Report: Critical Flaws in Cybersecurity Devices Exposed Entire Networks to Attack and Takeover
- Cyberoam Company Profile
- How We Discovered the Vulnerabilities
- How The Vulnerabilities Worked
- The First Vulnerability: Unauthenticated Root Remote Command Execution (pre-auth RCE)
- The Second Vulnerability: Unauthenticated Root Remote Command Execution (pre-auth RCE)
- Hardcoded Default Login Credentials, Discovered by Nadav Voloch
- How Many Networks Were at Risk?
- Potential Impact
- Potential Impact on Cyberoam
- Advice from the Experts
- How We Discovered the Exploit
- About Us and Previous Reports
This report covers two vulnerabilities in cybersecurity provider Cyberoam’s firewall and VPN technology, affecting the "email quarantine system,” reachable without authentication. They were discovered by different researchers working independently.
The first vulnerability was reported on in late 2019, while the second was shared with vpnMentor by an anonymous ethical hacker at the beginning of 2020. After confirming their findings, our team discovered a third flaw, which had also gone unnoticed.
These vulnerabilities, both independently and when put together, could have been potentially exploited by sending a malicious request, which would enable an unauthenticated, remote attacker to execute arbitrary commands.
Sophos has already published hotfixes to resolve both of these vulnerabilities.
Cyberoam Company Profile
Founded in 1999, Cyberoam is based in Ahmedabad, India and has a truly global reach:
550 employees around the world serve a customer base of 65,000 users, along with 5,500 technology and software partners. These are all spread between 120+ countries.
The company provides security solutions to “global corporations in the manufacturing, healthcare, finance, retail, IT sectors, and more, in addition to educational institutions, public sector and large government organizations.”
Cyberoam was bought by leading British security and data protection firm Sophos in 2014 and integrated into its product range.
The vulnerabilities we discovered were not the first flaw in Cyberoam’s security products. For many years, people have been identifying significant weaknesses in their software products and devices:
- July 2012: Two researchers revealed that Cyberoam was using the same SSL certificate across many of its devices. Doing so would have allowed hackers access to any affected device on Cyberoam’s network and intercept its data traffic.
- 2018: Indian media reported that a hacker had stolen massive portions of Cyberoam databases and put them up for sale on the Dark Web. Anonymous ethical hackers estimated over 1 million files relating to Cyberoam customers, partners, and internal operations were available for purchase online.
- 2019: Ethical hackers found another vulnerability and reported on it in online media. This is the basis for the flaw shared with us in January 2020 and is detailed below.
Who Uses Cyberoam Products?
Cyberoam mostly builds technology solutions for large enterprises and international organizations, integrating them into more extensive networks. These include:
- Network security solutions, such as firewalls and UTM appliances
- Centralized security management devices
- VPNs
- Anti-Virus, spyware, and anti-spam tools
- Web filtering
- Bandwidth management
- Much more
Cyberoam software is usually placed at the edge of a network, encircling it with numerous security tools.
In essence, it forms a gateway that allows access for staff and other permitted parties, while blocking any unauthorized entry into a network. This process also provides for high-level control of networks via Cyberoam devices and software.
Cyberoam also sells products designed for use in homes and small offices.
How We Discovered the Vulnerabilities
The main flaw in Cyberoam’s security involved two separate vulnerabilities in how an email is released from quarantine on a Cyberoam device.
Both unrelated issues could have been used to give hackers access to Cyberoam’s devices, and, as an end result, make it easier to exploit any device which their firewalls were guarding.
The first issue was discovered around the end of 2019, reported to Sophos, and resolved by Sophos and Cyberoam promptly.
The second was shared with us by an ethical hacker who wished to remain anonymous.
Once the internal team at our Research Lab, led by Nadav Voloch, verified the vulnerability shared by the anonymous hacker, Nadav continued to review the previous vulnerability disclosure and Cyberoam server interfaces. He then discovered that Cyberoam devices support default passwords.
In total, that makes two separate unauthenticated security flaws in the email quarantine feature of Cyberoam’s technology discovered within six months, in addition to supporting default passwords. We worked with Cyberoam by coordinating a disclosure timeline and a patch workaround.
