Online Privacy Guide for Journalists - Guard Your Sources
1. Introduction
Many veteran journalists, among others, have begun to notice that internet users are suddenly being bombarded with mentions of Watergate. Books like George Orwell's 1984 are on display at bookstores. And an air of danger to freedom of speech and freedom of the press is spreading slowly like a dark cloud over the Western Hemisphere, raising old fears.
When the American president accused his predecessor of surveillance; when he prevented major US media outlets access — previously always granted, and taken for granted — to press conferences; and when he incessantly accused the media of being the country's enemy number one, it shouldn’t be surprising that memories of President Nixon surface in direct correlation with every self-pitying tweet about SNL.
Many journalists, whom I have spoken with recently, are concerned about what lies ahead for the freedom of the press. Donald Trump’s tumultuous tenure as president, his apparent abuse of the system and spoken disregard for civil rights, and his possible return to office, are disconcerting for many people concerned with liberty.
Add to that the discovery from the CIA that almost all encryption systems can be compromised, if someone has the wherewithal to crack them — and you are en route to envisioning an utterly dystopian world. A world in which people cannot even be comfortable in their own home, in front of their smart TV while their smart vacuum whirs around them.
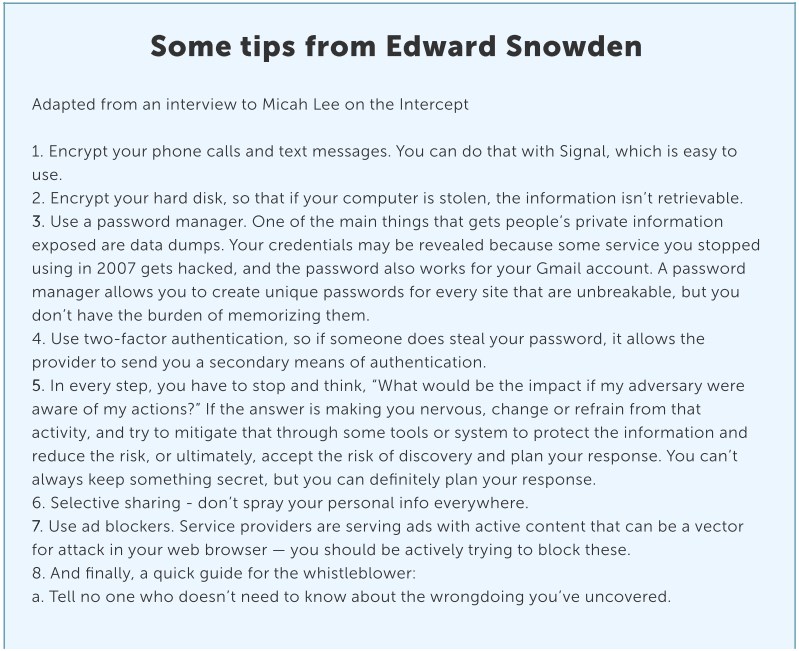
The good news is that, in spite of all this, there are some Edward Snowden styled privacy tips that make it difficult for anyone to try and intercept your emails, text messages, or phone calls. You can take measures to make the lives of those who want to uncover your sources, and the information being revealed to you, much harder. Of course, the degree of effort you’re prepared to take to protect your privacy, your sources’ anonymity, and your data’s safety should be commensurate to the likelihood of a real threat, be that hacking or spying.
“The old-fashioned promises — I’m not going to reveal my source’s identity or give up my notes — are kind of empty if you’re not taking steps to protect your information digitally,” Barton Gellman of the Washington Post said in an interview with Tony Locy. Gellman’s source, former NSA contractor Edward Snowden, helped uncover the scope of the NSA’s and British GCHQ’s operations.
So, what is it that needs to be done to ensure that a journalist's sources and data are secure and well? Some tips include:
- Securing on-device applications and functions: This is known as reducing the “attack surface,” i.e., limiting your installed apps to the bare minimum, installing only from trusted sources, selecting apps that require minimal rights, keeping the system fully patched and updated, and having the security controls recommended by recent best-practice white papers on the device.
- Isolating your devices and/or their environment: For example, the physical insulation of a computer for the purpose of checking files, or the use of prepaid mobile devices.
- Practicing caution both in the digital and real world: This has a lot to do with common sense and a little less to do with software. For example, never write down the name of a source, certainly not on any app or on any document that’s stored on your computer — and most certainly not on anything stored on the cloud.
