When using a VPN, you shouldn’t have to rely on a browser extension with a complex setup just to get the service working. However, that was exactly what happened when I set out to try Hide My IP.
I thoroughly tested the US-based VPN to see how effective it is for unblocking streaming sites, fast downloads, security, torrenting, and providing you with transparent policies. I signed up for the premium version to see everything it has to offer.
When it works, Hide My IP is very effective in some areas like speed and streaming.
However, it has some serious failings — particularly when it comes to its virtually unusable apps and unreliable connections. Add a concerning logging policy, and it quickly becomes clear that Hide My IP just can’t compete with other premium VPN services.
Try Hide My IP Today
Short on Time? Here Are My Key Findings
- Unblocks major streaming platforms. The browser extension works with Netflix, Disney+, Hulu, and more, but most of the apps are essentially unusable for streaming. Jump to streaming results here.
- Speeds are inconsistent. I enjoyed a fast connection on the browser extension and Android app, but most of the apps either didn’t work or slowed speeds to a crawl at best. You can see my findings here.
- No-logs policy isn’t very clear. If you’re concerned about how your online data is used, there are elements of Hide My IPs privacy policy that are concerning.
- Basic security measures. The VPN has strong encryption, and the browser extension worked well but, it’s likely to leak your IP, DNS, and more using the apps.
- Torrenting is allowed. But the unreliable apps make this impossible. The vague privacy policy also raises doubts over anonymous use, and downloading copyrighted material is against the terms of use.
- Ping may be too high for serious gamers. Speeds are good, but you might find that you lose the competitive edge with ping rates particularly high.
- 30-day money-back guarantee. You’ll be able to try Hide My IP risk-free and request a refund if you’re not 100% happy.
Hide My IP VPN Features — 2025 Update
8.4
|
💸
Price
|
2.91 USD/month
|
|
📆
Money Back Guarantee
|
30 Days |
|
📝
Does VPN keep logs?
|
No |
|
🖥
Number of servers
|
145+ |
|
💻
Number of devices per license
|
7 |
|
🛡
Kill switch
|
Yes |
|
🗺
Based in country
|
United States |
|
📥
Supports torrenting
|
Yes |
Streaming — Clunky Setup, But Works
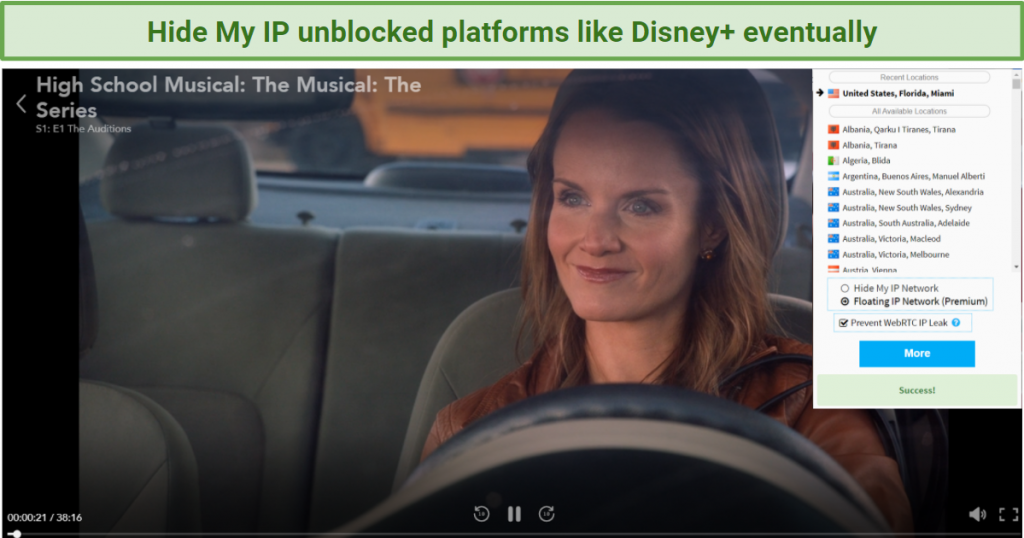
I only had success unblocking Netflix US, Disney+, Hulu, and other major platforms using the browser extension, and no luck with Amazon Prime Video and HBO Max. For reliable VPNs that let you stream from anywhere, have a look at these providers.
At first it didn’t unblock any streaming platforms with the Windows app. I played around with the settings, enabling “require US-based IP," “hide my IP with all internet applications," and “DNS protection." Every US server I connected to did nothing to unblock Netflix US. I had the same issue with UK servers for BBC iPlayer.
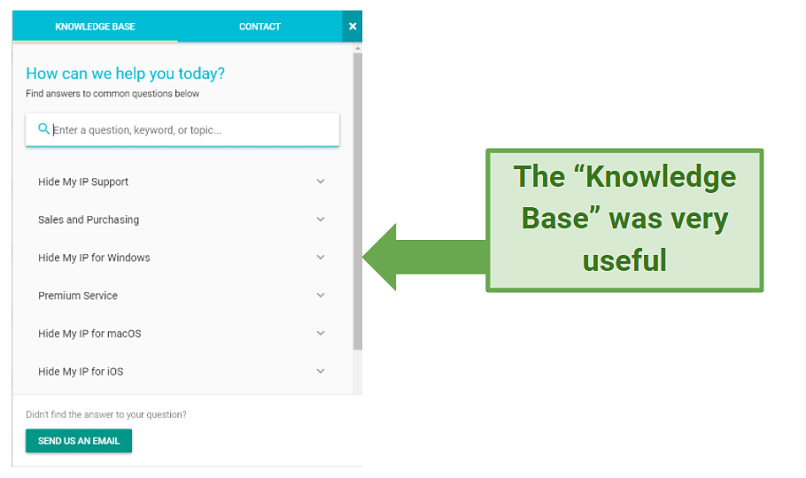
I contacted support but, in the interim, I discovered from the Knowledge Base that you need to use the floating IP network option in the browser extension when streaming. It’s worth noting that this feature is only available in the premium version. If you’re using the free 7-day trial version, you’re probably out of luck for streaming most major platforms.