Timeline
First vulnerability discovered and resolved: Late 2019
2nd vulnerability reported to us by anon. source: 01/02/2020
Cyberoam Contacted: 06/02/2020, 11/02/2020
Reply Received: 12/02/20
Action taken: 24-26/02/20
How The Vulnerabilities Worked
In basic terms, the vulnerabilities gave hackers indirect access to any Cyberoam security device via their centralized web-based firewall Operating System (Firewall OS) interface.
This was possible due to an error in how Cyberoam had set up access to user accounts on their devices.
These vulnerabilities required no authentication to exploit. An attacker simply needed to know the IP address of the vulnerable Cyberoam device, and they could have a reliable shell without any crashes.
Once hackers gained remote access to the CyberoamOS shell, they could indirectly access any server file and monitor the entire network. This is also a privileged position to pivot into other devices connected to the same network (often an entire organization).
Our individual simple research on the scale of the vulnerability showed at least 170,000 unique internet-connected firewalls were potentially affected by the vulnerability. Each one of these was acting as a potential doorway to thousands of independent organizations across the globe.
Because Cyberoam devices and VPNs are often used as a foundational security gateway protecting large networks, any vulnerability in their software would have severe implications for an affected network.
Hackers could then theoretically easily pivot into other devices on that network and control any connected computer, laptop, phone, tablet, or smart device.
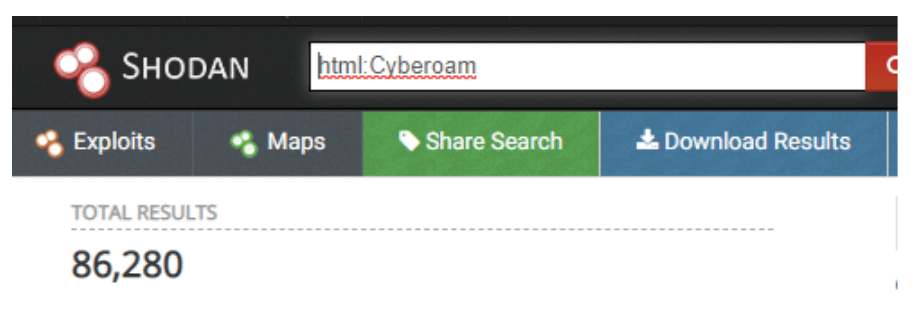
Locating Cyberoam Devices on Shodan
Before going into detail about each individual vulnerability, it’s essential to know how a hacker would identify Cyberoam devices in the first place.
Doing so is quite straightforward, as the information is publicly accessible via the internet search engines like Shodan and ZoomEye.
Shodan and ZoomEye are search engines for internet-connected devices that allow you to see every device or server operating within a network range, and it’s location via an IP address.
Using Shodan, we could easily filter the IP addresses of roughly 86,000 Cyberoam devices. However, we believe this is a small fraction of the actual size of its network as there are many more hidden devices not connected to the internet and under non-default configurations.
*Shodan is just one example of this type of search engine. There are many more tools that provide a similar service without collecting user information. This makes their users harder to track and more popular with criminal hackers.
The First Vulnerability: Unauthenticated Root Remote Command Execution (pre-auth RCE)
This flaw was found in the FirewallOS of Cyberoam SSL VPNs around Q4 of 2019.
This vulnerability allowed access to any Cyberoam device by exploiting its email quarantine release system without needing to know the username and password for the account linked to it. We found many banks and big corporations were using Cyberoam products as a gateway to their network from the outside, so this opened direct access to their intranet (local networks, often with more sensitive data).
Exploiting the vulnerability also allowed relatively easy escalation to ‘root’ access on the device because of its need to run in a privileged setting, which would grant any hacker total control of the target device.
They would then potentially have privileged access to, and potentially control of, the network into which that Cyberoam device was integrated.
