Deep Dive: Can Anyone Be Truly Anonymous Online?
- How Hackers Get Your Info?
- Governments and Privacy: Who is the Strictest?
- Anonymity vs. Privacy: Explained
- Who should be concerned about anonymity and why
- Anonymity + Browsers and Search - Part 1
- Anonymity + Browsers and Search - Part 2
- Anonymity + Free Email Accounts
- Anonymity + SMS and Messaging Apps
- Anonymity + Social Media Apps
- Anonymity + Sharing Apps
- Anonymity + Public WiFi
- Anonymity + Passwords
- Anonymity + Dating/Hookup Apps and Online Porn Sites
- Anonymity + Job Sites and Virtual Work
- Anonymity + Online Shopping
- Anonymity + Online Gaming
- Conclusion
With tech giants becoming more and more central to our daily lives, the internet is increasingly scrutinized for its lack of anonymity. As cyberattacks and data breaches are the subject of more and more headlines, it’s hard not to question how secure your identity ever truly is online. According to a recent study, nearly half of Americans are convinced their personal data is less secure than it was five years ago. In that same study, 14% of the surveyed claim a fraudster tried to take out loans and credit lines in their names. In 2014, according to government data, 7% of all U.S. residents 16 or over were victims of identity theft.
Concern about online anonymity stretches well beyond identity theft. In 2019, Human Rights Watch issued a report that advised a 12-point code of conduct for students and educational professionals under threat from surveillance by the Chinese government. From the report: “Chinese authorities have long monitored and conducted surveillance on students and academics from China and those studying China on campuses around the world. Chinese diplomats have also complained to university officials about hosting speakers – such as the Dalai Lama – whom the Chinese government considers “sensitive.”
No matter what’s driving your concerns about risk--whether it’s an intrusive and overbearing government or more general and common-sense apprehensions regarding identity theft--it’s wise to investigate where and how you can attain different levels of anonymity online. Our guide goes beyond addressing and rehashing the well-known methods to protect your identity (firewalls, antivirus software, VPNs, onion routers, etc.).
Said another way: this isn’t just another “how to protect yourself online” guide. This is a personalized, well-researched, and informed critical discussion of how and where you can hide behind complete anonymity while you conduct yourself personally and financially online.
We will also explain the critical difference between privacy and anonymity. Think of this distinction: privacy applies to actions and anonymity applies to your identity. You can attain privacy in an instant by browsing the web using a VPN plugin in a browser. Shielding your identity--your real name, where you live, your date of birth, your family’s names and more--is more time consuming and complex.
And how doable is it? Living an online life (using an email account, interacting on social media, banking, shopping) makes complete anonymity almost impossible.
You can, however, decide where and when you want or need to be anonymous, which is precisely the focus of this guide.
Our guide explains:
- When you can be completely anonymous online
- How to isolate experiences and activity on the web when your activity needs to be absolutely anonymous
- Who needs to protect their anonymity more than others and when and how to execute that
- Apps and organizations that are notorious for sharing personal details vs. those that are devoted to protecting both your identity and your privacy
How Hackers Get Your Info?
Hollywood and entertainment has gone out of its way to create a glamorous and often mythic quality to cybercrime and cybercriminals. Films and TV shows (looking at you, Mr. Robot) often involve depictions of fast and easy hacking, that anyone with a decent internet connection and a USB thumb drive can break encryption codes. While there are definitely some hackers who are better than others: the notion that true encryption is breakable is pure fantasy.
When an app or a website leverages actual 256-bit encryption: it’s unbreakable. The issue is the amount of companies that are lax or utterly negligent when it comes to encrypting user data behind a secure firewall. In short: the encryption standards aren’t to blame. It’s when they aren’t properly implemented that users suddenly find their personal data has been leaked.
In truth: hackers aren’t all that remarkable. They, like most criminals, are looking for easy opportunities to use your identity to open lines of credit or use your credentials to make online payments.
For example, in 2014 when many celebrities discovered leaked photos of them online, it wasn’t because a genius hacker familiar with breaking through layers upon layers of firewalls broke into various iCloud accounts. The criminal in question used the oldest trick in the book, and sent out phishing software (disguised-barely-as Gmail and iCloud requests) to capture usernames and passwords.
From the perspective of protecting your anonymity: it remains a user beware world. Some companies are better than others at safeguarding your data. The more you educate yourself (something you're doing right now by reading this guide for example) the less likely that your personal information will end up in the hands of a cyberthief.
Governments and Privacy: Who is the Strictest?
Becoming the victim of cybertheft is one thing, and something we all need to be careful to avoid. Arrest and the loss of your freedom and personhood is quite another. Not all countries and governments have the same attitudes, or even laws, when it comes to what you can read, watch, and even buy online. These bite-sized overviews below give you some idea as to the level of risk many citizens face daily from the strictest regimes around the world.
How Strict is Strict?
Censorship and Punishment in China, Iran, the UAE, and Russia
China

What Do They Censor?
Everything and anything they want or anything that they define as antithetical or damaging to the interests of the Chinese government or the Communist Party. The government runs and operates the country’s single ISP, giving it complete oversight into blocking content, punishing the sharing and distribution of illegal content.
What Content is Considered Illegal?
Anything that “harms the nation’s honor and interests”. In this case, “nation” really refers to the Communist Party’s and core socialist values; and “harm” means a contradiction of whatever that party defines as truth. If that all sounds vague: that’s the point. The more poorly defined those censorship laws are in China, the wider the net government authorities can cast against anyone who breaks them.
In 2006, a Harvard research study reported that China blocked as many as 18,000 websites. Currently, even popular websites and apps like Google and Facebook are blocked. Chinese authorities are particularly punitive when it comes to the possession of pornographic materials. Possession of porn could lead to a three-year prison sentence. In 2010, over 5,000 people were arrested in China in relation to shutting down over 60,000 pornographic websites.
What is the Punishment for Breaking these Laws?
The Chinese government has already made it impossible for online tech and privacy to thrive together. Fines, crackdowns, and what amount to government-sponsored denial-of-service attacks have put digital interactions monitored, measured, and heavily regulated.
“By 1997, Beijing had enacted its first laws criminalizing online postings that it believed were designed to hurt national security or the interests of the state.”
Iran
What Do They Censor?
By modern standards, the Iranian government has turned censorship into a machine--literally. Its Open Net initiative requires that internet service providers (ISPs) send all traffic through state-controlled gateways. This provides government authorities all of the power and logistics they need to block any internet traffic they deem inappropriate, which they did with a heavy hand during political uprisings in 2009. Check out our online censorship report which covers Iran’s troubling censorship patterns.
What Content is Considered Illegal?
Charting the vast overreach of the Iranian government and its vast censorship of online content is a full-time job. Currently, all of the following are considered illegal inside of the country: Instagram, Twitter, Facebook, YouTube, most messaging apps including Telegram, books not otherwise approved by the Culture Ministry, newspapers and media produced outside of the country. In short: anything.
What is the Punishment for Breaking these Laws?
Since the internet is state-run in Iran, the government can simply slow web traffic to a crawl, making watching or downloading anything almost impossible. Iran has used this filtering to block thousands of websites and apps including Twitter, Facebook, YouTube, and Google.
In 2018, Iranian President Hassan Rouhani blocked Iranian citizens’ access to Telegram and Instagram (both of those apps were key in the success of the 2017 uprisings). In 2019, in relation to protests against rising fuel prices, the government also slowed and blocked communications for citizens and journalists, a troubling trend for the international community equally concerned about human rights and digital rights.
“On Monday evening, more than 40 hours after the internet shutdown was introduced, not-for-profit monitoring site Net Blocks reported that connectivity in the country remained at just 5 percent of normal levels.”
SBS News Australia
“Alp Toker, the director of nonpartisan connectivity tracking group NetBlocks, says it took Iranian authorities about 24 hours to completely block the nation's inbound and outbound traffic—leaving it hovering at about 5 to 7 percent of typical connectivity levels.”
Wired Magazine
Alongside the vast power, the government has to block and shut down and block tech platforms, its system of capital punishment is terrifying and well-documented. The “criminals” often include rape victims, journalists, LGBTQ, and anyone having intimate relationships outside of a “traditional” marriage. Amnesty International found that there are over 100 offenses that are currently punishable by flogging including homosexuality, infidelity, and even consexual same-sex relations.