2. Communicating with Your Source and Safeguarding Sensitive Data
Let's start by enumerating some key Edward Snowden privacy tips you can take in terms of communicating with a source and safeguarding any sensitive data they’ve given you:
- Beware of big names: Presume that large companies' encryption systems and possibly even big name operating systems (proprietary software) have back doors that secret services in their country of origin (at least in the US and UK) can access. Bruce Schneier, a renowned security expert, explains it here.
- Always encrypt everything: Security experts use simple math to make their point: as you raise the cost of decrypting your files (say, for intelligence agencies like the NSA), you automatically increase the degree of effort expended on following you. If you're not Chelsea Manning, Julian Assange, Edward Snowden, or engaged in some criminal enterprise, surveillance teams may give up the effort even if your encrypted communications were stored. And should anyone decide to track you despite your efforts, it will be more of a headache if you use strong encryption like AES (Advanced Encryption Standard) and tools like PGP or openVPN, which are the strongest widely available encryption methods (VPN's are used by the US government itself). But if you want bullet-proof security, you will need more than the AES encryption method.
- Perform full disk encryption: This is done just in case someone gets their hands on your computer or phone. Full disk encryption can be done using FileVault, VeraCrypt, or BitLocker. Putting a computer in Sleep mode (instead of Shutdown or Hibernate) may allow an attacker to bypass this defense. Here, Mika Lee gives a complete guide for encrypting your laptop.
- Avoid chatting with sources on the phone: All phone companies store data related to the caller and the receiver's numbers, as well as the location of the devices at the time calls were made. In the US and several other countries, these companies are required by law to disclose information on registered calls in their possession. What can be done? You should use a secure call service, such as the Signal app — which was tested repeatedly for security — possesses. Although this may mean that both the source and the editor need to download the app, the process takes just a few minutes. Here is a guide on how to use it. If you’re curious, check out how many of your non-journalist friends are hanging out there. However you choose to communicate with your source, do not bring your mobile phone to sensitive meetings. Buy a disposable device and find a way to convey its number to the source in advance. The source needs to have a safe, disposable device too. Authorities can track your movement through cellular network signals, but carrying a second, disposable phone can make it harder on them to locate you retroactively in the exact same cafe where the source was sitting. If you fail to follow this rule, all local authorities will be required to do is ask (politely and legally) for the video filmed by the café's security camera at the time of your meeting.
- Choose secure messengers: Your calls (cellular and landline) can be monitored by law enforcement agencies and each SMS is like a postcard — all text is fully visible to anyone with the ability to intercept it. Therefore, use messenger apps that allow for secure end to end calls: Signal, which was already mentioned above, and Telegram are considered to be the safest (although Telegram as well as WhatsApp’s web apps were compromised once and then fixed). According to some experts, you can also consider using SMSSecure, Threema, and even Whatsapp. The Signal Protocol has actually been implemented into WhatsApp and Facebook Messenger, encrypting messages sent through these platforms. However, unlike Signal and WhatsApp, Facebook Messenger does not encrypt by default, nor notify users that conversations are unencrypted — but offer end-to-end encryption in an optional mode. You should also keep in mind that Facebook messenger and WhatsApp are both owned by Facebook. Adium and Pidgin are the most popular Mac and Windows instant messaging clients that support the OTR (Off the Record) encryption protocol and Tor — the web’s best encrypted browser, which we will get to in detail later (see how to enable Tor in Adium here). Naturally, you could also use the Tor Messenger itself, which is probably the safest of them all.
 Two final notes on texting. First, a cyber security expert I’ve discussed this with says you should assume that, even if your text is encrypted, the fact that these specific two individuals are talking, at this present time, might not go unnoticed. Second, you should also remember to delete the messages in your phone (although this may not be enough to withstand a forensic check), just in case your device falls in the wrong hands, to avoid exposing your sources.
Two final notes on texting. First, a cyber security expert I’ve discussed this with says you should assume that, even if your text is encrypted, the fact that these specific two individuals are talking, at this present time, might not go unnoticed. Second, you should also remember to delete the messages in your phone (although this may not be enough to withstand a forensic check), just in case your device falls in the wrong hands, to avoid exposing your sources. - Do not use organizational chats: Slack, Campfire, Skype, and Google Hangouts should not be used for private conversations. They are easy to crack and are exposed to disclosure requests from courts to resolve legal issues at the workplace. Therefore, it's best to avoid them not only when conversing with sources, but also in conversations between colleagues, editors, etc., when you need to pass information received from your source, whose identity must be kept under cover. Many popular VoIP services like Jitsi have built-in chat features, and several of them are designed to offer most of Skype's features, which make them a great replacement.