This is unusual for a VPN and not particularly user-friendly, as most users would expect the Windows app to be able to bypass streaming platform geoblocks. Once I figured this out, however, I was able to unblock most platforms with the browser extension.
The same is not true of the Android app, though — this unblocked the same streaming platforms below just by using the app, so this problem is specific to desktop streaming.
Unblocked: Netflix US, Disney+, Hulu, ESPN+, HBO Now, BBC iPlayer, Pandora, DAZN, and 10 Play
Once I’d worked out the unusual quirk with the browser extension, I had better results. I tested many US servers, including some in New York, Miami, Phoenix, and Texas. Some of these connections did fail to begin with, so I either had to reconnect or try an alternative server. The Miami server was the most reliable for me.
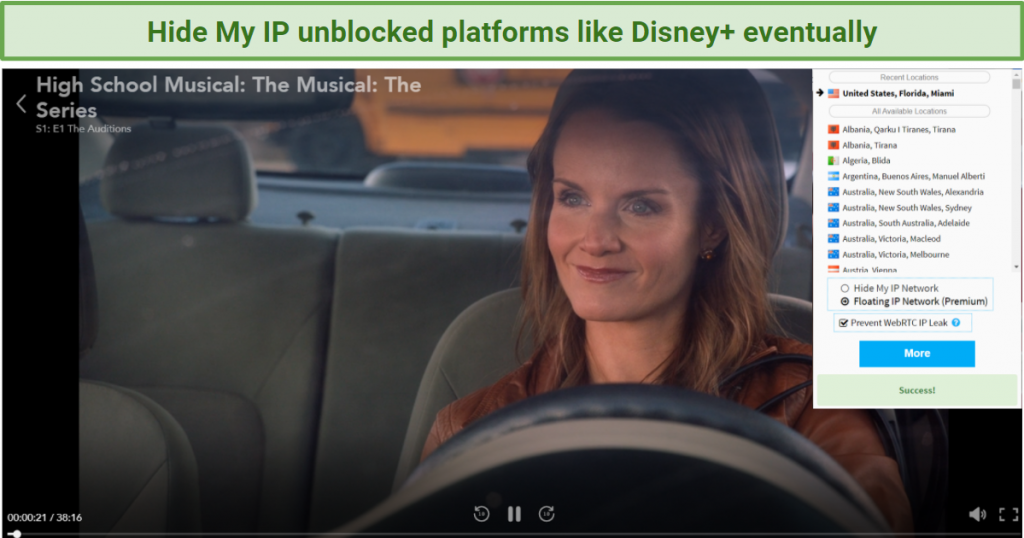 I had trouble unblocking US platforms initially but got results with the browser extension
I had trouble unblocking US platforms initially but got results with the browser extension
Netflix US was unblocked after a few tries. Once I found a reliable server, I accessed Disney+, Hulu, and other US-based platforms too. It took some time — around a minute — for the connection to ‘settle’ and the speed to reach a level for buffer-free viewing. On all the US servers I tried, I eventually got an average speed of around 28 Mbps — more than the 25 Mbps needed for UHD.
I was able to stream music on Pandora, watch Australian TV on 10 Play, and watch live sports on ESPN+ and DAZN once I’d established a decent connection. If you’re trying to access live sports quickly, I wouldn’t recommend Hide My IP for this as you could end up missing some of the action.
For that, I’d suggest you try these top VPNs for sports platforms like Sky Sports and beIN. If you’re not fussed about ease and speed of access to streaming sites, it will do the job for you.
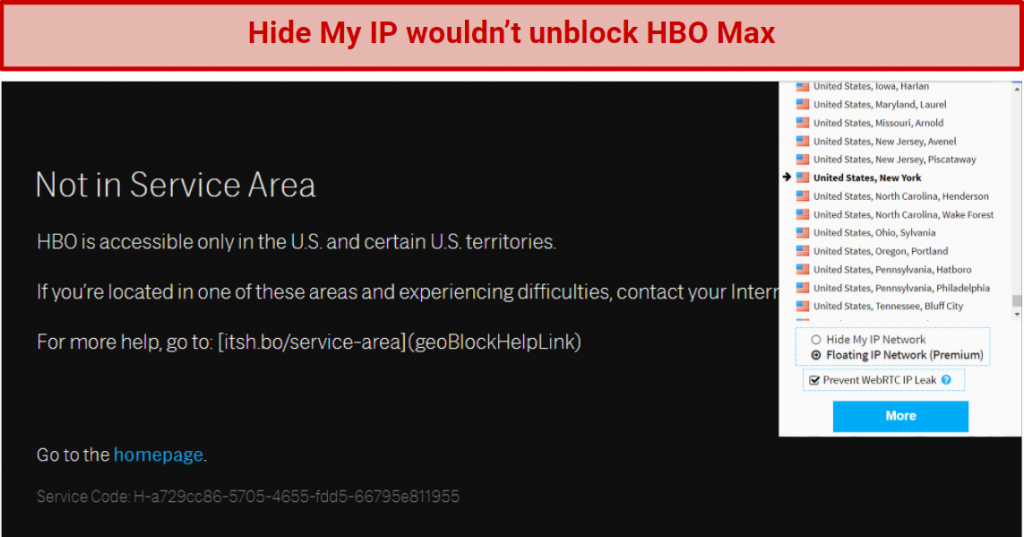
Blocked By: HBO Max and Amazon Prime Video.
Unfortunately, HBO Max was blocked on the extension, Windows desktop app, and Android app, regardless of which server I tried. I was greeted with an error message once I tried to log in beyond the (usually blocked) landing page — a sign that Hide My IP was doing something to get me that far, but not enough.