United Arab Emirates

What Do They Censor?
The UAE is one of the youngest nations in the world (founded in 1971), and it’s kept pace with regional neighbors as far as strict oversight of internet content is concerned.
What Content is Considered Illegal?
It remains a country where it is truly dangerous to express yourself. Same-sex relations (homosexuality) is criminalized. Transgender people are often arrested and fined.
What is the Punishment for Breaking these Laws?
Journalists and academics who write or publish any dissent against the government for its less-than-stellar human rights record are often arrested and punished. In terms of internet activity: anything and everything related to activity the government defines in broad terms as indecent or illegal could be blocked, or worse, lead to an arrest.
Russia
What Do They Censor?
Russia utilizes a national digital blockade system called Roskomnadzor that bans access to a wide range of newspapers and digital communication platforms. The ultimate goal of the government-led digital filtration system is to isolate Russia not just physically, but electronically, from the rest of the world. The state appears to be testing methods to shut down aspects of the internet on a whim (something its slowly learning is easier said than done).
What Content is Considered Illegal?
Russia seems bent on surpassing China as the country with the heaviest hand in controlling and censoring web traffic. With internet censorship on the rise, that poses an even greater threat to journalists and critics of the government.
What is the Punishment for Breaking these Laws?
For those living in a country that has an abysmal record on human rights (which goes double for anti-LGBTQ laws), the threats of reprisals from the government for online speech and information exchange are only going to get worse, especially if the nation’s heavy-handed and dangerous leaders interpret your actions as a threat. In 2019, Russian President Vladimir Putin signed a law that allows for massive fines and potential jail time for citizens who share or distribute online content that “disrespects” the government.
Anonymity vs. Privacy: Explained
For the purposes of this article: there is a distinct difference between privacy and anonymity. Think of privacy as the various measures that encrypt and hide your actions on the internet. For example, browsing the internet while using a VPN keeps anything and everything you do while your VPN session is active completely private.
Staying anonymous on the internet doesn’t just mean simply blocking your keystrokes from a web phisher or your ISP. Safeguarding your anonymity requires keeping your actual identity as secret as possible, especially when your freedom is at stake.
It’s a given that some organizations are not just legally entitled, but required by law, to confirm your identity. Most countries have strict “know your customer” (KYC) laws imposed on banks and other financial institutions intended to prevent money laundering and other financial crimes. In the modern world, it’s all but impossible not to have to deal with a bank (but you can avoid using your personal bank account for every purchase with clearing houses and digital currencies like PayPal, Bitcoin, or prepaid gift cards).
Despite the overreach of many nationalistic and dogmatically prohibitive authoritarian states, law enforcement still needs the ability to enforce the law. Like it or not: your national and regional authorities will always have access to your true identity, and in most cases, using a fake identity with law enforcement is a very serious crime. There are other reasons beyond law enforcement for governments to know your real identity. You need to exercise your right to vote, local jurisdictions need the ability to assemble juries and so forth.
We all have a footprint in the world, and there’s virtually no way to avoid that, especially if you intend to use the internet regularly. In fact, for people who live under the thumb of a dictatorship, improved online anonymity may be the only freedom of movement and expression they can enjoy. The key is to be shrewd and smart about where and when to strike a balance between utter disclosure on one end, and utter paranoia on the other.
For more information: take a look at our interactive tool that goes in-depth into what large tech and ecommerce companies track and how they use it.
vpnMentor’s Interactive Privacy Tracking Tool: Who’s Watching You?
To Disclose or NOT to Disclose: That is the Balance
Some institutions (legal and financial) will always have legal authority over your personal details. Expect that the government, insurance companies, tax authorities, and other institutions have a lawful right to know your actual whereabouts including address, DOB, identity, gender, etc. Why? Because they are legally obligated to persecute fraud, to verify individual identity, and more.
We are NEVER suggesting that you remotely make any attempts at executing identity fraud. Rather, identify opportunities for legal anonymity. Take advantage of when and how you can conceal your identity. Find the balance between utter transparency and complete (and nearly impossible) secrecy. Being constantly paranoid is no way to live your life, but you should be informed and concerned about risks and how to mitigate them.

“86% of internet users have tried to use the internet in ways to minimize the visibility of their digital footprints”
Pew Research
Who should be concerned about anonymity and why
While some people are more aware of their exposure--particularly people who live in dictatorships and under extreme censorship laws--many people still nonchalantly surf the web.
That, however, is changing. Increasingly, more of us are aware of the threats to both our privacy and identities online. According to a recent Pew Research study:
- 21% of internet users have experienced social media or email being hacked or taken over
- 50% of those surveyed said they were concerned about the amount of personal information that existed online
- 59% of respondents want the ability to use the internet completely anonymously
The chart below defines three levels of online anonymity, as defined both by the situation someone finds themselves in (for example living in a strict country) as well as various professionals who are obligated to do as much of their interactions online as anonymously as possible.
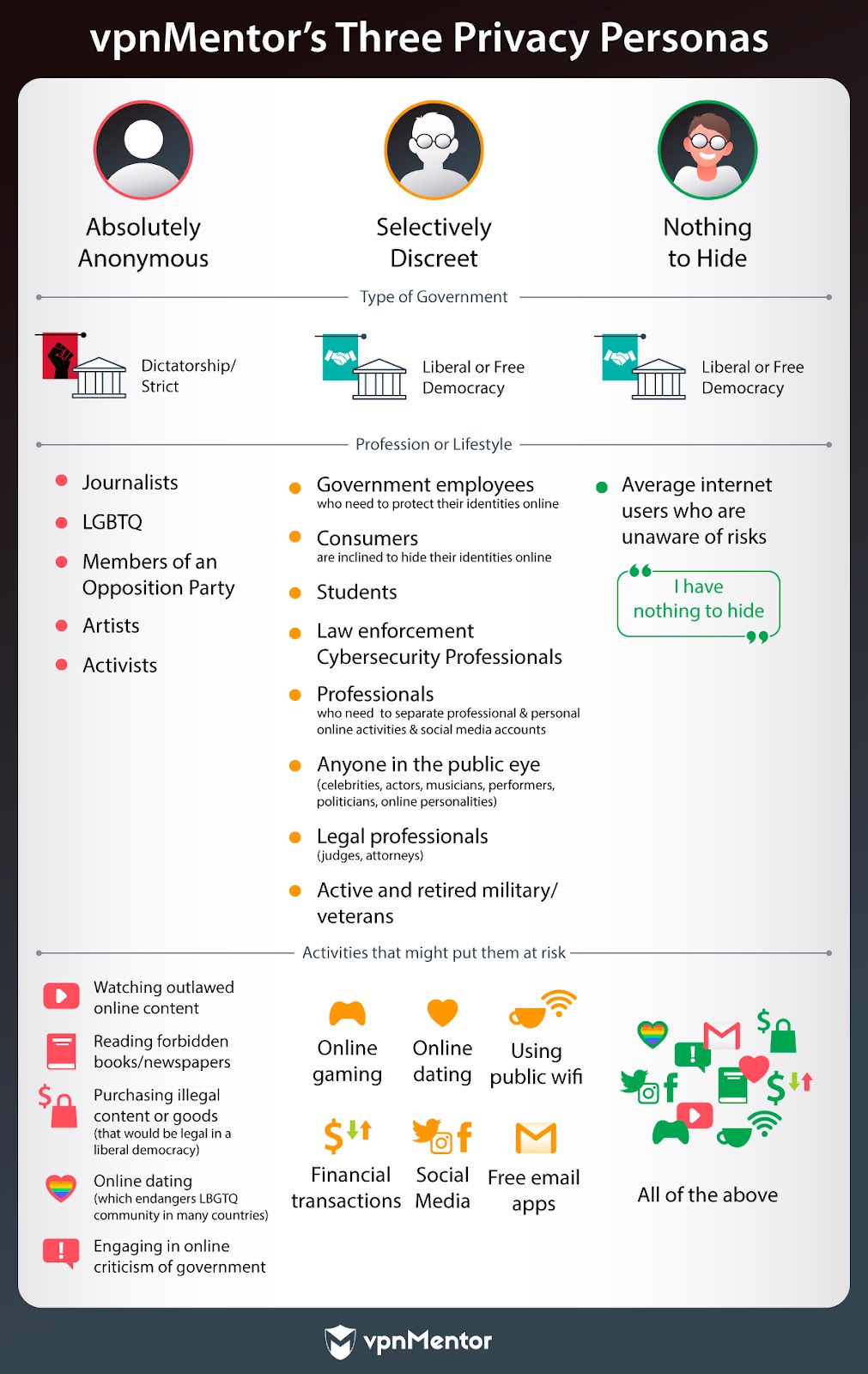
Google’s co-founder and former CEO, Eric Schmidt, once famously (or infamously) said: "If you have something that you don't want anyone to know, maybe you shouldn't be doing it in the first place." What he was talking about was criticism directed at his company for the widespread personal data that his search engine collected about its users.
