Report: Fieldwork Software Leaks Sensitive Customer Data
vpnMentor's research team found a leak in the Fieldwork software database.
Noam Rotem and Ran Locar, the heads of our cybersecurity research team, found a leaking database belonging to Fieldwork. Fieldwork offers small business software to manage their operations efficiently.
We found a large amount of exposed data in the breach. This included customer names, addresses, phone numbers, email address, alarm codes, signatures, client information, credit card details, photos, and other detailed comments. Most significantly, we found auto-login links that give access to a user's Fieldwork service portal. The implications of this breach are extensive.
We contacted Fieldwork when we discovered the leak. They were professional and efficient after receiving our email. Fieldwork closed the leak 20 minutes after speaking to them.
Examples of Entries in the Database
Fieldwork is a business management platform marketed towards the pest control, lawn care, pool cleaning, and other home service industries. Owned by Anstar, which produces pest control products, the software helps track employees who make house calls. The customer portal also includes invoice templates, scheduling interfaces, and product tracking.
The information leaked in the database included:
- Auto-login links
- Email addresses of users
- Email addresses of their customers
- Full names
- Phone numbers of customers
- Addresses
- GPS locations
- IP addresses
- Emails and texts sent to users or customers
- Billing details
- Full credit card details
- Filtered passwords
- Signatures
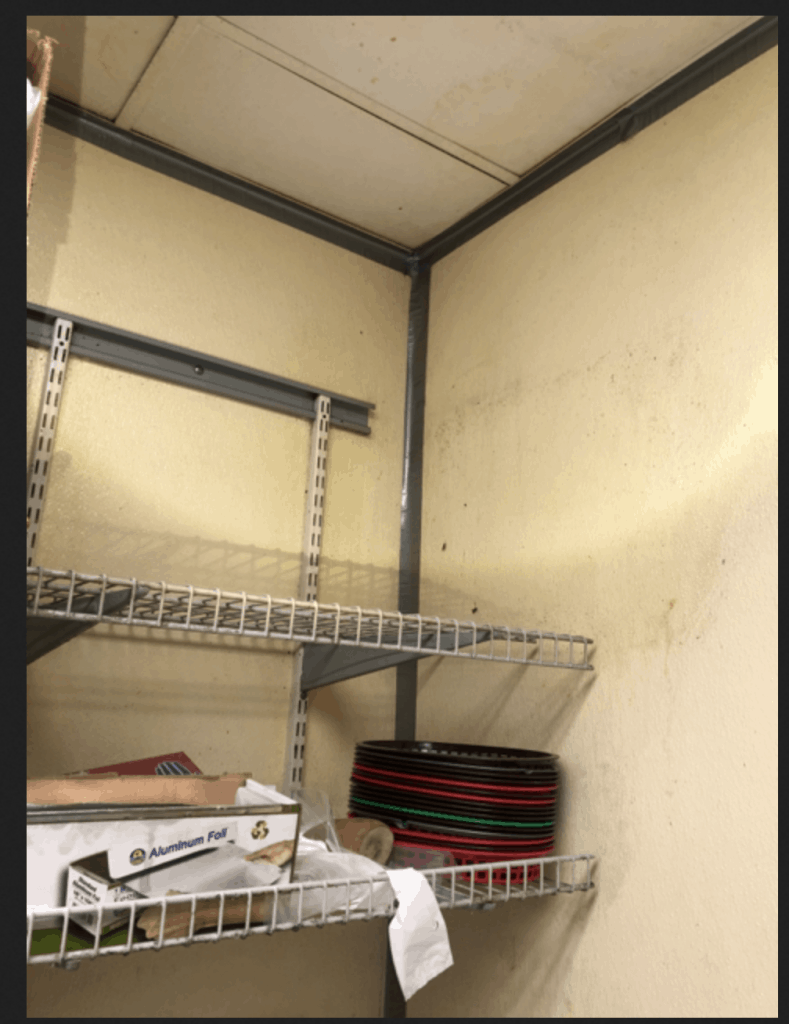
- Pictures of work sites
- Comments or instructions
The most impactful piece of information we discovered in the database was an auto-login link that gave anyone direct access to a company's backend system. Records in the backend included detailed and sensitive client information, as well as an extensive amount of the company's administrative infrastructure.
Much of the information was also present in the database; however, we only saw logs from the last 30 days. Based on the data configuration, the database seemed to store the logs for no more than 30 days before sending them to another system for processing or analysis.
It's possible based on the other information we had in the database that one could have gained access to the backend. Even so, it would have been a more complex project.
