Report: State in India Leaves Data From Covid-19 Surveillance Tool Open, Risking Safety for Millions of People Across the Country
We can reveal that a surveillance platform built to track and trace COVID-19 patients in India has been compromised due to a lack of data security protocols that inadvertently left access to the platform wide open, along with exposing the data of millions of people from across India.
Named “Surveillance Platform Uttar Pradesh Covid-19”, the software appears to have been built by the regional government of Uttar Pradesh, a state of India.
However, vulnerabilities within the platform left it easily exposed to malicious hacking and attack, which could have devastated Uttar Pradesh’s response to the Coronavirus pandemic.
Data Breach Summary
| Owner of the Data | Government of Uttar Pradesh, India |
|---|---|
| Headquarters | India |
| Industry | Healthcare; Coronavirus response |
| Data storage format | Exposed git repository and directory listing |
| Size of data stored | Over 54GB and growing daily |
| Suspected no. of files | 230+ in the directory listing |
| No. of people exposed | ~8 million and growing daily |
| Date range/timeline | 2020 |
| Geographical scope | Predominantly Uttar Pradesh state; additional data from the national government of India |
| Types of data exposed | PII data and medical status of individuals tested for COVID-19, admin usernames and passwords, and more. |
| Potential impact | Hacking and attack; disruption to India’s Coronavirus response; fraud; much more. |
Timeline of Discovery and Uttar Pradesh's Response
- 1st August 2020: Our web scanner detects the open systems
- 9th August 2020: Data breach reviewed and analyzed
- 10th August 2020: Israeli embassy in India contacted
- 3rd September 2020: Prof Triveni Sigh, from the UP Cybercrime department, contacted
- 27th August, 7th September 2020: CERT-In contacted
- 10th September 2020: Data breach is secured
Uttar Pradesh’s Coronavirus surveillance platform was compromised through numerous vulnerabilities, all pointing to a severe lack of security around this very sensitive project.
The first vulnerability was an unsecured git repository, which, in addition to containing the code for the surveillance platform, also contained a ‘data dump’ of stored login credentials for its admin dashboard. These included usernames and passwords for admin accounts on the platform, along with other sensitive data.
For ethical reasons, our team, led by renowned analysts Noam Rotem and Ran Locar, didn’t test the usernames and passwords to access the surveillance platform’s admin dashboard, but conducted a thorough investigation to indirectly confirm their authenticity and prove it was possible to do so.
Based on the git repository discovery, Noam and Ran were able to dig deeper into the exposed platform and discovered another data breach related to it.
This time, an exposed web index revealed a directory listing of CSV files listing all known cases of COVID-19 testing in Uttar Pradesh and other parts of India, totaling over 8 million people. The web index was accessible without a password or any other form of identity verification and completely open to the public.
While the directory listing didn’t directly impact Uttar Pradesh’s surveillance platform, it severely compromised the safety of the millions of people listed in the CSV files, whose data probably originated from the surveillance platform and other sources.
After a thorough investigation, we created a report to share with the government of India.
This process takes careful attention and time to ensure everybody who reads the report understands its seriousness.
Occasionally, the parties involved in a data breach disregard our research, deny the facts, or play down its impact. So, we need to be thorough and make sure everything we find is correct and accurate.
Once the report was completed and all the information contained within verified, we reached out to the Israeli embassy in India, who forwarded our report to CERT-In, India’s Computer Emergency Response Team.
After some time without hearing back from them and the database still exposed, we decided to reach out to the CERT-In ourselves. We then later got in touch with Prof. Triveni Sigh from the UP Cybercrime department. As we saw no steps were taken, we reached out to the CERT-In again on the 7th of September to remind them of the pressing issue.
Examples of Data Exposed
Uttar Pradesh is a state in Northern India, with a population of over 200 million people. It's the most populous state in India, accounting for 14.8% of the nation’s total population.
India has struggled with responding to Coronavirus, and Uttar Pradesh is no exception.
At the time of writing, the state has recorded over 136,000 confirmed positive cases of COVID-19, roughly 5.66% of the total national number of cases in India (2.4 million).
We believe the exposed surveillance platform was built for the Uttar Pradesh Department of Health & Family Welfare and the state’s Directorate General of Medical Education & Training to track as much data as possible relating to individual cases of COVID-19 and its spread across the state.
However, in the rush to build and scale the software across Uttar Pradesh, numerous basic security protocols were overlooked.
