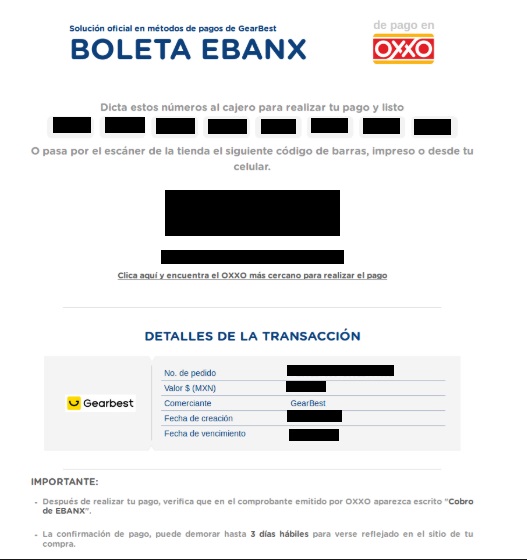
In the database we accessed, payments made using either of these methods include a URL for “ebanx.” These links show the active vouchers used, complete with their cash amounts. The data also includes Oxxo and Boleto vouchers’ unique barcodes; this information allows hackers to act as users. We could also access customer's receipts, complete with their banking information.
Order Details: Sex Toy Scandal
The exact content of people’s orders is visible on the Orders database. The exact make, color, size, and cost of each item can all be viewed, along with the user name and shipping address.
Compared to other information available across these unprotected databases, this doesn’t seem particularly shocking. However, the content of some people’s orders has proven very revealing – and in some instances, even life-threatening.
Hidden in the “Sales” section of Gearbest’s “Apparel” category, users can find a vast array of sex toys. The nature of the store’s open database means the details of your private purchases could quickly become public knowledge.
For many adults across the world, purchasing sex toys is not problematic. For example, the orders shown in the image below belong to people in Brazil and Greece.

These countries have very permissive laws regarding sexuality and homosexuality. For context, Brazil hosts the world’s largest Pride parade, and same-sex relationships have been legal in Greece since 1951. While the content of such orders being released could be embarrassing for the buyer, the publication of such information could not result in legal repercussions.
However, this is not the case everywhere. While examining the database, we came across order information for a male Pakistani user.
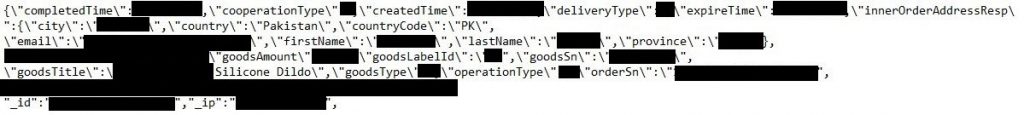
This customer purchased a silicone dildo; in fact, further inspection of the database shows that he actually bought three. Each purchase includes slightly different information, which is why a street address does not appear in the image above.
Pakistan does not enjoy the same liberal attitude to sexuality that many Western countries take for granted.
The country’s strict laws stipulate that adultery and pre-marital sex are criminal offenses punishable by imprisonment and fines. The country’s religious laws also allow for death by stoning or corporal punishment.
LGBT rights are limited, and the same punishments are applicable. The LGBT community also suffers social stigma, a lack of legal protection, and an Islamized society which precludes acceptance of LGBT people.
It’s also worth noting that culturally, it is unlikely that buyer made this purchase for his buyer’s wife.
These laws make our Pakistani shopper a prime example of why Gearbest’s open database is so dangerous. A simple search gave us his full name, email address, street address, and IP address. A more detailed search could probably show us his date of birth and account password, letting us see his previous order information.
We’re not malicious and are sharing this (highly censored) information to highlight the dangers of this open database. Others may have very different intentions. In the Pakistani government’s hands, this information could mean a literal death sentence for this user.
How Gearbest is Harming Itself
Gearbest is exposing millions of users’ data. However, the company is also hurting itself.
