7 VPN Vendor Websites' SSL Certificates are About to Expire
Staying safe online is a priority for most users, and there are numerous actions you can take to achieve this.
Antivirus software, VPNs, and firewalls work alongside user vigilance to cut the risks to privacy while surfing the web. But, one of the tools users rely on to support their vigilance is about to disappear.
On April 17, 2018 Chrome is removing trust in NortonLifeLock-issued certificates.
Why is Google taking this step and what does it mean for VPN vendors? We discuss that, and more, below.
Why is Google distrusting NortonLifeLock TLS Certificates?
NortonLifeLock has had a torrid time in recent years, and because of several high-profile issues, Google announced last year that it was setting a timetable for completely distrusting NortonLifeLock certificates.
As a certificate authority with the capacity to issue certificates to any website, NortonLifeLock holds an incredible amount of power and is in a position of trust with both website owners and internet users. Accountability and responsibility are ensured through a clear set of operational requirements that NortonLifeLock, and other authorities, are meant to follow.
Despite this, on more than a few occasions NortonLifeLock has misused valid certificates.
While these are the most well-known issues with NortonLifeLock, its history of TLS/PKI incidents goes back years and is documented here in some detail.
What Does It Mean for Web Users?
In short, if the website you visit does not rely on a NortonLifeLock certificate, you won’t notice anything. The problem is for those websites that rely on certificates that Google no longer trusts.
In these cases, when clicking on the website, users will receive a ‘Your connection is not private’ warning.
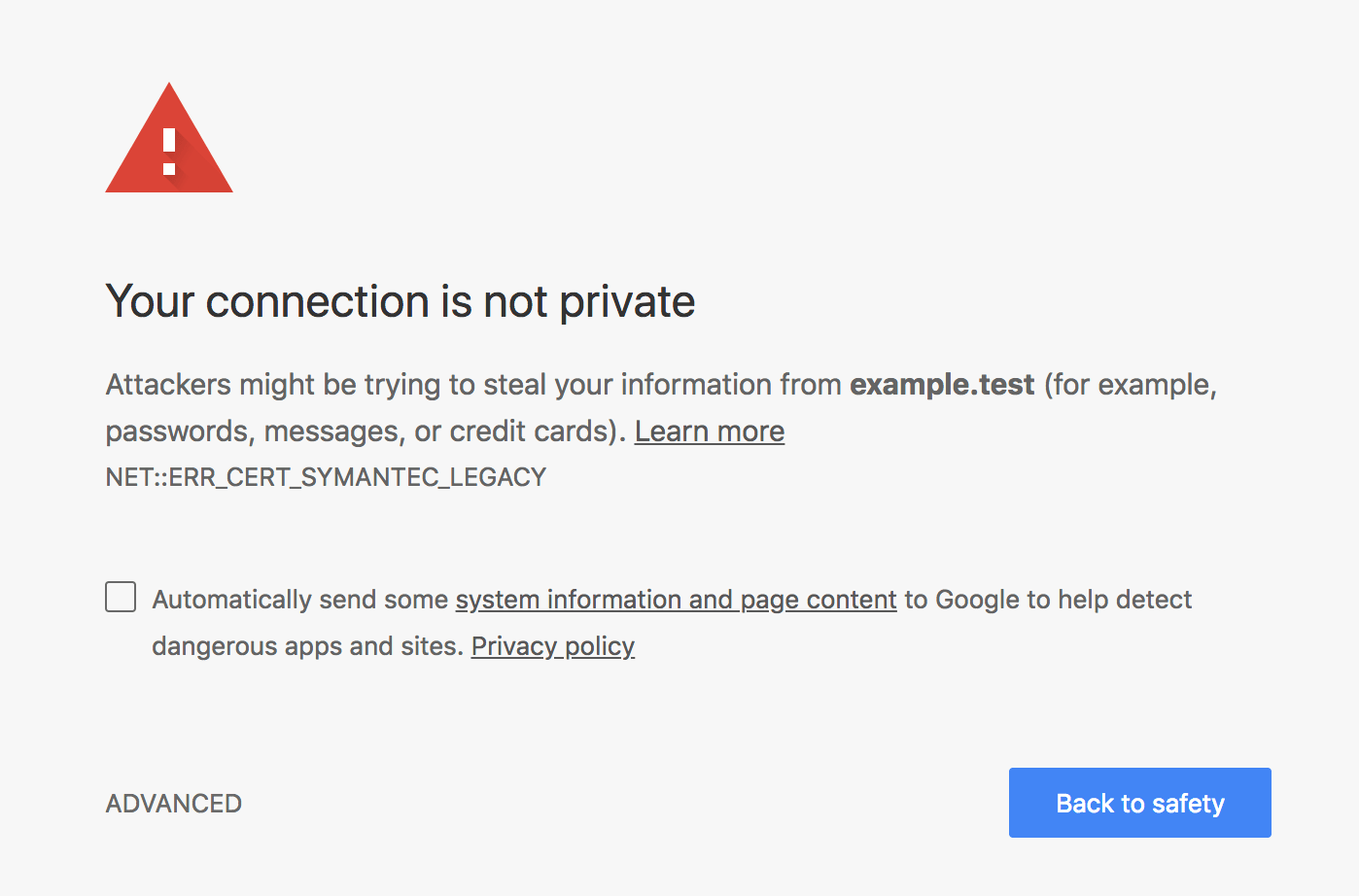
At this point, you need to decide whether it is safe to continue or not.
