Report: Ghana Government Agency Exposes 100,000s of Citizens in Massive Data Breach
Led by Noam Rotem and Ran Locar, vpnMentor’s research team discovered a data breach related to Ghana’s National Service Secretariate (NSS).
The NSS is a government program managing a mandatory year of public service for graduates of certain educational institutions in Ghana. Every year, thousands of students join the program from across the country to work in various public sectors, including healthcare.
The NSS was using Amazon Web Services to store over 3 million files from its programs. Despite password protecting some of the files in its cloud storage account, simple oversights by whoever created the account and uploaded and organized the files on the S3 bucket made this insufficient, and many files were still exposed.
As a result, up to 700,000 people from across Ghana were exposed to fraud, hacking, and identity theft - not to mention the dangers posed to the institutions they were working at and the Ghanian government itself.
Data Breach Summary
| Company/Org. | Ghana's National Service Scheme |
|---|---|
| Headquarters | Accra, Ghana |
| Industry | Public Sector |
| Size of data in gigabytes | Approx. 55 GB |
| Suspected no. of files | 3,814,795 |
| No. of people exposed | Most likely 500,000-600,000; Potentially up to 700,000 |
| Date range/timeline | March 2018 - present |
| Geographical scope | Ghana |
| Types of data exposed | PII data; ID cards; employment and educational records; much more |
| Potential impact | Phishing; fraud; ransomware; anti-government dissent and misinformation; extortion |
| Data storage format | Misconfigured AWS S3 bucket |
What is Ghana’s National Service Secretariate?
The National Service Secretariate (or National Service Scheme, NSS) was established to promote the development of Ghana’s public and private sectors.
The NSS is a one-year mandatory national service that all graduates of accredited tertiary learning institutions in Ghana are legally required to perform. Every year, 10,000s of graduates in Ghana are to serve for 12 months in various sectors, primarily within the public sector, such as healthcare, transport, and education.
Timeline of Discovery and Owner Reaction
- Date discovered: September 29th, 2021
- Date vendors contacted: October 6th, 2021
- Date of 2nd contact attempt (if relevant): October 12th, 2021
- Date CERT-GH contacted: October 7th, 2021; October 12th, 2021 (replied the same day)
Sometimes, the extent of a data breach and the owner of the data are obvious, and the issue is quickly resolved. But rare are these times. We often need days of investigation before we understand what’s at stake or who’s exposing the data.
Understanding a breach and its potential impact takes careful attention and time. We work hard to publish accurate and trustworthy reports, ensuring everybody who reads them understands their seriousness.
Some affected parties deny the facts, disregarding our research or playing down its impact. So, we need to be thorough and make sure everything we find is correct and accurate.
In this case, the NSS was using an Amazon Web Services (AWS) S3 bucket to store data collected from the public through its various activities. S3 buckets are an increasingly popular enterprise cloud storage solution. However, users must set up their security protocols manually to protect any data stored therein.
While the NSS had password-protected many documents stored on the S3 bucket, the bucket itself was left completely open, leaving the contents totally exposed and easily accessible to anyone with a web browser and technical skills.
Furthermore, due to a major oversight by whoever was in charge of organizing the documents, the password protection ended up being useless since other files with the same data were accessible in another folder in the same bucket.
Finally, many of the documents contained the NSS logo and text directly related to the scheme. Once we confirmed that the NSS was responsible for the data breach, we contacted the agency to notify them and offer our assistance. However, we never received a reply from the NSS.

We also reached out to Ghana’s Computer Emergency Response Team (CERT-GH) twice. The second time, they replied the same day requesting more information about our discovery. After disclosing the situation to them, CERT-GH replied:
"My team has verified and confirmed the vulnerability. A report has been prepared and shared with the CERT coordinating Gov Agencies incidents. We will be following up to ensure that the issue is resolved ASAP.”
We followed up several times to the Ghana's CERT, but never received a replied back. We also reached out to the Ghana's government, unfortunately without success.