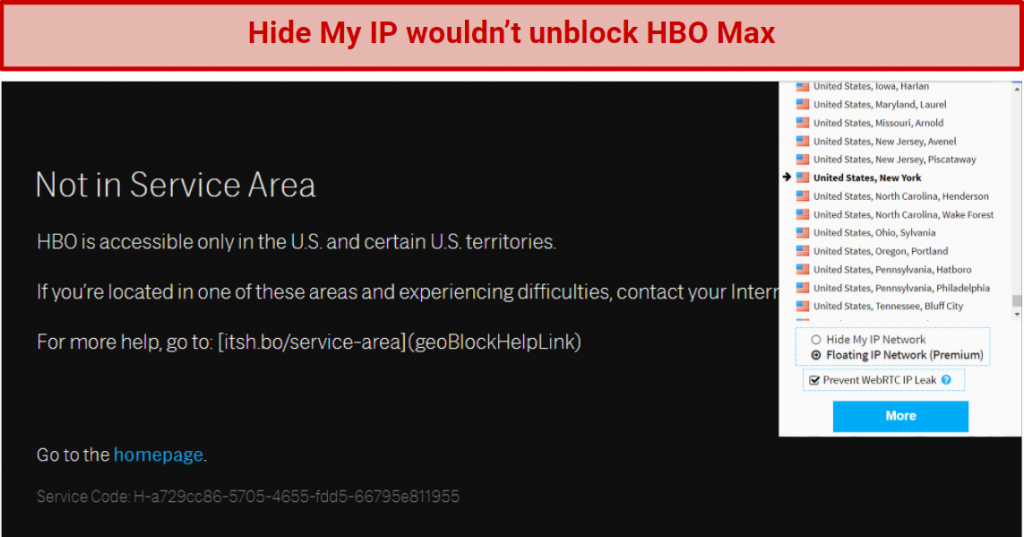 Even using the browser extension, Hide My IP failed to unblock HBO Max on any US server
Even using the browser extension, Hide My IP failed to unblock HBO Max on any US server
I discovered the same with Amazon Prime Video. Although I could log in, once I tried to access any content I was informed a VPN had been detected. These platforms are notoriously tricky for bypassing geoblocks. For the best of the best in streaming unblocking capability, you might want to check out these VPNs instead.
Speeds — Disappointing App Performance
The Windows app rarely worked, and when it did, Hide My IP’s servers were unreliable with atrocious speeds most of the time. The app seemed to prevent me from performing speed tests — although the browser extension fared much better. It worked much more reliably with my online tests and achieved consistent high speeds. For VPNs with reliable, superfast speeds on all the apps, here’s a roundup of the fastest.
Local Speeds
I first tested my base speed in the UK, before manually connecting to a local server using the Hide My IP native Windows app to note any speed changes. It took 5 attempts before I could get a reliable connection on a London server, or anything better than 1.5 Mbps.
|
VPN Disconnected (UK) |
VPN Connected
(UK) |
Speed With VPN Connected |
| Download |
44.10 Mbps |
42.3 Mbps |
4% decrease |
| Upload |
5.74 Mbps |
6.64 Mbps |
15% increase |
| Ping |
132 |
1 |
99% decrease |
Usually, you’d expect to see a slight drop when connected while the VPN encrypts your internet traffic, although there are exceptions to this rule. Hide My IP’s speeds didn’t decrease anywhere near enough to impact streaming, browsing, or gaming while connected to a local server. The ping actually decreased 99% on this particular test, which could be an anomaly, but would make a difference to online gaming.
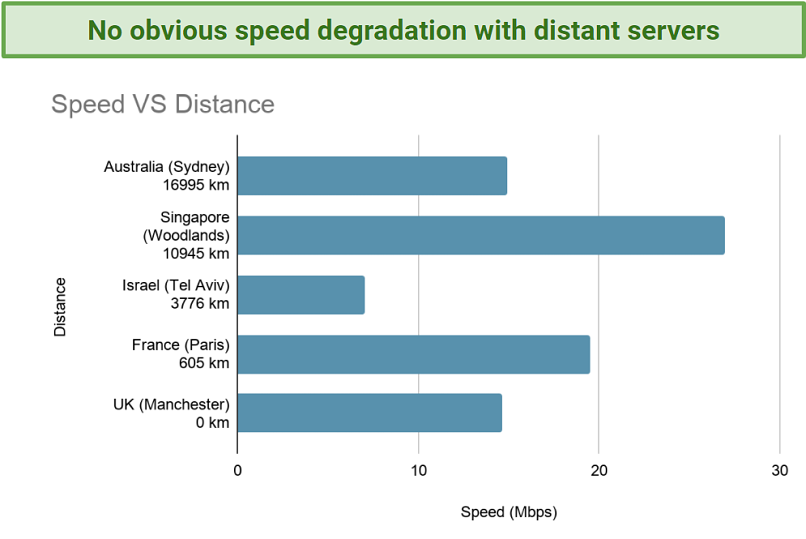
Long Distance Speeds
The Windows app was a near-total failure in my speed tests, as most of the time I couldn’t get a connection to even attempt a speed test. I tested 30+ global servers at increasing distances, including France, Greece, the US, Japan, and Australia. I had a brief connection to a New York server, but this failed before I could perform any testing.
This is totally unacceptable and very frustrating. I reached out to customer support on this, and the suggestion was to use the browser extension instead.
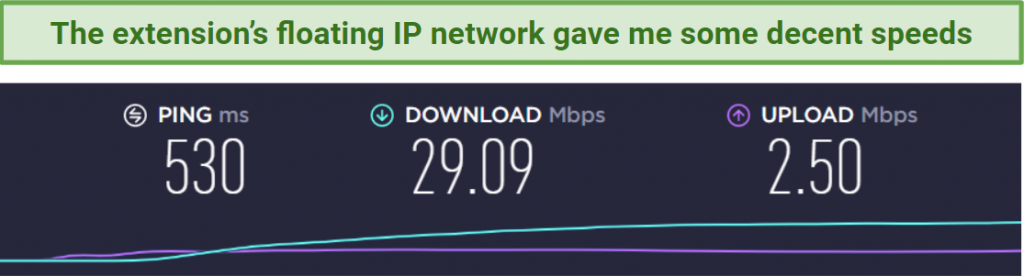
Using Hide My IP’s unusual (and far from ideal) configuration of a floating IP network within a browser extension, I experienced much better results. A few servers wouldn’t connect at all and took some time to build speed. However, I found working US servers in Miami, Texas, and New York — all averaging at around 28 Mbps. While this browser extension works well, there are some Chrome extensions that are more dependable.
