Report: 10,000s of Brazilians Exposed to Fraud in Massive Data Breach
Led by Noam Rotem, vpnMentor’s research team discovered a data breach affecting an enterprise software solution and exposing a database containing files related to a Brazilian financial company called Prisma Promotora.
A software tool was used to manage and interpret data from every aspect of the company’s operations.
Unfortunately, a cloud storage account connected to the software was left unsecured and publicly accessible by the software owner. It compromised the private information of 10,000s of people connected to Prisma Promotora, exposing them to fraud and other dangers.
Data Breach Summary
| Company responsible for the leak | Enterprise software provider |
|---|---|
| Data exposed | Prisma Promotora’s |
| Headquarters | Sao Paulo, Brazil |
| Industry | Consulting and financial services |
| Size of data in gigabytes | 574 GB |
| No. of files in S3 Bucket Exposing Prisma Promotera | 717,068 files |
| No. of lines in SQL database Exposing the Potential ERP Software Company | 10,000s |
| No. of people exposed | 10,000s |
| Date range | Mid-2020 |
| Geographical scope | Brazil |
| Types of data exposed | PII data; photos; credit card details; account login credentials; audio recordings |
| Potential impact | Fraud and identity theft; Scams, phishing, and malware; corporate espionage; theft; account takeover; database takeover |
| Data storage format | Misconfigured AWS S3 bucket and SQL database |
Timeline of Discovery and Owner Reaction
- Date discovered: 29th December 2020
- Date potential bucket owner contacted: 30th December 2020
- Date Amazon Contacted: 3rd January 2021
- Date Prisma Promotora Contacted: 5th January 2021
- Date of Response: -
- Date of Action: By 14th February 2021
Sometimes, the extent of a data breach and the data’s owner are obvious, and the issue is quickly resolved. But rare are these times. Most often, we need days of investigation before we understand what’s at stake or who’s exposing the data.
Understanding a breach and its potential impact takes careful attention and time. We work hard to publish accurate and trustworthy reports, ensuring everybody who reads them understands their seriousness.
Some affected parties deny the facts, disregarding our research, or playing down its impact. So, we need to be thorough and make sure everything we find is correct and accurate.
In this case, our team originally discovered an unsecured Amazon Web Services (AWS) S3 bucket containing over 570 gigabytes of files and data from a mobile app.
Upon investigating the mobile app, we determined that the data belonged to an Enterprise Resource Planning (ERP) system being used by Prisma Promotora that was connected to the AWS account.
We initially contacted the company we assumed was the owner of the bucket. As they didn’t get back to us, we contacted AWS directly to notify it of the breach. AWS often notifies users of breaches and misconfigurations when we are unsuccessful in doing so.
Meanwhile, we continued investigating the S3 bucket to confirm some additional details. After some additional research, we identified Prisma Promotora as the assumed sole owner of the exposed data, but not the S3 bucket itself. Due to this discovery, we also contacted the company to notify it of the breach and the risk to its customers.
The breach was closed about a month after this.
Example of Files in the S3 Bucket
The S3 bucket contained a massive amount of files from a wide range of sources. While we can’t confirm the data’s origins with 100% certainty, it appears to belong to the company Prisma Promotora, which was using the ERP software to track and manage customer data.
The files exposed huge amounts of Personally Identifiable Information (PII) data for 10,000s of people. This included:
- Full names
- Email addresses
- Phone numbers
- DOBs
- Debit card information
- Brazilian CNPJ identification numbers
- ID photos
- Home and workplace addresses
- Registration details for personal vehicles
- Police background check statuses
- Much more
We believe the S3 bucket was a backup, and the data we viewed was not recent. However, the PII data could still be used to compromise the security and safety of the people affected.
~105,000 Audio and Video Files
Voice recordings and videos in Portuguese apparently belonging to Prisma Promotera were exposed by the bucket misconfiguration.
Numerous voice recordings outlined negotiations for a loan agreement, with a person’s details and financial information explicitly outlined, including the ID number and bank account number.
In another audio recording, a person working at Prisma Promotora can be heard requesting a lot of sensitive information about a customer over the phone.