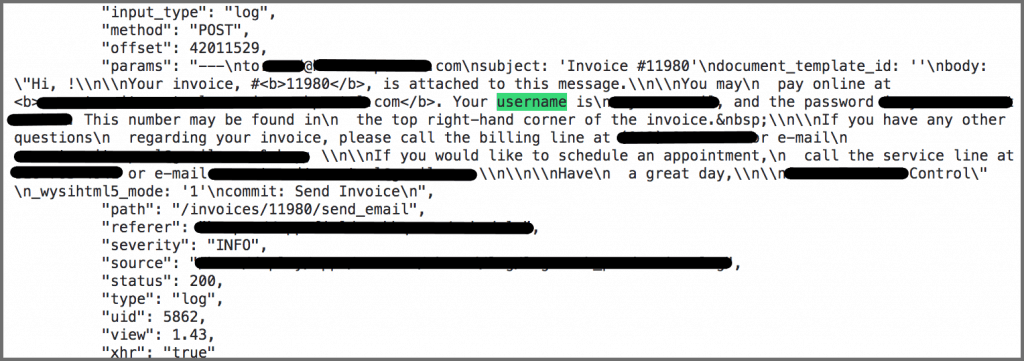
This is a log for an email template about logging in to the Fieldwork portal. This piece of data included email addresses that are not publicly available for clients to see. Though the password isn't given outright here, it left open the possibility of finding relevant information in other parts of the database.
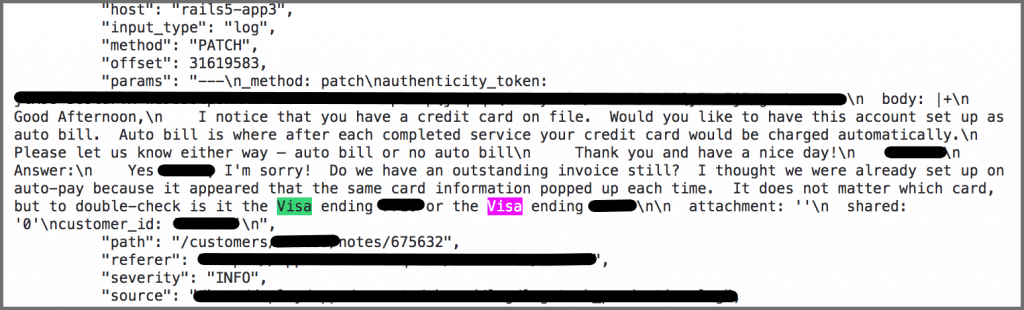
We found an extensive amount of detailed communication in the data logs. This email looks like it was sent from a pest control company that uses Fieldwork's software to a client of the company. The client disclosed the last four digits of their account credit card.
It’s a standard verification process that could have a negative impact based on the specificity of other data in the leak. A bad actor could have used this to their advantage.
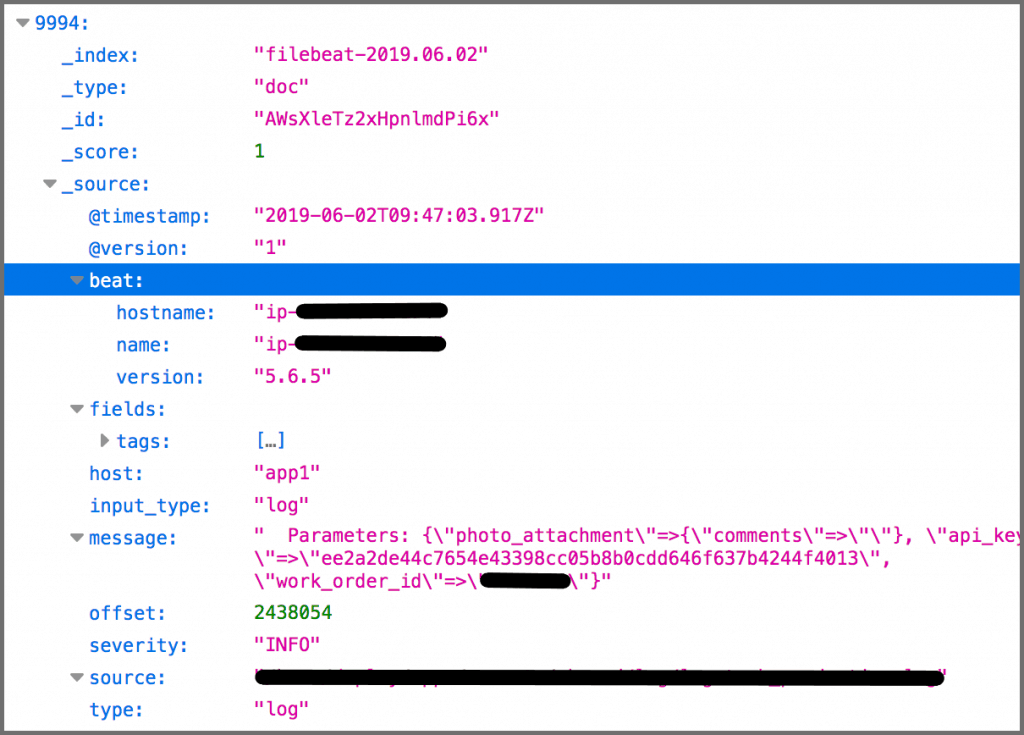
This log shows that there are also photos accessible in the data. It also exposed a user's IP address.
