How to Disable WebRTC in Seconds (Step-by-Step Guide)
A VPN is a powerful tool for stopping your personal information from falling into the wrong hands. But websites can exploit a technology called WebRTC to make direct connections between their servers and your web browser. These connections ignore your network settings and may even evade your VPN.
Read on to learn how to disable WebRTC so that your private information stays private. We'll also explain how a really reliable VPN service can help you stay even safer.
One of the big advantages of using a VPN is that it allows you to hide your personal IP address. When your web browser makes a direct connection to a server, this information is easily revealed.
If hackers, advertisers, or others learn your IP address, they gain access to information about your location, your internet service provider, and even the device you are using.
It doesn't matter what browser you're using. WebRTC is designed to run on all of them.
Fortunately, though, WebRTC can be disabled in any browser. In every case, it's an easy process if you know what you're doing.
This article will show you exactly how to disable WebRTC in each of the three main browsers: Google Chrome, Mozilla Firefox, and Microsoft Edge.
What is WebRTC?
You may be wondering why your browser includes such a glaring vulnerability. Well, WebRTC does serve a purpose for many users.
There may even be times when you want to reverse the steps in this guide to enable it again. You will need to do so if you want to share real-time audio and video over the internet. This is where WebRTC gets its name - it stands for "web real-time communication."