That mindset has always plagued many internet users: that only people who break the law or conduct nefarious business online should be concerned about anonymity. Even if you’re not doing anything “you don’t want anyone to know”, your privacy should be your choice.
It’s imperative in the 21st century that you at very least educate yourself about what organizations collect about you and what they do with that information. You may be unaware of the actual dangers posed by identity theft or disclosing your physical location in the wrong arena. The more you know, the less likely that you’ll make more informed decisions and actions about what information you enter online.
Identity theft accounted for 65 percent of all data breaches during the first half of 2018.
Source: Gemalto/Thales Survey
Anonymity + Browsers and Search - Part 1
When it comes to data collection and individual information, search engines and browsers are amongst the most invasive of the tech platforms. In the earliest iterations of the web, personalization, the notion that a web platform like Yahoo, MSN, or Google delivered services and content tailored just for you was revolutionary. Back in the early or mid-00s, very few of us contemplated the far-ranging consequences of saving our home address in Google Maps to make it faster and easier to generate directions.
Innovation was--and is--exciting. It was exciting to encourage Yahoo to personalize your news feed based on your location. It sounded reasonable that Google’s ultra-smart algorithm, the first widely adopted AI that most of us interacted with this century, could all but predict what you wanted to search for as soon as you entered terms into its now iconic search bar.
We’re now two decades into that level of so-called personalization and the tech giants have gone from innovators to the greatest harvesters of our personal data in the world. As more and more concern simmers around how to curb the tech giants’ constant appetite for our information, it’s hard to remember a time when we were so willingly transparent.
Journalists like Recode’s Kara Swisher have made careers out of sounding the alarm about our willingness to hand over all of our data to big tech. In this chilling essay for the New York Times, Swisher asks readers to be “paranoid about privacy.”
Whether or not you are aware of the current dangers to your anonymity, or are still convinced that you “have nothing to hide” this is precisely how your behavior is tracked by Google and big tech to turn your eyeballs and online behavior into profits.


Further Reading:
Anonymity + Browsers and Search - Part 2
Staying anonymous while you browse isn’t a switch. Think of it more like a recipe of ingredients that, when combined and used consistently, offer you the best possible outcome.

What Big Tech Already Knows about You and How They Know it
We’ve already learned that there are dozens of companies that have the capacity to capture and store everything about you just from seemingly harmless behaviors like turning on your phone or executing a web search. The tools that are in place to do this have been with us for a long time. In the right hands: they are mostly harmless. Knowing how they can make you vulnerable provides you with the information you need to protect your anonymity while you utilize common and popular web tools.
What is a Cookie?
A cookie is a unique code of data a website stores in your web browser to help identify you the next time you visit the site. Cookies are a key ingredient in the web’s personalization revolution. Without cookies, a website can’t remember what you clicked on during your last visit, what items you selected for your shopping cart.
Session cookies are set to expire as soon as you close your browser session (hence the name). Session cookies are not inherently dangerous. Persistent cookies, however, are more troublesome. Websites sometimes set persistent cookies that sit inside your browser and record secure data. For example, the reason you don’t have to log into most online mail accounts or social media accounts (like Facebook) is because those sites set a persistent cookie when you log in with your credentials.
The smarter advertisers get, the more and more they use cookies to store more and more information about you to create increasingly targeted ads. The better you are at managing your browser history (see our tips below), the less those websites can track you, and the more likely you can keep your online footprint private and secret.
What is JavaScript?
JavaScript is one of the most prevalent and popular web programming languages, namely because of what it can do. Its best feature is that while you’re on a popular site like YouTube, Facebook, Amazon and more, elements of Javascript can update data (likes, comments, infinite scrolling) without you having to refresh the entire page. Disabling JavaScript will make it all but impossible to interact on the web, especially for popular applications like gaming.
As with cookies, javascript alone isn’t the problem. The problem is that you don’t have any control over a third party’s web security. When an unencrypted or poorly encrypted website is exploited by a hacker, that attacker can use what’s called cross-site scripting to inject a payload (virus) onto your machine through a standard browser session.
Even if you think you don’t have anything to hide, you are still often at the mercy of websites and browser-based security vulnerabilities that you can’t predict.
What is a Location Based Service?
Using either data from your cell phone provider or a GPS service, location based services (LBS) work with your cell phone to pinpoint exactly where you are. Apps like Yelp, map applications, Facebook, Google, and nearly countless others use LBS to push content to you (in the form of ads) or send you information when you request it (pull request). You can turn off LBS for different apps, or turn on the setting so it’s active only when the app is in use.
The problem, increasingly, is that third parties have figured out ways to track your location even when you have turned off location services and your phone’s GPS sensors. In 2018, a Princeton study revealed that smartphone locations were still tracked with a mix of security exploits to track your physical whereabouts.
More recently than that, a stunning (and one-of-a-kind) New York Times report (One Nation Tracked) gathered some shocking information about how cell phone tracking software is leaving us--quite literally all of us--ultra vulnerable to the most remedial location-based technology services.
From the 2019 report: “Now, as the decade ends, tens of millions of Americans, including many children, find themselves carrying spies in their pockets during the day and leaving them beside their beds at night — even though the corporations that control their data are far less accountable than the government would be.”
The data in the report uses the precise location of millions of smartphones over a period of months between 2016-2017. It’s the largest report like it ever to be compiled by a news organization. They used (from anonymous sources) data not from law enforcement or government agencies, but from small, private and unregulated data location companies.
What Does Your ISP Know?
In countries where the ISP is government-run: there is no legal limit to the amount of personal data that an ISP can collect and store since the same body that provides internet access also writes the laws that govern it. ISPs in America were previously prohibited by law from collecting information about you. Until, in 2016, this happened:
ISPs can now collect and sell your data: What to know about Internet privacy rules
Prior to 2016, the FCC mandated that ISPs kept most of your personal data a secret. Now, after the passage of the 2017 law, ISPs are in the same business as Facebook, Google, and other data giants. They can sell your information for a profit.
In short: your ISP is legally allowed to collect and monetize any information they harvest when you visit an unencrypted website.
When you sign up for your internet service, you are going to have to share some personal information. Like a physical utility company, the service they provide you is tied to a location, whether that’s a phone or a residential or business address. So, your ISP may know who you are, but they don’t always have to know what you’re doing.
Using tools like VPNs, your ISP may know who you are, but at the very least, they won’t have any knowledge about your online behavior.
Further reading:
- What Your ISP Can Learn About You & How to Protect Yourself
- How to Stop Others from Tracking Your Browser History
Anonymity + Free Email Accounts
Most of us utilize a free email account for communicating and registering for online apps including e-commerce, social media, gaming, and dating. Many of those free services turn your eyeballs into profit. Google goes as far as using bots to scan your email content, and using that data to push relevant ads to you on behalf of their advertisers.
It’s not at all cynical to say that the large free services “rent your eyeballs” to advertisers. Then there’s also the threat posed by massive data breaches, like the massive scandal that plagued Yahoo.
For many reasons: those online email services don’t need to know the real you. Below is a how-to for using online email while ensuring that your true identity never surfaces.