As a result, there were three significant vulnerabilities within the platform’s infrastructure:
1) An unsecured git repository revealing technical information, including passwords to admin accounts on the platform and a SQL data dump.
2) This made the platform’s admin dashboard accessible to anyone with the passwords taken from the git repository.
3) A separate index of CSV files containing daily COVID-19 patient reports - accessible without a password or any other login credentials.
The platform's developers had wrongly deployed the unsecured git repository with the platform’s source code, database data dumps, passwords, and endpoints (URLs used to send and receive data from different sources).
The passwords were listed on the file twice: a hashed version using plain MD5 (without salt), which can be easily cracked using a dictionary, and a plain text version stored side-by-side on a separate column. By having a plain text version of each password, the already weak hashed version was made completely voided and useless.
Finally, most passwords were just 4-digits numbers, and many accounts shared the same 4-digit code as the platform’s administrators.
They then left the git repository completely unsecured and accessible without any login credentials.
It also appears that no security audits were undertaken on the git repository to review who had access to the data, and to implement robust security protocols, despite numerous parties spread throughout Uttar Pradesh using the surveillance platform to upload data.
As a result, anyone with knowledge of the platform’s URL and access to the git repository could gain complete access to its admin dashboard.
Not only did this expose any data stored therein to possible theft, but, based on additional information stored on the git repository, we believe that once a hacker had access to the admin dashboard of the surveillance platform, they would have complete control.
Control of the admin dashboard would allow them to take it over and make significant changes, such as:
- Modifying entries
- Closing case files
- Altering patients’ data
- Modifying test results
- Sending healthy people to quarantine
- Removing patients from quarantine early
- Switching negative test result to positive, and vice versa
Personal Identifiable Information Data
Within the directory listing, there were huge CSV files that listed daily COVID-19 records from the state. We believe these were complemented by interactive lists on the surveillance platform, based on our investigation of the git repository’s SQL data dump.
The earliest entries on the directory listing dated from the beginning of the pandemic in March, with new entries added daily until early August, when we discovered the vulnerabilities.
The lists included numerous forms of Personally Identifiable Information (PII) data for every individual tested for COVID-19 in Uttar Pradesh, including:
- Full names
- Ages
- Genders
- Residence addresses
- Phone numbers
![]() A sample of one CSV file listing individual daily cases and PII data
A sample of one CSV file listing individual daily cases and PII data