The technology has positioned itself as the main competitor of the popular video-calling software, Skype. It is more convenient because it works directly in the browser using JavaScript. This way, users don't have to download Skype or any other third-party software.
But the convenience comes with a price. A website's code can be written with scripts that open a WebRTC connection to any browser where it's actively running.
This means that WebRTC can leak your IP address even if you've never used the technology for its intended purpose. It doesn't matter whether you've actually accepted a direct audio/video connection or not.
As long as WebRTC is fully enabled in your browser, it's putting you at risk.
Disabling WebRTC in Chrome
Google and the Google Chrome browser's development team have vigorously advocated for the open-source code of WebRTC. This may shed light on why there isn't an option to deactivate WebRTC via Chrome settings. However, disabling it is still feasible and not particularly challenging; it merely calls for the installation of a browser extension.
Start by navigating to the Google Chrome web store. Click to open the following link in Chrome or type the URL into the Chrome address bar: https://chrome.google.com/webstore/
In the search field on that page, type "WebRTC Control." The browser extension should be the first result.
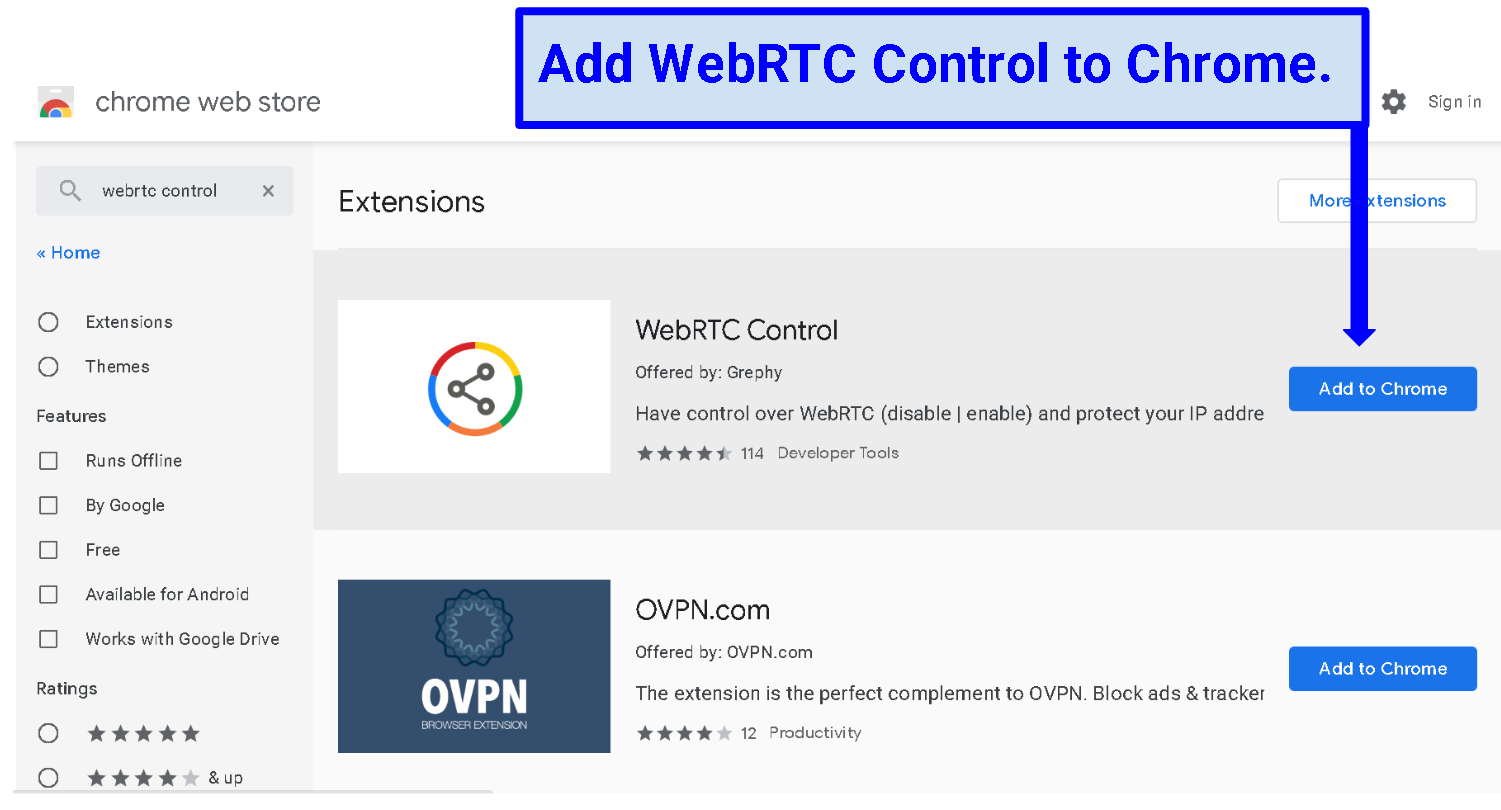 Install WebRTC Control from the Chrome Web Store
Install WebRTC Control from the Chrome Web Store