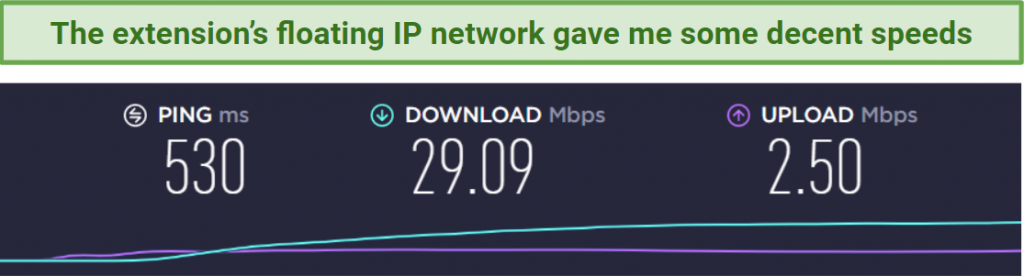 Hide My IP managed to deliver some decent speeds when I connected to a New York server
Hide My IP managed to deliver some decent speeds when I connected to a New York server
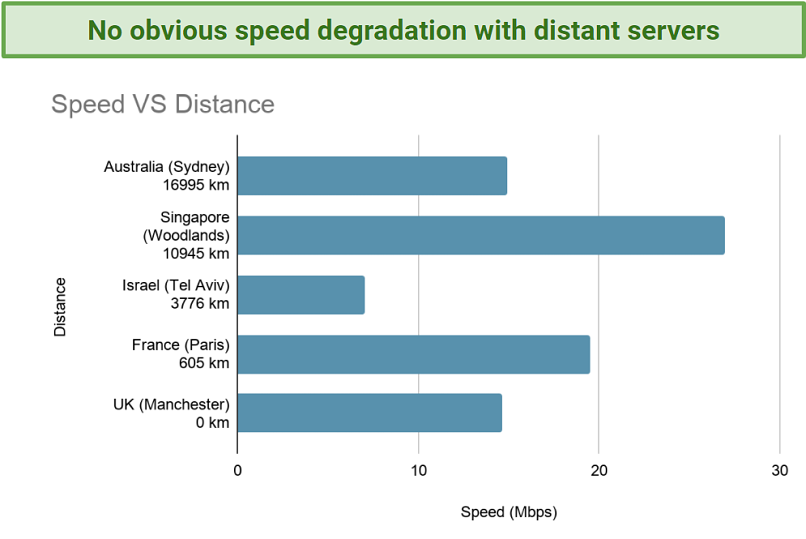
When connecting to global servers via the Chrome extension, Hide My IP performed well with decent speeds. I didn’t see any clear pattern of slowdowns with more distant servers, which can be expected with VPNs. You would have no problems with browsing, streaming, and some gaming using the extension.
 Using the extension, Hide My IP’s global servers delivered high enough speeds for HD streaming and fast browsing
Using the extension, Hide My IP’s global servers delivered high enough speeds for HD streaming and fast browsing
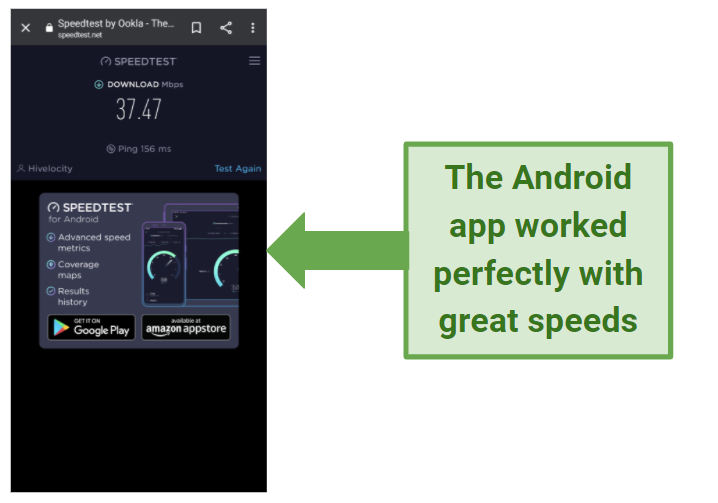
The Android version of the Hide My IP app worked much better than the Windows app. I got connected to all the US servers I tried within seconds, and reached consistently high speeds. A Tampa server I tested gave me over 37 Mbps, which is very impressive.
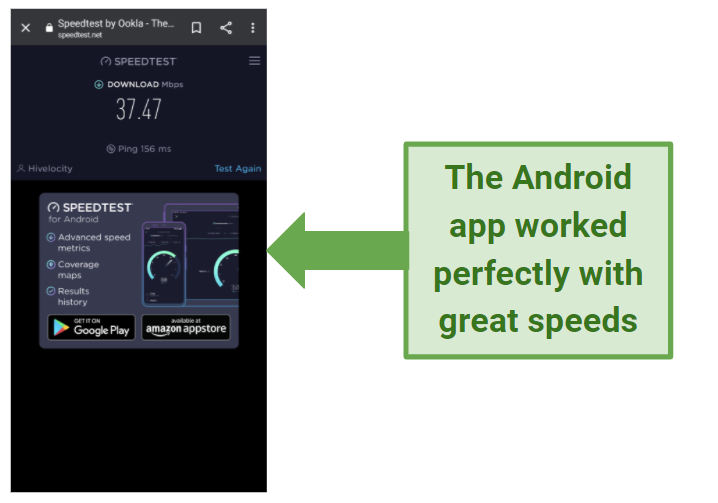 In contrast to the Windows app, the Android app gave me superfast speeds when connected to the VPN
In contrast to the Windows app, the Android app gave me superfast speeds when connected to the VPN
Overall, you can reach decent speeds with Hide My IP, but it takes some work to get there. If you have the premium version, and you’re happy using the floating IP network in the browser extension, the VPN will deliver on speed after some trial and error.
