Report: Web Browser for Developers Leaves User Data Exposed
Researchers Noam Rotem and Ran Locar, leaders of vpnMentor’s security team, recently uncovered a data breach affecting the Blisk browser, a web browser designed specifically for web development.
Based on Noam and Ran’s research it appears that the Blisk browser is collecting data from its users and bypassing any security measures they have in place.
This was a big data leak, with over 2.9 million records - totaling 3.4GB of data - exposed. It left potentially thousands of web developers all over the world vulnerable to online attacks and fraud.
It’s bad enough that Blisk is built to collect user data, and worse still that it’s then leaking this data to the outside world.
Blisk Browser Company Profile
Blisk is a web browser tailor-made for web developers, UX designers, and web engineers.
It gives web development teams and freelancers a unique workspace to build and test websites and app designs in real time, before launching or implementing changes in a live online environment.
Founded in 2014, Blisk boasts huge popularity amongst web developers around the world, along with many well known corporate customers: NASA, Microsoft, Apple, eBay, UNICEF, and many more.
Timeline of Discovery and Owner Reaction
Sometimes, the extent of a data breach and the owner of the data are obvious, and the issue quickly resolved. But rare are these times. Most often, we need days of investigation before we understand what’s at stake or who’s leaking the data.
Understanding a breach and its potential impact takes careful attention and time. We work hard to publish accurate and trustworthy reports, ensuring everybody who reads them understands their seriousness.
Some affected parties deny the facts, disregarding our research or playing down its impact. So, we need to be thorough and make sure everything we find is correct and true.
After confirming Blisk as the database’s owner, our research team informed the company of the vulnerability. Blisk responded quickly, and the breach was closed.
- Date discovered: 2nd December 2019
- Date vendors contacted: 4th December 2019
- Date of Response: 5th December 2019
- Date of Action: 9th December 2019
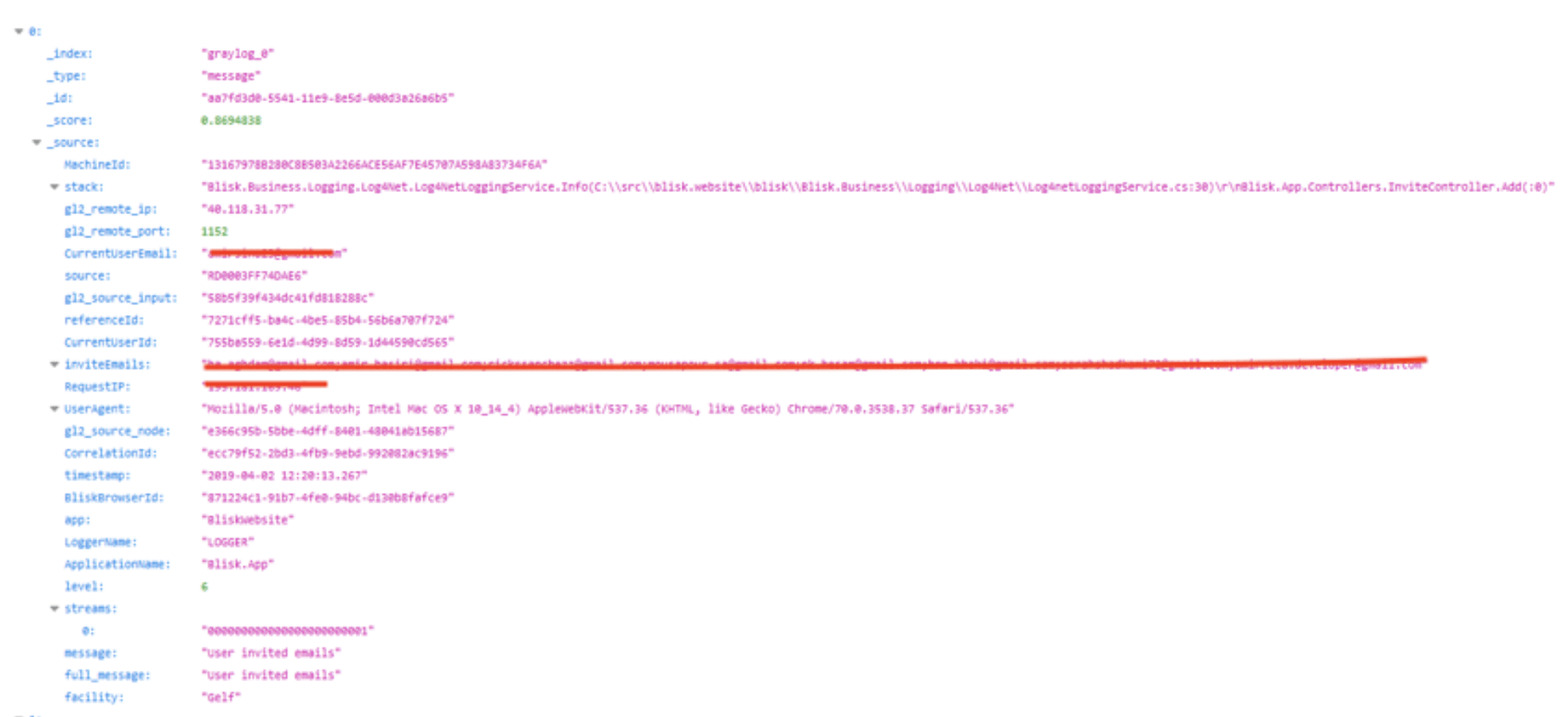
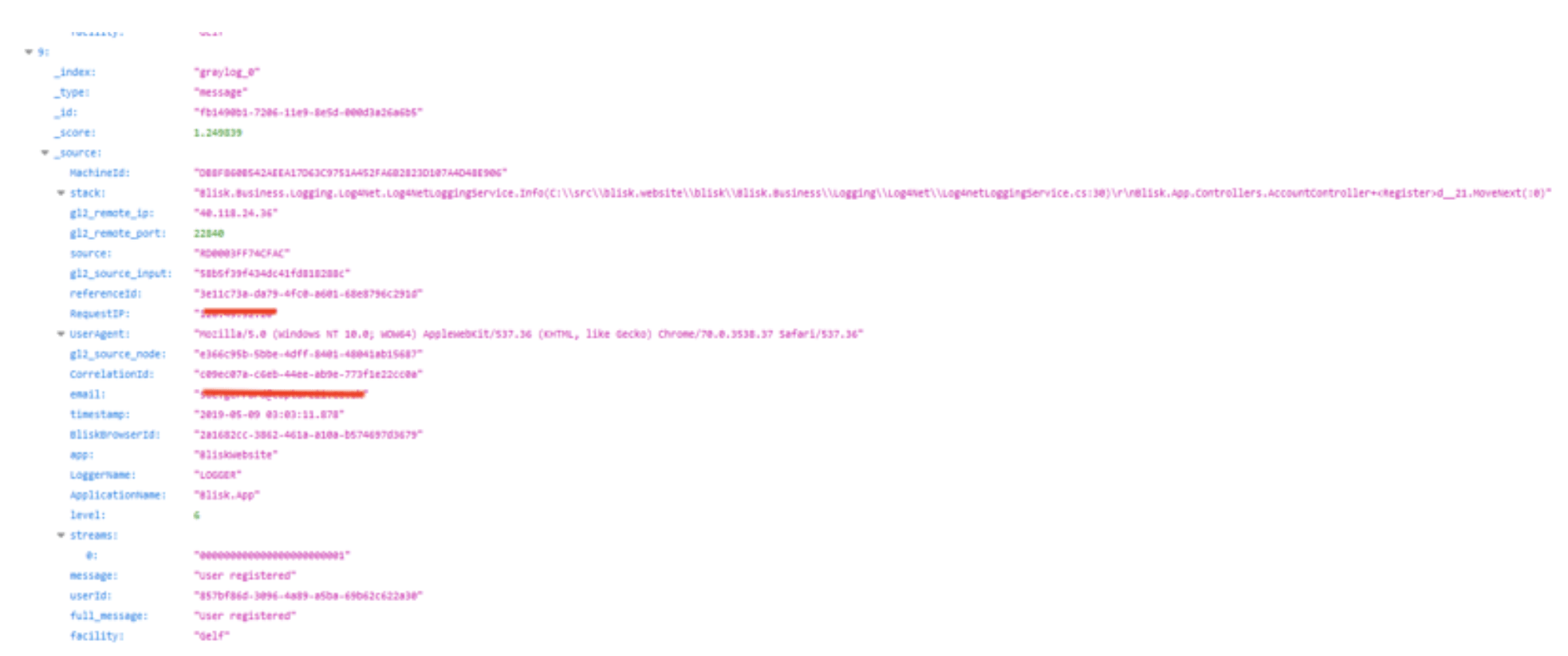
Example of Entries in the Database
Based on our team’s findings, we estimate the exposed database contained over 2.9 million individual records from Blisk users. This amounted to 3.4GB of data - a massive amount of information out in the open.