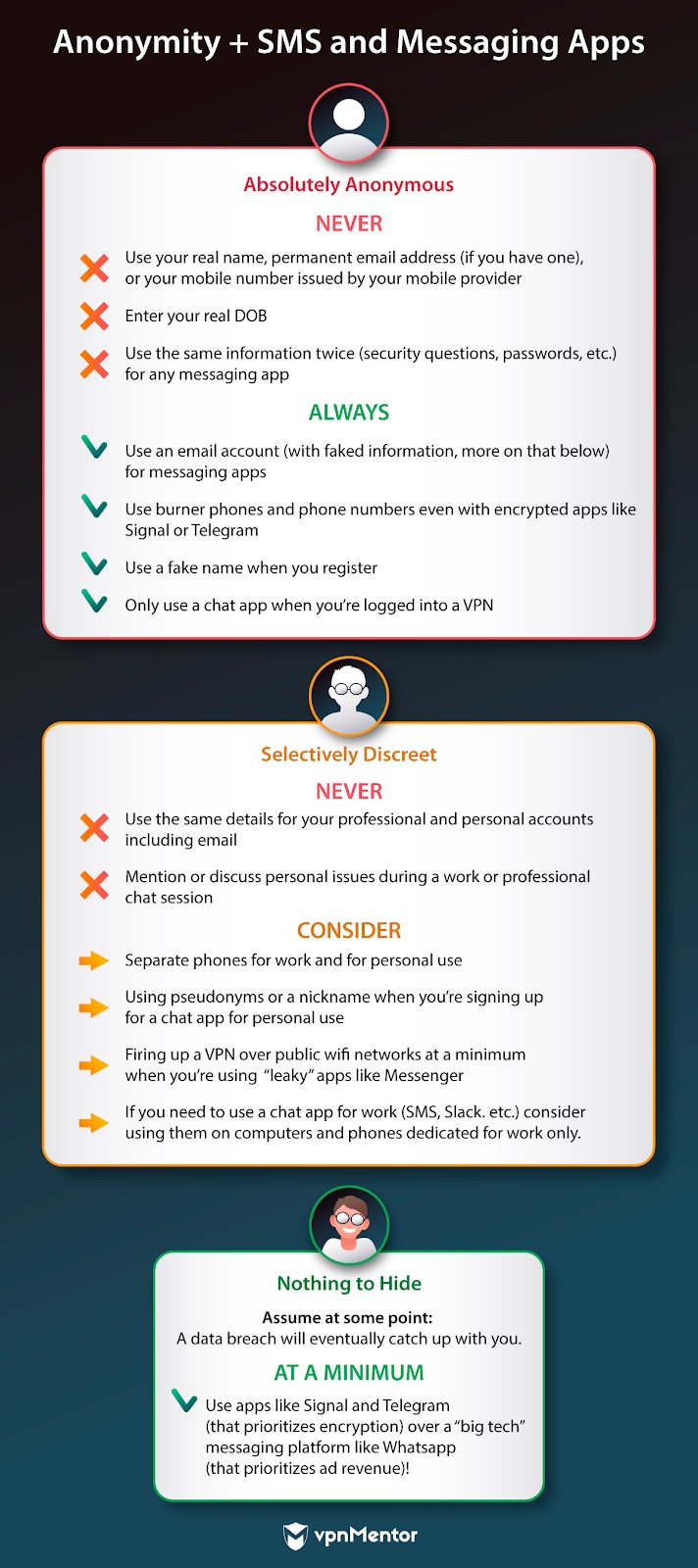
Anonymity + SMS and Messaging Apps
“If the servers of these companies fall victim to a data breach, malicious actors will gain access to the keys and can also decrypt your messages. The companies that host these services are then open to warrants from government agencies that want to investigate users' private communications.”
PC Magazine
Messaging apps (WhatsApp, Skype, Messenger, Slack) and SMS (text messaging) support end-to-end encryption. The session itself (especially if you’re using a VPN) is relatively private and inherently secure.
The system in which your information is stored, however? That’s another question. The company on the other end that’s running the app holds the encryption keys, as well as the keys to your anonymity. That anonymity is seriously jeopardized if your personal details (like your account login) is leaked.
When it comes to messaging apps: your anonymity is only as secure as the information you provide when you sign up for the app itself. While we always recommend that you avoid sharing personal details you don’t want leaking out within the chat (like a scan of a photo ID for example), if your goal is utter anonymity while you chat, you have to be cautious about what you share when you register.
Remember, when you’re registering to use a service like Signal, WhatsApp, Slack, and more: you don’t have to use your real name. Avoid entering any personal details so you can enjoy the freedom and convenience of these apps without incurring any of the risk.
Many chat apps (okay MOST chat apps) ask for a phone number when you register for double authentication. For free messaging apps, you can get around providing your “real” phone number by using a cloaking service or simply by using a burner phone.
Further Reading:
Anonymity + Social Media Apps
“Between 2013 and 2015, Cambridge Analytica harvested profile data from millions of Facebook users, without those users’ permission, and used that data to build a massive targeted marketing database based on each user’s individual likes and interests. Using a personality profiling methodology, the company - formed by high-powered right-wing investors for just this purpose - began offering its profiling system to dozens of political campaigns.”
The Facebook data breach wasn’t a hack. It was a wake-up call.
While social media continues to fall under public scrutiny, online networking often serves a value and a purpose in our lives. Digital marketing and communication professionals often must have personal social media accounts in order to do their jobs. As we saw in the Arab Spring uprisings, social media apps and online platforms like YouTube played a crucial role in disseminating information in countries with state-owned or propagandistic media outlets.
Facebook and Twitter--early in the dawn of social networking--maintained that collecting real names, DOBs, and verifying individual identities would make it less likely that users would be abusive online when they were using the platform. While that may have been well-intentioned, people remained unabashedly cruel and often dangerous on both Twitter and Facebook. As early as 2014, the GamerGate scandal made it painfully obvious that users are more than willing to be abusive without the mask of secrecy protecting them. Abuse on social media soon became the norm.
So, if verifying your identity wasn’t going to stop abuse, why still insist on identity verification? Post-2016, Facebook now claims it’s to stop the spread of fake news. So, if you’re in the business of opening a fake account to pay for sponsored posts or buy political ads, you may be out of luck.
Even with modified scrutiny behind the accounts that support paid ads and paid posts, it’s hard to see this as anything but post-scandal posturing. A study completed by Brown University in the U.S., the results of which were partly published by the UK newspaper The Guardian, revealed that 25% of all posts that question the scientific validity of climate change were posted and spread by bots. What’s more? Those bots can use the promoted tweet feature to give those posts even more exposure. From the article:
In 2017, a whistleblower revealed that an obscure political marketing and strategic agency called Cambridge Analytica leveraged a massive oversight in Facebook’s API to harvest the secret and private data of over 87 million Facebook users.
The reality is that the Facebook juggernaut (Instagram, WhatsApp, Messenger) has done absolutely nothing to earn the trust of global citizens where both privacy and anonymity are concerned. Time after time, scandal after scandal, the tech giants have proven that your personal data is for them to monetize and your personal identity is not worth protecting.


117 Million LinkedIn Emails and Passwords Posted Online

32 Million Twitter Passwords Compromised

Data from 87 Million Facebook Accounts Harvested by Cambridge Analytica
(Vox)

Research firm Gemalto: Social Media Accounted for over HALF of all Compromised Data Records in the First Half of the Year
(ITWeb)

Oops they did it again…
Facebook Discovers it Failed to Encrypt the Passwords to Hundreds of Millions of Profiles
(cnet)
...and...AGAIN?
Facebook reveals that it (WOOPS!) allowed some 100 app developers received access to millions of personal data points.
(ZDNet)

Anonymity + Sharing Apps
We all have to move around and use services that enable that movement. Most rideshare apps (like Uber) and rental-by-owner apps (Airbnb) confirm some aspects of your identity to protect both homeowners and drivers as well as passengers and riders. When you’re using rideshare and rental apps, it’s definitely a user-beware situation as both Uber and Airbnb have suffered massive data breaches.
Always weigh the value and convenience of the service before you decide to become a regular user. It’s a given that using the occasional rideshare may be more affordable than owning your own car. (It’s also a useful method of raising a needed influx of cash to pay off a surprise bill or keep up with the cost of living.)
When you register for one of these services and provide personal information, they may have the intent of protecting it; but they still get hacked. The bottom line is that you can and should protect yourself as best you can by taking small measures to ensure that your information remains relatively secure.
What does Airbnb ask for when you register?