This vulnerability was resolved and patched by Cyberoam and Sophos, who automatically installed a regex-based patch into their code to prevent such an attack from happening in the future. However, it was still possible to gain original remote root command execution capabilities due to the second vulnerability in a different parameter.
The Second Vulnerability: Unauthenticated Root Remote Command Execution (pre-auth RCE)
The second vulnerability was noticed sometime after the patch for the first bug came out. This was then brought to our attention by a security researcher who wishes to remain anonymous.
Vulnerable and non-vulnerable Cyberoam devices automatically installed a regex-based important patch to fix the previous RCE. However, this didn’t make it any harder to exploit the second vulnerability. Also, the regex patched used by the first fix would have been insufficient.
Bypassing the Regex Filter with Base64
Base64 is a binary-to-text encoding scheme that converts binary data (made up of 1’s and 0’s) into what’s known as an ASCII string format. It can also be used to perform the opposite function: turning regular command codes into binary sequences of 1’s and 0’s.
By encoding the previous RCE command through Base64 and wrapping it in a Linux Bash Command, a hacker could bypass the patch in Cyberoam’s regex filter and create a more versatile exploit targeting the quarantine email functionality of Cyberoam’s devices.
In fact, unlike the first vulnerability, they didn’t even need an account’s username and password, focusing instead on the request for releasing the quarantine email functionality.
The disguised RCEs could be entered into a blank POST parameter input on the login interface and sent directly to the servers from there.
Once an attacker gains a shell, it's usually game over. The attacker can send unauthenticated root RCE commands and easily pivot into other personal devices by exploiting DNS, SMB, and other local network issues.
Being the most severe form of RCE, it didn’t need any authentication to exploit. It also automatically granted “root” privileges, was highly reliable, and relatively straightforward to exploit.
Hardcoded Default Login Credentials, Discovered by Nadav Voloch
The final issue in Cyberoam’s security protocols was made possible by Cyberoam’s default hard-coded passwords for new accounts.
It seems accounts on the company’s software come with default usernames and passwords, which users are expected to change themselves. For example:
- cyberoam/cyber
- admin/admin
- root/admin
Though the previous vulnerabilities needed no authentication, this vulnerability meant that there was an alternative way to sometimes bypass authentication. Combining the vulnerability in Cyberoam’s FirewallOS with the default login credentials like those we found, you could access any Cyberoam server still in default mode and use this to attack the wider network.
Typically, security software avoids this issue by not using default login credentials and not allowing access to an account until the user creates their own.
Once again, by using Shodan to find Cyberoam devices, hackers could access any account still using the default usernames and passwords mode and take it over.
Using a brute-force attack targeting all Cyberoam’s servers, hackers could easily access any servers still in the default username/password mode at once.
How Many Networks Were at Risk?
We can’t say exactly but can give estimates.
At least 86,000 Cyberoam IP addresses are accessible via Shodan. By our estimates, the real number of potentially vulnerable systems running Cyberoam is likely much much higher. Most devices would be filtered with firewalls, won't be caught with internet search engines, or not connected to the internet 24/7.
Another estimate based on our Fofa.so research returns over 170,000 individual Cyberoam device IPs can easily be found connected to the internet.
Editor’s Note: After sharing our report with Sophos, they stated that numbers are lower, based on their telemetry. “This is an end-of-sale product with end-of-life approaching fast – there are not that many customers or appliances still active.” As our research shows different numbers, we decided to keep them and include the statement from Sophos. They estimate this vulnerability potentially impacted a maximum of 70,000 devices online.
Cyberoam and Sophos’ Response and Resolution
Once we had confirmed the technical details of the vulnerabilities, and Nadav’s later discovery, we contacted Sophos and Cyberoam immediately.
We outlined the nature of each issue, how we discovered them, and how they made networks vulnerable.
Sophos replied promptly and guaranteed the issues would be resolved ASAP.
On February 29th, we received notice from Sophos that they had taken the following steps to ensure the vulnerabilities in their firewall products were resolved:
Between February 24th and 26th, they distributed and automatically applied a hotfix to relevant versions of the Cyberoam firewall. A hotfix is a small piece of code developed to quickly resolve a major software flaw and distribute it wherever necessary.