- In extreme cases, consider using a Blackphone: This phone, which strives to provide perfect protection for web surfing, calls, text messages, and emails, is probably the best substitute for a regular phone if you are about to topple your government or getting ready to publish secret military files. In these cases, a bullet-proof vest may also come in handy. Alternatively, try to do without a cell phone, or opt for a cellular phone RFID signal-blocking bag. Even the Blackphone can be tracked using its IMEI (the mobile phone’s ID).
- Protecting data on your computer: It’s very easy to break regular passwords, but it can take years to break passphrases — i.e., random combinations of words. We recommend trying secure password management tools like LastPass, 1Password, KeePassX, so you’ll need to remember only one password. Even so, when handling important services such as your email, do not rely on password managers. In an interview with Alastair Reid in journalism.co.uk, Arjen Kamphuis, an information security expert, recommended that for encrypted hard drives, secure email, and unlocking laptops, one should choose a password of over 20 characters. Of course, the longer the password, the harder it is to crack — but the harder it is to remember too. That’s why he recommends the use of a passphrase. "It can be anything, like a line of your favorite poetry," Kamphuis says, "maybe a line from something you wrote when you were nine that no one else will know about.” Reid reports this thought provoking calculation, using the Gibson Research Corporation's password strength calculator: A password like "F53r2GZlYT97uWB0DDQGZn3j2e," from a random password generator, seems very strong, and indeed it is, taking 1.29 hundred billion trillion centuries to exhaust all the combinations even when the software is making one hundred trillion guesses per second.
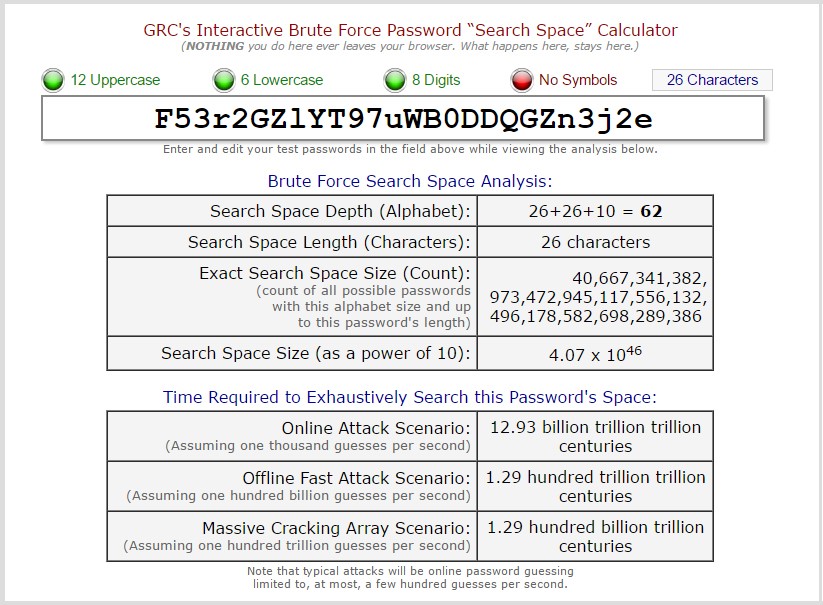
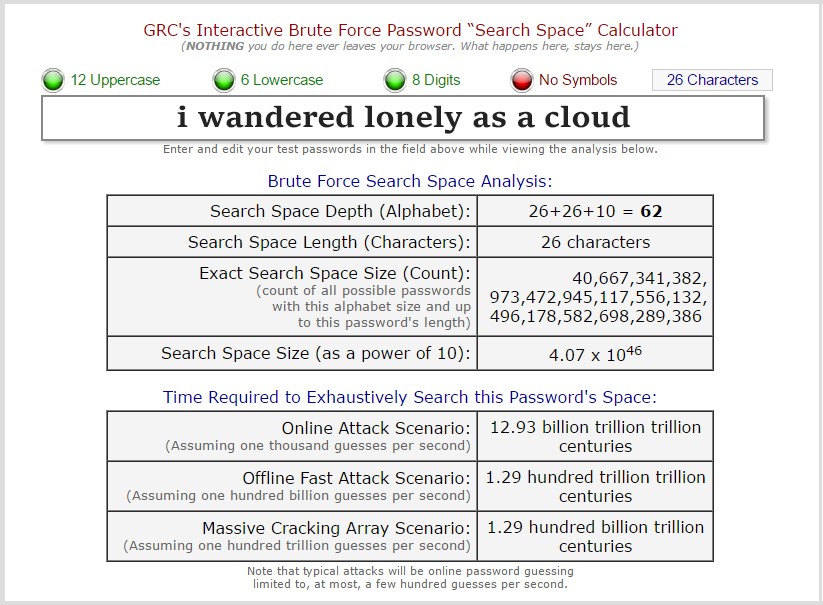 Screenshots from GRC.com, showing the difference in strength between a password and a passphrase. The phrase: "I wandered lonely as a cloud," he points out, is so much easier to remember and is also more secure, taking the same software 1.24 hundred trillion centuries to exhaust all possibilities. Well, passphrase it will be.