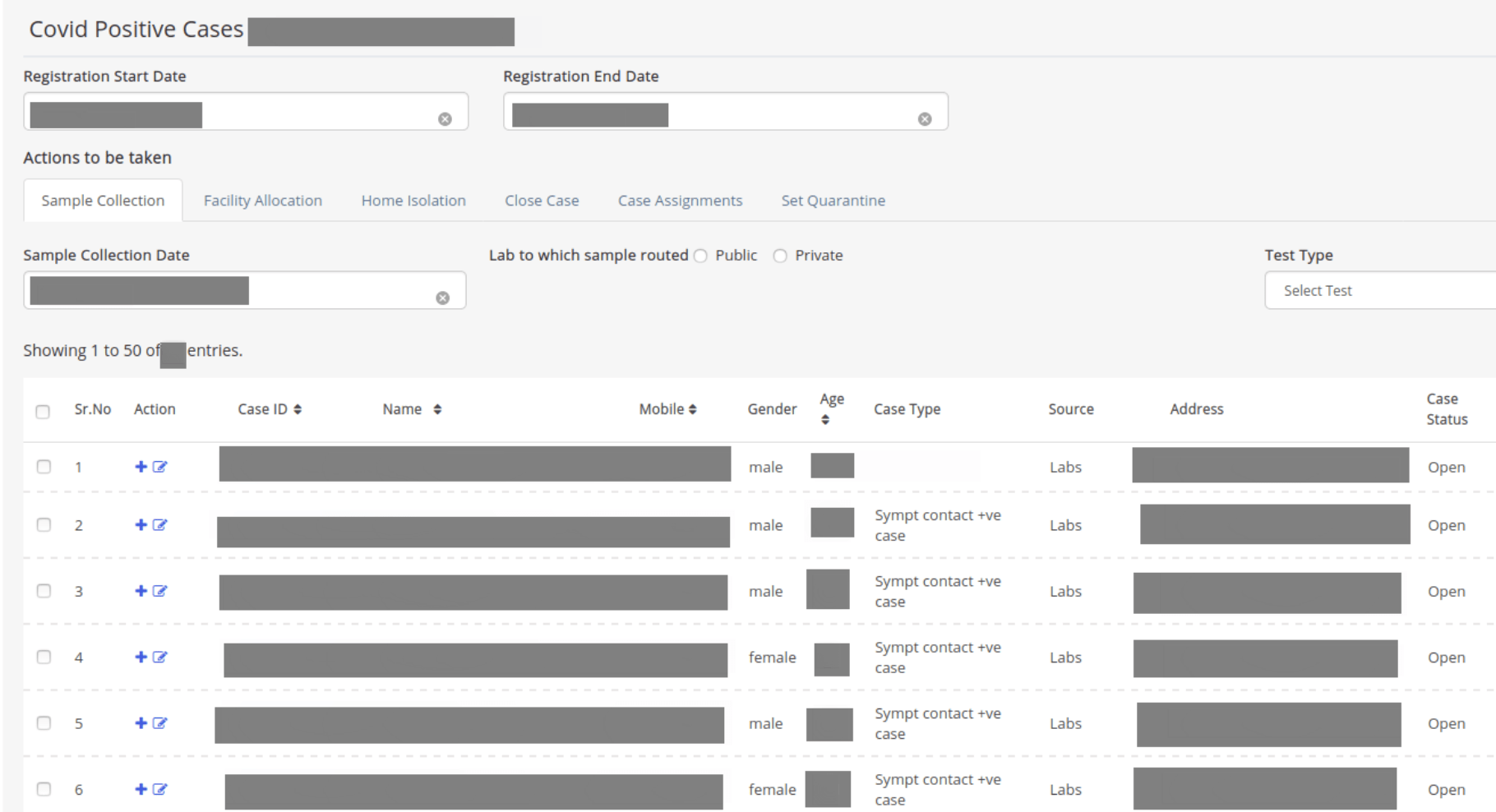 A screenshot of the patient list shows various data points recorded for every person tested.
A screenshot of the patient list shows various data points recorded for every person tested.
COVID-19 Diagnosis and Symptoms
According to the SQL data dump, every entry on the surveillance platform’s lists had a unique profile that provided further details of the health, testing status, and COVID-19 diagnosis for each person listed.
These entries revealed further information about each person listed:
- Case IDs
- Diagnosis
- Symptoms
- Medical records
- How the patient contracted COVID-19 (foreign travel, etc.)
- Place of isolation/quarantine (govt. Facility, at home, etc.)
Based on the names and details recorded in some entries, we believe Uttar Pradesh is also tracking non-Indian citizens and foreign residents in the country who have tested positive for COVID-19.
For example, entries with traditionally Vietnamese and Anglo-European names were listed.
The lists also included many health workers who have contracted the virus while working to treat patients and contain the spread of Coronavirus in India.
Macro Data for Coronavirus in India
Aside from revealing sensitive data of individuals within Uttar Pradesh, the surveillance platform also revealed information about Coronavirus’s status across the state, including:
- Trends in total cases, recoveries, and deaths over time
- The total number of people under surveillance
The platform also included data received and integrated from India’s national government, totaling about 8 million records of individuals across different states in the country.
These included the date of an individual’s entry into the country and other sensitive information.
Data Breach Impact
As explained above, with complete access to the surveillance platform’s admin dashboard, hackers or cybercriminals could easily take over and wreak havoc with the data and patient files, going so far as deleting records.
Such malicious actions would have many real-world consequences on the effectiveness of Uttar Pradesh’s response and action against Coronavirus, potentially causing extreme disruption and chaos.
However, the ripples from this vulnerability could be felt far beyond the ministries combating COVID-19 in Uttar Pradesh.
While India has struggled to contain COVID-19 and successfully manage outbreaks, distrust in the government has grown significantly, like in many countries. Several factors are to blame, including simmering tensions that pre-date the pandemic and the ever-present issues of fake news and disinformation campaigns.
News stories of a government ‘surveillance’ program tracking its citizens could be considered suspicious enough. One that exposed millions of people to hacking and attacks due to incompetence could sow further distrust in the government and its occasionally heavy-handed response to COVID-19.
Malicious parties could further exploit the story in disinformation and propaganda campaigns — sowing division and de-legitimizing government efforts to win public support.