Sophos’ hotfix completely disabled the vulnerability, and the firewall now requires user authentication at the login portal.
The hotfix will be included in the latest version of the relevant software, to be released soon.
All Cyberoam customers and partners are being notified to advise of the hotfix and the changes mentioned above. They will also be advised to change their admin credentials from the defaults.
The products affected with these vulnerabilities are ‘end-of-sale,’ meaning they’re no longer available for purchase. They will reach end-of-life after the first quarter of 2022 at the latest.
As such, Sophos doesn’t plan to make major programmatic changes in current Cyberoam products that would force customers to change the default credentials.
Two months after Sophos had confirmed the patch was installed, our team attempted the exploits again, following the same processes as before. As the exploit no longer worked on our device, we understood that the vulnerability in Cyberoam’s network had been successfully patched.
Potential Impact
As with any software vulnerability, the dangers were pretty serious. Successful exploitation could have allowed malicious attackers to gain unauthorized access to, and control of, 100,000s potentially sensitive corporate network devices all over the world. The security issues created by the vulnerabilities were easily ‘wormable’ to spread across networks. If someone wanted to, they could have easily automated taking over all Cyberoam servers in a matter of minutes.
Having access to, and control of, an entire network would allow them to commit a massive range of frauds, attacks, and theft:
- Theft of private data
- Network, account, and device takeover
- Manipulating legitimate network packets to be malicious.
Fortunately, we discovered and disclosed these vulnerabilities responsibly to Sophos, who acted quickly to issue hotfixes.
Had these vulnerabilities been discovered by criminal hackers, the impact on networks affected could have been catastrophic.
Potential Impact on Cyberoam
These are just the three most recently known significant security flaws in Cyberoam’s products within the last 8 years. Data security and cybercrime continue to grow as concerns amongst business owners, governments, and the general public.
Finally, had this vulnerability been discovered by criminal or malicious hackers, it could have led to direct attacks on Cyberoam’s network, their partners, and partners’ clients.
This vulnerability has been resolved. However, Cyberoam could still face increased attention from hackers aware of consistent flaws in their security protocols and looking for more flaws elsewhere.
Advice from the Experts
If you or your company are currently using any Cyberoam security device, make sure you have received and installed the latest security patch from Sophos.
Make sure nobody in your network is still using the default login credentials provided by Cyberoam, or you have manually disabled any still in use.
To learn more about data vulnerabilities and security in general, read our complete guide to online privacy.
For a more in-depth guide on how to protect your business, check out our guide to securing your website and online database from hackers.
It outlines the various methods employed by cybercriminals to target internet users, and the measures you can adopt to maintain your online safety.
How We Discovered the Exploit
An anonymous ethical hacker approached us due to our ongoing large scale web mapping project, who reached out to us after discovering the bypass to the previously fixed issue.
When our team is made aware of a data breach or vulnerability, they use cutting edge techniques to verify the nature of any exploit or data leak. We then alert the companies involved in the issue.
As ethical hackers, we’re obliged to inform a company when we discover flaws in their online security. This is the case any time we find a vulnerability. For example, when we tested three of the most popular VPNs in the world and found leaks in every one.
And that is what we did as soon as we were made aware of this bypass. We reached out to Cyberoam and Sophos, not only to let them know about the vulnerability but also to explain how it works.
Sophos quickly replied, and the process to resolve the issue started immediately.
These ethics mean we also carry a responsibility to the public. Cyberoam users must be aware of the previous vulnerabilities that impacted them, as well.
The purpose of our Research Lab is to help make the internet safer for all users.
We do our best to keep sensitive user data private by finding and exposing widespread software flaws like this one.
About Us and Previous Reports

This has included a critical data leak by a popular photo app that exposed 100,000s of American citizens to fraud. We also revealed, through another anonymous hacker, that a mobile payment provider had compromised the diners at restaurants and similar businesses all over the USA. You may also want to read our VPN Leak Report and Data Privacy Stats Report.




Please, comment on how to improve this article. Your feedback matters!