Screenshots from GRC.com, showing the difference in strength between a password and a passphrase. The phrase: "I wandered lonely as a cloud," he points out, is so much easier to remember and is also more secure, taking the same software 1.24 hundred trillion centuries to exhaust all possibilities. Well, passphrase it will be. - Two-factor authentication: In a regular two-stage authentication you sign in with your password and receive a second code, often via a text message to your smartphone. You can use Yubikey, as well as hardware tokens, to further secure sensitive files on your computer. For more information, read the 7 golden rules for password security.
- Assign a computer for inspecting suspicious files/attachments: The easiest way to distribute malware and spyware is through installation via USB or through attachments and email links. Therefore, you should use one air-gapped computer to examine these threats under quarantine. With this computer, you can freely use a USB and download files from the internet, but do not transfer the files to your regular computer or re-use that USB.
- How to buy your own secured computer: Security expert Arjen Kamphuis recommends purchasing a pre-2009 IBM ThinkPad X60 or X61. These are the only modern-enough laptops with modern software systems, which enable replacing low level software. Another point to take into account is that you should not buy your computer online, as it may be intercepted during delivery. Kamphuis recommends buying it from a second-hand store for cash. He also points out that you should abolish all connectivity: Remove all Ethernet, modem, Wi-Fi, or Bluetooth capabilities. Personally, I know security experts who wouldn’t even trust a computer like that.
- ThinkPad X60.
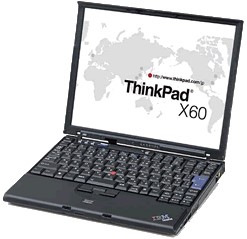 ThinkPad X60. Don’t buy it online
ThinkPad X60. Don’t buy it online - Educating your sources: By the time the original and valuable information reaches you, it may already be too late. Your source may have made every possible mistake, leaving behind a trail of evidence. But beyond the need to secure the information once it's in your hands, you should strive to teach your sources how to hide the information: store it securely and communicate safely via safe devices. Most people have no clue how to handle sensitive information or what they’re up against the moment they get in touch with you.
- Use a designated secure system for receiving documents: Replace Dropbox or Google Drive and use something less popular but more secure. For example, SecureDrop is a designated system allowing you to receive files from anonymous sources and to safely scan and check them. Edward Snowden described Dropbox as "hostile to privacy" and recommended SpiderOak instead. OnionShare is another free service that allows transferring files easily and anonymously.
- Don’t keep notes: Don’t keep notes on a laptop, in calendars, or in your contact lists on your cell phone or computer or in the cloud. Do not keep a record of your source’s name, initials, phone number, email, or user name in messengers. Just don’t.
- Visual tracking: On the way to sensitive meetings, avoid using public transportation and guide your source to do the same. You should also avoid meeting places such as modern malls, where video cameras are spread all over the place.
- Evading social media: Some people prefer to opt for radical anonymity. If, for some reason, you need to vanish from the face of the earth without leaving a full blown profile behind on every social media, totally delete your accounts. It's different from deactivating them, a state in which all your info is stored and can be re-activated.
- Make friends among hackers: This will help you avoid big mistakes, save time and headaches, and keep you up to date on the technological arms race.
- Payment method: Pay for everything in cash, consider using Bitcoins — buy them anonymously (use this Business Insider guide for that purpose) — and, if you have somebody willing to accept them at the other end of the transaction, use Dash. A prepaid credit card from an online store is also an option.
- Scribble wisely: If you jotted down information on a piece of paper, what they used to call a note in the Precambrian world, destroy it. And don't forget even that wrinkled one at the bottom of your pocket. Yes, right next to that gum.