~608,000 media files, including photos and videos
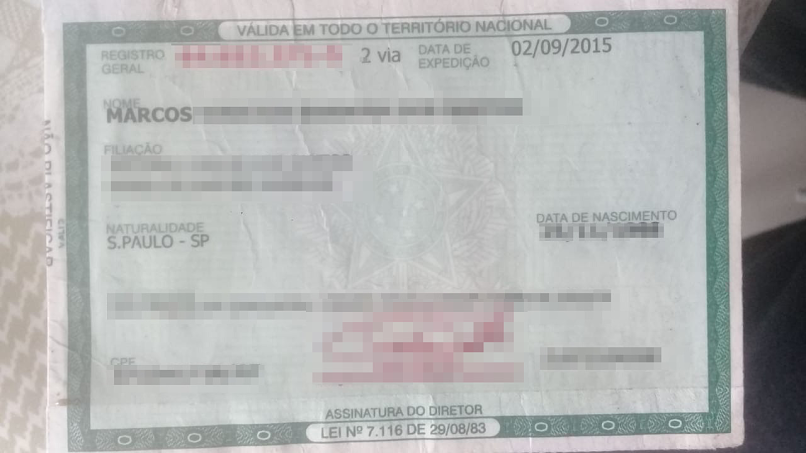
The photos contained images of credit card photos, identification documents, and more. It’s unclear what the purpose was for people uploading photos of their IDs and debit cards.
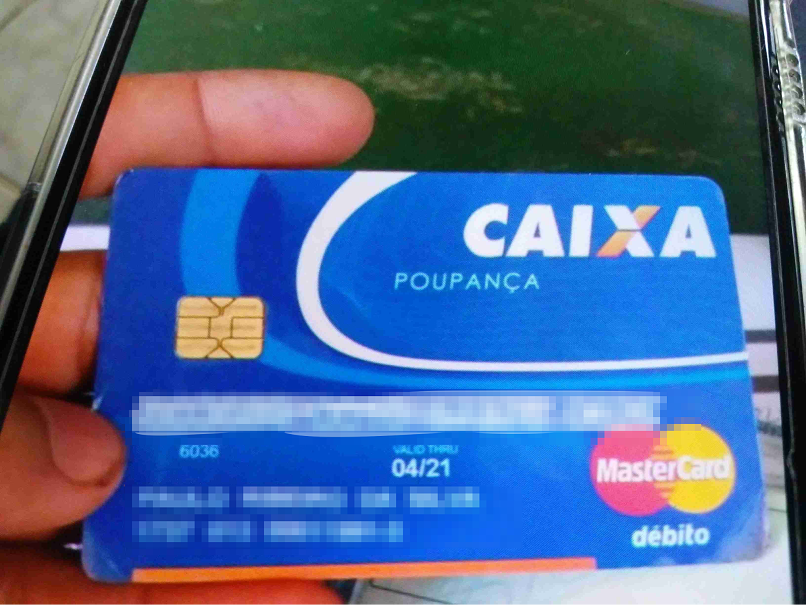
Photo of debit card still valid until 2021
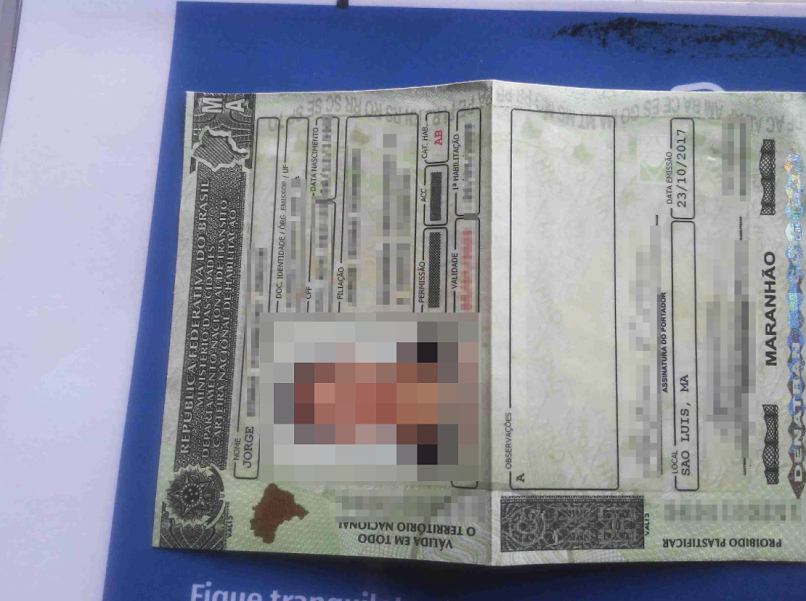
A Brazilian ID card
~1,700 Documents
Documents including scans and soft copies of invoices, proof of registration documents, police background checks, etc.
