ThreatMetrix – A Global Identity Network of Users, Machines, and Behaviors
- Let’s talk a little bit about your background. You founded a security company that was later acquired by ThreatMetrix – correct?
- In describing your platforms and products on your web site, you talk about roles, rather than features or benefits. Why is that?
- What are the essential features of your platform?
- How do you price your services?
- How do you define your market? Who is your specific target audience within that market?
- Who do you see as your main competitors?
- How many active customers do you have today? Where are they mainly located?
- You are the VP for the Asia Pacific region. How would you describe that market? How is it different from the North American and European markets?
- In addition to your software products, you also offer both training and professional consulting services. What percentage of your customers takes advantage of them? What percentage of your overall revenues comes from these services?
- How do you see the security software market evolving in the next few years?
- What are some future plans for ThreatMetrix?
- How many employees do you have today? Where are they located?
- How many hours a day do you normally work? What do you like to do when you are not working?
- Is there anything else you would like to share with our readers?
When a user visits your company’s website to make a purchase or to apply for an account, how do you know that they are in fact who they claim to be? Are they using a stolen identity or spoofing an existing one? Just about every business today needs to ask these questions, in order to avoid monetary (or other) losses due to identity fraud.
Ted Egan, the Vice President for Asia Pacific at ThreatMetrix, explains to us how his company’s global identity network collects and analyzes data in order to help businesses reliably confirm (or deny) the identity of visits/users on their web sites. He also shares with us some thoughts on the future of the security software market and on the challenges of dealing with customers all around the world.
Let’s talk a little bit about your background. You founded a security company that was later acquired by ThreatMetrix – correct?
In 2005, I co-founded a company called TrustDefender, where we developed a platform for identifying malware and securing mobile devices. We originally started in the Australian credit union space, which was facing serious problems. However, three months after we launched in Australia, we started getting calls from large organizations in the US.
In 2011, we merged with ThreatMetrix. We already knew each other and our product paths were converging, so it really made a lot of sense for both companies.
In describing your platforms and products on your web site, you talk about roles, rather than features or benefits. Why is that?

What we have found is that if we just talk about features, we tie ourselves up in knots. While features solve problems, they often create other problems and you do not always see how to solve the overall problem(s). We try to provide a single view and to describe the problems we solve, using these roles and use cases:
- Cybersecurity
- Digital Experience
- Executive Leadership
- Fraud Management
- Mobile Business
What are the essential features of your platform?
Digital businesses need a comprehensive and layered approach to confirm the identity of a user or a new account applicant. Relying on static identity data alone, as is common today, is ineffective, since it can be easily stolen or spoofed by fraudsters.
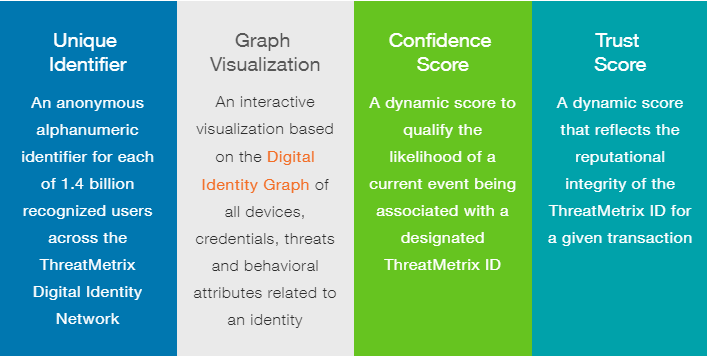
We have created a global digital identity network. We authenticate logins as soon as a user comes to a web site. We do this on multiple levels – user, device, and behavior. Every day, we handle more than 70 million transactions, so we have a lot of data on users and devices. Of course, we tokenize this data, so that there is no personally identifiable information. Based on all of our collected data, we calculate both a confidence score and a trust score for the current user and event.
Our Digital Identity Platform is delivered as a SaaS (Software as a Service) that delivers a real-time experience for our customers. It addition to its core technology and functionality, we also provide a set of APIs (Application Programming Interfaces) that make it very easy to integrate with other devices and applications.