3. How to become anonymous online
Beyond securing the communications with your source, and protecting possible breaches of the sensitive data you get hold of, other Edward Snowden privacy tips revolve around avoiding being tracked while browsing. Online habits can disclose or provide hints as to the story you’re working on, or worse, hint or disclose the identity of your source. Here are the golden Edward Snowden privacy tips for surfing the net safely:
- Private browsing mode: There are two basic ways to maintain anonymity while surfing the web. The first, most basic and popular, yet insufficient way is to browse the information in private mode, an option that most browsers allow. Your browsing history will not be saved, and basic tracking technologies such as HTTP cookies, used by advertisers, will be prevented from creating your detailed profile. But this is more of a nice to have privacy: It basically hides your browsing history from family members who can access your computer. Your IP address can still be monitored and information regarding all the sites you visited is still exposed to your ISP.
- Use alternative browsers: Browsers such as Dooble, Comodo Dragon, or SRWare Iron, which focus on user privacy, are limited in their capabilities. You can achieve a similar degree of privacy offered by these browsers simply by deleting cookies — bits of code which have been downloaded to your system by websites you visit, that monitor your activity and sometimes even follow which content you consume. Another way to remain anonymous is by neutralizing your browser’s location settings, and installing various features aimed at achieving anonymity. To check whether you disabled all cookies effectively, you can use the app CCleaner, which also handles Flash cookies, but none of these browsers are fully encrypted. The only standard browser that ensures total privacy is the Tor browser. Tor is ugly and slow, but it will protect you and your sources. The next section will give a more detailed account of it.
- TOR: This “notorious” browser, which was developed by the US Navy, allows you to operate in a hidden network, carry out private communications, and set up websites anonymously. Tor's browser, which can be downloaded at Torproject.org, makes it very difficult to monitor your activities on the internet, or let governments or your ISP pinpoint your location. The only drawback is that it's slow at times, and a bit cumbersome — but that's only because Tor routes you through three encrypted random relays around the world, before landing you at your destination site. You should also bear in mind that your neighbors may be shady characters.
Another option related to Tor is to download Whonix, a secure operating system that is focused on privacy. It works as an access gate to Tor, and only allows connections with Tor sites and users. But the most popular Tor OS is Tails (The Amnesiac Incognito Live System). Tails can be booted from a USB stick or DVD, and it anonymizes all information. Edward Snowden is considered a fan of this software. Qubes is another OS that supports Whonix and is recommended by Snowden. - Alternative search engines: Google, the most popular search engine, saves your search history in order to optimize the results. To stop this personalization you should click on: Search Tools > All Results > Verbatim. Or you sign into your Google account on www.google.com/history, find a list of your previous searches, and select the items you want to remove by clicking the ‘Remove Items’ button.
 DuckDuckGo. A search engine that doesn’t store your info
DuckDuckGo. A search engine that doesn’t store your info
But to avoid being monitored entirely, you should use a search engine such as DuckDuckGo. If you find it difficult to give up Google, download Google Search URL Fixup to at least keep away URL Trackers.
- Direct treatment of "short-term" computer memory: Another way to neutralize options for monitoring your surfing is by deleting the DNS (domain name system) cache. Deletion is done using simple commands in the operating system. Rebooting the router — which sometimes has a DNS cache — or rebooting the computer can also reboot both their respective DNS cache, if the router has one.
- Try to avoid HTML Web Storage: Web Storage is built into HTML5, and unlike cookies, the stored information is impossible to monitor or selectively remove. Web storage is enabled by default, so if you're using Internet Explorer or Firefox, simply turn it off. You can also use the add-on for Chrome to remove the stored information automatically.
- Use a VPN: As I mentioned already, your ISP can monitor the sites you surf, and anyone who wants to eavesdrop on you can also intercept your communications. To protect all incoming and outgoing communications, use a VPN (for a complete explanation, click here). VPN encrypts all your communications so that even the ISP or the secret services, or just hackers hovering around your favorite coffee shop’s Wi-Fi, won’t be able to know who you sent an email to, which service you used, etc. The use of a VPN is very common among people who, for example, wish to see the complete Netflix movies catalog outside of the United States, but not every VPN is suitable for journalists. A VPN for journalists won’t necessarily be the fastest one or have the best support, but it has to be trusted not to keep VPN logs — that is, it cannot determine who you are, what sites you’ve visited and so on. A safe VPN is bound to be provided by a company who’s not located at one of the "14 Eyes" countries, where intelligence networks are allowed to collect and share information with one another; firstly and foremost, in the USA. So VPN companies located in the territory of the former Soviet Union countries have an advantage. Their courts do not easily hand out orders to retrieve information collected by local companies, be it regarding their citizens or foreign nationals. Here you'll find a list of 5 VPN services that stand out regarding privacy and all are located outside the "14 Eyes" countries. By the way, even if governments are on the hunt for traffic that is sheltered by a VPN, you can still use stealth VPNs like TorGuard. Tor and VPNs give you the perfect protection when someone is trying to retrieve your browsing history in order to profile you.