All you have to do to enable it is click "Add to Chrome," then click "Add extension" in the dialogue box that opens. WebRTC Control will install automatically and Chrome will open a new page that includes some additional information about the browser extension.
You can read up on the extension or you can right-click on the extension icon in the upper-right corner of the browser in order to change its options. But all you need to do is ensure that the icon has a blue circle around it. That means WebRTC Control is enabled and is doing its job.
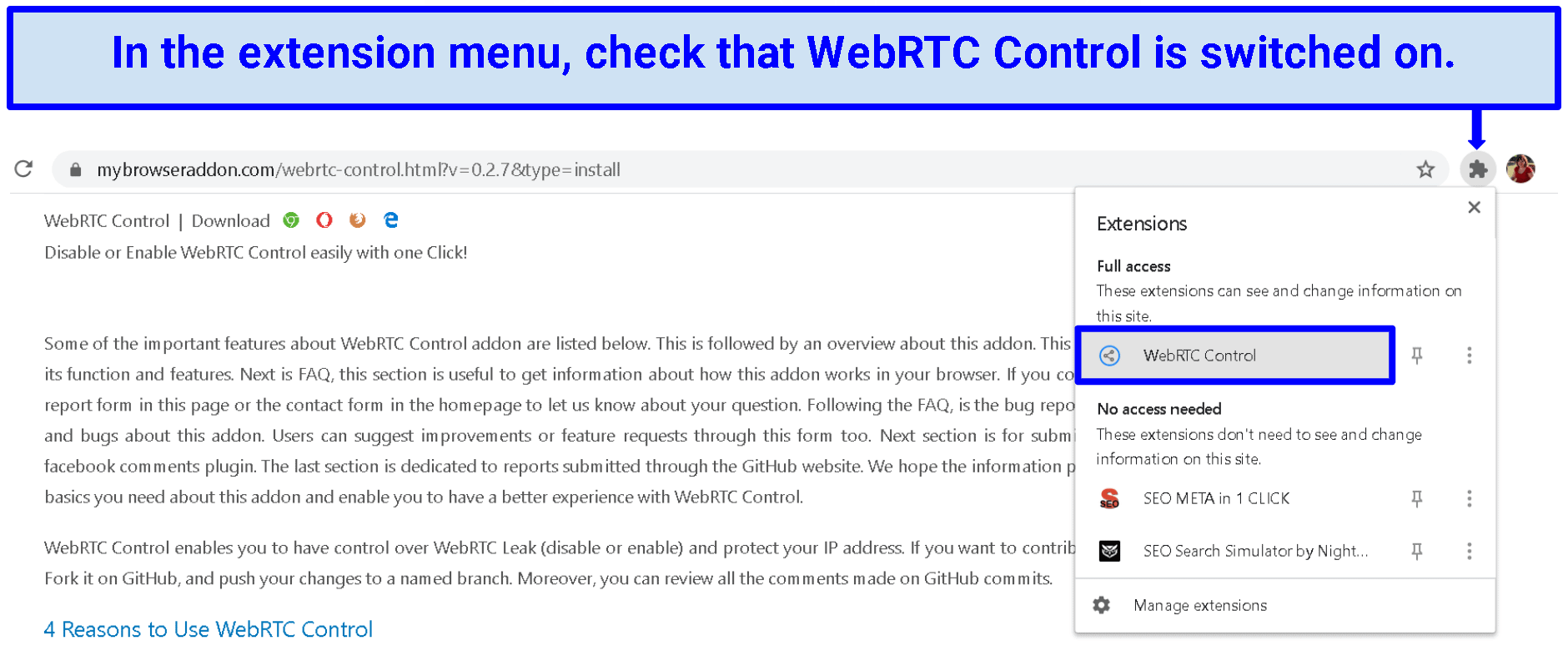 A blue circle around the WebRTC Control logo indicates that it is working
A blue circle around the WebRTC Control logo indicates that it is working
Disabling WebRTC in Firefox
Mozilla Firefox also has browser extensions available that will disable WebRTC. But there is an even easier way of doing so. Just type "about:config" into the address bar and then click the button on the warning page that says "I accept the risk!" If you just make the specified change, your browser's performance won't be affected in any way.
On the spreadsheet-style page that opens, type "media.peerconnection.enabled" in the search field. That term should now be the only thing that appears on the site. On the right side of that row, under "Value," it will say "true" if WebRTC is enabled.
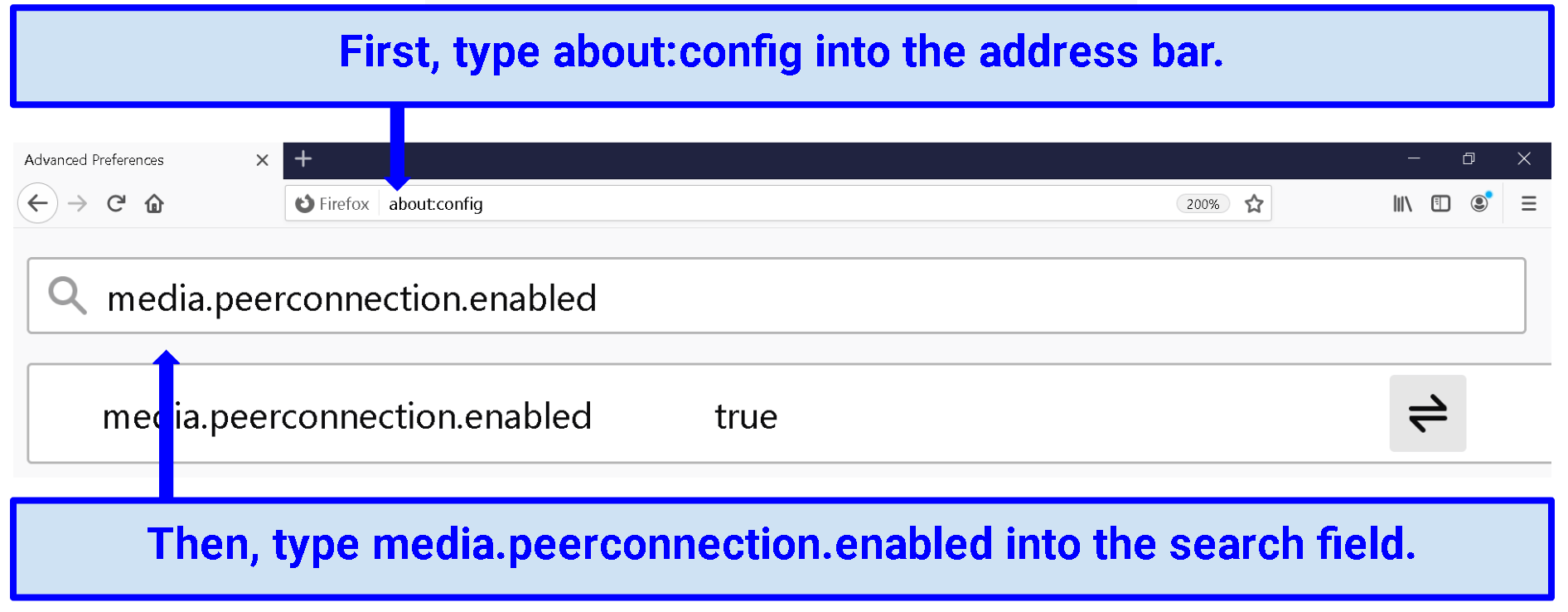 WebRTC is "true," which means it is enabled
WebRTC is "true," which means it is enabled
To disable it, all you need to do is double-click anywhere on the row and change the value to "false."