Each of these entries contained sensitive personal information data on Blisk users, including:
- Over a thousand email addresses – including a ca.gov email address
- IP addresses
- User Agent details
The leak affected Blisk users across the globe. During our research, we viewed entries from users in many different countries, including:
- Germany
- France
- United Kingdom
- China
- Italy
- Russia
- Japan
- Australia
- Brazil
- Czech Republic
- South Africa
- Hungary
- Many more
There are several issues in this data leak. First of all, and most obviously, that Blisk was not keeping the data secure in any way.
Secondly, the nature in which it was collecting the data.
Finally, and most concerning of all, Blisk’s web browser actively bypasses security measures put in place by users. Since the browser “sees” what the user sees, it can potentially bypass every encryption, 2-factor authentication, and any other measure they have in place. If the user is using software that is not heavily secured, this can lead to very serious security breaches.
It appears that no matter what security measures you put in place while using Blisk, your data would still potentially be leaked.
Data Breach Impact
The data that has been exposed in this breach involves email addresses, IP addresses, and user agent details. The exposure of the kind of information in this breach has some serious implications.
Email Details
When email addresses are exposed, these details can be used in a variety of ways.
For example, not only can email addresses be spammed with junk messages, but cybercriminals can send phishing emails (emails designed to glean information such as login details, passwords, or financial information) and emails that contain links to websites infected with malware.
Although we’d expect web developers to be able to recognize phishing emails and other malicious content, if a malicious person could send an email that looks like a newsletter from Blisk, even experts could be fooled!
IP Addresses
While it’s a myth that an IP address can expose identity details, if hackers have access to your IP address, they can still exploit this information.
For example, a malicious hacker could use a port scanner to discover the services running on a computer, including the OS (operating system), and then discover if the computer is running any outdated (vulnerable) services. It’s like a burglar looking for an easy way into a house.
There are myriad options for hackers to exploit vulnerabilities discovered this way, including using malware or a trojan to gain access to a computer–putting all kinds of data at risk! It’s also possible for a cybercriminal to use DoD (denial of service) attacks to force a web connection to go down.
Of course, hackers can also sell the data they’ve gathered on the dark web.
User Agent Data
User agent data isn’t a super-high risk, but if cybercriminals have access to this information, they can create custom exploits that are more likely to be successful with a specific browser and operating system setup. This is especially valuable in this case, where developers working on specific sensitive applications can be targeted for a classic supply chain attack.
Advice from the Experts
Blisk could have easily avoided this leak if they had taken some basic security measures to protect the database. These include, but are not limited to:
- Secure your servers.
- Implement proper access rules.
- Never leave a system that doesn’t require authentication open to the internet.
Any company can replicate the same steps, no matter its size.
For a more in-depth guide on how to protect your business, check out our guide to securing your website and online database from hackers.
For Blisk Users
If you’re a web developer using Blisk and are concerned about how this breach might impact you, contact the company directly and ask them to explain exactly how they are resolving the issue.
To learn more data vulnerabilities in general, read our complete guide to online privacy.
It shows you the many ways cybercriminals target internet users, and the steps you can take to stay safe.
We also suggest using a VPN to hide your IP address. This is a quick and easy way to add an extra layer of protection while online.
How and Why We Discovered the Breach
In the course of a major web mapping initiative, the research group at vpnMentor identified a breach in Blisk's database. Our investigative team utilizes port scanning to scrutinize specific IP blocks and checks open gaps in systems for any vulnerabilities. Every one of these gaps is then meticulously probed for potential data leakage.
When they find a data breach, they use expert techniques to verify the database’s identity. We then alert the company to the breach. If possible, we will also alert those affected by the breach.
Our team was able to access this database because it was completely unsecured and unencrypted.
The company was using an Elasticsearch database, which is ordinarily not designed for URL use. However, we were able to access it via browser and manipulate the URL search criteria into exposing the database schemata.
The purpose of this web mapping project is to help make the internet safer for all users.
As ethical hackers, we’re obliged to inform a company when we discover flaws in their online security.
These ethics also mean we carry a responsibility to the public. Blisk users must be aware of a data breach that impacts them also.
About Us and Previous Reports

This has included a huge data leak exposing the data of 10,000s of American restaurant diners. We also revealed that a company owned by European hotel giant AccorHotels compromised the privacy and security of hotel guests around the world. You may also want to read our VPN Leak Report and Data Privacy Stats Report.
[Publication date: 14.03.2020]




Please, comment on how to improve this article. Your feedback matters!