Furthermore, individuals may become increasingly reluctant to report possible cases of COVID-19 due to fear of their private data being exposed, and other issues addressed further down.
Finally, had hackers working with states unfriendly to India discovered these vulnerabilities, they could have exploited them to undermine the country’s Coronavirus response for political gains. Over recent months, news stories suggest this is occurring elsewhere, as malicious state actors exploit the pandemic to attack their rivals when they’re most vulnerable.
As a result, India’s struggles to contain the devastation caused by COVID-19 could be complicated and handicapped beyond repair.
Avoidable delays and loss of life would be real risks.
For COVID-19 Patients
Aside from the obvious dangers of having their COVID-19 treatment disrupted — with potentially lethal consequences — the people exposed in this data breach could have faced many secondary risks by having their data leaked.
With such detailed PII data and medical records exposed, they’re vulnerable to viral attacks and financial fraud on a massive scale. There have been many proven cases of cybercriminals successfully exploiting Coronavirus in phishing campaigns and other forms of fraud to steal from victims across the globe.
Hackers could use the information in Uttar Pradesh’s platform to create fraudulent emails appearing to victims as the relevant government agencies and ministries checking up on former COVID-19 patients, or as companies reaching out to them for a related reason.
There could also be a real risk to their personal safety.
COVID-19 patients may face recrimination or persecution within their local communities if fearful and desperate neighbors suspect or blame them for spreading the virus in their area. Many of the people listed as positive in the admin dashboard and CSV files were self-isolating at home after testing positive. They could be particularly vulnerable to harassment or rejection from within their community.
As mentioned previously, a data breach of this seriousness and magnitude could heighten tensions within India, especially if hackers exploited it to disrupt Uttar Pradesh’s COVID-19 response.
The lists of COVID-19 patients could also be used to fuel xenophobia and anti-Chinese sentiments in India. There were many seemingly foreign-born patients on the lists, suspected of contracting COVID-19 through ‘foreign travel.’ These people, and foreigners in general, could easily be blamed for importing the virus into India and attacked for doing so.
This is already happening in countries around the world. People who look ‘foreign’ — especially people from China and its neighboring countries — are being harassed and victimized in public, often through physical violence.
With tensions between the Indian and Chinese governments running at all-time highs, a list of foreigners importing Coronavirus from East Asia would be a great tool in anti-Chinese propaganda efforts.
Regardless of how hackers and cybercriminals decided to exploit Uttar Pradesh’s COVID-19 surveillance platform, had they found it, the consequences for thousands (maybe even millions) of Indian citizens and foreign residents across the country could have been devastating.
Advice from the Experts
The Uttar Pradesh government could have easily avoided exposing its citizens’ data if it had taken some basic security measures to protect its citizens' data. These include, but are not limited to:
- Securing its servers.
- Implementing proper access rules.
- Never leaving a system that doesn’t require authentication open to the internet.
A business can also replicate the same steps, no matter its size, to keep customer data safe.
For a more in-depth guide on how to protect your business, check out our guide to securing your website and online data from hackers.
How and Why We Discovered the Breach
The vpnMentor research team discovered the breach in Uttar Pradesh’s surveillance platform as part of a huge web mapping project. Our researchers use port scanning to examine particular IP blocks and test different systems for weaknesses or vulnerabilities. They examine each weakness for any data being leaked.
Our team was able to access this git repository and live directory listing from the system because it was completely unsecured and unencrypted.
Every time we uncover a data vulnerability of this nature, we employ specialized methods to confirm the identity of the database owner, who is typically a commercial enterprise.
However, sometimes it can be a government or state agency.
As ethical hackers, we’re obliged to inform a company or government when we discover flaws in their online security. We reached out to Uttar Pradesh’s government to let them know about the vulnerability and suggest ways in which they could make their system secure.
These ethics also mean we carry a responsibility to the public. Indian citizens must be aware of a data breach that exposes so much of their sensitive data.
The purpose of this web mapping project is to help make the internet safer for all users.
About Us and Previous Reports

This has included an enormous data breach exposing millions of users of India's BHIM e-payments app. We also revealed that a group of popular free VPNs logged and leaked their users’ data from across the globe. You may also want to read our VPN Leak Report and Data Privacy Stats Report.
[Publication date: 12th August 2020]




Please, comment on how to improve this article. Your feedback matters!