You also have the option of setting the VPN up as a Smart DNS Proxy for better speeds than the app, if you have the patience for this. However, proxies don’t encrypt your connection like a VPN, so you have to manually set up the service with the DNSCrypt client.
The whole process seems overly complicated and time-consuming when other VPN services provide native apps with good speeds and strong encryption — without any additional configuration.
If you’d rather use a provider with more reliable speeds and easier setup, check out our rundown of the fastest VPNs here.
Are Hide My IP’s Speeds Fast Enough for Gaming? Yes, for browser gaming
The speeds Hide My IP delivers are generally fast enough for light gaming, but only using the browser extension on a PC. You may also get good speeds using the smart DNS for gaming on a console or PC. However, the ping may not be good enough for serious competitive gaming. For that, I’d recommend using one of these high-end VPNs.
Generally, you need a ping below 170ms to have a leading edge, and I was getting above 500ms on most servers I tested. Ironically Singapore had the lowest ping at around 280, even though it’s one of the furthest servers away from me.
If you’re a PC gamer and playing games outside a browser, you might be disappointed with the slow speeds and unreliable connections using the Windows app.
 Speeds were great on the New York server I tested while playing Krunker, but ping wasn’t good
Speeds were great on the New York server I tested while playing Krunker, but ping wasn’t good
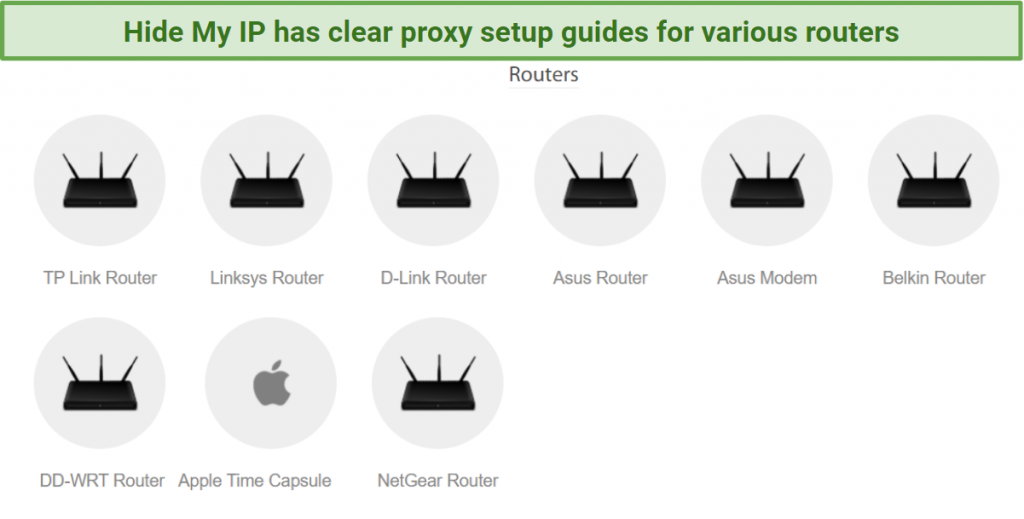
It’s possible to use Hide My IP with your gaming consoles, like a PS4/PS5 or Xbox One — the main advantages being access to games servers and DLC from different countries, and protection from DDoS attacks. This took me around 10 minutes to set up on my PS4.
You can also set up the VPN on your router if you want to use it with other consoles that don’t support VPNs (there’s a helpful guide for router set up in the Knowledge Base).
Server Network — Good Selection, But Unreliable
Hide My IP has 145 servers in 77 countries — a relatively good range to choose from, but unfortunately it seems to be potluck whether they’ll work for you. The server selection also differs between the app and the browser extension. For example, Tampa, FL is not an option on the floating IP network.
Using the Windows app, I found that most servers I tested either established an incredibly slow and unusable connection, or didn’t connect at all. Of the 30+ I tested — including Atlanta, Tokyo, and Perth — only the server in Tampa, FL managed to change my IP address when I checked. A server in London actually had me appearing in Greece.
This could mean that the IP database isn’t geographically accurate, and you could end up mistakenly geolocating yourself in the wrong country — bad news if you want the VPN to bypass geo-restrictions.
Security — Windows App Offers Poor Protection
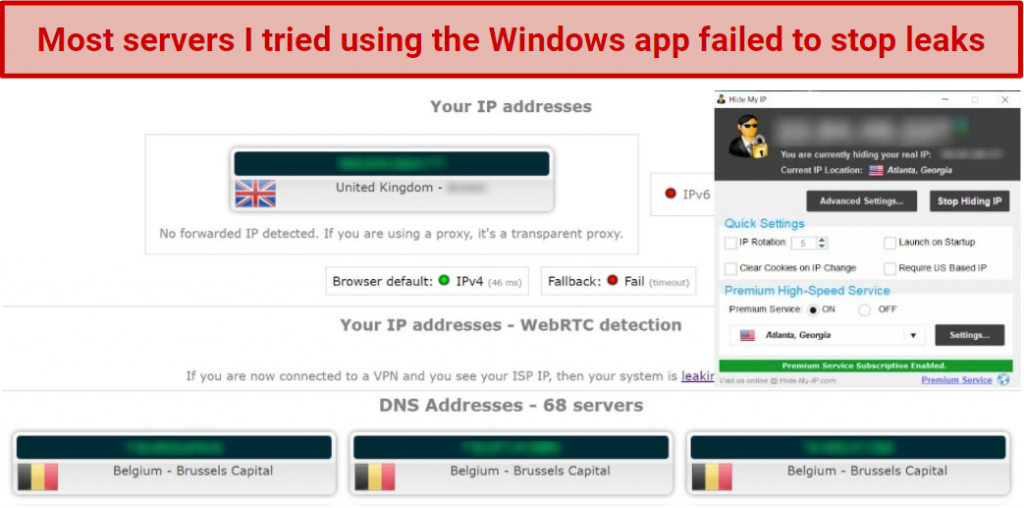
Hide My IP didn’t offer the protection I was looking for when using the Windows app. Out of 30+ servers I tried, most showed my real IP and location when checking for leaks — including the servers in Tokyo, New York, and Atlanta.