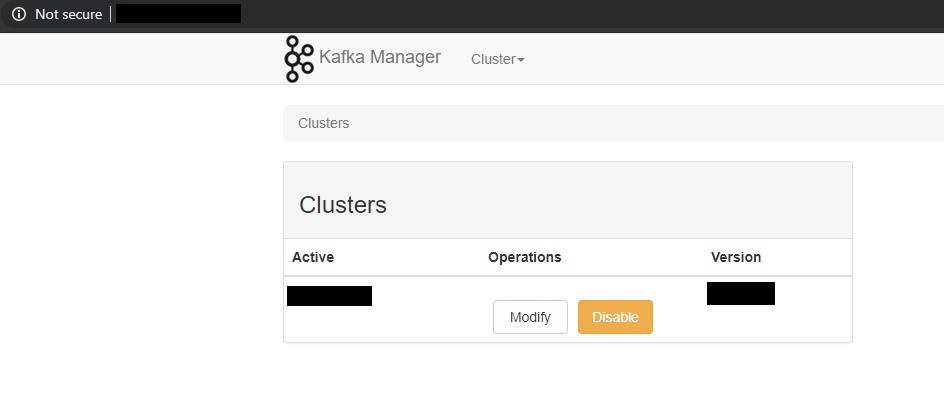
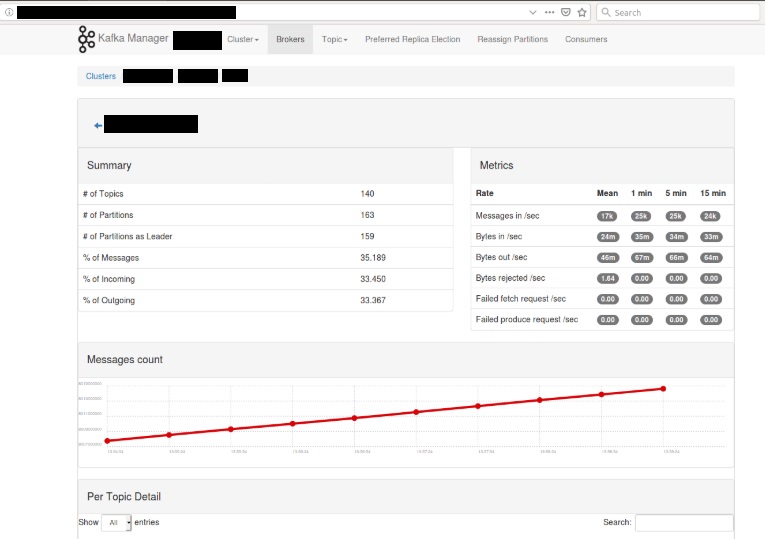
The indices our hackers discovered aren’t just for their user databases. They also included URL access to Gearbest’s – and Globalegrow’s – Kafka system.
Kafka is a data management program that helps large corporations control the amount of site data sent through each of their servers. This serves two purposes: it prevents server overload and maintains efficiency, and allows companies to collect big data.
This kind of access allows malicious hackers to manipulate information, reassign database properties, and even disable entire sections of the company’s server. Depending on the function of each server, this could disrupt data collection, order placement, and stock and warehouse management.
Ethical Hacking
We discovered this breach as part of an ethical hacking project. Noam Rotem, a well-known white hat activist and hacker, along with Ran L. and their team, is running a web scanning project which examines IP blocks and system holes for data leaks.
They verified the database’s owners by creating, entering, and identifying data.
They discovered that Globalegrow’s entire database is unprotected and mostly unencrypted. The company uses an Elasticsearch database, which is ordinarily not designed for URL use. However, we were able to access it via browser and manipulate the URL search criteria into exposing up to 10,000 schemata from a single index at any time.
As ethical hackers, we are obliged to reach out to websites when we discover security flaws. This is especially true when a company’s data breach affects so many people – and in Gearbest’s case, this issue impacts hundreds of thousands of people every day.
Nonetheless, these ethics also entail a responsibility to the public. It is imperative for Gearbest shoppers to be conscious of the risks associated with utilizing a site that shows no endeavor to safeguard its users.
We repeatedly contacted both Gearbest and Globalegrow to inform them of this breach, and to let them when we would be publishing this article. They had several days’ notice. Unfortunately, our repeated attempts to ask these companies to step up and protect their users have been unsuccessful. At the time of publication, we were yet to receive a response.
Past Reports
We recently revealed that Dalil experienced a massive data breach. Dalil is Saudi Arabia’s largest phone directory app, and the breach affected more than 5 million users. You may also want to read our report of fake apps used in Iran to monitor users, VPN Leak Report and Data Privacy Stats Report.
Please share this report on Facebook or tweet it.




Please, comment on how to improve this article. Your feedback matters!