Mailfence, a new secure email that fights to reclaim internet privacy
Pattrick de Schutter is a typical serial entrepreneur. He founded Allmansland, one of the first web agencies in Belgium back in 1994; A couple of years later he launched IP Netvertising, the first ad-sales house in Belgium, which was later sold to RTL; In addition, he also took part in a number of successful ventures, including rendez-vous.be, Belgium’s first ever dating site, and express.be the only independent business news site in Belgium.
In recent years, he's been operating ContactOffice, a virtual office software, and mailfence, an email privacy service, while devoting himself to fighting internet privacy violation and for improving the safety of users in Belgium and world-wide.
In this interview, he tells us his thoughts on international law, personal privacy and everything in between.
vpnMentor: Reading through your website, I get the feeling there is a strong ideology behind mailfence's activity. Could you tell us about the motivation and values behind Mailfence?
Mailfence is really the brainchild of a number of worried internet entrepreneurs. At ContactOffice we have always believed that users have an absolute and irrevocable right to Internet privacy. That is why we have never commercialized our user databases. During more than 15 years of business, users have always been spared advertising and have never been tracked or profiled. Following Snowden’s revelations in the summer of 2013, about massive government surveillance of Internet users, it became clear that users privacy on the Internet was seriously threatened. This was unacceptable to us.
We therefore started the Mailfence project approximately three years ago.
Rather than immediately start announcing things, we preferred to stay under the radar until we could present a solution which we could really be proud of.
vpnMentor: You mention on your website that you donate 15% of the Pro plan revenues to support the Electronic Frontier Foundation and the European Digital Rights Foundation. What can you tell about these organizations and your connection with them?
We are only a small part of a big movement which is currently taking its first steps. In order for a movement to succeed, you need alliances. We intend to support several foundations that will fight along with us for Digital rights and respect for privacy. Except for having shared goals, we do not have any direct connection with them.
vpnMentor: Do you have any personal experience regarding privacy violation? Would you mind sharing it with our readers?
Yes, most probably all the time. However, I was never made aware of it, which is the biggest problem with privacy violation: you only discover when it is too late or when a whistleblower releases data.
vpnMentor: Mailfence is committed to protect their customers from eavesdropping. What makes an email account vulnerable to eavesdropping?
There are various aspects to this issue. For now I will focus on the device aspect, and email account aspect.
Firstly, vulnerability to eavesdropping really depends on the safety of the user's device, which is being used to run a particular piece of software. If the device has been compromised (via a keylogger or a malware), then security measures taken by the email service provider will be of no use.
The Email Account aspect focusses on the security and privacy of emails and SMTP, as old as it is, with the STARTTLS non-availability on most of today’s mailing servers, thus putting email messages in plaintext makes them prone to meaningful eavesdropping.
Other aspects are related to the use of weak crypto-mechanisms, backdoors and malware, which make it possible for intruders to successfully eavesdrop.
vpnMentor: Who typically does the eavesdropping and for what purposes?
It can be done by a great deal of adversaries for various purposes.
Oppressive governments have mass surveillance programs, which not only passively eavesdrop, but also retain the obtained data for unlimited durations. So in short, all of your digital communications are being recorded, regardless of whether or not a specific target is at hand and without proper legal binding. As Eduard Snowden has well-put, their policy of “Collect ALL” means they will always have something against you to stand you liable for.
Yet another kind of foe can be commercial competitors, who engage in surveillance to acquire a strategic advantage, a matter that is always sensitive and highly valuable. Lastly, but equally significant, there exist hackers and assailants who conduct such activities for their individual benefit.
vpnMentor: What solutions are available today?
The technology for email security and privacy was proposed in 1991 (PGP), and the foremost implementation is GnuPG, which has been around for over a decade now, but have never really took flight in properly securing our email accounts. The reason for that is of course its poor usability, which is far too complex for a typical user, who over time got used to interactive and user-friendly GUI based solutions. Though we’ve seen Gpg4win/GPGtools, they still didn’t break the deal. Now, there is ‘hushmail’ that bypasses the OS+device dependency upon providing a dynamic web-application, but it is unable to form a sufficient level of trust and has many technical limitations.
Then recently, we’ve seen solutions like Prontomail and Tutanota, which came into existence along the lines of similar approach, with improved ease-of-use - but completely missed the point of balancing the thin line of security over convenience.
vpnMentor: Can you explain the difference between privacy violation and legitimate business intelligence gathering?
This is rather a legal question and I am not a lawyer. In addition it also depends on the country one operates in. Privacy is a fundamental human right. It underpins human dignity and other key values such as freedom of association and freedom of speech. Nearly every country in the world recognises the right of privacy in their constitution. At the least, it is a right of inviolability of the home and secrecy of communications. Legally, legitimate business intelligence gathering would not infringe with the privacy legislation of the country where it takes place. More info on this can be found here.
vpnMentor: How widespread is the phenomena of email Government surveillance, and do you find it to be more common in certain countries then others?