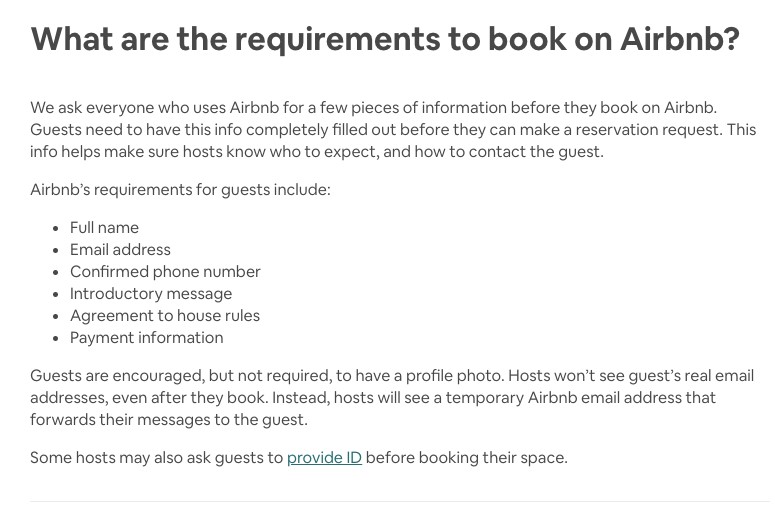
Airbnb is no stranger to data breaches. You can’t make a reservation request without filling out a basic Airbnb application. Suggestions: use an anonymized email address just for your Airbnb profile, use payment information (like PayPal) that isn’t linked to your physical address. Consider using a burner phone as a phone number and use as little information about your physical location when you sign up.
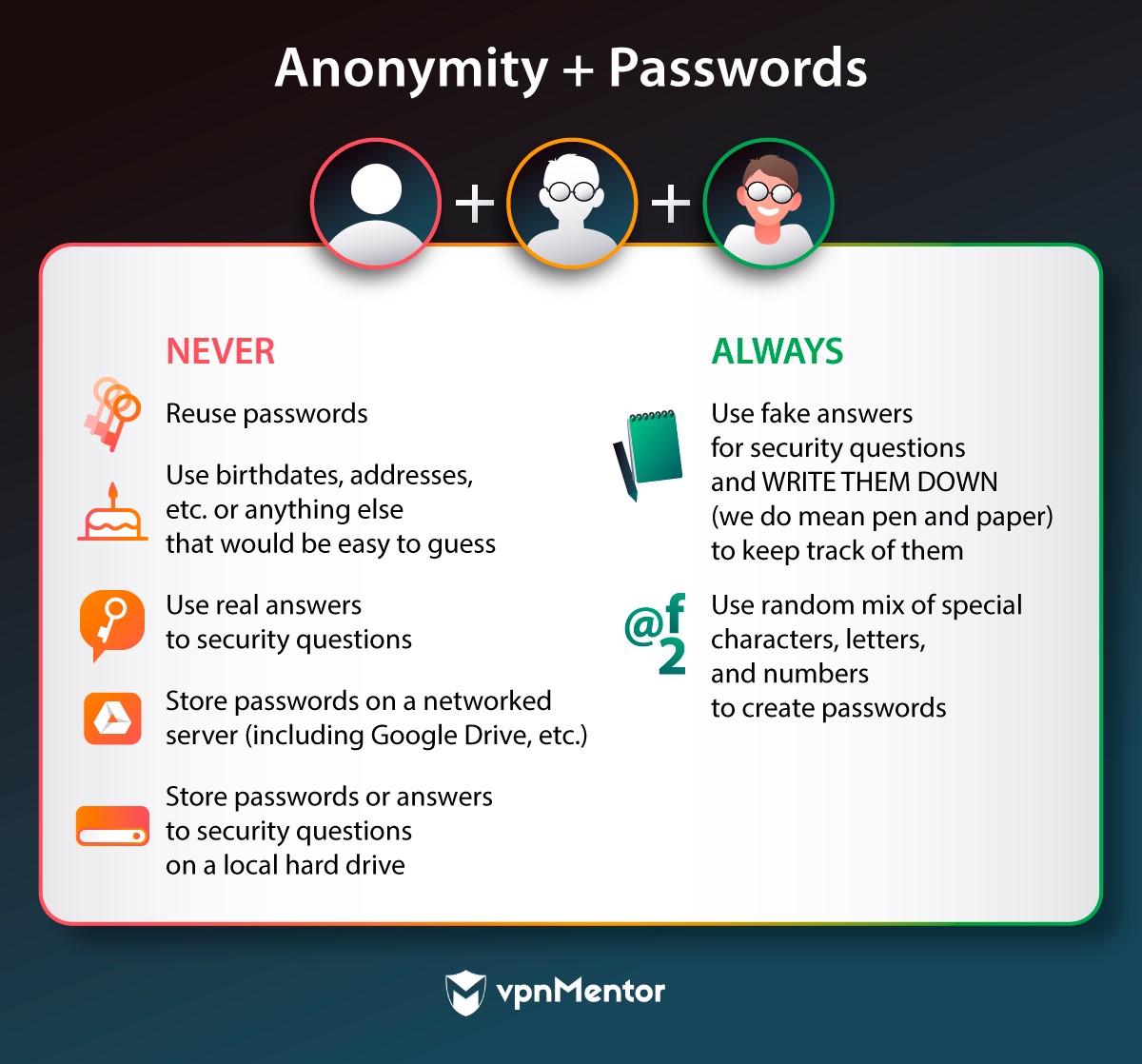
What does Uber ask for when you register?
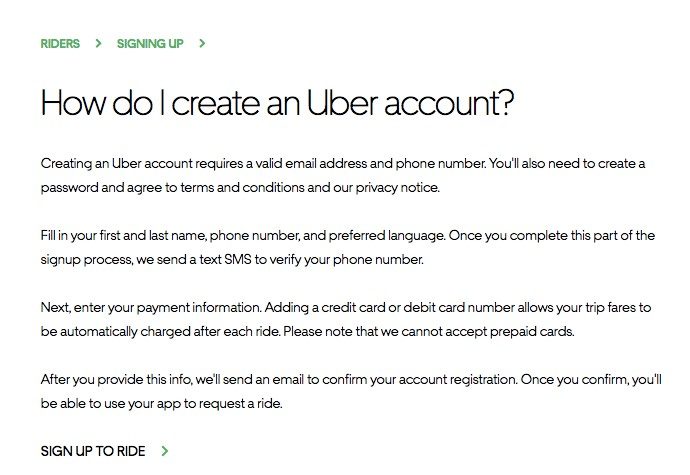
Uber asks for even less information than Airbnb. The same rules apply here: the less information that gets stored in its system about you, the better. For example, you don’t have to save your home or your work address on the app itself. The app’s location services will find you when you need a ride.