We believe that customers – and their executive management – should have full control of their destiny, so we are very open and do not adopt a black box approach to our platform. Our customers decide and implement their own policies, benchmarks, etc.
We also offer an additional product, our Dynamic Decision Platform, in order to address the needs of large enterprises. These large organizations, such as banks, want real-time analytics, machine learning, and the ability to integrate with other vendor solutions.
How do you price your services?
We have a transaction-based pricing model, where organizations buy blocks of transactions on an annual basis. They are also required to purchase an annual support and maintenance contract.
Just to give you a rough idea, it would cost a small business or startup about US$20,000 per year to get started, and then increase from there as the company grows.
How do you define your market? Who is your specific target audience within that market?
Our traditional market is the eCommerce market, where fraud is a real problem. This market is the basis for our growth in the US (which we entered in 2008). Our fastest growing market today, and possibly already our largest overall market, is banks and peer-to-peer loan providers. As you can well imagine, this market also struggles greatly with customer identity and fraud issues.
We are also seeing great interest and are making headway in the social media space.
Who do you see as your main competitors?
We don’t really talk about competitors. Clearly, our competitors are everywhere. If you are looking for a standalone, point solution, there are plenty of options out there. However, if you want a more comprehensive solution, go with ThreatMetrix and then integrate specialty solutions into it.
We are integrating many of our competitor products into our platform and are seeing large enterprises also integrating our competitors’ products in their ThreatMetrix infrastructure.
How many active customers do you have today? Where are they mainly located?
We current have about 5,000 direct customers. However, beyond that, we have some partners that incorporate our platform for thousands of their customers.
We now have customers in almost every one of the existing 242 countries/territories. Having said that, most of our customers are located in four main areas:
- Asia Pacific, Australia, and New Zealand
- Europe (both eastern and western)
- Middle East
- US and Canada
You are the VP for the Asia Pacific region. How would you describe that market? How is it different from the North American and European markets?
Every market is culturally different. Even the Asian market breaks down into distinct countries and cultures:
- China and Hong Kong
- Korea and Japan
- Southeast Asia
- Philippines, Singapore, Thailand, and Indonesia
- India, Pakistan, and Sri Lanka,
- Australia, New Zealand, and Fiji
In order to better address cultural differences, we support many markets via local partners.
In addition to your software products, you also offer both training and professional consulting services. What percentage of your customers takes advantage of them? What percentage of your overall revenues comes from these services?
Yes, we do offer optional professional services, but I can’t really talk to percentages, because it is something of a moving target. Bigger companies are using professional our professional services more and more, but smaller companies do not really need them, since they are just using the basic features of our platform.
How do you see the security software market evolving in the next few years?
We see an increasing emphasis on digital identity and behavior, but we are still in the early days of tracking and managing this data.
We also see that the attacks on systems are getting more sophisticated all the time. Moreover, the techniques being used to hide and spoof identities are also getting more sophisticated.
What are some future plans for ThreatMetrix?
We are going to continue building our digital identity network, mapping both human and machine identities, on a global basis. We are expanding to provide our services across different types of businesses and transactions.
We firmly and sincerely believe that we can make a real difference in protecting customers and businesses around the world, every day.
How many employees do you have today? Where are they located?
With a current workforce of more than 240 individuals, we continuously strive to maximize automation in our operations. Our dedicated employees are spread across various global locations, encompassing London, Paris, Amsterdam, Hong Kong, Singapore, Sydney, San Jose, and New York.
How many hours a day do you normally work? What do you like to do when you are not working?
If you ask my wife, she will tell you that I am always on, 24x7… I work every day as long as is necessary, but I do need to have some time off in order to exercise and to relax.
I love to go hiking in the bush and to go touring with my family – it really helps to clear my head away from technology. I also love to read.
Is there anything else you would like to share with our readers?
I take great pride in the people that I work with at ThreatMetrix. They are some of the smartest and greatest people that I have ever worked with. They are committed to the cause and are always working hard – much more than at any other company I have ever been involved in.




Please, comment on how to improve this article. Your feedback matters!