An IP leak can reveal your real location, and leave you exposed to cyber-threats. You’ll also want to prevent DNS leaks, where your internet traffic with your ISP is susceptible to privacy breaches. WebRTC leaks are browser-specific — essentially peer-to-peer communication between your browser and the webpage that can expose your IP address.
Only the US server in Atlanta worked once to change my IP address, but then the following day would not successfully protect me again. My IP and DNS requests were exposed, and it didn’t block WebRTC.
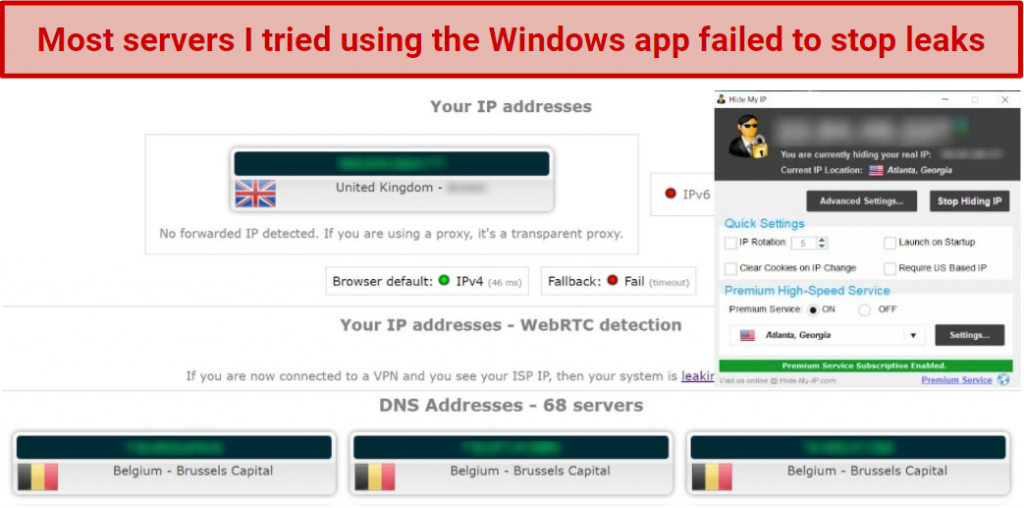 The app showed I was connected, but my IP, DNS, and WebRTC were leaked
The app showed I was connected, but my IP, DNS, and WebRTC were leaked
You should be able to use the Smart DNS to get around these app issues, but it’s complicated and time-consuming. I wouldn’t recommend using the Hide My IP Windows app at all — instead, have a look at these Windows VPNs that are much more secure and reliable.
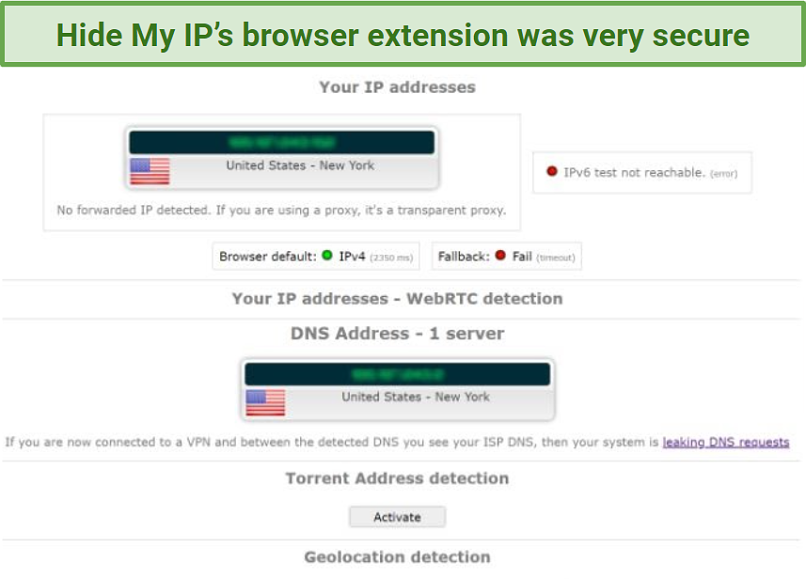
However, the browser extension (premium version only) was brilliant. Every server I connected to worked within around 10 seconds. It successfully changed my IP address, hid my DNS requests, and WebRTC was blocked (for this you need to select the option to disable it). I’d certainly put more trust in the browser extension to keep my online activity safe.
IPv6 was also disabled — which is a good thing. If your ISP supports IPv6 you’ll want a VPN that directs this type of traffic through the secure tunnel. Many don’t, leaving your data exposed, so it was good to see that Hide My IP prevented these leaks.
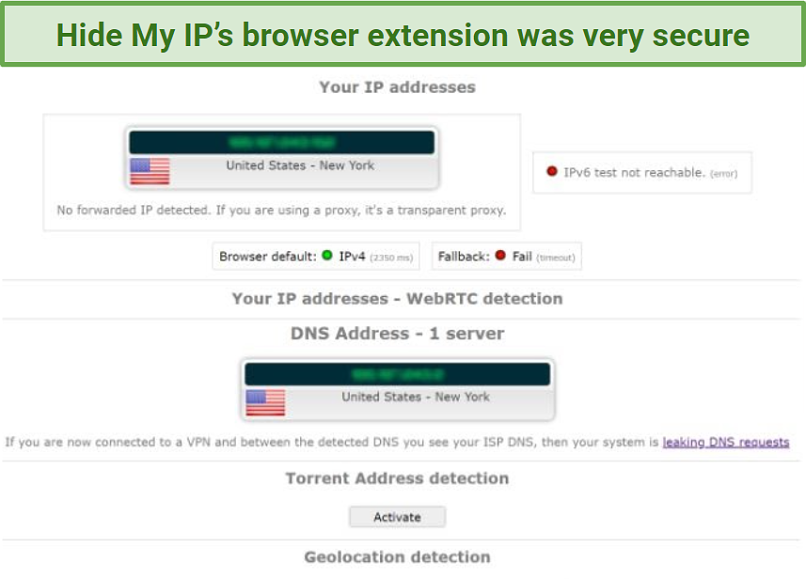 In contrast to the Windows app, the Chrome extension gave me excellent security
In contrast to the Windows app, the Chrome extension gave me excellent security
Hide My IP uses military-grade AES 256-bit encryption with a 2048-bit key, so you should be protected from the most sinister of cyber-attacks. Other than that, the security details on the webpage are pretty scant. You shouldn’t have to contact customer support to find out more as I did.