- Repair DNS leaks: Using a VPN does not protect you completely, because DNS traffic may hint at your identity. DNSLeakTest.com will allow you to detect such leakage. If the test shows that DNS is of your VPN, you can relax, but if it shows that the DNS is of your ISP, you are not anonymized. In this case you, check out what you can do here.
- Virtual Machines: This nifty little trick is actually a second (virtual) computer, which operates as an app in your operating system. You can download files or open links in a similar way to the isolated computer I recommended earlier, so that your computer is less exposed to malware or spyware of any kind. Virtualization software, like VirtualBox, should be opened using a secure operating system. File downloading is done with the virtual machine internet connection shut down; after using the file, you'll need to delete it — and depending on your adversary, perhaps delete it along with the machine.
 HMA proxy server. I’ll hide yours, if you’ll hide mine
HMA proxy server. I’ll hide yours, if you’ll hide mine - Proxy server: As in the case of virtual machines, here too the activity moves to another “area” and allows you to keep safe from spying and other attacks. Actually, the proxy servers substitute your IP address with theirs, which can mislead people into thinking you’re in a different country, for instance. HideMyAss.com/proxy, Psiphon (open source), and JonDo all provide a similar service. Some experts say that these should be used with a VPN and/or Tor for higher levels of security. But then, some experts I’ve talked to claim that if you bother using Tor, you’re as secured as one can be anyway.
- Three more types of extensions that can increase your level of security: To verify that the internet protocol where you operate is https secure, you can install an extension called HTTPS Everywhere, made by the Electronic Frontier Foundation's (EFF), one of the organizations that funds the Tor Project. This extension is recommended by many cyber experts; it will ensure that websites you visit use the secure protocol, which is definitely not an insurance policy against anything, but better than the unencrypted protocol. The second type of extension controls the data that JavaScript reveals to websites (in order to improve your browsing experience). Two popular options here are ScriptSafe and NoScript. Another extension is the Ghostery browser. This extension will reveal who is following you among 2,000 companies, and will allow you to block any that are unwanted. It’s sweet, but you probably won't be blocking the NSA this way. Privacy badger, a project by the EFF, also works similarly.
4. Securing your email
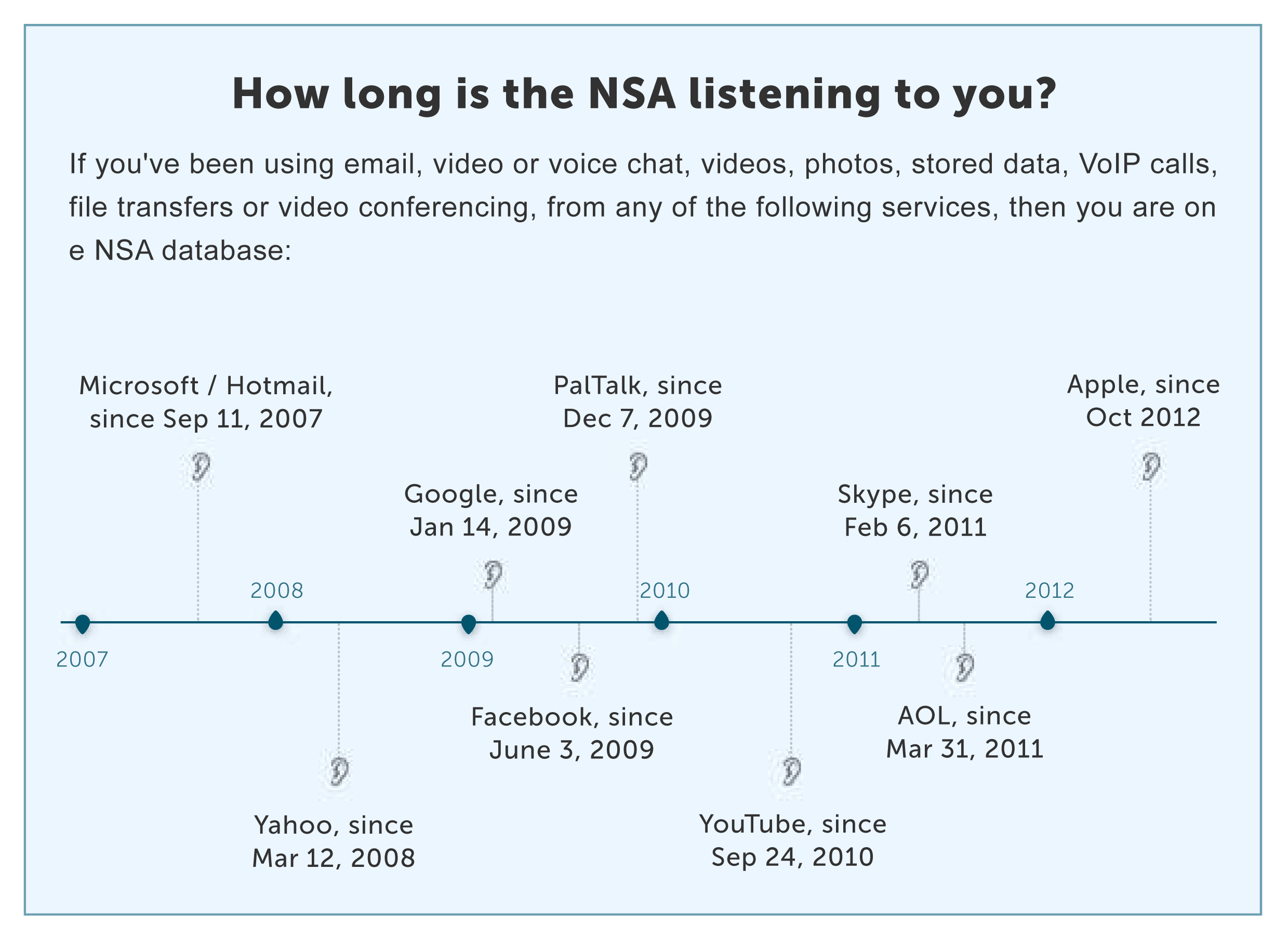
What steps can you take to secure your email? Ensuring the privacy of emails is a particularly challenging issue, as companies like Google and Microsoft are likely to disclose your emails to government agencies when legally obligated. So, what are the best Edward Snowden privacy tips for protecting your emails?
- Safe extensions: The simplest option, assuming you use common web mail services such as Yahoo and Google, is to install the browser plugin Mailvelope, and make sure that the person on the receiving end does too. This extension simply encrypts (and decrypts) e-mail. In 2018 Gmail introduced a functionality called confidential mode that facilitates the sending and receiving of secured emails.