We followed up several times to the Ghana's CERT, but never heard back from them again. We also reached out to the Ghana's government, unfortunately without success.
Example of Entries in the S3 Bucket
In total, there were over 3.8 million files stored on the NSS’s S3 bucket.
The NSS took steps to protect peoples’ identities by password-protecting sensitive files within the S3 bucket. However, this was done haphazardly and inconsistently, and ended up being inefficient, as those same files were exposed elsewhere in the bucket.
Different file types were stored across individual folders to keep them apart. But as we’ll demonstrate, this wasn’t enough to protect peoples’ data.
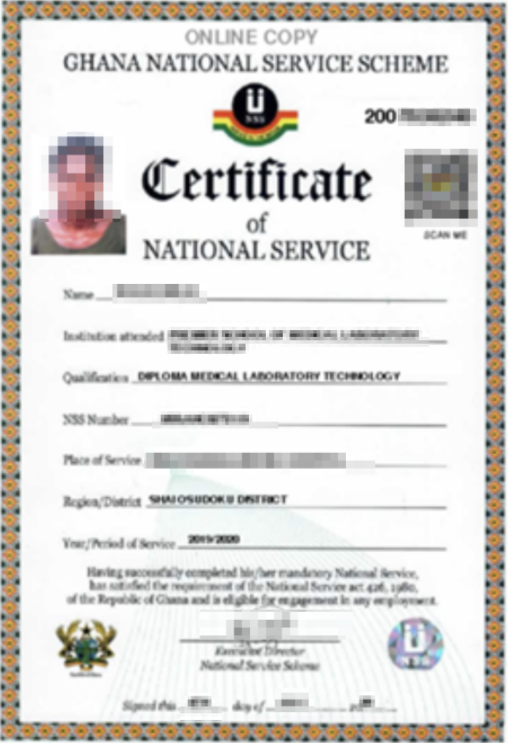
NSS Certificates PDF Files - 60+ certificates Accessible (330k+ password-protected and inaccessible)
One folder in the S3 bucket contained 330,000+ individual certificates for people who had completed the NSS. Each one was stored as an individual PDF file.
60+ of these PDF files were completely unprotected. 330,000+ were secured via passwords.
However, as we’ll explain below, the password protection may have been useless due to QR codes leading to the same files stored elsewhere.
Each unprotected certificate contained a massive amount of data about the person exposed, including:
- Personal photos
- Full names
- Institutions attended
- Qualifications
- NSS no.
- Place of residence
- Period of service in the NSS
For ethical reasons, we didn’t try to open the password-protected files, but we assume they all contained the same information.
QR Codes - 749,000
In a separate folder, the NSS was storing 749,000 QR codes that, when scanned, produced a URL that led directly to unencrypted certificates (similar to the one above). These QR codes were not encrypted or password-protected in any way.
For security and ethical reasons, we only scanned a sample of the QR codes, so we can’t confirm if these were the certificates of the same people mentioned above, or a completely new set, thus exposing an additional 749,000 people.