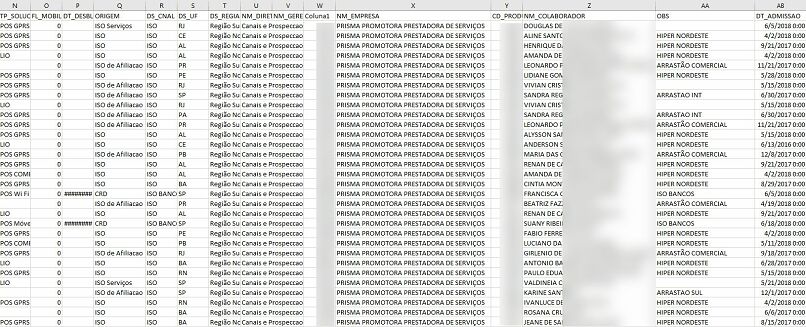
~2,000 Microsoft Excel Sheets
During our investigation, we viewed a small sample of excel sheets containing PII data (including names, addresses, and phone numbers) for over 27,000 people (due to duplicate entries, this number isn’t 100% accurate).
Due to ethical concerns (and not to breach their privacy further), we couldn’t estimate how many people were exposed across the 2,000 Excel Sheets stored on the S3 bucket.
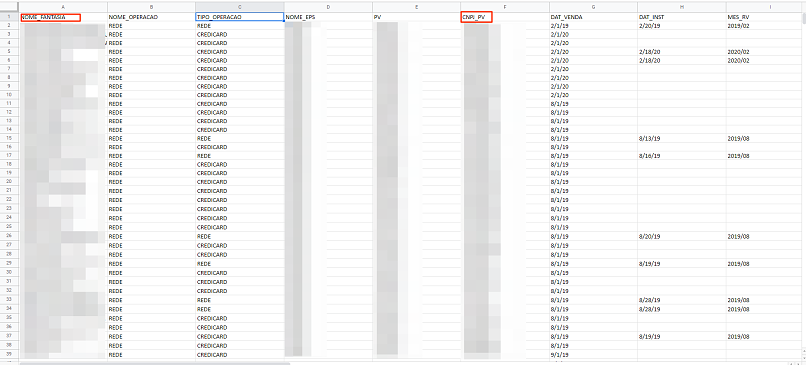
A snippet of excel sheet showing name and ID number for 20k+ people
Some of the excel sheets seemed to have exposed employees from Prisma, too, with details about their activities, as outlined in the file sample below.
SQL Backup File
As well the various file types outlined above, the S3 bucket contained a second backup SQL database from the potential owner of the bucket.
While much smaller than the bucket, the SQL database also contained highly sensitive data.
We estimate the SQL backup contained over 500,000 files, each containing various forms of additional PII data.
Some entries also appeared to contain login credentials for accounts on the app.
Mobile Application Files
The S3 bucket also contained various mobile application files (APK files), which gave indirect access to the backend of the login page for the ERP app. With this access, we were able to view a live SQL database and see its contents.
The exposed SQL database adds to the severity of the breach significantly and highlights the lack of security protocols put in place by the S3 bucket’s owner.
Data Breach Impact
The exposed files and databases compromised the security of 10,000s of people.
For Prisma Promotora and Its Customers
Hackers could use the exposed PIIs from the leak to commit various forms of fraud, access private accounts on external platforms, and pursue identity theft targeting anyone whose details were revealed.
They could also use the contact information and PII data to set up elaborate phishing campaigns. In a phishing campaign, cybercriminals send fraudulent emails imitating real businesses and trick victims into providing private data (such as credit card details) or clicking a link embedded with malicious viruses like malware and spyware.
Alternatively, cybercriminals could use the voice recordings to create scripts imitating businesses and ring their customers. Using the PII data and scripts, they could easily build enough trust to fool people into providing financial information that can be used to defraud them at a later date.