- Secure email providers: Hushmail is an example of an email service that provides better security than the more common networks you use, but it may be forced to hand over emails to the US government under a court order, and it does log IP addresses. Another email service with similar features and security levels is Kolab Now, which prides itself among other things with storing data exclusively in Switzerland.
- Disposable Email Addresses (DEA's): This is an email created ad hoc for a specific purpose, which is completely anonymous and is deleted immediately after use. This solution, commonly used when signing up for various services in order to avoid spam, is also a great solution for maintaining anonymity. However I wouldn’t advise journalists to communicate with their sources over it, because security is not its strongest trait. There are dozens of such temporary emails, but the British Guardian, for example, recommended Guerrilla Mail and Mailinator. Using Guerrilla Mail in the Tor Browser ensures that not even they can connect your IP with your email address. Likewise, if you use email encryption software, such as GnuPG, on Tor, you're all set and secure.
- Encrypting your mail: Wired got this recommendation from Micah Lee, a privacy-focused technologist who worked with the EFF and First Look Media (here is an interview Lee held with Edward Snowden): Encrypting messages with webmail can be tough. It often requires the user to copy and paste messages into text windows and then use PGP to scramble and unscramble them (PGP — Pretty Good Privacy — is an encryption program that provides cryptographic privacy and authentication for data communication). That is why Lee suggests a different email setup, using a privacy-focused email host like Riseup.net, the Mozilla email app Thunderbird, the encryption plugin Enigmail, and another plugin called TorBirdy that routes its messages through Tor. As Reid pointed out in his interview with Kamphuis on journalism.co.uk, Greenwald almost lost the NSA story because he initially ignored Snowden's instructions on email encryption. In other words, if you want a story that will go down in history it makes sense to be secure. Kamphuis agrees that PGP can be trusted. As he and Reid explain, with PGP encryption, you have a public key, like your public phone number, and a private key. The public key can go on Twitter biographies, business cards, websites and wherever else your work is publicized, but the private key must be stored securely, as with any other sensitive information. Then, when a source wants to send information, they will use your public key to encrypt their email, that only your private key can unlock. Kamphuis recommended the GNU Privacy Guard, an open-source version of PGP, that is simple to set up and has an active support community. For encrypting files, data and hard drives, he suggested consulting his free ebook, “Information Security for Journalists,” published with Silkie Carlo and released through the CIJ, which fully explains the process. If you do choose to encrypt the message itself regardless of your mail provider’s identity, using zip with a password is a good idea, and 7ZIP is a recommended tool for accomplishing that.