The UK-USA treaty is an agreement between the United Kingdom, United States, Australia, Canada, and New Zealand to cooperatively collect, analyze and share intelligence. The members of this group, which are known as "The Five Eyes", focus on gathering and analyzing intelligence from different parts of the world. While Five Eyes countries have agreed not to spy on each other as adversaries, leaks by Snowden have revealed that some Five Eyes members monitor each other’s citizens and share intelligence to avoid breaking domestic laws that prohibit them from spying on their own citizens. The Five Eyes alliance also cooperates with groups of third party countries to share intelligence (forming the Nine Eyes and Fourteen Eyes), however Five Eyes and third party countries can and do spy on each other. So to answer in a nutshell – it all depends on the matter of effective intelligence sharing, which gives them open-access to almost every part of the world, not to mention the reports of US agencies digging (intercepting) right into the fiber lines across the pacific so to sustain their policy of ‘Collect All’ with flying colors.
vpnMentor: On your website you specifically mention that you are not American and that you follow Belgian legislation. What is the advantage in that?
The terrifying scale of the NSA’s attack on public cryptography and its deliberate weakening of common international encryption standards have demonstrated that no proprietary software can be trusted – and the biggest suspects are the United Stated and the United Kingdom.
Information security services based in the US cannot be trusted, more specifically due to National Security Letters (NSLs) and accompanying “gag orders”, which forbid the recipient from talking about the request (asking for a court order ? etc…).
This combination allows them to secretly force companies to grant complete access to customer data and transform the service into a tool of mass surveillance. This is where we have the biggest advantage: In Belgium, the authorities cannot force a company to reveal the data of a user. Such requests must be accompanied by a Belgian court order.
vpnMentor: Mailfence states that files shared between 2 mailfence users are only stored on your servers and are therefore 100% private. What precautions do you take to keep your server private?
Being communicated over TLS, our servers are properly hardened, isolated and taken care of with high-end security measures. More precisely, they are located in Level 3 Communications in Brussels (with tight physical security), so we have full control over them, and provide no sneaky remote or third-party access to anyone.
We also use Debian as our operating system, because they take their security responsibilities and updates very seriously. In most cases, an update for a security issue will be available within hours of the original report.
Finally, we follow kernel-level firewalling and only allow necessary communications. Of course, there are many other measures, but for security reasons, I cannot disclose them all...
vpnMentor: What about emails and files which a Mailfence user shares with someone who uses a standard email server like Gmail or yahoo? How vulnerable are they to privacy violation?
Needless to say, their data-privacy is at stake, as it will always be available to ‘big brother’ (NSA) via backdoors, weakened encryption and deceptive security features.
Moreover, their dirty programs (cookies, scripts…) of data scanning to bombard you with tailor-made ads simply crush your online privacy to another level.
vpnMentor: We've all seen how email identity forgery can trick even the smartest of email users. For this particular purpose, Mailfence supplies its users with a digital signature. Can you explain how a digital signature can help in preventing email identity theft?
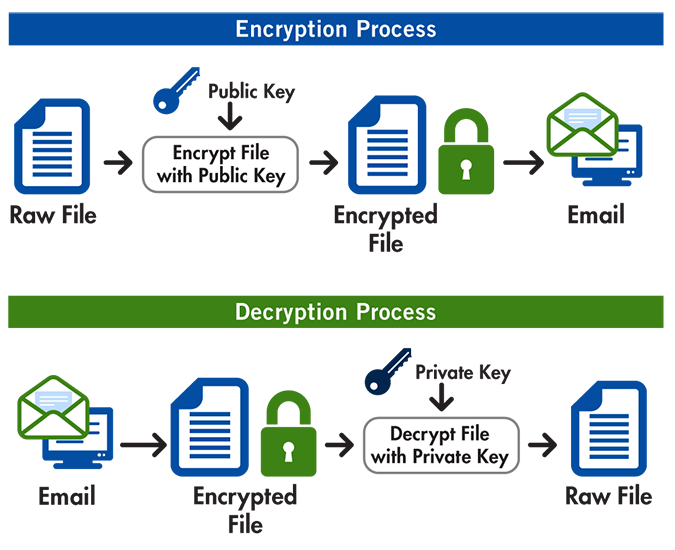
Digital signatures use crypto-based incentives to protect your identity. At Mailfence, the digital signatures (PGP/MIME) allows users to sign their emails with their personal key which can only be used & accessed by themselves. The recipient then receives these signed emails and verifies their authenticity, which as a result proves that an email is indeed sent by its claimed owner, that the email has not been modified during transit, and that it has not been maliciously or fraudulently repeated or delayed.
Also, each of our users is able to verify the fingerprint of the key that has been used to sign a specific message – which further endorses the validity of the sender's identity.
vpnMentor: How can Mailfence help in filtering out malicious emails which are supposedly sent by friends?
Mailfence has various inner-mechanisms for filtering the malicious emails – which include virus checking routines, enhanced spam avoidance measures and user-side blacklisting.
vpnMentor: What measures would you recommend for someone who's identity has been forged?
We’ve seen various cases where a user private key has been compromised (or he/she has lost the passphrase to use it), and their emails are now being signed with forged digital signatures. We strongly recommend those users to revoke their key by using a direct revoke option or via a revocation certificate from Mailfence, which will publish their revocation request to public key servers and let people know that they don’t use that keypair anymore.
Our “How-To” manual provides detailed instructions for such cases as well.




Please, comment on how to improve this article. Your feedback matters!