Archived Documents - 1,700+
Various documents were archived data. Most of these files were not recent and had no password protection or encryption. These included:
- Correspondences between various parties within the NSS
- Employment notices (including salary notices)
- Payment receipts
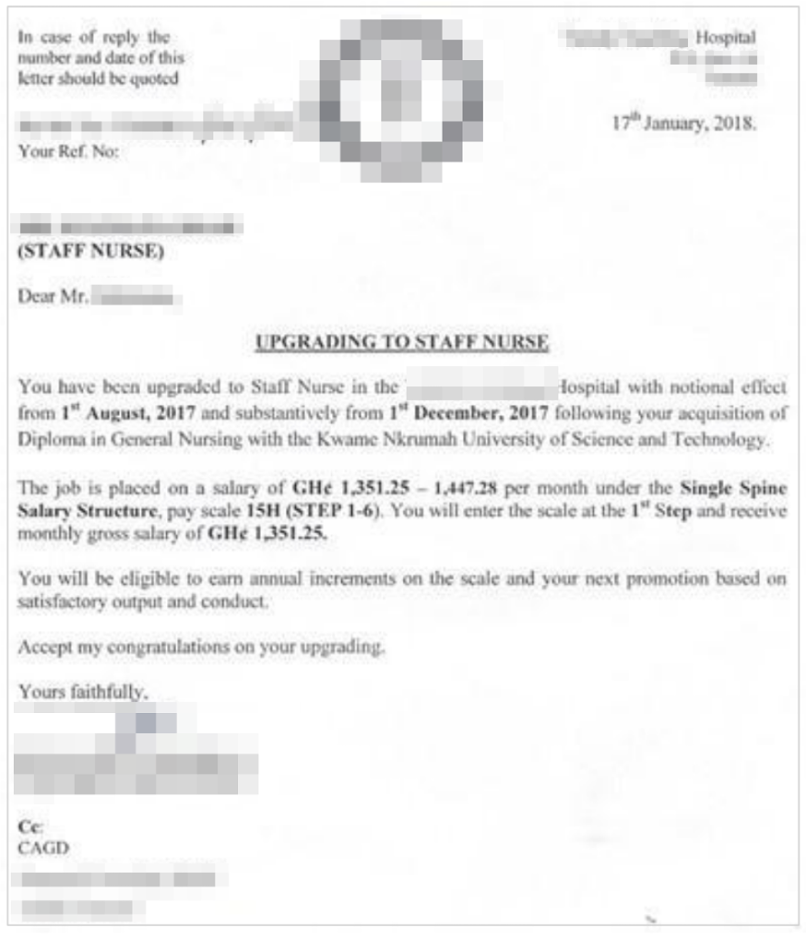 Salary notice, equivalent to $222.79 - $238.62
Salary notice, equivalent to $222.79 - $238.62
 Caption: receipt for $73.79
Caption: receipt for $73.79
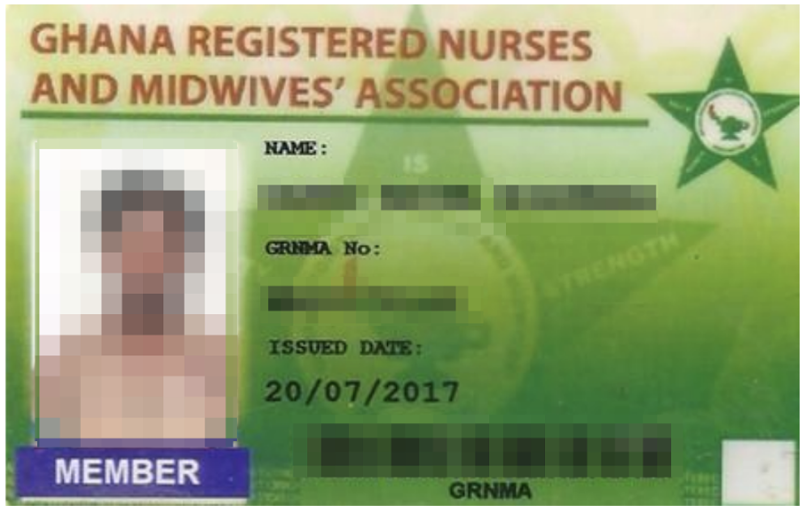
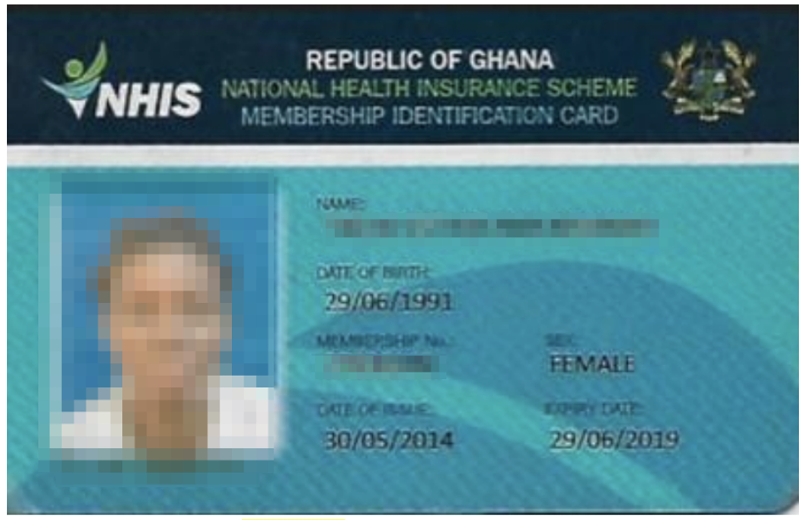
ID cards - 12,000+
The NSS was also using the S3 bucket to store IDs and program membership cards from participants. These included government IDs, such as the Ghana National Health Insurance Scheme, and professional IDs, most likely based on a person’s placement in a certain industry (i.e., working as a nurse or midwife).
