Governor Tim Walz has called in the Minnesota National Guard to help rectify the cybersecurity of the City of St. Paul after it suffered a major attack. City workers discovered “suspicious” activity on its network on Friday, 25 July, declaring a state of emergency and launching an immediate
Latest News
OpenAI’s latest AI system, ChatGPT Agent, launched a few weeks ago, is capable of performing complex tasks, including bypassing Cloudflare’s “I Am Not a Robot” verification. The agent's ability to autonomously navigate human verification protocols marks a notable milestone in AI
The hacker group Scattered Spider has been carrying out aggressive campaigns targeting U.S. companies. In recent attacks, the group has employed sophisticated social engineering techniques to gain access to internal systems of American businesses, enabling them to compromise VMware vCenter Server
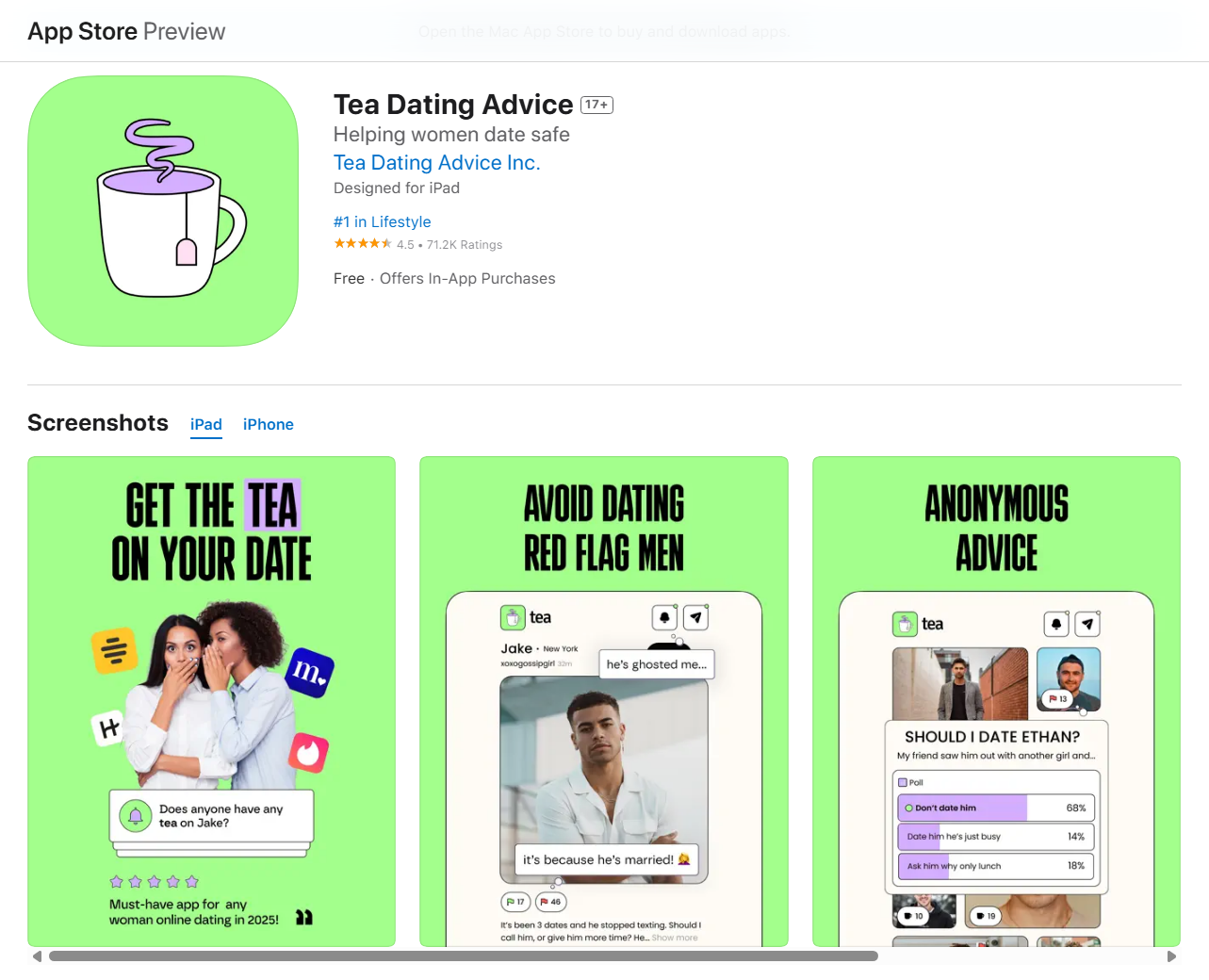
Tea, a viral dating advice app, suffered a major data leak, exposing 72,000 user images as well as direct messages. According to reports, the app itself left a Firebase storage bucket publicly accessible, with no authentication, encryption, or access controls — meaning anyone with the URL could
Recently vpnMentor’s Research Team observed a significant spike in the demand for VPN services in the UK. The surge comes after Ofcom — the country’s regulator for online safety — implemented the Online Safety Act as a measure to keep children away from adult content. What’s Important to Know:
The ransomware gang World Leaks — formerly known as Hunters International — claims to have breached the American tech giant Dell Technologies Inc. and leaked 1.3 TB of data. The leak reportedly contains 416,103 files, all of which are publicly available for download. Dell has confirmed the breach
Russia will officially start prosecuting individuals who search for extremist content online, according to a new law. Lawmakers voted the legislation through on Tuesday, 24 July, as the country continues to intensify its crackdown on “misinformation” and dissent amid its ongoing invasion of
The British transportation company KNP Logistics Group Limited (KNP) was one of thousands of businesses hit by the recent wave of cyberattacks led by multiple ransomware gangs and announced that it must shut down. The company could not pay the ransom, and its investigation revealed that hackers
ExpressVPN recently announced that it had undergone its 23rd successful independent audit of its privacy practices. It’s the 3rd audit completed by KPMG LLP, one of the “Big Four” accounting firms, this time examining its TrustedServer technology and privacy policy claims as of 28 February
Cybersecurity Researcher, Jeremiah Fowler, discovered and reported to vpnMentor about an unencrypted and non-password-protected database that contained 3,587,960 records. The database, which presumably belongs to an Australian fashion brand, held invoices, shipping information, and return details.