This photo was linked in an open Amazon bucket that we discovered in the data.
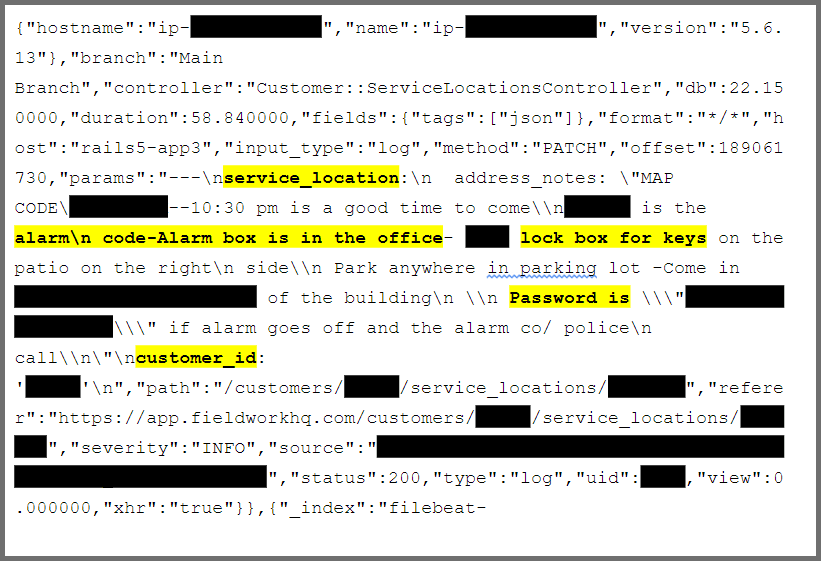
This communication log not only says what time the appointment is but also includes specific instructions for getting in the building. This includes multiple alarm codes, lock box codes, and passwords that were disclosed by the client. We found other logs that included comments on where clients hid their keys.
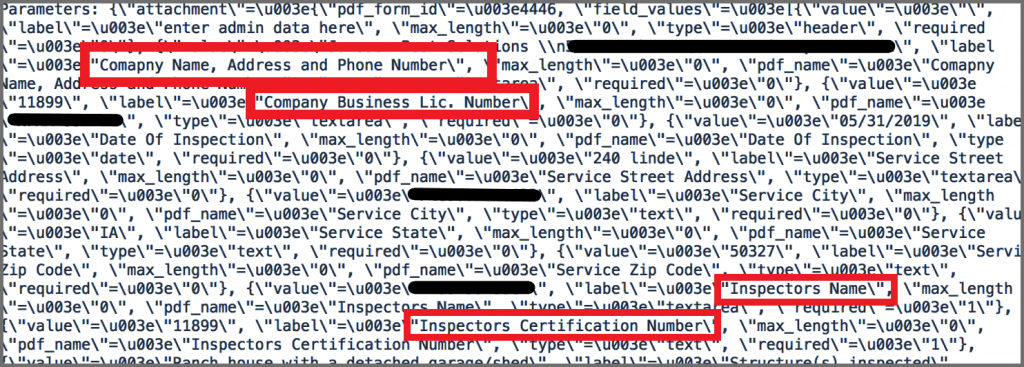
Many of the companies that use Fieldwork have public addresses, but this data also gives information about their clients that companies wouldn't disclose to the public. It also provides the company's license number.
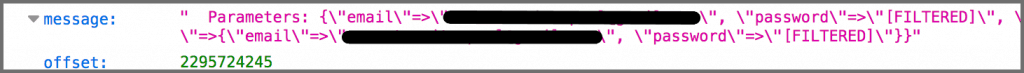
This log does hide the password, but it gives us clear email addresses associated with an account. Based on information in other records, it's possible that a bad actor could still access the missing credentials.
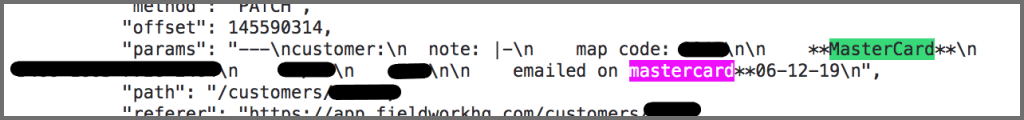
Even without any customer identification, the full credit card number, with an expiration date and a CVV number was visible.
