Report: Australian Marketing Company Exposes 100,000s of People to Fraud
Led by Noam Rotem and Ran Locar, vpnMentor’s research team recently discovered an enormous data breach by the Australian marketing software firm Acquirely.
Acquirely offers businesses in Australia “digital customer acquisition” services through various forms of online marketing and lead generation. Much of the company’s activities involve harvesting data from the public, which can be converted into leads for its partners.
However, Acquirely was storing some of this data out in the open on an unsecured cloud account. As a result, the company exposed over 200,000 Australians to a wide range of online attacks and fraud.
Data Breach Summary
| Company | Acquirely |
|---|---|
| Headquarters | Melbourne, Australia |
| Industry | Sales and Lead Generation |
| Size of data in gigabytes | 5.2 GB |
| Suspected no. of files | 3,453 |
| No. of people exposed | 200,000+ |
| Date range/timeline | Data dating back to 2019; Backed up on the bucket from April - October 2020 |
| Geographical scope | Australia |
| Types of data exposed | PII data and personal information |
| Potential impact | Phishing; fraud; identity theft; corporate espionage |
| Data storage format | AWS S3 bucket |
Company Profile
Acquirely was founded in 2001 and is currently headquartered in Melbourne, Australia.
It provides corporations with a wide range of B2C marketing services, including email marketing, direct response campaigns, permission-based marketing, and much more.
Acquirely claims to work with many well-known Australian and global brands.
 Acquirely’s biggest clients, according to its website
Acquirely’s biggest clients, according to its website
Timeline of Discovery and Owner Reaction
- Date discovered: 9th September 2021
- Date vendors contacted: 12th September 2021
- Date of 2nd contact attempt (if relevant): 15th September 2021
- Date Amazon contacted: 15th September 2021
- Date CERT Australia contacted: 20th September 2021 (replied on the same day)
- Date of response: 18th October 2021
- Date of action: 21th September 2021
Sometimes, the extent of a data breach and the owner of the data are obvious, and the issue is quickly resolved. But rare are these times. We often need days of investigation before we understand what’s at stake or who’s exposing the data.
Understanding a breach and its potential impact takes careful attention and time. We work hard to publish accurate and trustworthy reports, ensuring everybody who reads them understands their seriousness.
Some affected parties deny the facts, disregarding our research or playing down its impact. So, we need to be thorough and make sure everything we find is correct and accurate.
In this case, Acquirely was using an Amazon Web Services (AWS) S3 bucket to store data collected from the public through its various activities. S3 buckets are an increasingly popular enterprise cloud storage solution. However, users must set up their security protocols manually to protect any data stored therein.
Acquirely failed to implement any security measures on its S3 bucket, leaving the contents totally exposed and easily accessible to anyone with a web browser and technical skills.
Once we confirmed that Acquirely was responsible for the data breach, we contacted the company to notify them and offer our assistance. After our initial attempt at outreach failed, we tried the company again and contacted AWS in the meantime.
With no reply from either party, we contacted the Australian national Computer Emergency Response Team (CERT). They replied the same day and said they’d reach out to Acquirely directly and provide further advice to mitigate any risk from the data breach.
After following up with the CERT Australia a second time, we received the following reply:
"The Australian Cyber Security Centre (ACSC) has not received any contact from Acquirely in relation to this matter. You may wish to try contacting Amazon Web Services directly with your concerns."
After a few weeks, we received a very professional reply from Acquirely that it had taken steps to protect its sensitive files stored on the cloud after the ACSC reached out to them on the 21st of September.
Example of Entries in the S3 Bucket
While it’s not clear how long Acquirely had been collecting this data, it appeared it was all backed up over a short period: from April to October 2020.
Acquirely had collected (and exposed) the data of over 200,000 people residing in Australia. It appears that most of this data was provided voluntarily by people entering competitions run by Acquirely for its clients. However, the people sharing their data likely expected the company would take some basic measures to protect it.