- Back to basics: Yes, I know that this is back to email security 101 — but please try to avoid phishing. Watch the “from” field in your email for little misspellings; a third party can pose as somebody you know. And one last word on email encryption: One of the real problems to bear in mind is that even after encrypting them, not everything is encrypted. The email addresses of the sender and recipient, the subject line, and the time and date when the email was sent, are all out in the open. Attachments and the message itself are the only data that is encrypted.
5. Final words
These are perhaps the most radical Edward Snowden style privacy tips I ran through, when preparing this ebook.
As Micah Lee put it when interviewed on privacy on WIRED: “If your computer gets hacked, the game is over. Creating a virtual sandbox around your online communications is a good way to keep the rest of your system protected. Tor is awesome and can make you anonymous. But if your endpoint gets compromised, your anonymity is compromised too. If you really need to be anonymous, you also need to be really secure.”
And Journalist Tony Locy puts it in even harsher words in an article published in an ebook about the future of cross-border investigative journalism for the Nieman Foundation at Harvard: “Some journalists, computer scientists, and privacy advocates are so alarmed that they recommend reporters go old school... and rely on in-person interviews and snail mail.”
I hope I have helped people in the trade, and others, gather some information that will clarify what needs and can be done to ensure your and your source’s security in these uncertain times.
6. List of Sources for This Book
- Security for journalists: How to keep your sources and your information safe
https://www.ire.org/security-for-journalists-how-to-keep-your-sources-and-your-information-safe/ - Securing data, sources and yourself
https://www.ire.org/securing-data-sources-and-yourself/ - Surveillance and Security: Are reporters and news organizations doing enough to protect sources?
http://niemanreports.org/articles/surveillance-and-security/ - Muckraking Goes Global: The Future of Cross-Border Investigative Journalism
http://niemanreports.org/books/muckraking-goes-global-the-future-of-cross-border-investigative-journalism/ - The Ultimate Guide for Online Privacy
https://www.vpnmentor.com/blog/ultimate-guide-online-privacy/ - What Is a DNS Cache?
https://www.lifewire.com/what-is-a-dns-cache-817514 - How to Anonymize Everything You Do Online
https://www.wired.com/2014/06/be-anonymous-online/ - 19 ways to stay anonymous and protect your online privacy
https://www.extremetech.com/internet/180485-the-ultimate-guide-to-staying-anonymous-and-protecting-your-privacy-online - Edward Snowden explains how to reclaim your privacy
https://www.extremetech.com/internet/180485-the-ultimate-guide-to-staying-anonymous-and-protecting-your-privacy-online - Information security for journalists: staying secure online
https://www.journalism.co.uk/news/information-security-for-journalists-/s2/a562525/ - NSA targets the privacy-conscious
http://files.gendo.nl/presentaties/CIJ_Infosec&countersurv_4-07-2014.pdf - Obama DOJ formally accuses journalist in leak case of committing crimes
https://www.theguardian.com/commentisfree/2013/may/20/obama-doj-james-rosen-criminality - Your WhatsApp secrets are safe now. But Big Brother is still watching you…
https://www.theguardian.com/commentisfree/2016/apr/10/whatsapp-encryption-billion-users-data-security - Obama Pursuing Leakers Sends Warning to Whistle-Blowers
http://www.bloomberg.com/news/2012-10-18/obama-pursuing-leakers-sends-warning-to-whistle-blowers.html - 6 encryption mistakes that lead to data breaches
https://www.crypteron.com/blog/the-real-problem-with-encryption/?gclid=Cj0KEQiA9P7FBRCtoO33_LGUtPQBEiQAU_tBgDgBzD9wIXv94vwhj3qwhc6ewEYYeyjIeiXtMQiwF3caAsFn8P8HAQ

You can help others! Click to share on Facebook or Tweet!
Great post! Your insights on website were spot-o n. If you’re looking for more detailed information,



Please, comment on how to improve this article. Your feedback matters!