Potentially more were stored in other folders.
Passport Photos - 912,000
The NSS was storing different types of passport photos submitted by participants with varying degrees of protection installed.
The breakdown is as follows:
27,000 regular passport photos - password protected
865,000+ biometric passport photos - unprotected
Monthly Evaluations - 2 CSV Files (35 MB)
These two CSV files contained over 43,000 unique records from participants of the NSS between 2018 and 2020.
There was no password protection or encryption on the files. Some of the records included the monthly payments being made to participants, their full name, the position they were assigned to (with location), NSS number, and much more.
Unmarked Files - 30,000
Finally, the S3 bucket also contained a document dump with a mix of different files types all stored together with no organization or protection. These included biometric passport photos, ID cards, and other documents uploaded by staff at the NSS.
Data Breach Impact
This data breach represents a serious risk to the government of Ghana and 100,000s citizens across the country.
For The Ghanaian Government and The NSS
Had this data breach been discovered by malicious or criminal hackers, it could have been a devastating blow to the government of Ghana. By leaking private data belonging to up to 700,000 of its citizens, the government risked a massive backlash from the public.
Across the globe, cyberattacks are increasing, and the general public is becoming much more aware of the dangers. Concurrently, in many countries, trust in the government is deteriorating rapidly, often fueled by online misinformation, disinformation, conspiracy theories, and the COVID-19 pandemic.
Hopefully, this data will remain out of criminal hands. Still, if news of the breach spreads far enough and becomes distorted in any way, the Ghanian government will be held responsible by its citizens for putting them at risk. This could also lead to broader distrust in the government, if citizens - along with partners like businesses and other governments - grow skeptical about its data protection policies and reluctant to provide any private data for fear of it being leaked.
Aside from the reputational damage caused by the data breach, both the individuals affected and the government and the NSS could also face serious security risks as a result of phishing campaigns based on the data exposed.
In a phishing campaign, criminals send victims fake emails and text messages imitating real businesses and organizations. By building the victim’s trust, they hope to trick them into any of the following actions:
- Providing additional PII data (i.e., social security numbers) or private information (i.e., bank account details) that can be used in the fraudulent activities listed above.
- Inputting debit or credit card details into a fake payment portal, so they can be scraped and used by criminals or sold on the dark web.
- Clicking a link embedded with malicious software that infects a user’s device, such as malware, spyware, and ransomware.
In the case of a government or similar entity, they could convince an employee to accidentally provide access to an otherwise secure area of a government network, or click a link that allows hackers to access an entire network. They could then plant spyware, ransomware, or similar viral software that takes down an entire branch of the Ghanaian government or public infrastructure. Or simply spies on the government undetected.
Attacks like these are becoming increasingly popular, often orchestrated by rival or antagonistic governments, and exploiting the general lack of education around cybersecurity in the workplace.
Furthermore, hackers could use the NSS assets stored in the open S3 bucket, such as logos and letter templates, to create highly effective phishing attacks due to the presence of correspondence between NSS staff and participants. It would only take one employee uneducated in spotting fake emails to compromise an entire network by clicking a malicious link.