The company’s activities mean the range was vast, with people not only sharing considerable Personally Identifiable Information (PII) data, but also personal details about their lives.
This data was stored in numerous forms:
- 3 CSV files with 436,000 lines of data (203,000 from unique entries)
- A handful of smaller CSV files, most of which were empty
- A few thousand images that didn’t pose any risk
The data we viewed in these CSV files included:
- Emails
- Names
- Dates of birth
- Phone numbers
- Home and work addresses
The following screenshots are samples of the data exposed, which we’ve edited to protect the identities of the people affected.
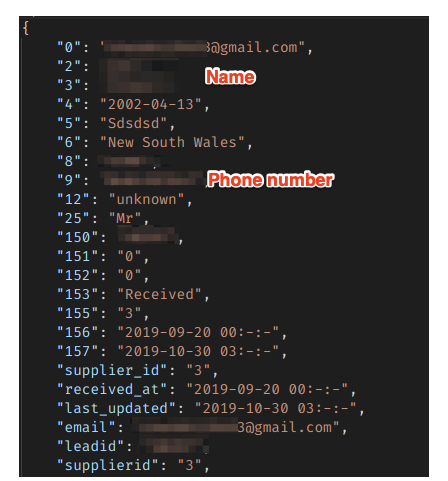 Records PII data for someone living in New South Wales
Records PII data for someone living in New South Wales
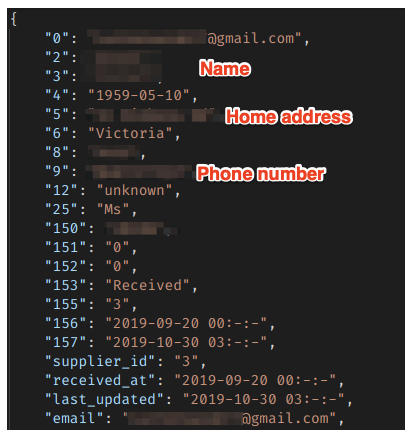 PII data from someone in Victoria
PII data from someone in Victoria
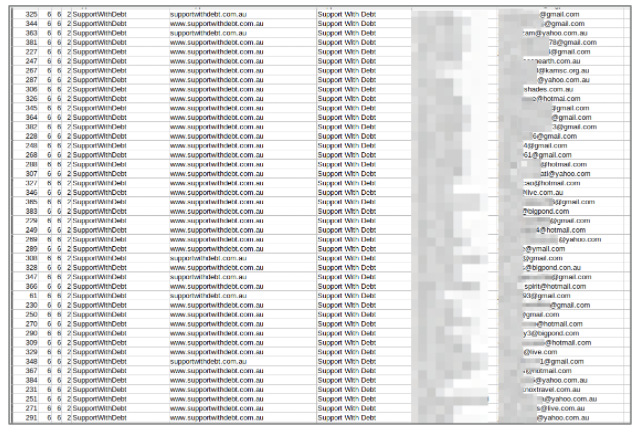 Email address and other PII data collected for an Acquirely client
Email address and other PII data collected for an Acquirely client
Data Breach Impact
Had malicious or criminal hackers discovered Acquirely’s AWS account before it was secured, they could have used the data in a wide range of criminal schemes.
The exposed data would have been enough for skilled hackers to commit many of the most common forms of fraud, including:
- Identity theft
- Tax fraud
- Insurance fraud
- Mail fraud
- Bank account takeover
- Debit or credit card fraud
- Mortgage fraud
- And many more...
However, even if the exposed data wasn’t sufficient to exploit for criminal gains, it could also be used to carry out complex phishing campaigns.
In a phishing campaign, criminals send victims fake emails and text messages imitating real businesses and organizations. By building the victim’s trust, they hope to trick them into any of the following actions:
- Providing additional PII data (i.e., social security numbers) or private information (i.e., bank account details) that can be used in the fraudulent activities listed above.
