Report: Cloud Storage Data Breach Exposes Users' Private Information
Led by cybersecurity analysts Noam Rotem and Ran Locar, vpnMentor's research team recently found a serious breach in an open Amazon S3 bucket owned by secure cloud storage provider Data Deposit Box.
The leak exposed detailed information about 270,000 private files uploaded by customers through the company's secure cloud storage service. The database also revealed personally identifiable information (PII) of customers, which could have serious consequences for those affected.
Data Deposit Box Company Profile
Data Deposit Box is a public company that offers secure cloud backup storage services to individuals and small businesses. The business is based in Canada but has over 350,000 users spread across 84 countries.
Data Deposit Box allows customers to continuously backup an unlimited number of devices to their accounts through the company's app and web portal.
Timeline of Discovery and Owner Reaction
Sometimes the extent of a data breach and the owner of the data are obvious, and the issue quickly resolved. But rare are these times. Most often, we need days of investigation before we understand what's at stake or who's leaking the data.
Understanding a breach and its potential impact takes careful attention and time. We work hard to publish accurate and trustworthy reports, ensuring everybody who reads them understands their seriousness.
Some affected parties deny the facts, disregarding our research or playing down its impact. So, we need to be thorough and make sure everything we find is correct and true.
In this case, we identified Data Deposit Box as the owner of the database. Before publishing this report, we reached out to the company to share our findings and provide guidance on how to resolve the issue.
Once we finally received a reply, Data Deposit Box responded quickly to secure the data. The company assured us that they are currently working with their customers to ensure their data is safe going forward.
- Date discovered: December 25, 2019
- Date owners contacted: December 30, 2019
- Date database closed: January 6, 2020
Example of Entries in the Database
More than 270,000 files were exposed in the data breach, with leaked files dating back from 2016 to the present day. We were able to view sensitive user account information, as well as some of the stored contents.
Examples of leaked private user data include:
- Admin login credentials, including usernames and unencrypted passwords
- IP addresses
- Email addresses
- GUIDs (globally unique identifiers for resources)
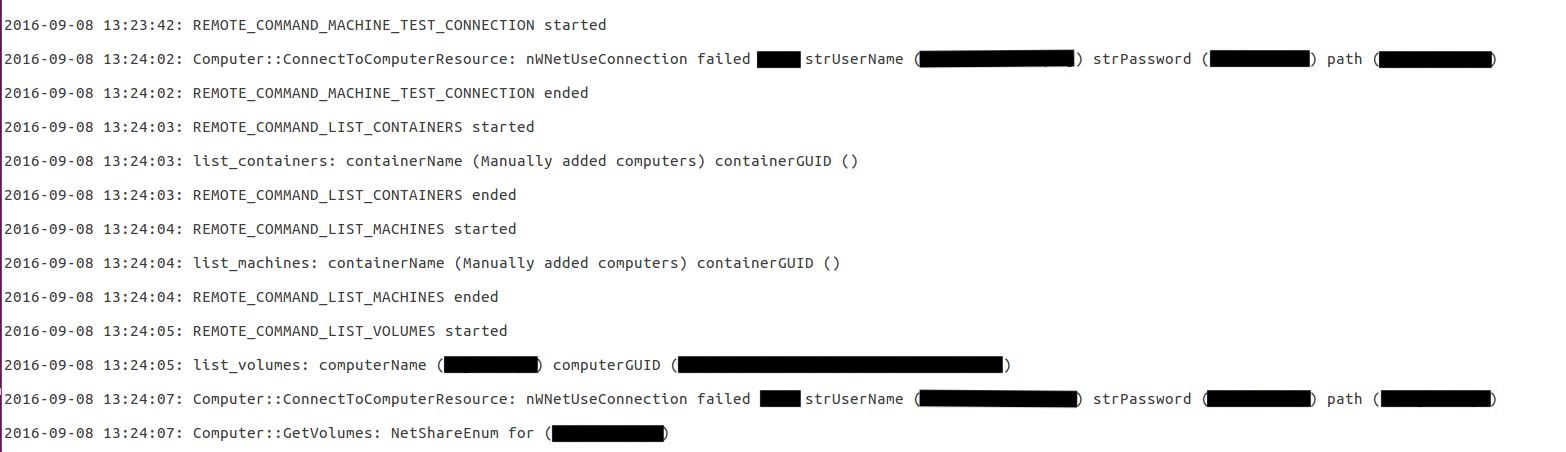
Shockingly, we were able to view users' login credentials in plain text. In the image above, the censored text contained unencrypted administrator usernames, passwords, and users' local computer name and GUID.
You can see an example of an email address exposed in the breach in the code here:

