Report: Global Sporting Goods Giant Leaks Spanish Employees' Data & More
The vpnMentor cybersecurity research team, led by Noam Rotem and Ran Locar, have uncovered a leaking, active database with over 123 million records and greater than 9GB in size on an ElasticSearch server, belonging to Decathlon Spain (and possibly Decathlon UK as well).
Decathlon Company Profile
Decathlon Group is a privately-held sporting goods retailer that was founded in 1976 and reportedly employs around 93,000 people in total. Although the company is headquartered in Northern France, it is truly international with stores in 49 countries around the globe, including Spain and the United Kingdom.
The company is not one to shy away from making technological advances, introducing in-store mobile checkouts and inventory robots. However, these API-enabled tech systems are a soft spot for vulnerabilities, particularly when the correlating databases are not properly secured.
Timeline of Discovery and Owner Reaction
Sometimes the extent of a data breach and the owner of the data are obvious, and the issue quickly resolved. But rare are these times. Most often, we need days of investigation before we understand what’s at stake or who’s leaking the data.
Understanding a breach and its potential impact takes careful attention and time. We work hard to publish accurate and trustworthy reports, ensuring everybody who reads them understands their seriousness.
Some affected parties deny the facts, disregarding our research or playing down its impact. So, we need to be thorough and make sure everything we find is correct and true.
In this case, we easily identified Decathlon as the owner of the database and have contacted the company with our findings.
Date discovered: February 12th, 2020
Date company notified: February 16th, 2020
Database closed: February 17th, 2020
Examples of Entries in the Database
The leaked Decathlon Spain database contains a veritable treasure trove of employee data and more. It has everything that a malicious hacker would, in theory, need to use to take over accounts and gain access to private and even proprietary information.
Data that our research team was able to find and verify included:
Data Impacted
- Employee usernames
- Unencrypted passwords
- API logs
- API username and unencrypted password
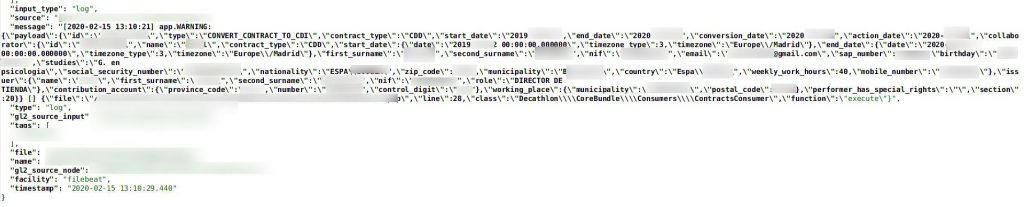
- PII of employees
- Social security numbers
- Full names
- Nationalities
- Mobile phone numbers
- Full addresses
- Birthdates
- Education
- Work email addresses
- Employment contract information
- Working hours
- Location
- Qualifications
- Contract period
- Roles
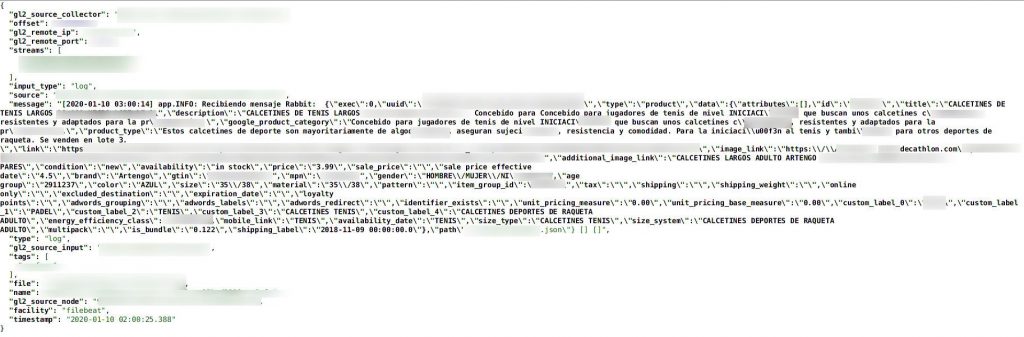
- Customer email and login information, unencrypted
- Private IP addresses
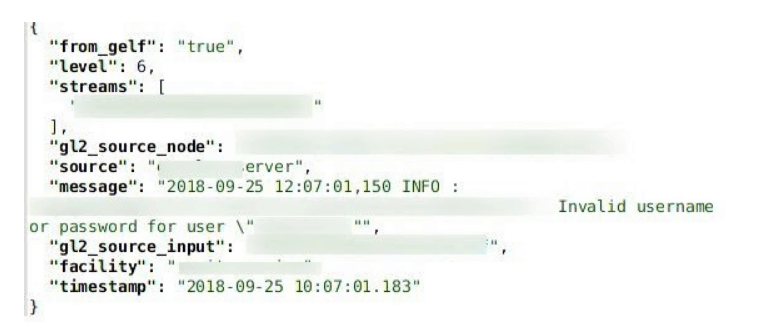
Login attempts, including username and password.