It seems that the SQL backup also resulted in a breach of login details for user accounts on its software. Possessing usernames and passwords, cybercriminals could effortlessly seize control of Prisma Promotora accounts, paving the way for a range of illicit activities against the company.
Finally, the breach also exposed shipping details for shipments processed on the ERP software. If these were live, hackers could attempt to reroute or steal the shipments.
For The S3 Bucket Owners
Cybercriminals could also target the company responsible for the breach in numerous ways, such as taking over its databases or stealing private company data.
The company’s competitors could also exploit the data breach, using any bad publicity generated to entice clients to rival software solutions. Simultaneously, had malicious hackers accessed the S3 bucket and databases, they could have provided access to competitors, allowing them to see inside the company’s code and imitate it in their products.
Advice from the Experts
This data breach could have been easily avoided if some basic security measures had been followed. These include, but are not limited to:
- Securing the servers.
- Implementing proper access rules.
- Never leaving a system that doesn’t require authentication open to the internet.
Any company can replicate the same steps, no matter its size.
For a more in-depth guide on how to protect your business, check out our guide to securing your website and online data from hackers.
Securing an Open S3 Bucket
It’s important to note that open, publicly viewable S3 buckets are not a flaw of AWS. They’re usually the result of an error by the owner of the bucket. Amazon provides detailed instructions to AWS users to help them secure S3 buckets and keep them private.
In this case, the quickest way to fix this error would be to:
- Make the bucket private and add authentication protocols.
- Follow AWS access and authentication best practices.
- Add more layers of protection to their S3 bucket to further restrict who can access it from every point of entry.
For Prisma Promotora's Customers
If you’re a customer or client of Prisma Promotora and are concerned about how this breach might impact you or people connected to your business, contact the company directly to determine what steps it's taking to protect your data. But remember, according to our findings, Prisma Promotora wasn't responsible for the bucket and probably not for the misconfiguration either.
We recommend businesses thoroughly vet all 3rd party software solutions you integrate into your operations to ensure they follow the strictest possible data security practices. Doing so reduces the risk of a data breach, leak, or hack that impacts clients and customers without your knowledge.
To learn about data vulnerabilities in general, read our complete guide to online privacy.
It shows you the many ways cybercriminals target internet users and the steps you can take to stay safe.
How and Why We Discovered the Breach
The vpnMentor research team discovered this data breach as part of a huge web mapping project. Our researchers use large-scale web scanners to search for unsecured data stores containing information that shouldn’t be exposed. They then examine each data store for any data being leaked.
Our team was able to access this S3 bucket because it was completely unsecured and unencrypted.
Whenever we find a data breach, we use expert techniques to verify the data’s owner, usually a commercial business.
As ethical hackers, we’re obliged to inform a company when we discover flaws in their online security. We reached out to the potential owner of the bucket, AWS, and Prisma Promotora, not only to let them know about the vulnerability but also to suggest ways to secure their system.
These ethics also mean we carry a responsibility to the public -who should always be aware of a data breach that exposes so much of their sensitive data.
The purpose of this web mapping project is to help make the internet safer for all users.
We have no evidence - and no way of knowing - whether the data in our reports have been accessed or leaked by anyone else. Only the database owner has access to that information.
We do our best to prevent this from happening by reaching out to the companies and ensuring they secure their leaking database as soon as possible.
We never sell, store, or expose any information we encounter during our security research.
About Us and Previous Reports
vpnMentor is the world’s largest VPN review website. Our research lab is a pro bono service that strives to help the online community defend itself against cyber threats while educating organizations on protecting their users’ data.
Our ethical security research team has discovered and disclosed some of the most impactful data breaches in recent years.
This has included an enormous data breach exposing financial records from 100s of European social media influencers. We’ve also uncovered potential criminal activities and scams targeting users on Spotify, Instagram, and Facebook.
You may also want to read our VPN Leak Report and Data Privacy Stats Report.
Help Us Protect The Internet!
Introducing The Leak Box
The Leak Box is hosted on the Dark Web and allows ethical hackers to anonymously report any data breach they find online. Alternatively, anyone can submit a breach here on vpnMentor, any time, from anywhere, without compromising your privacy.
[Published on March 2nd, 2021]




Please, comment on how to improve this article. Your feedback matters!