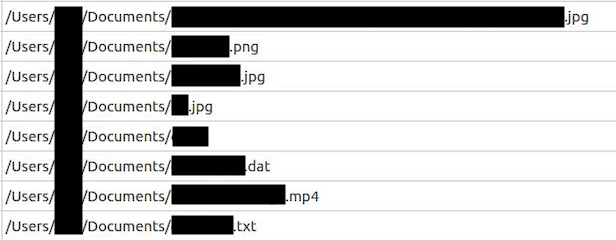
Through the leaked database, we were also able to view some information about users' stored files. This included each file name, type, size, the date last modified, and the file path on the user's local disk. An example of this can be found below.
Data Breach Impact
The data breach creates significant risks for affected Data Deposit Box users, and it will also affect the company itself.
Impact on Data Deposit Box Users
The unencrypted usernames and passwords exposed in this breach may allow malicious parties to access Data Deposit Box's customers' accounts. We didn't log into any users' accounts for ethical reasons, but we could've easily done so. The bad news is that if we're able to do this, hackers could do it too.
According to its website, Data Deposit Box offers two-factor authentication, which may protect some accounts from hackers. However, effective hackers may be able to get around this by gaining access to email accounts or even by hijacking phone numbers.
If a hacker successfully gains entry to a user's account, they'll be able to access all files stored by that user. Both the mobile app and the web portal provide users–and therefore hackers–with remote access to all stored files.
Even if they can't gain entry to a user's account, malicious actors can still learn sensitive information from leaked file names. When hackers gain intimate knowledge about users' local files, this puts the affected businesses and individuals at serious risk. Hackers can use this information to create highly effective targeted cyber attacks.
Another concern is that malicious parties could use leaked email addresses for phishing attacks and other scams in order to gather more sensitive information.
They can use this knowledge to gain trust and trick individuals into providing more information or access to private accounts. In this way, they can create highly effective personalized scams, possibly even leading to identity theft.
Impact on Data Deposit Box
When customers sign up for Data Deposit Box's secure cloud storage service, the company promises to protect your files and accounts with robust encryption. The fact that we were able to view unencrypted passwords, file names, and other sensitive data means best practices weren't being followed.
It may be difficult for users to trust the company with their sensitive data in the future as a consequence of this data breach.
Impact on Competitors in the Cloud Storage Industry
Data Deposit Box isn't the only cloud storage provider impacted by this. Whenever a serious data breach occurs, it can have consequences for the entire industry.
Competitors in the cloud storage services industry may find it more challenging to convince customers to trust them. These companies may need to do more to prove to customers that their service is truly secure.
Advice from the Experts
Data Deposit Box could have easily avoided this leak if the company had taken some basic security measures to protect the Amazon S3 bucket. These include, but are not limited to:
- Secure your servers.
- Implement appropriate access rules.
- Never leave a system that doesn't require authentication open to the internet.
Any company can replicate the same steps, no matter its size. To learn more about how to protect your business, check out our in-depth guide on securing your website and online database from hackers.
For Affected Customers
If you're a customer of Data Deposit Box and you're concerned that you or your company's data may have been leaked through this data breach, we strongly recommend that you take steps to improve your online security now before a serious problem occurs.
Take a look at our complete guide to online privacy to learn steps you can take to boost your security online and protect yourself from cyber-attacks.
Since hackers may try to target you using information exposed in the data breach, it's also a good idea to use a VPN. A quality VPN encrypts your traffic, masks your IP address, and protects you from hackers and other threats to your privacy online.
How and Why We Discovered the Breach
The vpnMentor research team discovered this breach in Data Deposit Box's database as part of our large-scale web mapping project.
Our research team scans ports to find known IP blocks. The team then searches for vulnerabilities in the system that would indicate an open database.
Our team successfully gained access to Data Deposit Box's Amazon S3 bucket as it was entirely devoid of any security or encryption. Utilizing a web browser, the team was able to reach all the files stored on the database.
After finding a data breach, we do our best to link the database back to the owner. We then contact the owner to inform them of the vulnerability and suggest ways that the owner can improve the security of their systems.
As ethical hackers and researchers, we never sell, store, or expose the information we encounter. Our goal is to improve the overall safety and security of the internet for everyone.
About Us and Previous Reports

We recently found a large data breach that exposed the browsing history of mobile internet users in South Africa. We also discovered over 1TB of data leaked by Chinese online retailer LightInTheBox.




Please, comment on how to improve this article. Your feedback matters!