Eventually, I found out that there’s an automatic kill-switch in the Windows app, and Hide My IP uses OpenVPN protocols. Even that information was disappointing; I’d like to see a kill switch available for all platforms and to have more protocol options.
Privacy — Unclear Stance on Logging Policy
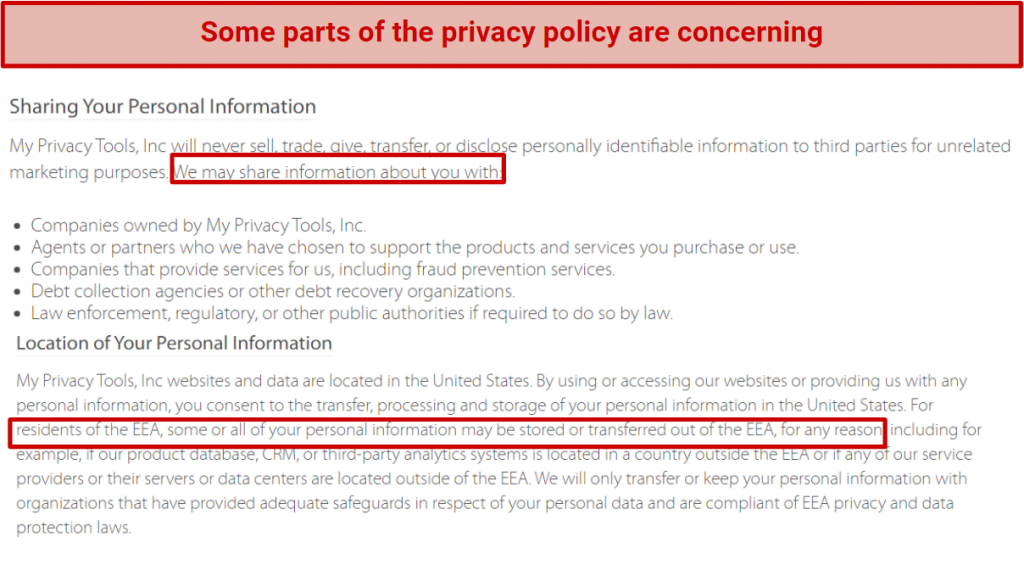
Hide My IPs no-logs policy is too vague. The company is based in San Diego in the US, and therefore subject to the 5 Eyes alliance — meaning the VPN could be legally compelled to hand over your sensitive data to government agencies.
This isn’t a problem if a VPN isn’t logging your activity, but some parts of Hide My IP’s policy raise questions.
The privacy policy openly states that the VPN may share your information and that “some or all of your personal information may be stored or transferred out of the EEA, for any reason".
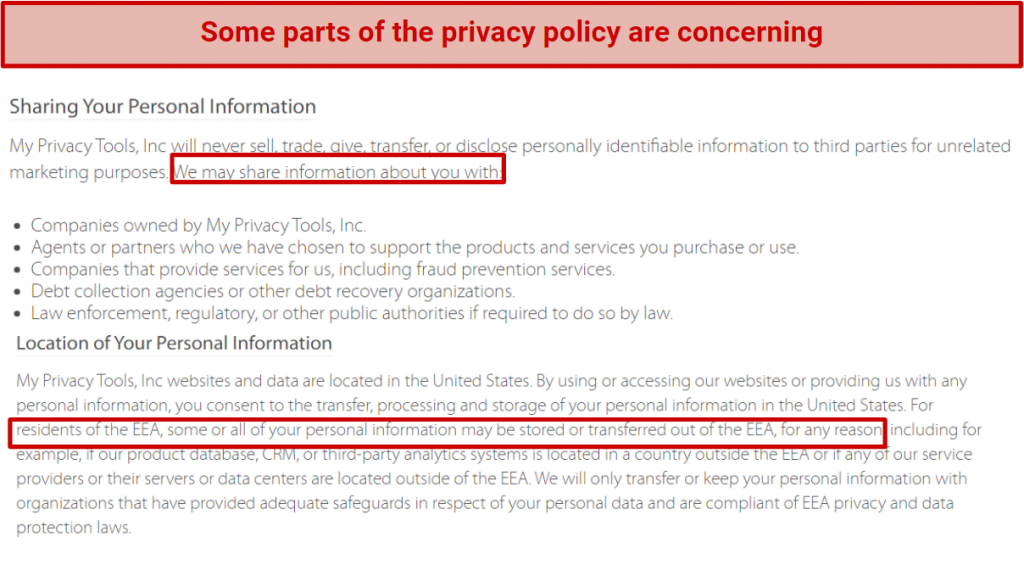 The privacy policy contains clauses that I found to be questionable
The privacy policy contains clauses that I found to be questionable
I did reach out to Hide My IP’s customer support to ask more about these worrying clauses. Unfortunately, the answer I got was very brief — sticking to “we do not have logs" without further clarification. The VPN isn’t independently audited, so we can only take Hide My IP’s word that it’s not logging your online activity.
One plus point is that there’s an accountless VPN option that you can purchase on a daily basis. No account or subscription is required, and you can purchase with Bitcoin. That does give you a bit more anonymity and is something I’d like to see more VPNs offering.
On the webpage you’ll also find a free list of open proxies, so you can use these without the need for any authentication as well (though the service takes a lot of setting up to make it secure, and won’t suit you if you’re looking for quick and easy installation).
