Meet eyeShare - A Process Automation Solution for Managing IT Operations with Ease
Ayehu CEO Gabby Nizri has been in the industry of software engineering and IT Management since 1995. He started his career at Walla.com, Israel's number one portal for internet communications at the time, where he created a scalable infrastructure that turned routine activities into automated processes while improving efficiency, thus saving his team's valuable time. Since then, he has been developing 24/7 data center operations, and created eyeShare, a fully automated solution that takes the load of routine maintenance tasks off IT departments. In this article Nizri lays his views on legacy systems, IT process automation, and the rapidly changing scenery of the IT industry. Share
Ayehu's eyeShare solution has been deployed by major enterprises worldwide, and currently supports thousands of IT operations across the globe. How do you explain your success?
In 2007, when I co-founded Ayehu together with my partner Yaron Levy, we set out to create a tool that will simplify the 24/7 management of IT operations, but we never imagined the outcome will be so much like a robot.
When we first started conceptualizing this project, I intentionally recruited some students and graduates without much background and experience so that we would generate some fresh ideas. We created a simple tool that enables users to design workflows without writing a single line of code, using logic rather than technology.
We managed to automate all Level 1 network operation's day-to-day activities, including intercepting alerts, troubleshooting, resolution, and escalation to level 2 where needed. Today, eyeShare reduces time to resolution by 80%, which is a major improvement for any IT department.
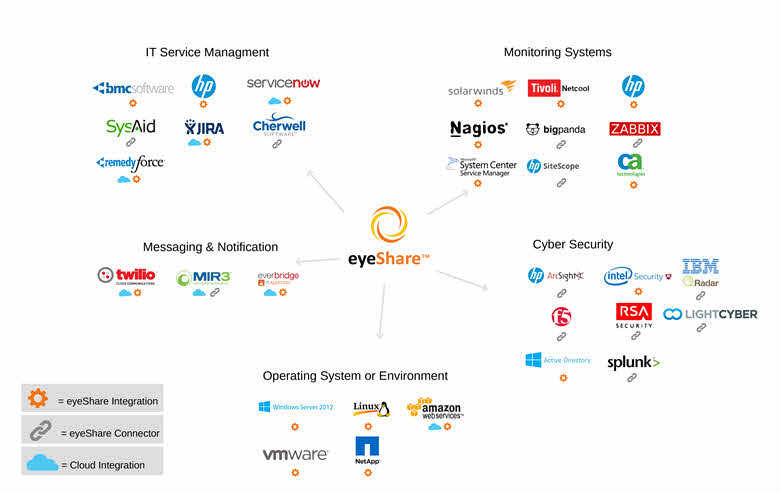
Our platform can be integrated into many IT service management, remediation and security tools into the SIEM (intel's McAfee ESM, IBM's Qradar, HP ArcSight and Splunk). Once integrated, our platform allows the user to orchestrate and automate processes and workflows between all of these applications. Whenever we capture an incident that is coming from the cyber security tool being used, we streamline the entire process across IT and security in order to investigate contain and remediate the issue as quickly as possible.
By adopting an automated approach towards IT management, one could speculate that many IT experts may find themselves without a job.
10 years ago people's resources were not an issue. It was widely understood that in order to maintain a healthy environment people and resources would be required. Today, however, with resources having become more scarce, we are fortunate to have the technology to reduce costs and make maintenance easier and more efficient. Regardless, from our perspective, we're certainly not looking to eliminate IT jobs but to empower the teams, helping them to become experts in strategic problem solving.
The IT outsourcing services market still relies on people, but companies are limited in how many employees they can hire. In that sense, automation cuts down the costs of mundane repetitive activities, saves loads of time and effort, and leaves no room for "human mistakes." With automation, you can scale your business without scaling the team, which has become the mainstream.
Another issue is that there's a huge lack of skills in the market, and company owners are struggling to find reliable IT personnel. Humans make mistakes that can potentially cause severe damages to an IT operation. A "virtual operator" on the other hand can learn a process once, and repeat it over and over again; so unless the error comes from the person who built the process to begin with, automated processes will always be safer and more accurate than manual labor.
People have fear from automation because it holds a great change and can even be risky if not done properly.
Simultaneously, it's essential for a human presence to monitor these procedures and manage particular incidents that haven't been automated. In this way, IT managers can enhance their functions and advance them beyond mere routine upkeep

Some might argue that automation is a risk to security. How would you address such claims?
If IT and network operation centers are responsible for avoiding downtime, think about the cyber security guys, who need to deal with the potential of critical infrastructure like power and water being shut down. To avoid that, they need to be using the same tools and procedures, and therefore they too benefit greatly from automated procedures across the entire IT operation.
The main challenge is that IT and Security are often works in silos by different departments with different incentives and mindsets.
While IT operators tend to be the earlier adaptors, later stage adapters from the Security sector are also starting to embrace automation and are opening to new ideas and technologies that reduce the resolution time, because they see the benefits from their end.
Some might argue that people are more reliable then machines, but if the tools are running on your private network, and if you're only giving permissions to well defined processes, security becomes a very minor issue compared to providing a password to a person. People on the other hand have motives, hidden intentions,
So if you compare risks vs. rewards, the answer is clear. Little risk big rewards.
How do you convince an IT person who's been maintaining their servers for years, to move to automated services? How do you gain their trust?
One of our greatest challenges is convincing old fashioned IT managers, who are used to working with their own legacy systems, that automating their processes is a good idea.
Many of them, especially the ones with more experience, feared placing their trust in an automated system, and they had a point: if it's not broken, don’t fix it, right?
But this holds back many companies with legacy systems, which are getting harder and harder to maintain and are slowly going out of the market. However, increasingly IT leaders are recognizing the opportunity in automation, and upon retirement, they want to leave their company with something meaningful they have done. From their perspective, automation is a game changer.
Using eyeShare, IT managers will be able to replace most maintenance work with automated processes, using a simple to use workflow canvas. This will help them to create next-generation hybrid IT departments with changing ratios of humans and robots.
We've seen a similar shift when cloud storage was first introduced. The next step is to add a virtual operator that simplifies human work while maintaining a stable environment.
People will then be able to save thousands of hours doing mundane routine work, and dedicate their time to doing something meaningful for their business and for themselves.



Please, comment on how to improve this article. Your feedback matters!