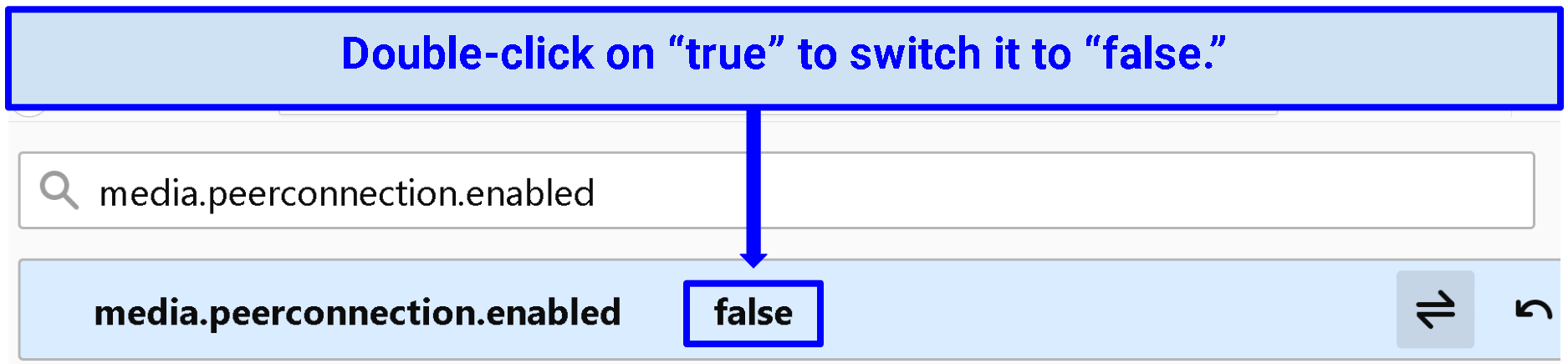 WebRTC is "false," which means it is disabled
WebRTC is "false," which means it is disabled
If you need to enable WebRTC at any time, just repeat the process. But remember to set the value as "false" again once you're no longer using a direct, peer-to-peer connection.
Disabling WebRTC in Edge
Microsoft Edge makes it every bit as easy to switch WebRTC on and off.
More specifically, it partially disables the technology to address the specific security concern that arises from it.
If you type "about:flags" into Edge's address bar, you'll see a list of developer settings. At the bottom of that list is a checkbox that says "Hide my local IP address over WebRTC connections."