Further Reading:
- Why You Shouldn’t Use Your Airbnb WiFi (vpnMentor)
- The Dangers Of Using WiFi At An Airbnb (Fast Company)
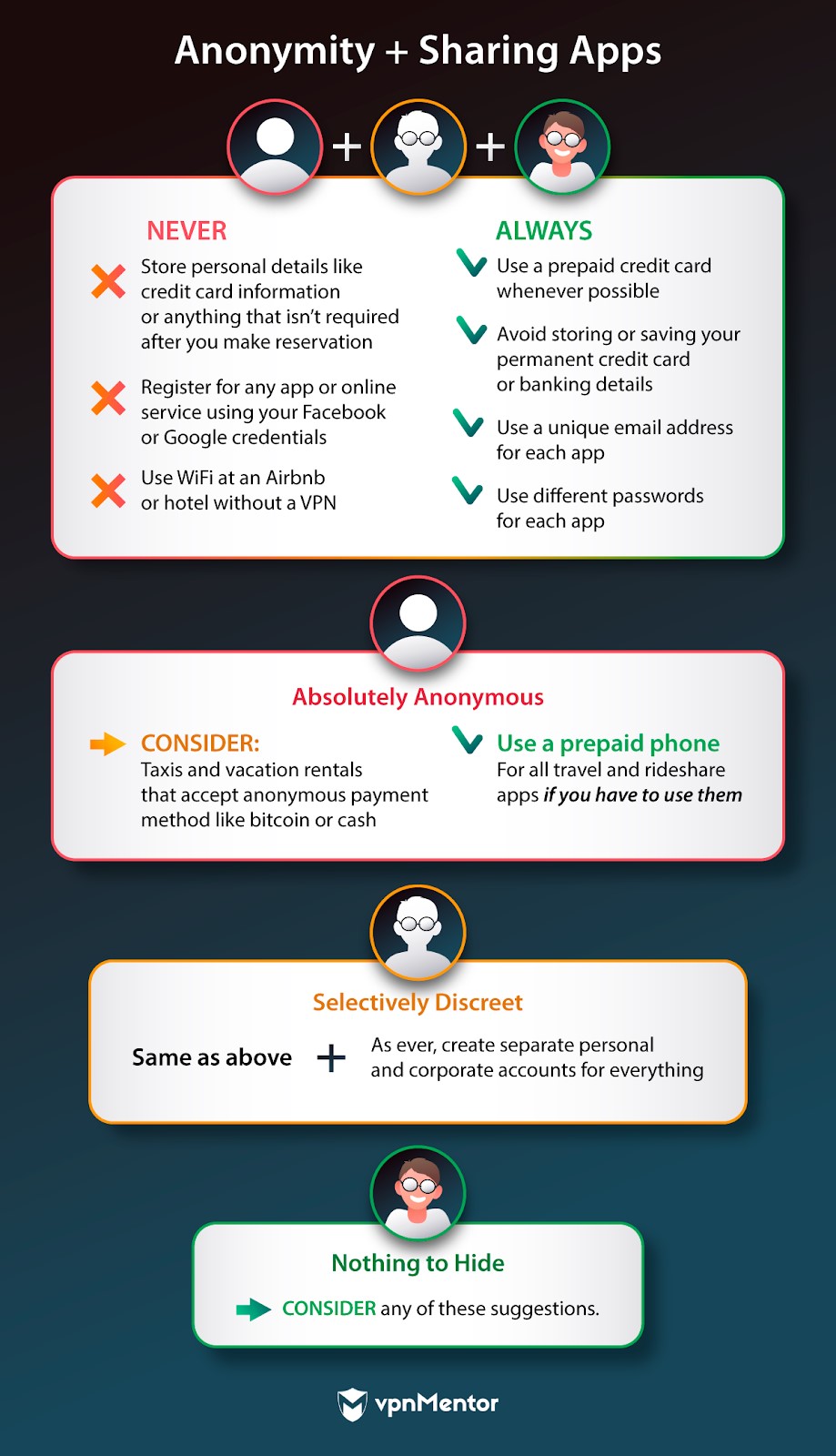
Anonymity + Public WiFi
You should feel free to use an open WiFi network when you need it. The trick is: how do you do it anonymously?
Your online security is tantamount to swiss cheese when you’re using a public/free WiFi network. The same can also be said for using private networks. For example: if you sign onto a friend’s WiFi account at their house, you have no way of knowing how private or secure that network really is. How many other people have the key to that network? What if a neighbor is able to jump onto their signal at any time?
We all periodically need to take advantage of an open WiFi network. Shared coworking spaces and cafes are increasingly popular for busy professionals. That WiFi in the hotel or cafe is there for a reason: people need it.
The reality is that hackers and cybercriminals have massive security holes they can leverage on an unencrypted network, leaving you and your anonymity exposed while you use it. As recently as 2019, CNET reported about the massive co-working company WeWork’s baffling wifi vulnerabilities. Even when coworking is central to a company’s business model: it drops the ball when it comes to security and encryption.
That means that your security and privacy on a public network at a hotel, coffee shop, or restaurant is likely an afterthought. Protecting yourself on a public wifi network is not just good common sense: it’s your responsibility.
Further Reading:
- Why You REALLY Need to Stop Using Public WiFi
- Steps to Protect Yourself on Public WiFi
- How Russian Spies Infiltrated Hotel WiFi to Hack Victims Up Close
- Warning: free hotel WiFi is a hacker’s dream
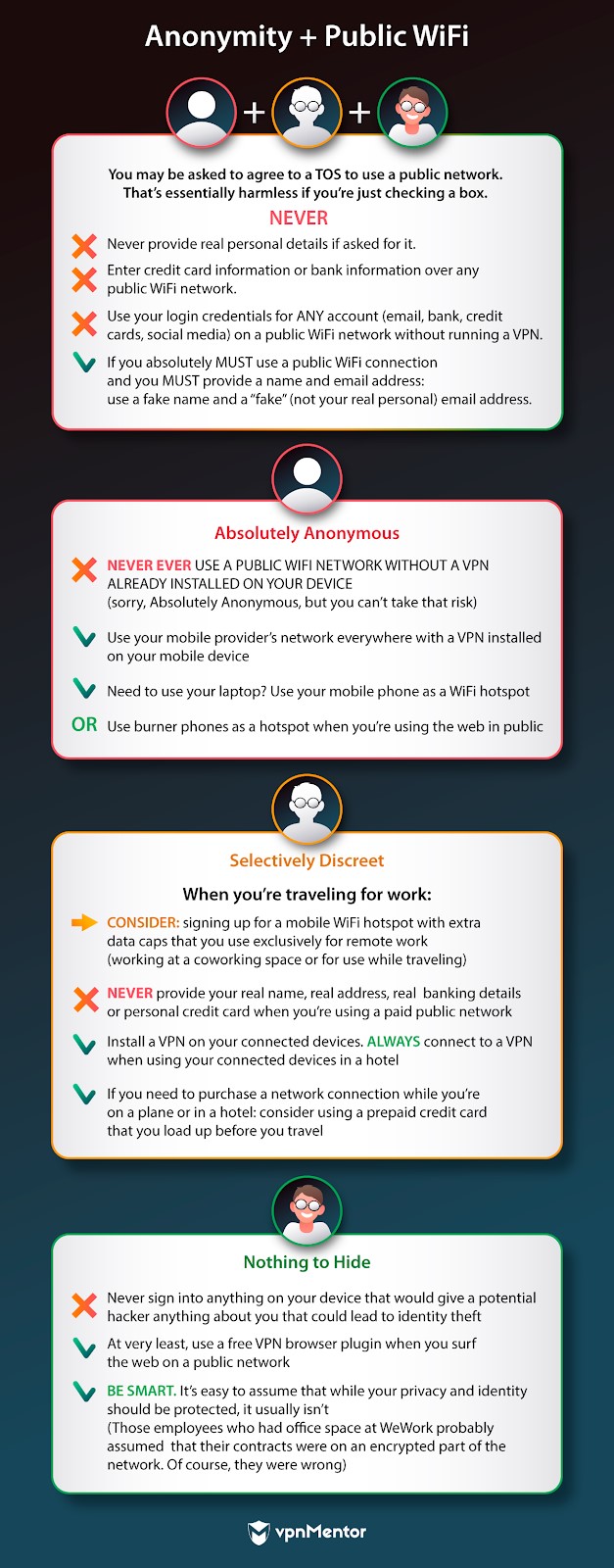
Anonymity + Passwords
What you say in your passwords can say a lot about you..or not. In general: people rarely realize how much information they’re giving away when they create passwords. It’s natural to use personal details because that makes our passwords memorable. It’s less important that your passwords are memorable, and more important that they are anonymized.
PRO TIP: Use vpnMentor’s password checker to verify if your password is appropriately strong.