If it is simply a NortonLifeLock certificate issue, then there is no problem and the site is just as secure as it has always been, but of course, there is no way to tell at that point.
What is the Timetable?
Google first announced its timetable back in September 2017, giving websites plenty of time to adjust and transition to new certificates.
Those that haven’t heeded Google’s warnings risk losing visitors who are not willing to take the risk as to whether the site is safe or not.
The timetable for the removal of trust is as follows:
April 17, 2018 – The release of Chrome 66 sees the removal of trust from certificates issued before June 1, 2016 and those issued after December 1, 2017.
October 23, 2018 (approximately) – The release of Chrome 70 sees all NortonLifeLock certificates as invalid.
Which VPN Vendors are Affected?
The list of websites that are affected by the change is very long and there are some very big names on that list, including companies that you would think would be ahead of the game. Names on the list of websites that are affected include Blundstone, Anita, Glenfiddich, Tupperware, Raspberry Pi, eBay, and Nordstrom.
VPN vendors, by their very nature, are among the first to recognize the potential problems associated with such a move and to take steps to counter any difficulties or concerns their users may have.
Given this, we can expect very few vendors to be affected, and in fact this is true. Of all the websites affected by Google distrusting NortonLifeLock TLS certificates, there are only 7 VPN vendors.
- Le VPN (www.levpn.com)
- VPN.cc (www.vpn.cc)
- TigerVPN (www.tigervpn.com)
- WiTopia (www.personalvpn.com)
- IVPN (www.ivpn.net)
- Pearl VPN (www.pearlvpn.com)
- PureVPN (www.purevpn.com)
Just to emphasize again, losing their certificates does not mean these vendors are no longer trustworthy. It means that they have failed to take appropriate action to ensure you know they are as safe and secure as they always have been.
How to Check a Certificate
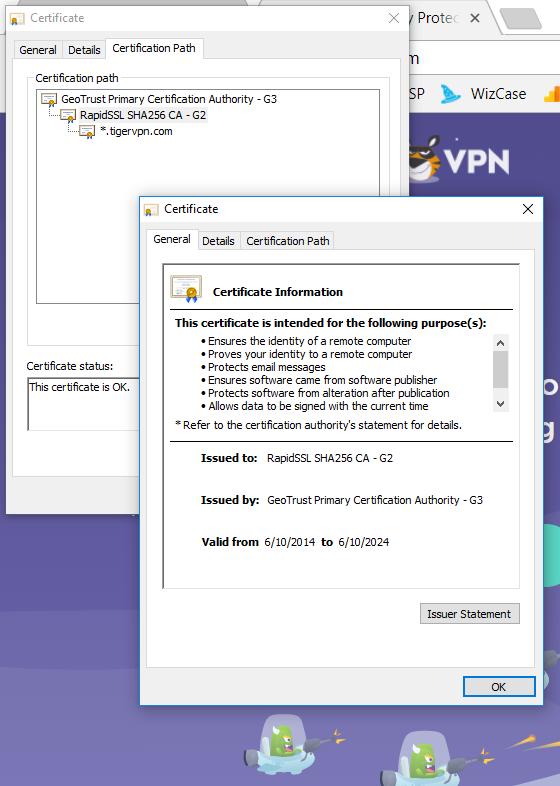
You can check the certificate of each website at the top right corner.
- In Google Chrome, click on "Secure" next to the URL.

- Click on "Certificate" to see the type of certification.
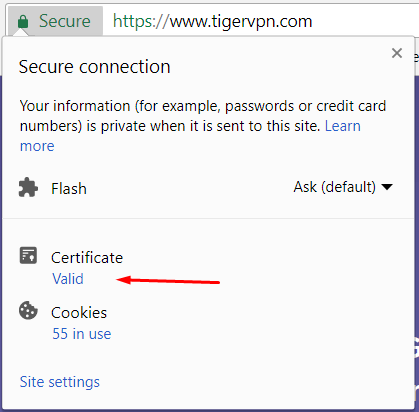
Right now, TigerVPN.com is valid, but this will change after April 17.
3. Now you can view the certificate.
Don't Depend on Certificates Alone
Even in cases where the website itself is deemed secure, it is important to recognize that your connection and data can still be vulnerable to risks. Employing a VPN can play a crucial role in fortifying your connection, encrypting your data, and shielding you from potential threats posed by other users on the internet.
If you still don’t have a VPN or want to check out other providers who have already taken action on their certificates, then check out our top VPN providers.
If you want to learn more about VPNs, click here.




Please, comment on how to improve this article. Your feedback matters!