Torrenting — P2P Allowed but Apps Not Secure Enough
The VPN allows torrenting, but the apps aren’t good enough for it. In addition, Hide My IP is very clear on disallowing copyrighted material. A lot of VPNs say the same, but they have watertight logging policies that ensure you can torrent safely — even if you accidentally download copyrighted material.
Hide My IP may claim to be torrent-friendly but, as it’s based in the US and hasn’t got the most reassuring privacy policy, it’s a risky choice for P2P activity.
 Some VPNs clearly dissuade users from downloading copyrighted content
Some VPNs clearly dissuade users from downloading copyrighted content
Even if you want to take the risk, Hide My IP isn’t reliable for torrenting anyway. I tested BitTorrent with the VPN’s Windows app and couldn’t get it to work at all. The only way I could establish a connection and get speeds fast enough for P2P traffic was with the smart DNS proxy service. Again, this extra level of configuration was frustrating, and a proxy won’t encrypt your torrenting data.
Overall, I wouldn’t recommend Hide My IP for torrenting due to the concerns around privacy, and the clunky performance of the apps. Take a look at our best VPNs for torrenting to see some better options.
Does Hide My IP Work in China? Yes
The customer support for Hide My IP indicated that their service is functional in China. Yet, based on my experience finding it inconsistent, I'd be skeptical about its effectiveness in such a heavily restricted environment.
That said, I would strongly advise you not to use the Windows app in China, or another country where VPNs may not be encouraged due to my experience with IP and DNS leaks.
Take at a look at these VPNs assured to work in China.
Simultaneous Device Connections — 5 Simultaneous Connections
The premium version of Hide My IP allows 5 simultaneous devices. You can install or use the VPN on up to 5 devices without any blocks or bandwidth restrictions. I used it on 2 Android mobile devices, a PS4, and a Windows desktop without any connectivity issues besides the difficulties with the Windows app.
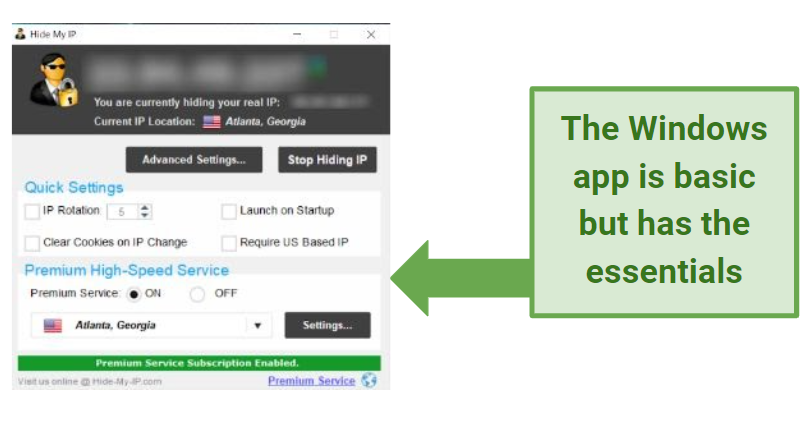
Device Compatibility — Wide Range of Devices Supported
There are dedicated apps for major platforms including Windows, Mac, Android, and iOS. The iOs version. To get the VPN working on your iOS devices, such as an iPhone or iPad, you’ll also need to set it up via the OpenVPN Connect app in conjunction with the iOS Hide My IP app. You may find this to be a lengthy process, but there is a handy online guide that is very easy to follow.
Unfortunately, apart from the Android app, I found most of the apps to be almost unusable, especially the Windows version. For VPNs that are assured to work with Windows, I recommend these providers. The Android app has some settings not found in the Windows app, like enabling the kill-switch and choice of preferred protocol (TCP or UDP). However, it doesn’t have the IP rotation option or additional DNS settings.
The Hide My IP browser extension worked much better than most of the apps. You’ll find it available for Chrome, and Firefox, so you should be able to use it on any Linux device.
You can use Hide My IP with the Smart DNS Proxy, enabling you to use it with any WiFi-enabled device, even if it doesn’t have a native app. You can use it this way with your PS4, Smart TV, and more - and any device on your network if you set it up on your router. There are guides on the webpage covering everything from older versions of the platforms above, Ubuntu, and Chromebook, to a list of compatible routers.
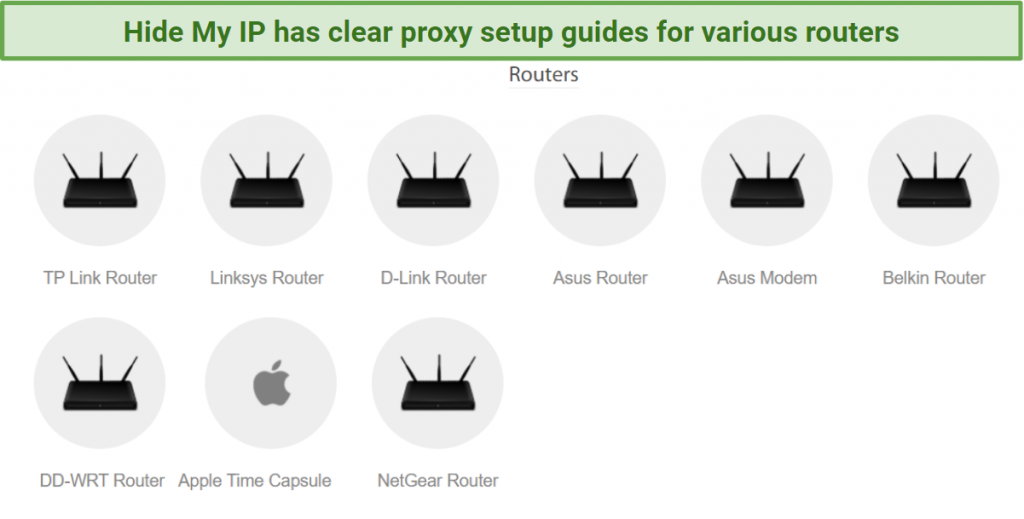 I was able to find helpful manual setup guides for many platforms, including a list of routers
I was able to find helpful manual setup guides for many platforms, including a list of routers