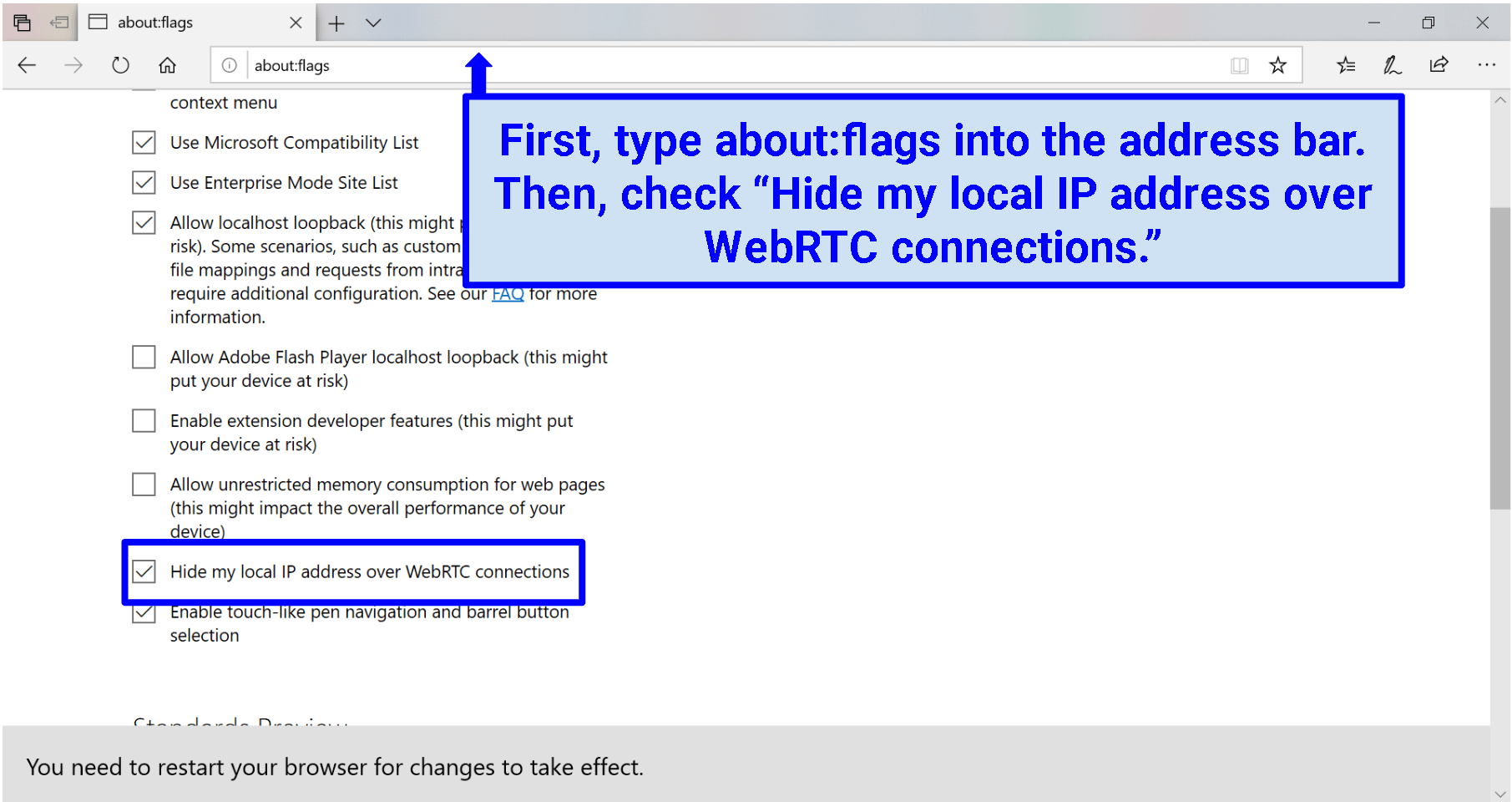 Tick "Hide my local IP over WebRTC connections"
Tick "Hide my local IP over WebRTC connections"
By default, that box should be unchecked. Of course, you'll want to click so the feature is enabled. You won't be turning WebRTC connections off completely, but you will be boosting your security, especially if you're already using a recommended VPN.
When you click the box, a message will pop up to remind you that you need to restart your browser for the change to take effect.
The good thing about this feature in Microsoft Edge is that it allows you to use WebRTC more securely, without the need to toggle it on for video chat, and off for regular browsing.
Conclusion
WebRTC is a potentially serious security vulnerability. It affects everyone, regardless of the browser or operating system they are using. And it may even affect people who are vigilant about safeguarding their privacy with a VPN. But despite all this, it is unusually easy to correct the problem. In just a few seconds, and with just a few clicks, you can expand your VPN's safeguards to places where they normally might not reach. Then, even the sneakiest online code won't be able to force you to reveal your IP address.





Please, comment on how to improve this article. Your feedback matters!