SecureMySocial – Making Sure You Never Share Something That You Shouldn’t
- You have established yourself as an expert and thought leader in many different aspects of security. Please tell me a little bit about yourself and your background.
- Unlike most other security products that focus on protecting businesses from outsiders, SecureMySocial focuses on protecting businesses from their own employees.
- Please give me an overview of your product.
- How do these features translate into benefits?
- Is SecureMySocial currently available? What is the pricing?
- Whom do you see as your main competitors and how do you see your tools as different and/or better than theirs?
- You recently wrote an article for Inc. titled “How Posting On Facebook About 10 Concerts You Attended Can Get You Robbed.” I guess that is a perfect example of the type of things you are targeting – right? Can you explain what the threat is and how your software can prevent it?
- What are your top three tips for safety on social media – for both businesses and individuals?
- What do you expect to be the major changes in the security world in the next few years?
- What are your future plans for SecureMySocial?
- How many hours a day do you normally work? What do you like to do when you are not working?
Most of us are too busy having fun on social media to recognize the many dangers that lurk there. We have gotten into the habit of sharing everything, which could easily lead to significant information falling into the wrong hands. This is true both for our personal information as well as for confidential company information.
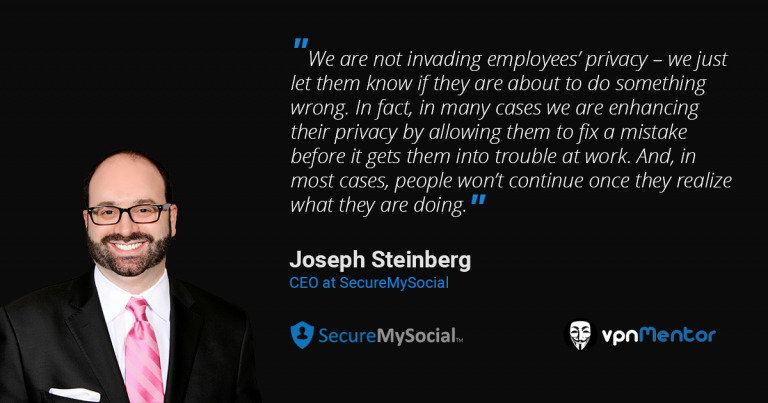
Joseph Steinberg, the CEO of SecureMySocial, explains what are the types are “bad” posts that are often shared on social media and how his company’s product can both prevent the damaging posts and also train employees for the future.
You have established yourself as an expert and thought leader in many different aspects of security. Please tell me a little bit about yourself and your background.
I have been in the information security space for almost 20 years. In 2005, in conjunction with human factors expert, Shira Rubinoff, I started my first company, Green Armor, which provides online authentication software.
I started writing on the info-security field in 2000, and, since 2012, I have been a regular columnist, first for Forbes, and later for Inc.
A few years ago, I perceived changes occurring in social media and I began working on a solution about which I filed several patents; Those patents formed the basis of SecureMySocial.
Unlike most other security products that focus on protecting businesses from outsiders, SecureMySocial focuses on protecting businesses from their own employees.
Yes, that is true, but in addition to protecting company data and reputation, we also protect employees from making all sorts of other mistakes.
We are not invading employees’ privacy – we just let them know if they are about to do something wrong. In fact, in many cases we are enhancing their privacy by allowing them to fix a mistake before it gets them into trouble at work. And, in most cases, people won’t continue once they realize what they are doing.
Please give me an overview of your product.
The biggest problem with social media today is the oversharing of information. This includes both company data as well as personal data.
The goal of the SecureMySocial platform is to protect both employers and employees from the damage that could occur because of inappropriate posts on social media. We also protect employees from ruining their professional lives and/or personal relationships.
Our system protects against many different types of posts, including:
- Inappropriate
- Corporate Data
- Compliance violations
The system comes with Standard Rules (e.g. not leaking email addresses, not sharing that you are far from home, etc.), Business Rules (protecting against all sorts of risks to a business), and Ignore Rules (allowing exceptions to general rules).
Businesses can also define their own custom rules.
How do these features translate into benefits?
Our approach provides three main forms of value:
- Reduce the number of social media incidents that need to be dealt with.
- Provide a better defense for employers if something does go wrong, (e.g. regulatory issues or employee termination due to social media activity).
- Really train people what not to do on social media – not just provide general policies and platitudes.
Our software also delivers another big benefit. We can use our data collection and analysis for early warning signals (e.g., someone overshared information that may lead to spear phishing attacks, someone shared a cell number that is being used for multi-factor authentication, etc.) and other security functions, which can be shared with other security tools an organization may already have in place.
Is SecureMySocial currently available? What is the pricing?
Yes. Although we just recently started selling the product, we filed our first patents five years ago before people realized the significance of the problems that we solve. SecureMySocial is sold on a per user per year basis, based on the number of users in the organization.
Whom do you see as your main competitors and how do you see your tools as different and/or better than theirs?
We mainly compete with existing social media monitoring tools.
We have three main differentiators:
- We are not a proxy. Our software lives in the cloud and talks directly to the social media platform(s) via their native API. This allows us to protect users outside of the office as well. Wherever someone is, and whatever device he or she is using, we can still deliver security.
- We respond in real-time. For example, our auto-delete features.
- We can address semi-public posts – e.g., a post set to Friends-of-Friends visibility where millions of people may see it, but yet many social media monitoring tools will not.
- We have an issued US Patent on what we do, and more patents in progress.
You recently wrote an article for Inc. titled “How Posting On Facebook About 10 Concerts You Attended Can Get You Robbed.” I guess that is a perfect example of the type of things you are targeting – right? Can you explain what the threat is and how your software can prevent it?
Sharing info about concerts you have attended could help criminals social engineer someone, and may even give clues as to how to answer challenge questions used by some sites for authentication. SecureMySocial can warn people in real time if they make the problematic concert posts.
What are your top three tips for safety on social media – for both businesses and individuals?
I think that the three most basic things to remember in order to stay safe on social media are:
- Be aware of what you are doing
- Use multi-factor authentication and strong passwords -- and do not reuse the passwords on any other sites
- Do not accept friend requests (or linkedIn connections) from people you do not know. (Please see my article entitled “How to Be Better at Social Media Than Mark Zuckerberg” for more suggestions https://www.inc.com/joseph-steinberg/how-to-be-better-at-social-media-than-mark-zuckerberg.html
What do you expect to be the major changes in the security world in the next few years?
- The Internet of Things (IoT) is a big issue and to be addressed properly will require substantial changes in multiple areas.
- Artificial Intelligence (AI) will be used increasingly more in the battle against hackers – and by hackers against organizations.
- We will see a lot more efforts and tools to address security issues on social media. We are still in the early stages of dealing with it.
What are your future plans for SecureMySocial?
Currently, our focus is solely on catering to the security needs of businesses. However, we have exciting plans to broaden our scope and encompass additional scenarios, such as catering to the security requirements of parents and individuals.
For example, today’s parental control software is often doomed to fail, because it essentially requires parents to spy on their children. Our approach is one of self –monitoring, where the children are warned if they are about to do something wrong. This creates a better feeling for the kids, makes them more compliant, and helps them to understand what is right and what is wrong.
How many hours a day do you normally work? What do you like to do when you are not working?
Too many hours, but at least they are flexible hours, so that I can still spend good amounts of time with my wife and three daughters. Nevertheless, the truth is that I really enjoy the work and the writing that I do.



Please, comment on how to improve this article. Your feedback matters!