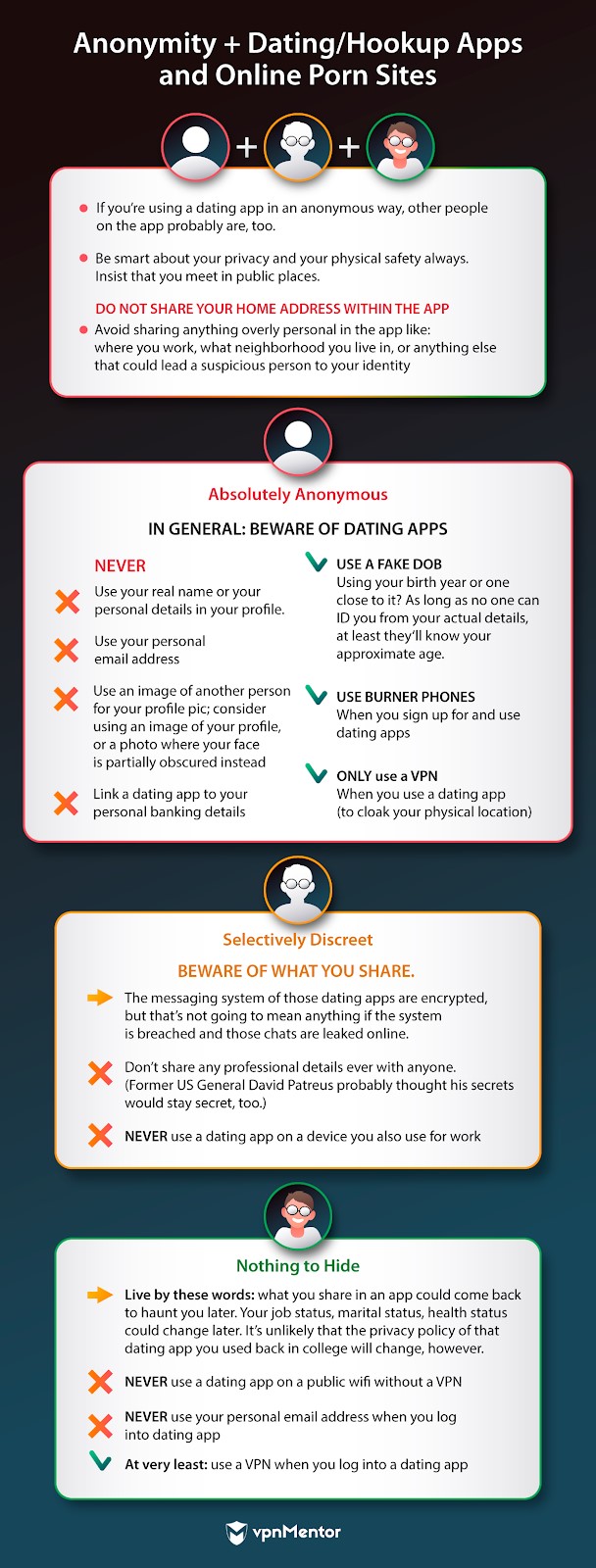
Anonymity + Dating/Hookup Apps and Online Porn Sites
Dating and hookup apps like Tinder and Grindr are currently the de facto method for meeting new people. From a security standpoint, those platforms are not merely irresponsible when it comes to protecting your identity. Like all the big data giants, dating apps have proven to be utterly lax and indifferent to locking down your personal information.
In 2018, Buzzfeed verified Grindr was sharing users’ HIV status and location information with two outside organizations. The company only agreed to stop sharing its users personal medical history (a clear violation of well-established medical privacy laws in the US) when it became the subject of a well-documented and publicized investigation.
Worth noting, before shutting down the practice, Grindr defended itself, “claimed that such sharing is normal in the tech industry, that the sensitive data was encrypted, and that users consented to the transfer of this data in the app’s fine print.” In other words: we told you, in a very small font that no one ever reads, that we could share your private medical history with whomever we like.
In one of the web’s most infamous data hacks, nearly 37 million former Ashley Madison customers are still feeling the sting of the site’s 2015 data breach. Now several years on, users are still living under the threat of potential extortion.
Porn sites are hardly known for locking down user data. vpnMentor’s internal investigation discovered a serious security leak that impacted the personal information for the performers on the online porn site Pussy Cash.
This circles us back to the value and utility of an app. Dating apps and any third-party site in general are simply not a safe place to trust with your true identity, particularly if a data breach could lead to blackmail. Even if the worst outcome is a public embarrassment, that could still result in the loss of a job, income, and reputation.
Further Reading:
- 5 Best VPNs for OkCupid
- Report: Dating App Leaks Explicit User Messages & Other Private Data
- Report: Niche Dating Apps Expose 100,000s of Users in Massive Data Breach
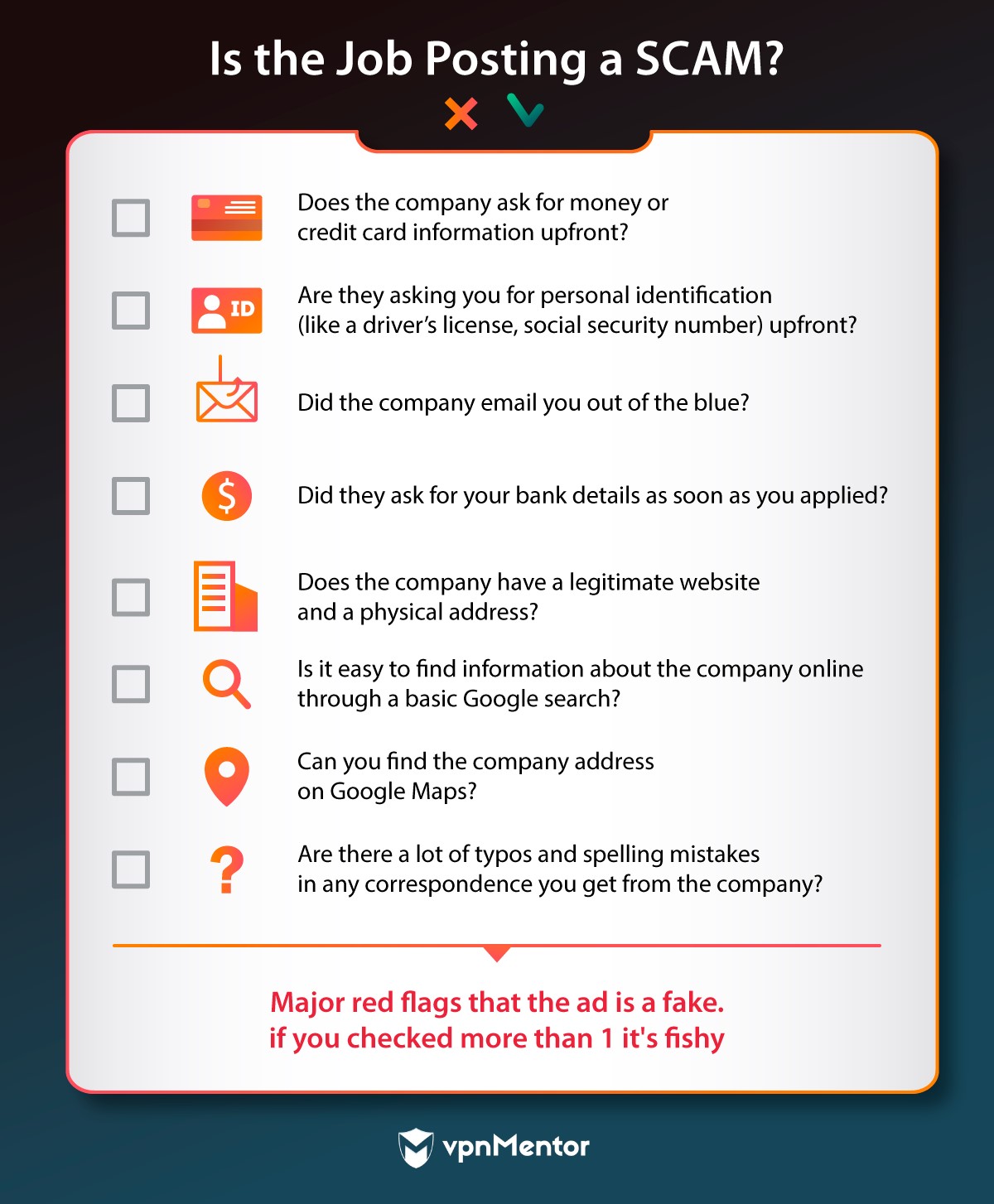
Anonymity + Job Sites and Virtual Work
Engaging in online job applications has become a common practice in today's gig economy. It's not uncommon for individuals to work remotely for employers they may never have the opportunity to meet in person. Whether you are responding to an online advertisement from a recruiter or agency, or submitting a cover letter to a private company, there are numerous methods available to safeguard your online anonymity when embarking on an online job search.
Some general security notes about applying for a job online.
- Job sites are just as likely to suffer a major data breach as anyone else is.
- Scammers and phishers often use job postings to get access to your personal information and your bank accounts.
- Subpar email marketers use job ads to resell the emails they scrape from the applications to advertisers.
So, before you even apply, give yourself a few minutes to determine if the job is legit.