Data Breach Impact
There was an extensive amount of information included in the data, even if only 30 days of logs were available. Though Fieldwork filtered passwords in some places, some of the templates that we viewed gave detailed information about finding account credentials. We also had free access to an auto-login link that was included in the database. This allowed access to the customer portal.
Access to the portal is a particularly dangerous piece of information. A bad actor can take advantage of that access not just by using the detailed client and administrative records stored there. They could also lock the company out of the account by making backend changes. Even if there were authentication steps involved in changing login information, it's possible that some of this information was present in the open database.
Furthermore, if the login links were easy to organize, someone with malicious intent could easily save them. In that case, it wouldn't matter if the database were closed. They would still have direct access to a large number of accounts. Saving the other account credentials in the database was always a possibility, but it would be a more time-consuming and challenging task. Access to the backend portal means someone could open a company's records at any time, even after Fieldwork fixed the breach.
There is a significant amount of location data logged in the database, which, combined with the portal access, has severe consequences. This opens up the possibility of in-person theft or attacks. Not only do we have business addresses and GPS coordinates, but we have also detailed descriptions of how to enter a building or office. Because clients openly disclosed alarm codes or how to access their keys, there could be insurance consequences as well. Insurance companies could void a policy if policyholder negligence caused a break-in.
The photos that were viewable in the Amazon photo bucket could have served as further confirmation of a location. They also may have disclosed that a client had valuable inventory. With the location information, a thief could break in undetected and make off with client stock.
If any of these attacks had occurred based on the data breach, it would profoundly impact the companies who relied on Fieldwork for building their businesses. For starters, a breach could undermine their clients' trust. This could lead to clients employing a competing company that didn't use leaky software to protect themselves better.
With unfiltered credit card information logged in the database and in the portal, it's too easy for a malicious player to run up fraudulent charges on these credit cards. Credit card companies require sensitive card data to be strongly encrypted while a CVV number shouldn’t be stored after authentication as per PCI regulations. We had access to all of the credentials needed to place a purchase or even copy a card. In the data we did find, it was unclear whether these card numbers belonged to the companies using Fieldwork or to their clients. However, portal access makes it simple to determine.
Outside of direct portal access, the credentials we did have could also have an impact outside of the Fieldwork account. Credentials from one account can often be used to access another account. When we have full names and addresses, we can build a picture of a user. A bad actor can take this information to gather more data. They could then use this information to steal a person's identity. Some could even open new accounts in a user's name.
One danger of exposing email addresses involves malicious players using them for phishing attacks. If a company's client list can be viewed along with the company email address, it is even easier to fool clients into opening an email that includes malware. This can give hackers direct access to a system that had no connections to this open database. Companies have a moral obligation to keep their clients' data secure. In this case, any company using Fieldwork did not uphold this.
When hackers can infiltrate a system, they have a lot of options open to them. Shutting down operations will cost the company significant amounts of money. A hacker could also sell stolen data to a competing company. Fieldwork markets its products to small businesses, which have fewer financial resources available if they're shut down by a hack.
Lastly, we discovered signatures in the data. By copying the shape of a signature, a bad actor has yet another tool to commit identity theft through forgery. Most digital signatures link to an IP address. However, if we have all of a user's credentials, including credit card number, IP address, and signature, the task of forgery is simplified.
Advice from the Experts
There are a few simple steps Fieldwork could have taken to protect its database from the start. Here are a few expert tips to prevent or patch a breach in a database.
- Secure your servers.
- Implement proper access rules.
- Never leave a system that doesn’t require authentication open to the internet.
For a more in-depth guide on how to protect your business, check out how to secure your website and online database from hackers.
How We Discovered the Breach
In the comprehensive web-survey project carried out by our research team, they discovered a data breach. Led by Ran and Noam, the group performs scans of known IP blocks' ports. This enables them to search for vulnerabilities in the system. Once they locate a leak, they leverage their substantial expertise in cybersecurity to verify the identity of the compromised database.
Each time we discover a breach, we contact the owner of the database to alert them to the leaking data. If possible, we will also inform others affected by the openings in the system. Our goal with this project is to create a safer and more secure internet for users everywhere.
About Us and Previous Reports

We recently discovered a massive data breach impacting 78 thousand patients taking Vascepa. We also revealed that xSocialMedia suffered a widespread data breach. You may also want to read our VPN Leak Report and Data Privacy Stats Report.
Please share this report on Facebook or tweet it.



Please, comment on how to improve this article. Your feedback matters!