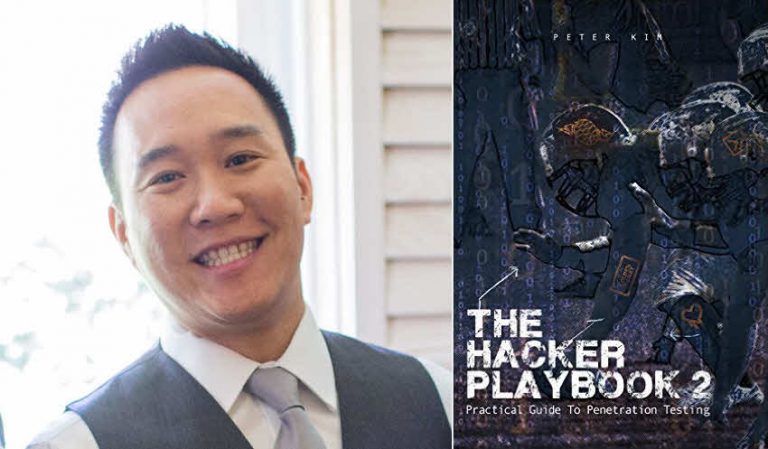
The Hacker Playbook 2: Practical Guide To Penetration Testing - Free Chapter Included
Peter Kim describes himself as heavily involved in the security community. He's spent the last ten years working as a penetration tester and incident responder for a variety of business sectors. On his free time, he manages a local hackerspace in Santa Monica, and writes about his research at the SecurePla.net blog. His latest book, The Hacker Playbook 2: Practical Guide To Penetration Testing is a compilation of different methodologies that he's learned over the years, many of which he has presented at multiple security conferences over the years. In this article, Peter Kim gives vpnMentor readers a sneak preview to his book. Share
What made you write this book?
The book was originally written as a collection of my lifetime of notes and tips from my 12 years of offensive security. I love to teach those passionate about hacking and this was a way to get my ideas and thought processes to a broader audience. I've read tons of other security books and while I've read other great ones, I felt a gap with being able to demonstrate real world attacks. This was made to fill in that gap.
What new knowledge did you gain whilst writing the book?
One thing that stuck out to me is that security is a never ending learning experience. There is no finish line and most importantly, you can't think of security as a job but a lifestyle. Those that seem to understand and "get it" are those that are passionate and motivated.
What would you advise to beginners seeking to launch a cyber security career?
The best advice I can give to those trying to break into the industry is get involved, contribute to the security community, participate in CTF competitions, and don't get overwhelmed!
Below is the first chapter of The Hacker Playbook 2: Practical Guide To Penetration Testing by Peter Kim
If you're interested in picking up a copy, grab one from Amazon here.
Hunched over your keyboard in your dimly lit room, frustrated, possibly on one too many energy drinks, you check your phone. As you squint from the glare of the bright LCD screen, you barely make out the time to be 3:00 a.m. “Great”, you think to yourself. You have 5 more hours before your test is over and you haven’t found a single exploit or critical vulnerability. Your scans were not fruitful and no one’s going to accept a report with a bunch of Secure Flag cookie issues.
You need that Hail Mary pass, so you pick up The Hacker Playbook and open to the section called “The Throw - Manual Web Application Findings.” Scanning through, you see that you’ve missed testing the cookies for SQL injection attacks. You think, “This is something that a simple web scanner would miss.” You kick off SQLMap using the cookie switch and run it. A couple of minutes later, your screen starts to violently scroll and stops at:
Web server operating system: Windows 2008
web application technology: ASP.net, Microsoft IIS 7.5
back and DBMS: Microsoft SQL Server 2008
Perfect. You use SQLMap to drop into a command shell, but sadly realize that you do not have administrative privileges. “What would be the next logical step...? I wish I had some post-exploitation tricks up my sleeve”, you think to yourself. Then you remember that this book could help with that. You open to the section “The Lateral Pass - Moving through the Network” and read up and down. There are so many different options here, but let’s see if this host is connected to the domain and if they used Group Policy Preferences to set Local Administrators.
Taking advantage of the IEX Power Shell command, you force the server to download Power Sploit’s GPP script, execute it, and store the results to a file. Looks like it worked without triggering Anti-Virus! You read the contents of the file that the script exported and lo and behold, the local administrative password.
The rest is history... you spawn a Meterpreter shell with the admin privileges, pivot through that host, and use SMBexec to pull all the user hashes from the Domain Controller.



Please, comment on how to improve this article. Your feedback matters!