For NSS Participants
Had malicious or criminal hackers discovered the NSS’s AWS account before it was secured, they could have used the exposed data in a wide range of criminal schemes.
The exposed data would have been enough for skilled hackers to commit many of the most common forms of fraud, including:
- Identity theft
- Tax fraud
- Insurance fraud
- Mail fraud
- Bank account takeover
- Debit or credit card fraud
- Mortgage fraud
- Many more...
However, even if the exposed data wasn’t sufficient to exploit for criminal gains, it could also be used to carry out complex phishing campaigns targeting individuals exposed in the breach.
While not as severe as a successful phishing attack against a government, if an individual is successfully tricked, it can destroy their livelihoods.
Furthermore, much of the data exposed in this breach is permanent and can never be changed. For example, the victim of a hack can change their phone number, credit card, and email address. However, you can’t change the high school you graduated from, your social security number, or personal details like your gender and date of birth.
Once this information is out in the open, it can be used against you repeatedly for the rest of your life.
The risks of a successful phishing attack are heightened in this case, as many people involved will now be working at medical facilities. Such facilities are considered high-value targets by cybercriminals, who can demand high ransoms by threatening to disrupt patient care, destroy records, and inflict devastating, potentially fatal damage. Cyberattacks on hospitals and medical institutions have been on the rise in recent years as a result.
Due to the number of people exposed in this data breach, cybercriminals would only need to successfully scam a small fraction for any criminal scheme to be considered successful.
Advice from the Experts
If the NSS had implemented some fundamental security measures, it could have readily prevented the exposure of its participants' data. These measures encompass various basic security practices, including but not limited to:
- Secure its servers.
- Implement proper access rules.
- Never leave a system that doesn’t require authentication open to the internet.
Any company can replicate the same steps, no matter its size.
For a more in-depth guide on how to protect your business, check out our guide to securing your website and online data from hackers.
Securing an Open S3 Bucket
It’s important to note that open, publicly viewable S3 buckets are not a flaw of AWS. They’re usually the result of an error by the owner of the bucket. Amazon provides detailed instructions to AWS users to help them secure S3 buckets and keep them private.
In this case, the quickest way to fix this error would be to:
- Make the bucket private and add authentication protocols.
- Follow AWS access and authentication best practices.
- Add more layers of protection to the S3 bucket to further restrict who can access it from every point of entry.
For NSS Participants
If you’re a participant in the NSS and are concerned about how this breach might impact you, contact the department directly to find out what steps it's taking to protect your data.
To learn about data vulnerabilities in general, read our complete guide to online privacy.
It shows you the many ways cybercriminals target internet users, and the steps you can take to stay safe.
How and Why We Discovered the Breach
The vpnMentor research team discovered the NSS’s data breach as part of a huge web mapping project. Our researchers use large-scale web scanners to search for unsecured data stores containing information that shouldn’t be exposed. They then examine each data store for any data being leaked.
Our team was able to access this S3 bucket because it was completely unsecured and unencrypted.
Whenever we find a data breach, we use expert techniques to verify the owner of the data, usually a commercial business.
As ethical hackers, we’re obliged to inform a company when we discover flaws in their online security. We reached out to the NSS and Ghanaian government, not only to let them know about the vulnerability but also to suggest ways in which they could make their system secure.
These ethics also mean we carry a responsibility to the public. NSS users must be aware of a data breach that exposes so much of their sensitive data.
The purpose of this web mapping project is to help make the internet safer for all users.
We have no evidence or way of knowing whether the data in our reports have been accessed or leaked by anyone else; only the database owner can know that.
We do our best to prevent this from happening by reaching out to the companies and ensuring they secure their leaking database as soon as possible.
We never sell, store, or expose any information we encounter during our security research.
About Us and Previous Reports

This has included exposing the growing popularity of cybercrime groups on Telegram. We also revealed how a popular Chinese game developer was leaking data from over 1 million people. You may also want to read our VPN Leak Report and Data Privacy Stats Report.




Please, comment on how to improve this article. Your feedback matters!