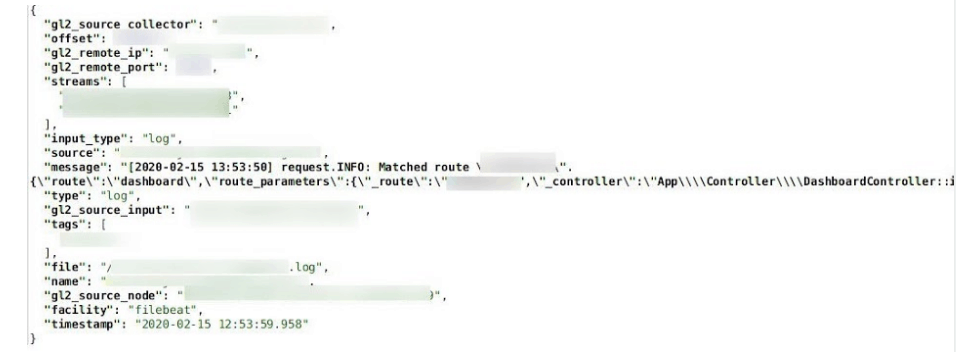
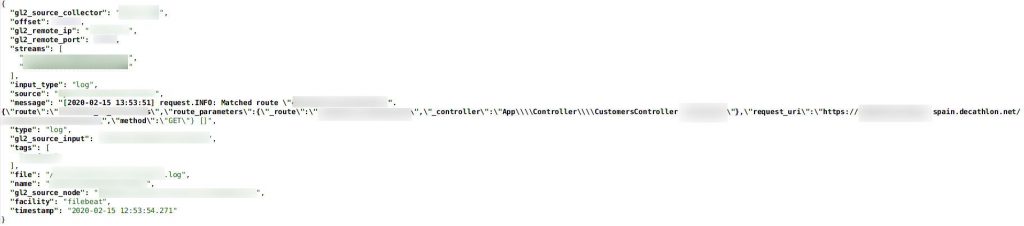
API details
Affected Regions
Our research team was only able to confirm that the database belonged to Decathlon Spain, with a strong possibility of Decathlon United Kingdom information included as well. These are the countries where we found local Decathlon data included in the leak, but we did not go through all 123 million+ records, and it is possible that there are more locations in additional countries that were impacted.
Data Breach Impact
Corporate Espionage
Full unencrypted logins for administrators seem to have been made available in this leak. The loss of control over this access could lead to cyber criminals taking over accounts and obtaining otherwise confidential information about stores, employees, and customers.
Inventory details
Phishing
Phishing attacks are a very real possibility with this type of leak. There are email addresses of customers and employees, tied to a retailer from which both categories of people would be acclimated to receiving frequent marketing and administrative emails. It’s simple to hide a high-risk link behind an image of an otherwise real ad promising a great seasonal deal.
Identity Theft
Knowing the full name, birthdate, and other PII of an individual can provide criminals with enough information to steal that person’s identity.
Identity theft does not always mean that the thief will claim that they are a particular individual in real life; it also allows them to engage in credit fraud, drain your bank account, and engage in scams to family, friends, and other associates of the identity theft victim.
Store director PII
Physical Threats
Employees’ positions and work locations are spread throughout this database, as well as their own physical home addresses. This could lead to disgruntled former coworkers or irate customers tracking them down and threatening their physical safety and well-being.
Advice from the Experts
Decathlon could have easily avoided this leak if they had taken some basic security measures to protect the database. These include, but are not limited to:
- Secure your servers.
- Implement proper access rules.
- Never leave a system that doesn’t require authentication open to the internet.
Any company can replicate the same steps, no matter its size. For a more in-depth guide on how to protect your business, check out our guide to securing your website and online database from hackers.
For those affected by the leak
You can contact Decathlon directly and find out how they are resolving this issue and plan on protecting your data better in the future. If you may have your personal information on the Decathlon platform - and are concerned about how this breach might impact you or other data vulnerabilities in general, read our complete guide to online privacy to help better protect yourself online in the future. It shows you the many ways cyber criminals target internet users, and the steps you can take to stay safe. You can also use a VPN to hide some of the data collected by Decathlon. A VPN will mask your IP address and country of residence, giving you an added layer of protection even if your data is leaked.
Customer-related data
How and Why We Discovered the Breach
During an extensive web mapping endeavor, the research team at vpnMentor detected a breach within Decathlon's database. To identify potential system vulnerabilities, our researchers implement port scanning, examining specific IP blocks and inspecting open gaps. Each of these gaps is then thoroughly assessed for possible data leaks.
When they find a data breach, they use expert techniques to verify the database’s identity. We then alert the company to the breach. If possible, we will also alert those affected by the breach.
We were able to access Decathlon's database because it was completely unsecured and unencrypted. Using a web browser, the team could access all files hosted on the database.
The purpose of this web mapping project is to help make the internet safer for all users. As ethical hackers, we’re obliged to inform a company when we discover flaws in their online security.
However, these ethics also mean we also carry a responsibility to the public. This is especially true when the companies data breach contains such a huge amount of private and sensitive information.
About Us and Previous Reports

In the past, we’ve discovered a breach in LightInTheBox that compromised the data of its customers. We also revealed that nearly the entire population of Ecuador was exposed in a government-linked data breach. You may also want to read our VPN Leak Report and Data Privacy Stats Report.




Please, comment on how to improve this article. Your feedback matters!