Further Reading:
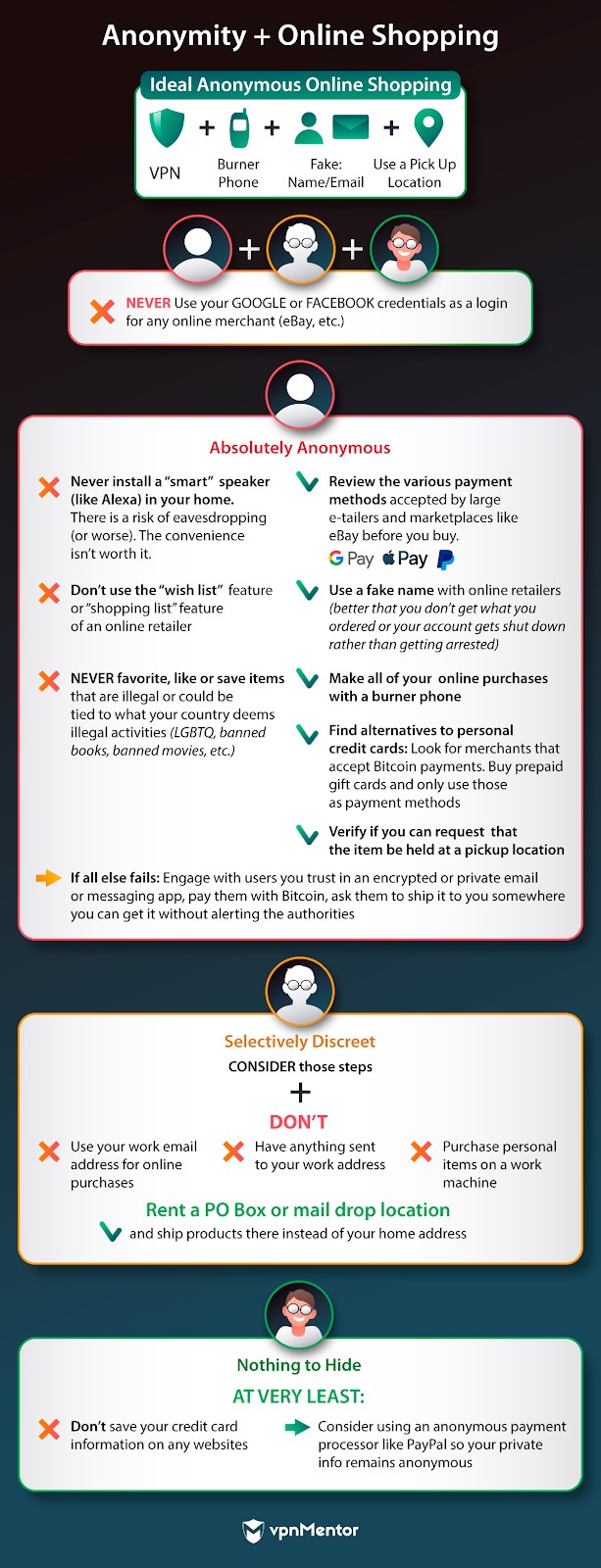
Anonymity + Online Shopping
By 2023, 22% of all global retail sales will happen online. Online shopping is certainly convenient and relatively easy to do from almost any device you own. Using a VPN when you shop online protects your inherent privacy, but how do you truly shop online in an anonymous way?
Online retailers, after all, often know a lot about you.
- Depending upon where you have your purchases shipped, e-tailers know (and store) your address and phone number
- Those companies may store your credit card details on file
- Retailers can easily draw a picture of you based on your wish lists, purchase, browsing, and search history.
Then, there’s also the potential of data breaches. The retail industry is certainly no stranger to them.
Residents of strict countries have more reason to be concerned about anonymity, especially when you buy illegal products and books. While it’s not remotely illegal in the U.S. to buy, for example, a vibrator or a magazine, the same can’t be said in, say, Saudi Arabia.
No matter where you live, you deserve the same level of personal expression and access to goods as everyone. The steps below should help keep your identity under wraps as you shop. Remember, also, that sometimes the convenience isn’t worth it.
Further Reading:
- How to Pay Anonymously. Anonymous Payment Methods Explained
- Report: Asus Router App Leaks Customer Data and Exposes Alexa Users
- Report – Gearbest Hack: Hundreds of Thousands Affected Daily by Huge Data Breach
- Report: Aliznet Data Breach Exposes Data for Millions of Canadian Customers
- Security researchers expose new Alexa and Google Home vulnerability
- Google Home and Amazon Echo hit by big bad Bluetooth flaws
Anonymity + Online Gaming
Without stating the obvious: people love playing games. It’s increasingly the world’s favorite online pastime. On the surface, video games are a harmless and fun hobby and a great way to socialize. We all have to acknowledge the hidden dangers that make games and gaming companies just as vulnerable to online criminals, hackers, and anonymity leaks.
Gaming companies understandably focus on more your gaming experience and less your personal security. The gaming companies are great at a lot of things. They work with remarkable designers, they certainly deliver engaging and fun content. We’re not saying don’t play games. Instead, beware of how rampant data breaches with even the largest gaming companies can be.
Yes: Gaming Companies Also Get Hacked
EA Games Leaks Personal Data of 1600 FIFA 20 Competitors
“Contenders signing up for the FIFA 20 Global Series competition were asked to enter personal information into what should have been a blank online form to verify their EA account details. But instead of being empty, the form's fields displayed the personal information of gamers who had already signed up for the soccer video game challenge.”
Data Breach Warning For 200 Million Android And iOS Gamers
“Zynga is home to some of the best known social games, including the likes of Farmville, Mafia Wars and Zynga Poker. However, according to the report that broke September 29 at The Hacker News, Gnosticplayers has claimed to have breached the Words With Friends player database.”
Fortnite Breach Suit Highlights Video Games' Oversized Cyber Vulnerabilities
“A lawsuit filed in the U.S. District Court for the Eastern District of North Carolina is based on cybersecurity firm CheckPoint’s January announcement that hackers breached Epic Games users’ accounts and had access to their passwords, credit and debit card information, and other personally identifiable information.”
Gamers: Beware of Swatting Pranks
Swatting is a form of online revenge that started in the ranks of social media. It’s evolved into something far more sinister and dangerous, where fellow gamers report fake crimes on other players.
It earned the name because the act of calling in a (fake) dangerous threat to local police triggers the arrival of a SWAT team. Those teams arrive on-site armed to the teeth and prepared for an armed conflict. From CNN: “At the most basic level, swatting is similar to the prank calls you and your friends might have made growing up. The difference is, swatting is a prank call made to authorities with the express purpose of luring them to a location -- usually a home -- where they are led to believe a horrific crime has been committed or is in progress. This results in a forceful response from the local police or SWAT teams, who have no way to know the call is a hoax.”
Terrifying Examples of Swatting Pranks Gone Very (Very) Wrong
A feud over a $1.50 bet between two COD players resulted in the shooting death and a 20-year jail sentence:
A "Call Of Duty" Gamer Was Sentenced To Prison For A Police Swatting Prank That Killed A Man
A global Fortnite champion was himself the victim of a swatting prank when he was all of 16 years old. His life was saved when one of the armed officers happened to recognize him from the neighborhood. Shockingly, this entire incident happened while he was live streaming on Twitch, the video platform favored by gamers globally.
Fortnite 'swatting': Armed police enter Bugha's home
Follow the steps below to ensure that even as a gamer, your personal anonymity and physical safety are never threatened.

Conclusion
We believe that everyone should feel entitled to free and open movement on the internet. That does mean that for many, if not all, of us, that movement and freedom comes with a cost.
Unfortunately, companies and services that should ultimately be protecting your privacy and your identity either refuse to (Facebook, Google) or often fail to (gaming companies, retailers, banks, rideshare, and travel apps).
The bottom line: paranoia is never a substitution for action and information. Educate yourself, stay informed, adjust your behavior, and then live your life freely and openly within those digital borders that you create and maintain for yourself.
If you found this guide helpful, please share it with so more and more people around the world can use the web in a more anonymous, and secure, way.
(Feel free to share and copy this post or parts of it to your site, blog, or social networks. All we ask is that you attribute it to vpnMentor.com)







Please, comment on how to improve this article. Your feedback matters!