- Inputting debit or credit card details into a fake payment portal, so they can be scraped and used by criminals or sold on the dark web.
- Clicking a link embedded with malicious software that infects a user’s device, such as malware, spyware, and ransomware.
Due to the number of people exposed in this data breach, cybercriminals would only need to successfully scam a small percentage for any criminal scheme to be considered successful.
Finally, one of Acquirely’s clients was a debt relief company. Hackers could use this information to target people in debt with highly exploitative schemes that put them under enormous pressure. As a result, they may be much more vulnerable to extortion or fraud, with devastating consequences.
For The Company
Acquirely may also suffer as a result of this data breach. The public is a lot more aware of data breaches by companies and the potential effects on their lives than in the past. Acquirely could face significant backlash from people concerned that they provided private data to a company taking insufficient precautions to protect it.
Furthermore, current clients may try to distance themselves from the company or cancel contracts to ensure they’re not adversely impacted. Potential future clients may be dissuaded from working with Acquirely and hire its competitors instead.
If they had somehow gained access to the data, the same competitors could also use this breach to gain insight into Acquirely’s business model and copy it wholesale, or simply use it as a marketing tool by running negative publicity campaigns against the company.
Finally, the Australian government may take legal or regulatory actions against Acquirely for leaking so many citizens’ private data.
In the short term, all these outcomes would have a direct impact on Acquirely's revenues and its operational sustainability over the coming years.
Advice from the Experts
Acquirely could have easily avoided exposing its customers’ data if it had taken some basic security measures. These include, but are not limited to:
- Securing its servers.
- Implementing proper access rules.
- Never leaving a system that doesn’t require authentication open to the internet.
Any company can replicate the same steps, no matter its size.
For a more in-depth guide on how to protect your business, check out our guide to securing your website and online data from hackers.
Securing an Open S3 Bucket
It’s important to note that open, publicly viewable S3 buckets are not a flaw of AWS. They’re usually the result of an error by the owner of the bucket. Amazon provides detailed instructions to AWS users to help them secure S3 buckets and keep them private.
In the case of Acquirely, the quickest way to fix this error would be to:
- Make the bucket private and add authentication protocols.
- Follow AWS access and authentication best practices.
- Add more layers of protection to its S3 bucket to further restrict who can access it from every point of entry.
For The Public
If you think you’ve interacted with Acquirely recently and are concerned about how this breach might impact you, contact the company directly to find out what steps it's taking to protect your data.
To learn about data vulnerabilities in general, read our complete guide to online privacy.
It shows you the many ways cybercriminals target internet users and the steps you can take to stay safe.
How and Why We Discovered the Breach
The vpnMentor research team discovered Acquirely’s data breach as part of a huge web mapping project. Our researchers use large-scale web scanners to search for unsecured data stores containing information that shouldn’t be exposed. They then examine each data store for any data being leaked.
Our team was able to access this S3 bucket because it was completely unsecured and unencrypted.
Whenever we find a data breach, we use expert techniques to verify the owner of the data, usually a commercial business.
As ethical hackers, we’re obliged to inform a company when we discover flaws in their online security. We reached out to Acquirely, not only to let them know about the vulnerability but also to suggest ways in which they could make their system secure.
These ethics also mean we carry a responsibility to the public. Members of the public must be aware of a data breach that exposes so much of their sensitive data.
The purpose of this web mapping project is to help make the internet safer for all users.
We have no evidence or way of knowing whether the data in our reports have been accessed or leaked by anyone else; only the database owner can know that.
We do our best to prevent this from happening by reaching out to the companies and ensuring they secure their leaking database as soon as possible.
We never sell, store, or expose any information we encounter during our security research.
About Us and Previous Reports

This has included exposing the growing popularity of cybercrime groups on Telegram. We also revealed how a popular Chinese game developer was leaking data from over 1 million people. You may also want to read our VPN Leak Report and Data Privacy Stats Report.




Please, comment on how to improve this article. Your feedback matters!